Regulatory clarity premium
Simplified compliance rules across jurisdictions would increase access stability by reducing legal uncertainty for multinational service providers operating in multiple regulatory zones. When firms face divergent data protection or cybersecurity mandates—such as under GDPR, CCPA, and Brazil’s LGPD—their default response is often to restrict functionality or withdraw services from ambiguous markets to avoid penalties; harmonized standards lower this compliance tax, enabling more consistent service uptime and user access, especially in edge jurisdictions. This effect is driven not by technical security improvements but by the strategic choices of corporate actors who prioritize regulatory predictability over redundant safeguards, revealing an underappreciated incentive structure where legal coherence becomes a de facto infrastructure for availability.
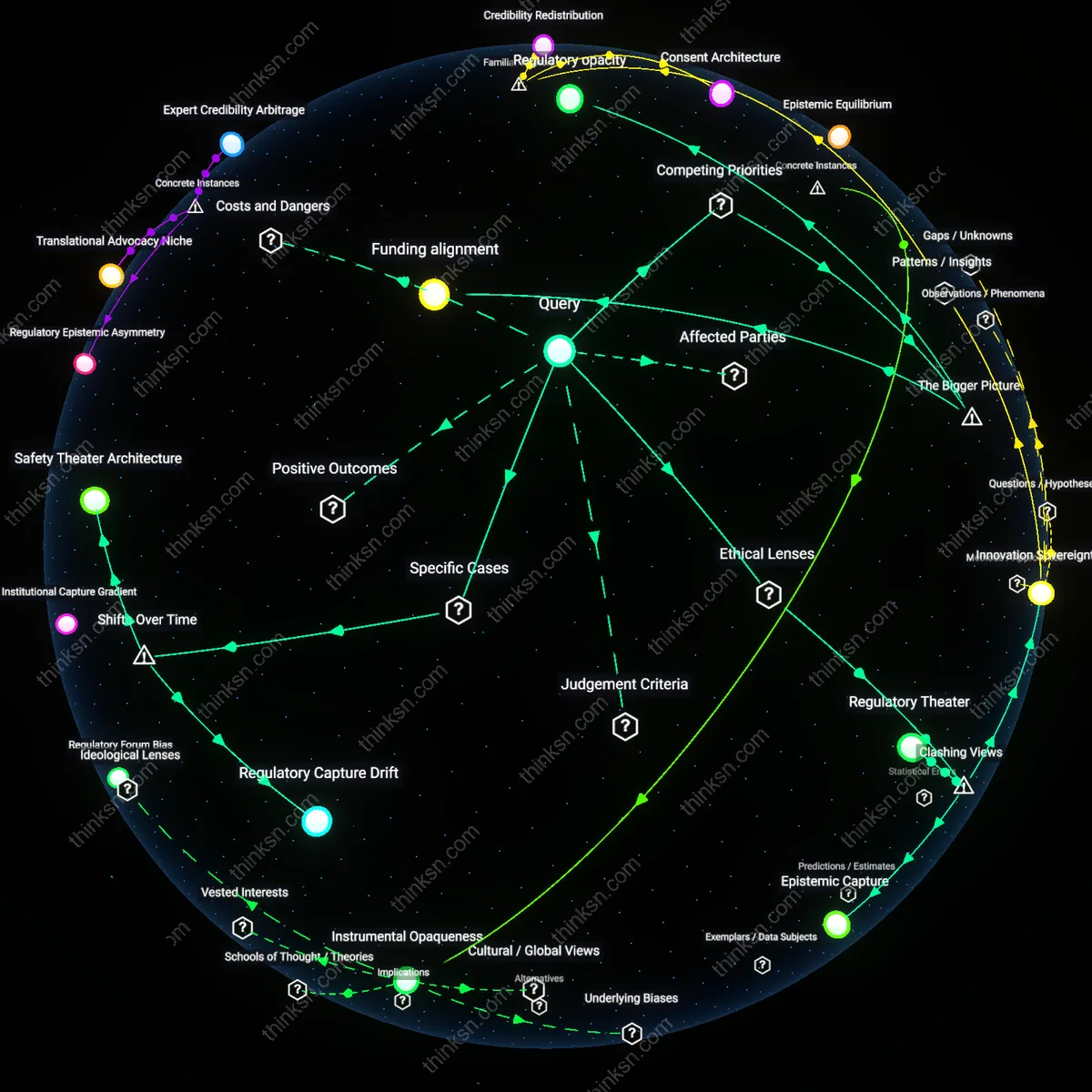
Enforcement capacity drain
If companies simplify compliance rules across overlapping jurisdictions, access stability may decline in weaker regulatory environments due to the erosion of localized enforcement leverage. National regulators in smaller or less-resourced states—such as those in the Global South—often rely on jurisdictional complexity as a counterweight to corporate power, using tailored audits, data localization, or conditional licensing to compel adherence; streamlining rules at a supranational level risks centralizing compliance authority with dominant firms, reducing the ability of local agencies to demand accountability or service continuity. This dynamic exposes how access stability is not just a product of technical systems but of political bargaining, where jurisdictional friction paradoxically sustains accountability.
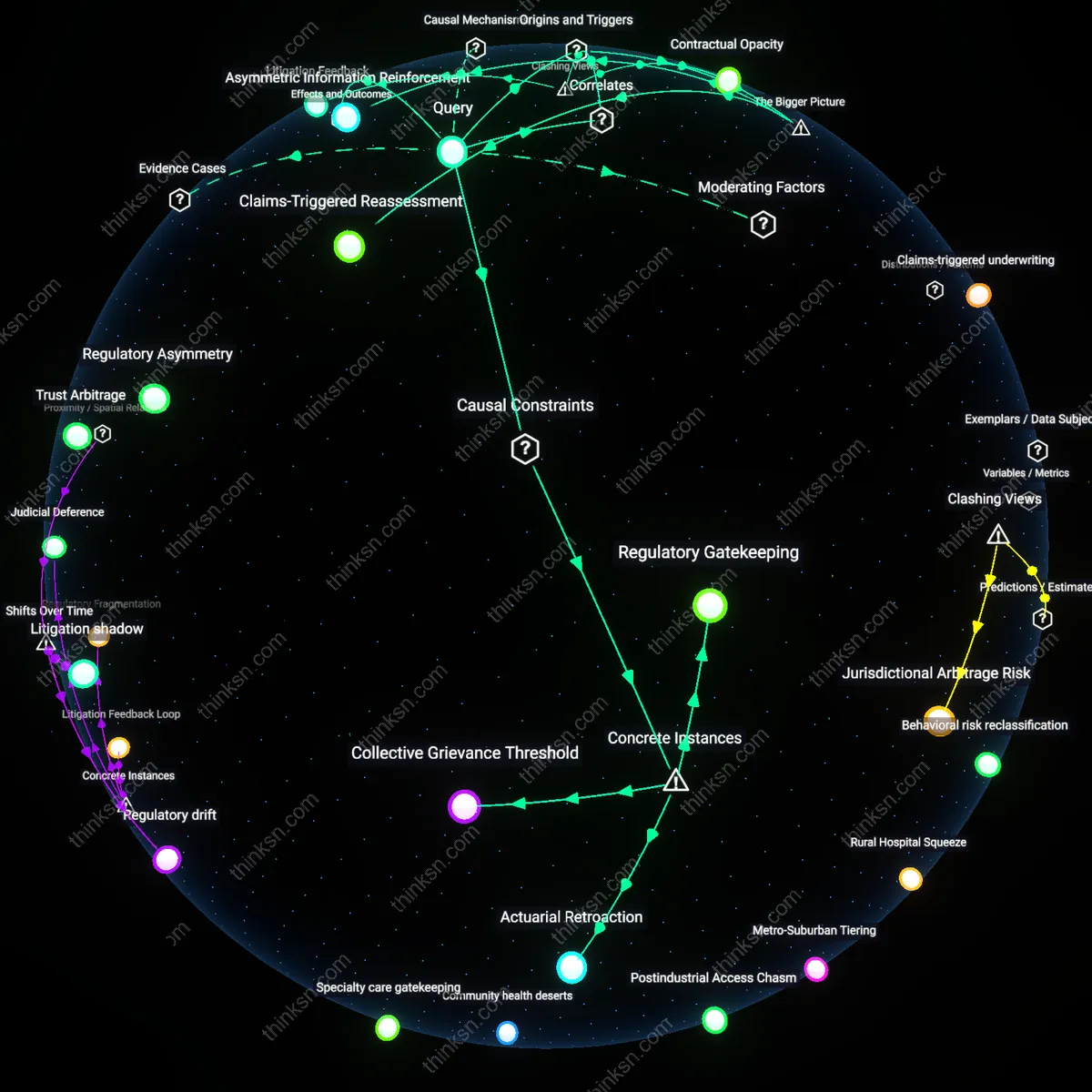
Risk convergence externality
Standardizing compliance across jurisdictions can destabilize access by creating monoculture-like vulnerabilities in governance design, where a single compliance framework adopted globally becomes a systemic risk node when challenged by novel threats or jurisdiction-specific crises. For example, if a unified AI auditing standard is adopted across the EU, Canada, and Japan, a flaw in its incident reporting logic could synchronously disable access controls across platforms like cloud providers or social media during high-stakes events, such as elections or pandemics. Unlike layered security, which diversifies risk through redundancy, harmonization concentrates institutional trust in shared procedural logic—making access stability more efficient under normal conditions but more fragile under stress, akin to financial system dependencies on common credit rating models.
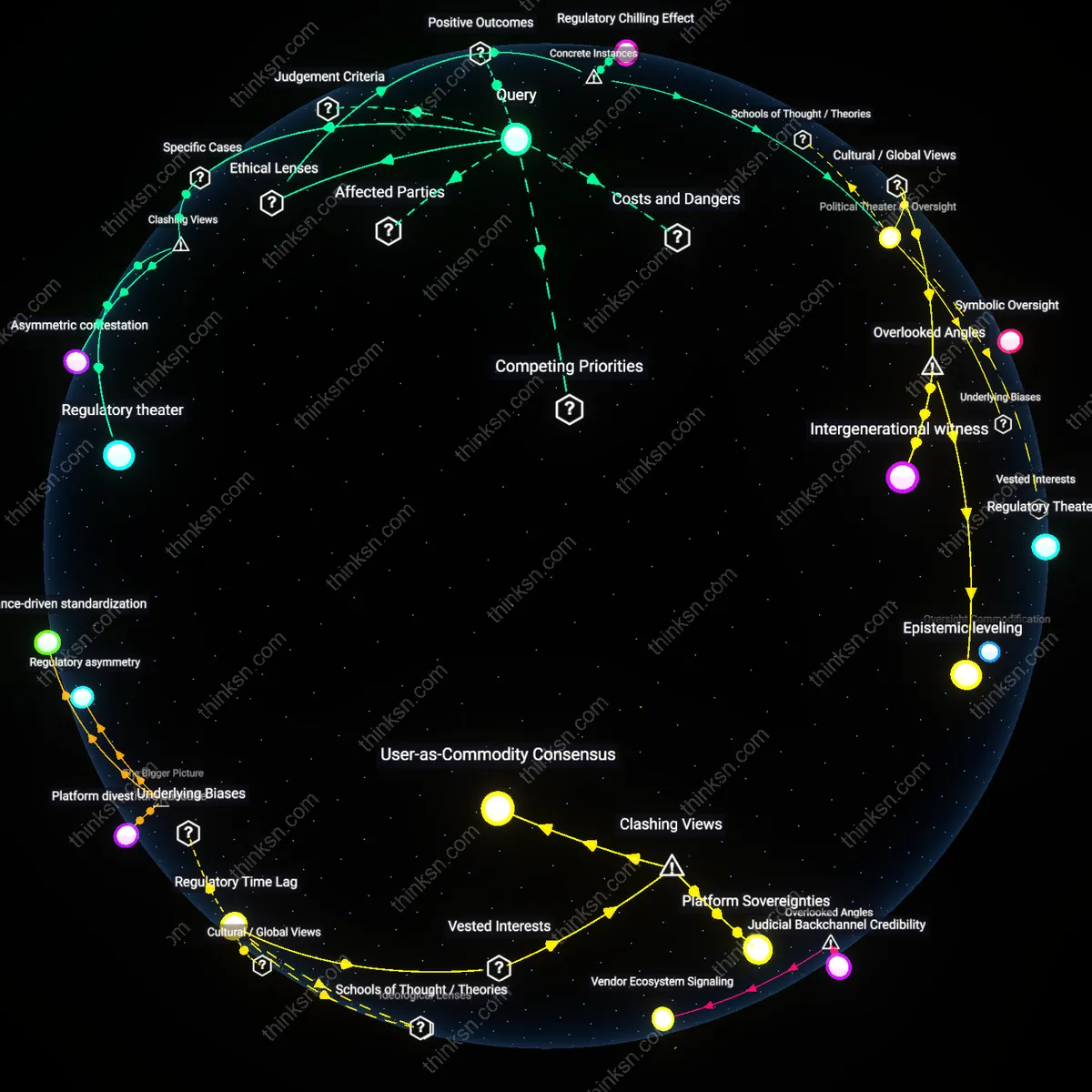
Compliance arbitrage
Simplified compliance rules across jurisdictions would enable firms to exploit regulatory gaps rather than reduce operational friction. Multinational corporations, particularly in tech and finance, actively monitor jurisdictional discrepancies to consolidate data processing in regions with weaker enforcement, using standardization as cover for de facto deregulation. This mechanism mirrors tax arbitrage strategies seen in offshore finance hubs, where harmonized reporting rules have historically enabled firms to minimize accountability without improving transparency. The non-obvious consequence is that apparent regulatory simplicity can erode access stability by encouraging forum shopping instead of strengthening baseline protections.
Enforcement dilution
Harmonizing compliance rules across jurisdictions would weaken access stability by defaulting to the lowest common denominator in enforcement capacity. Agencies like the EU’s EDPS or the U.S. FTC operate under distinct statutory mandates and resource constraints, meaning any cross-jurisdictional framework must compromise on stringency to gain adoption. This dynamic systematically disadvantages high-enforcement regimes, as seen in the GDPR’s extraterritorial challenges when U.S. firms comply through minimal technical adjustments rather than substantive changes. The underappreciated risk is that standardization does not equate to strengthening oversight—instead, it often institutionalizes weakest-link enforcement.
Infrastructure rigidity
Streamlining compliance rules would lock in existing digital infrastructures by reducing pressure to adapt access controls to local contexts, ultimately decreasing system resilience. Cloud providers like AWS or Azure optimize for uniform policy deployment across regions, meaning simplified rules encourage hardcoded compliance workflows rather than context-sensitive access governance. This creates systemic brittleness, as seen during cross-border health data sharing in the 2020s, when uniform consent frameworks failed during regional emergencies due to lack of adaptive granularity. The overlooked insight is that regulatory redundancy can function as a form of distributed fault tolerance, not just bureaucratic overhead.
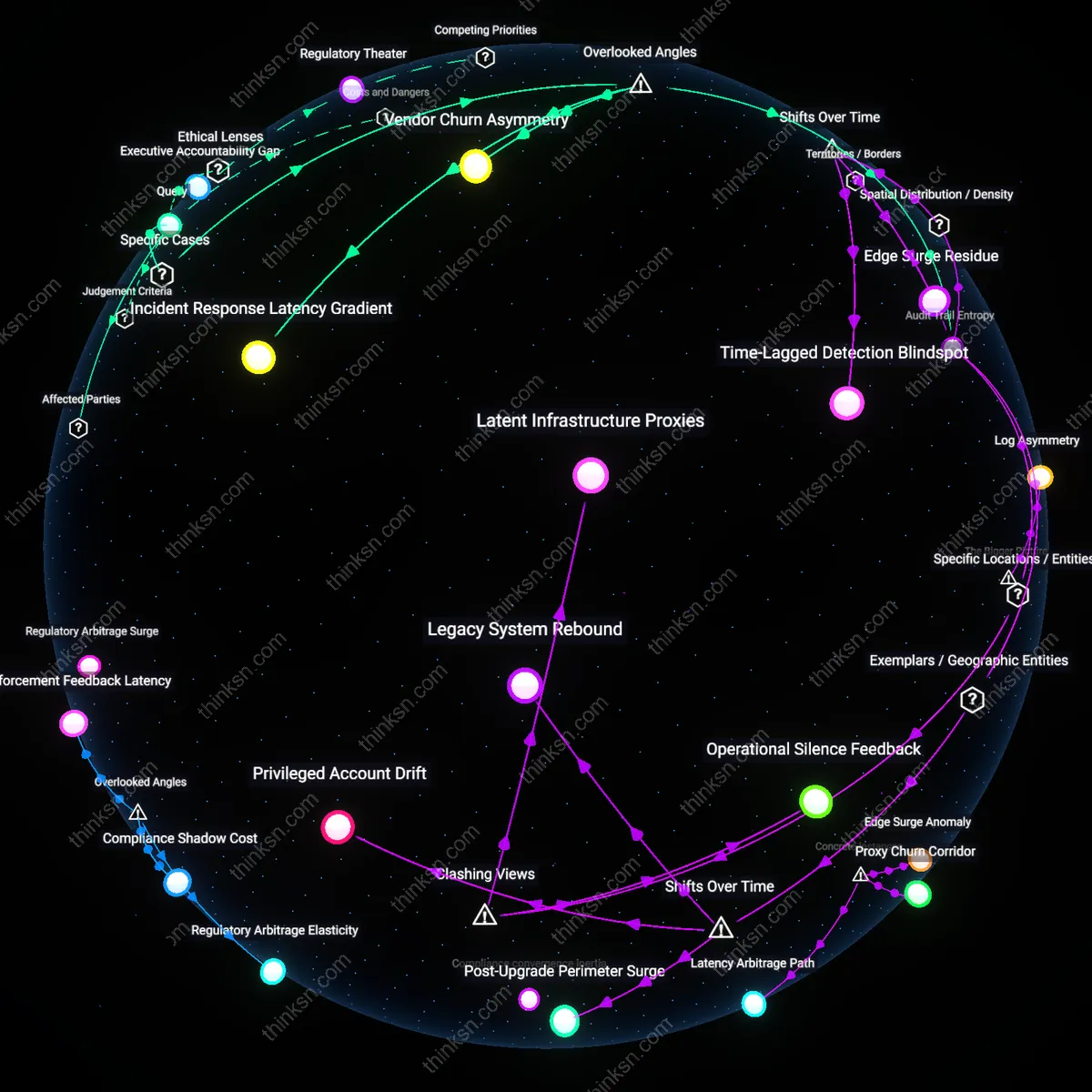
Regulatory Arbitrage Surge
Simplifying compliance rules across jurisdictions would destabilize access by incentivizing firms to migrate operations to the weakest regulatory tier, exploiting harmonized standards as a floor rather than a ceiling. This mechanism operates through multinational corporations leveraging legal subsidiaries in permissive jurisdictions—like Ireland for data routing or Delaware for corporate registration—to set precedent for minimal adherence, thereby eroding the de facto strength of stricter local regimes. The non-obvious consequence is that reduction in complexity doesn’t enhance stability but amplifies strategic noncompliance, revealing how uniformity without parity in enforcement enables race-to-the-bottom dynamics.
Compliance Opacity Trap
Streamlined rules would reduce transparency in accountability mechanisms, making it harder for civil society and oversight bodies to detect violations, especially in high-risk regions like healthcare data exchanges between the EU and U.S. The condition enabling this is that simplified frameworks obscure jurisdictional handoffs—such as when a HIPAA-GDPR hybrid rule merges audit requirements into a single reporting standard, eliminating granular tracing of where breaches originate. This reveals that less procedural friction doesn't clarify responsibility but masks enforcement gaps, challenging the assumption that clarity and compliance are inherently aligned.
Security Externalization Cycle
Reducing layered compliance would shift security burdens onto end-users and smaller ecosystem actors, as dominant platforms like cloud infrastructure providers relax internal controls under the guise of regulatory alignment. This occurs because large tech firms use harmonization as leverage to rationalize consolidated security protocols—such as AWS adjusting access controls to meet an average of regional standards—leaving edge systems in education or local government underprotected. The dissonance lies in recognizing that top-down simplification doesn't strengthen systemic resilience but institutionalizes risk deflection, exposing how centralization masquerades as efficiency.
Regulatory Arbitrage Elasticity
Simplifying compliance rules across jurisdictions would increase access stability by reducing the incentive for firms to exploit gaps through regulatory arbitrage, a mechanism most visible in fintech firms operating across EU and ASEAN markets where mismatched data localization requirements currently drive forum shopping. The stability gain emerges not from fewer rules, but from narrowed differentials in enforcement thresholds, which diminishes the competitive advantage of choosing lax regimes—this dynamic is overlooked because standard analyses treat harmonization as a top-down legal outcome rather than a function of how differentially strict thresholds shape firm migration. The elasticity of arbitrage opportunities, not the number of rules, becomes the key variable determining access continuity.
Compliance Shadow Cost
Access stability would degrade for mid-tier cloud service providers if compliance rules were simplified, because reduced procedural complexity would lower the shadow cost of regulatory entry barriers maintained by dominant providers through lobbying in bodies like the OECD and ISO. These incumbents leverage intricate, overlapping standards to create de facto moats—simplification would flatten this advantage but trigger retaliatory standardization in technical interoperability specs, disrupting smaller players reliant on niche compliance-as-differentiation. This effect is typically missed because analyses focus on burden reduction, not how complexity functions as a covert instrument of market segmentation among vendors in multi-jurisdictional SaaS supply chains.
Enforcement Feedback Latency
Streamlining compliance across jurisdictions would initially destabilize access due to increased enforcement feedback latency, particularly in cross-border health data systems where regulators in Canada and Germany rely on delayed audit cascades from local compliance artifacts to detect breaches. When rules are simplified, the volume of audit triggers drops, thinning the observational data that agencies use to calibrate risk models, thereby extending the time between violation and corrective action. This latency effect is rarely considered because harmonization debates assume faster compliance equates to faster enforcement, when in practice it reduces diagnostic granularity in monitoring systems that depend on procedural redundancy as a surveillance proxy.
Regulatory arbitrage reduction
Harmonizing compliance rules across EU member states through the General Data Protection Regulation (GDPR) decreased the instability caused by fragmented national interpretations, enabling organizations to rely on a single, unified framework for data access and processing across 28+ jurisdictions. This coherence reduced legal unpredictability for cross-border data flows, particularly for SMEs previously burdened by conflicting requirements, revealing that alignment—not accumulation—of rules can stabilize access by eliminating jurisdictional gaming. The underappreciated lesson is that complexity fuels strategic noncompliance, not security, and that simplification can be a stronger stabilizer than additional controls.
Compliance convergence inertia
After the 2008 financial crisis, the Basel III accords sought to harmonize banking regulations globally, but instead of reducing complexity, national implementations in the U.S., EU, and Japan layered additional domestic safeguards atop the common framework, creating new frictions in access to international capital markets. Despite intent, this patchwork perpetuated instability because institutions faced competing interpretations of 'simple' rules, demonstrating that simplification fails without enforcement homogeneity. The non-obvious insight is that procedural alignment matters more than rule design—without synchronized application, even streamlined rules fragment into de facto barriers.
Legitimacy-driven adherence
In 2015, India’s Unified Payments Interface (UPI) replaced a fragmented landscape of state and bank-specific digital payment protocols with a single, simplified national standard, dramatically increasing transaction stability and access for over 300 million users. By reducing compliance overhead for fintechs and banks alike, UPI fostered widespread voluntary adherence not because of stricter enforcement but because the system’s simplicity made noncompliance irrational. The overlooked mechanism is that ease of use generates compliance as a default behavior, not through force but through systemic attraction—proof that access stability emerges not from control depth but from rule clarity.