Are Third-Party Auth APIs Leaving You Vulnerable?
Analysis reveals 5 key thematic connections.
Key Findings
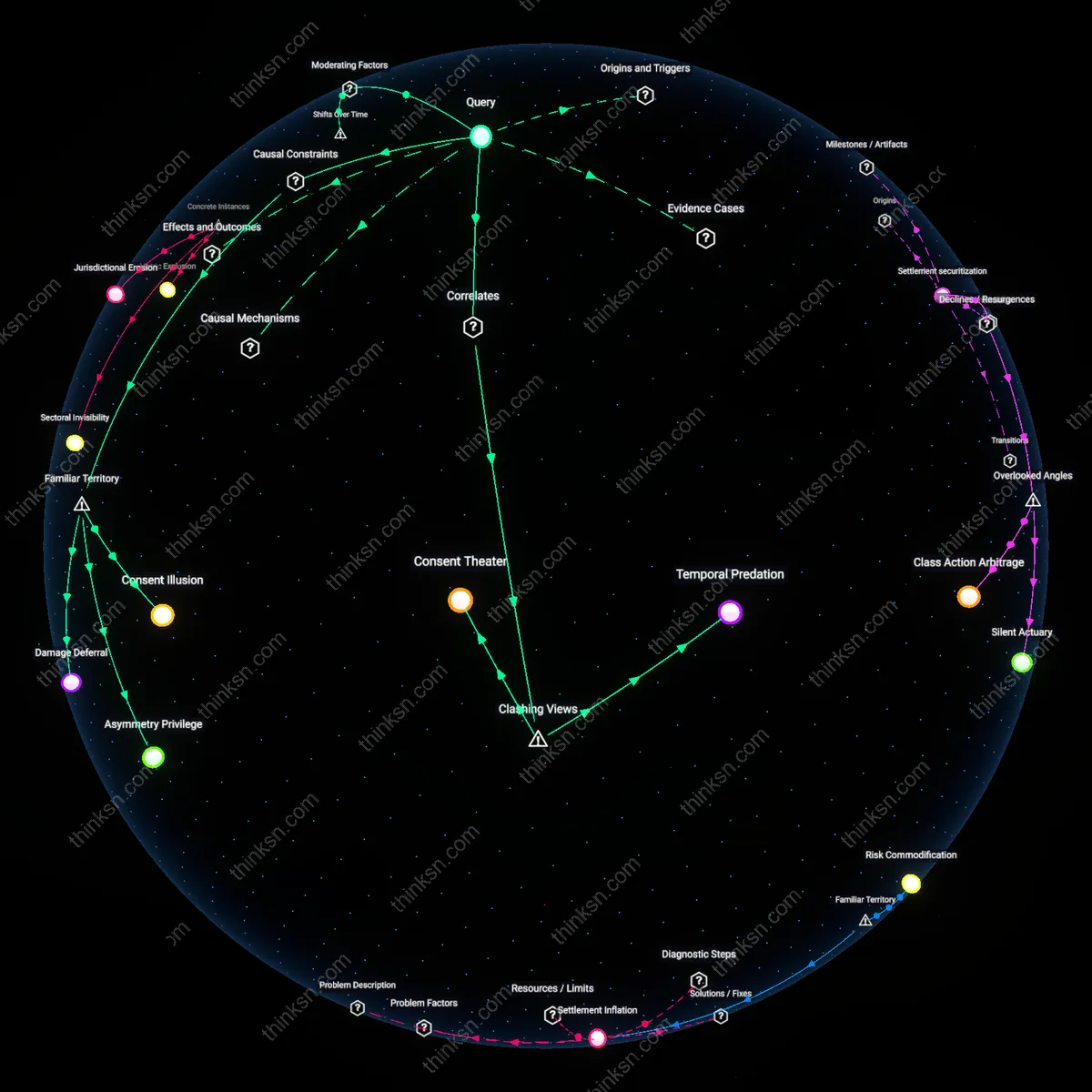
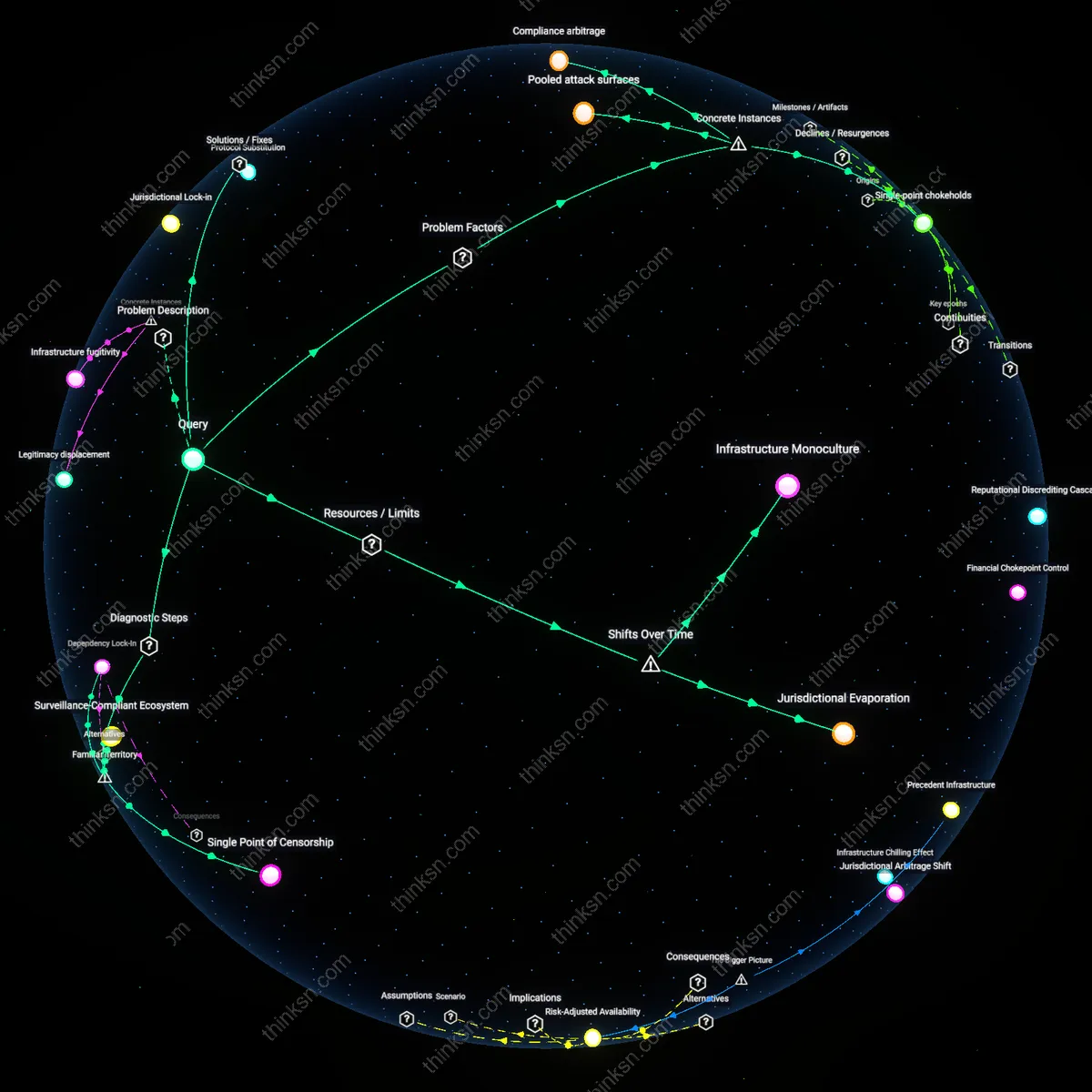
Authentication Monoculture
Reliance on a few dominant identity providers like Google or Facebook consolidates authentication power into centralized platforms, making widespread system failure inevitable when one is compromised. This concentration emerges not from technical superiority but from network effects and corporate partnerships that lock in user access pathways. Most users perceive convenience as the primary trade-off, overlooking how homogenized trust architectures amplify breach impacts across services, rendering individual security practices irrelevant during cascading failures.
Credential Asymmetry
Users surrender exclusive control over their identity credentials to third-party providers, creating a power imbalance where affected individuals cannot independently verify or revoke access after a breach. Platforms like OAuth enable seamless logins but operate opaque audit trails that prevent users from tracking credential misuse. While the public associates account safety with strong passwords or 2FA, the underlying dependency means security decisions are made remotely by corporate entities with misaligned incentives.
Compliance Mirage
Regulatory frameworks like GDPR or SOC 2 certification create an illusion of systemic accountability, leading services and users to assume third-party auth providers inherently protect their data. This trust is institutionalized through compliance signaling rather than verified operational resilience, so breaches expose how oversight fails to enforce real-time security obligations. The familiar association of certification with safety masks the absence of enforceable user redress when centralized providers fail.
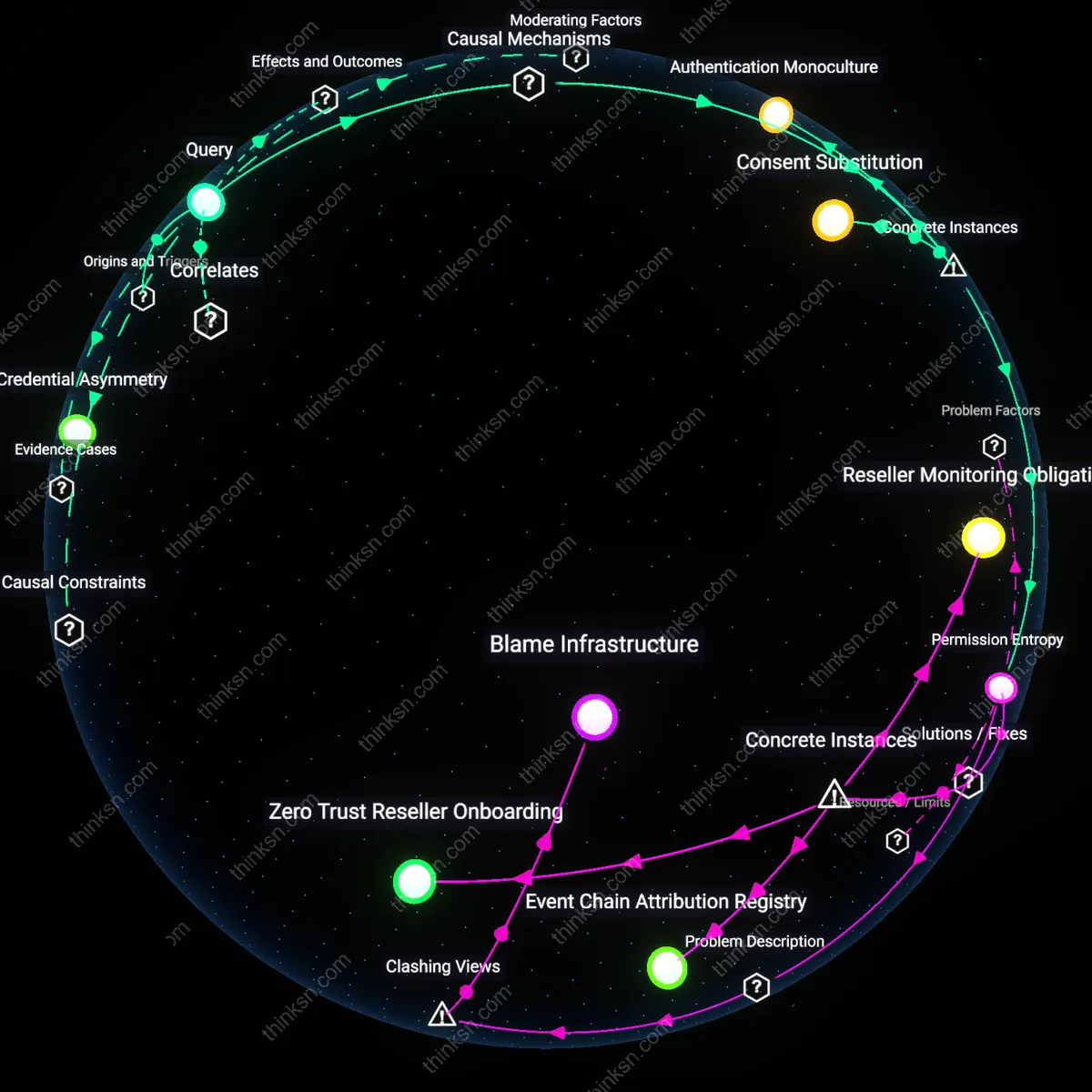
Consent Substitution
When Google's OAuth 2.0 implementation was exploited during the 2017 'Copycat' malware campaign, malicious apps gained access to user data under the guise of legitimate authentication, illustrating how third-party authorization routines can misrepresent user intent. Despite individual users carefully managing permissions, the architecture treats API consent as a proxy for ongoing control, allowing approved apps to act autonomously long after initial authentication. The breach revealed that user agency is institutionally deferred to the provider's access-granting logic, which treats each approved token as a substitute for continuous oversight. This mechanism systematically replaces meaningful consent with technical compliance, rendering individual vigilance irrelevant once authorization is embedded in provider-mediated workflows.
Permission Entropy
The 2020 Okta reseller compromise led to unauthorized access to customer systems at firms like DoorDash and Alphabet’s CapitalG, not through direct penetration but via cascading authentication privileges inherent in identity management layers. As Okta delegated administrative capabilities to third-party resellers without equivalent security mandates, attackers exploited the trust transitivity built into the API ecosystem—where one provider’s lax controls pollute downstream clients. This shows that individual organizations cannot isolate their security posture when identity is mediated through layered vendors, as permission structures accumulate complexity and invisibility over time. The overlooked consequence is that even robust internal safeguards become ineffective when external dependencies introduce unmonitored vectors of escalation.