Is Single-Sign-On Convenience Worth Employer Data Power?
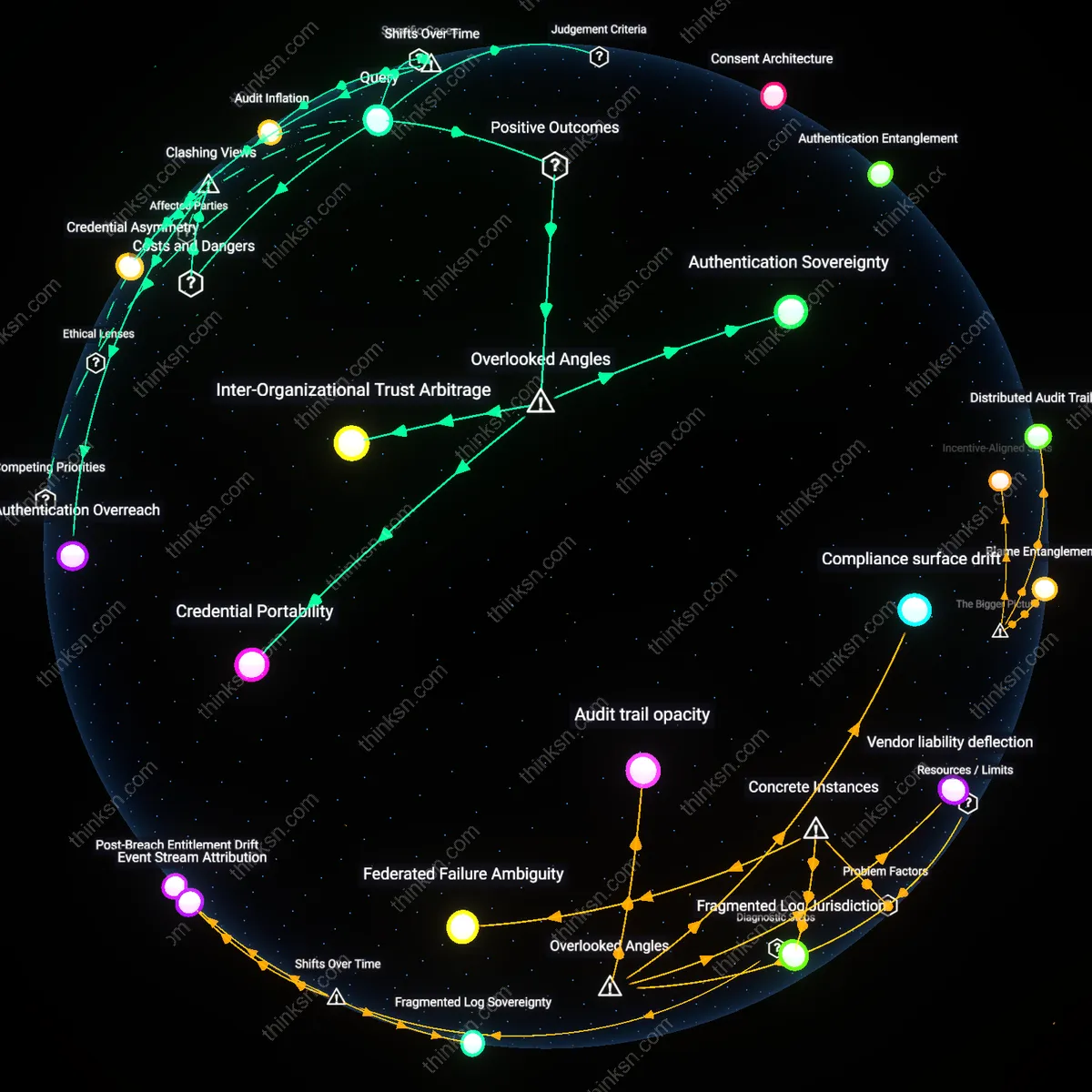
Analysis reveals 9 key thematic connections.
Key Findings
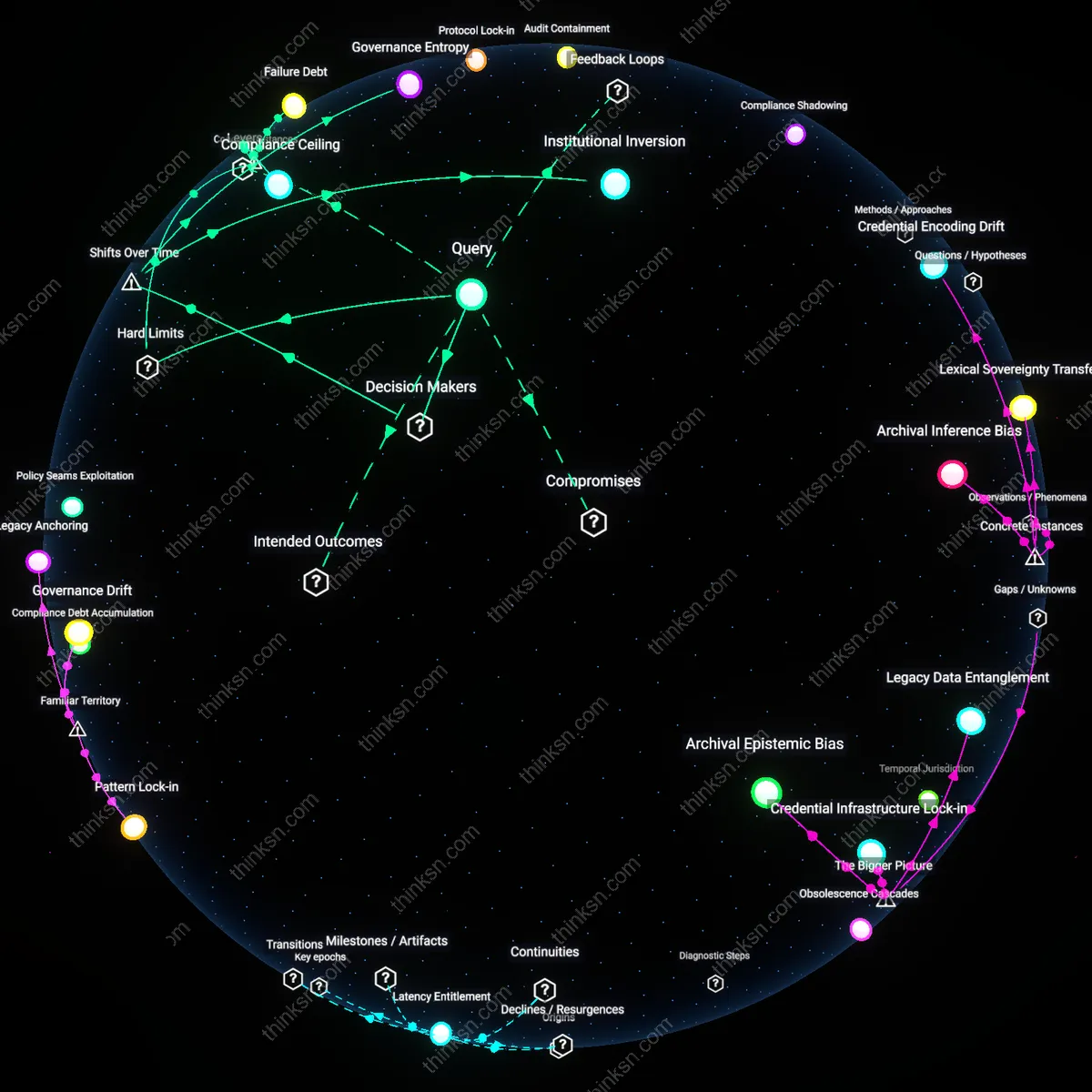
Consent Architecture
Professionals can reclaim agency by designing SSO systems where explicit, revocable employee consent gates each data access instance. This shifts control from employer-as-default-administrator to employee-as-permission-grantor, operating through standardized OAuth 2.0 workflows in corporate identity providers like Okta or Azure AD. The non-obvious insight is that SSO efficiency does not require perpetual employer access—just coordinated permission pulses—making autonomy structurally compatible with seamless login.
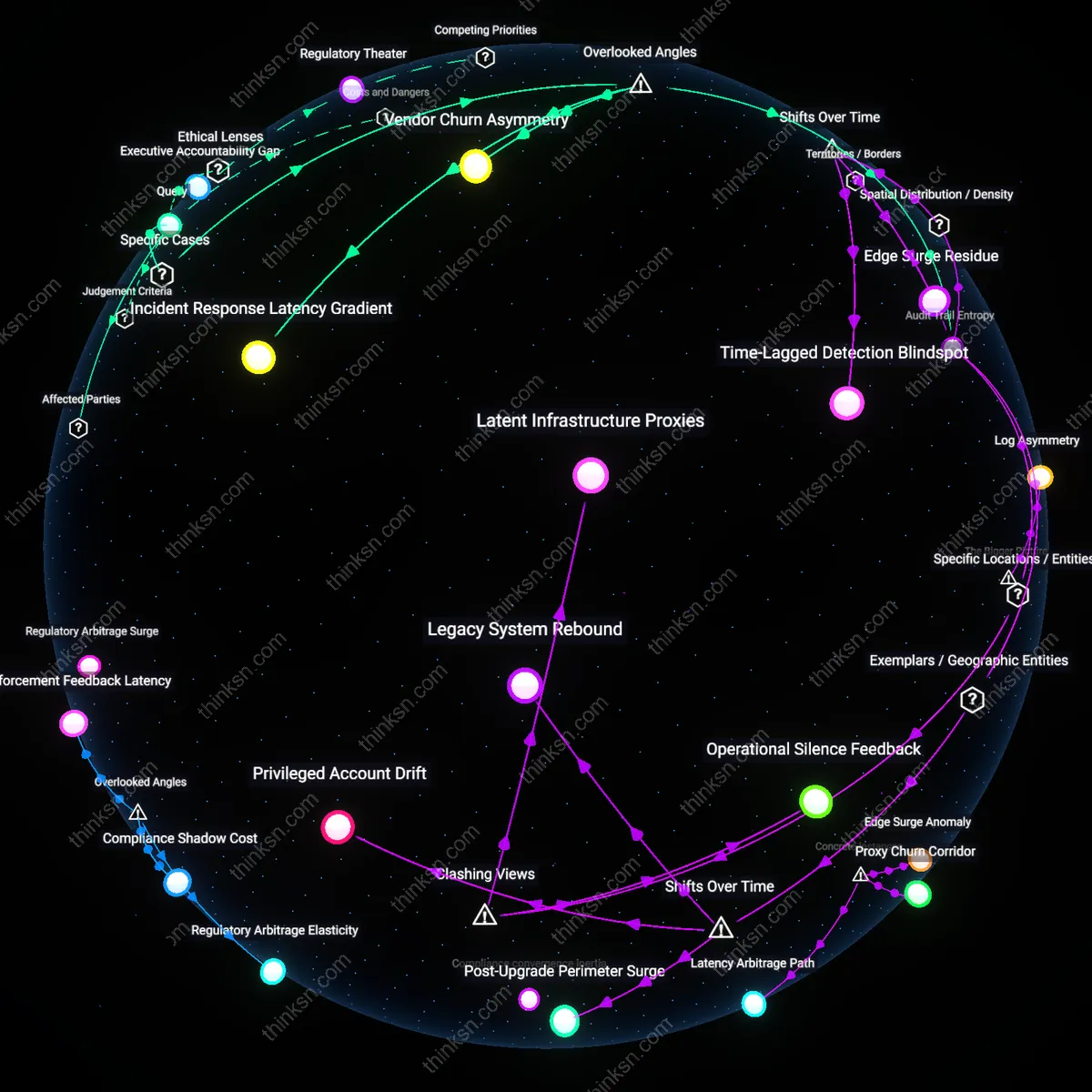
Authentication Entanglement
Employers inherently compromise ethical boundaries when they bundle work access with personal digital identity through SSO, as when Google Workspace or Microsoft 365 become both professional portals and de facto personal accounts. This convergence creates structural dependency, where employees cannot exit employment without identity disruption, mirroring public concerns about tech monopolies. The underappreciated risk is not data misuse per se, but the coercive continuity enforced by embedded credential ecosystems.
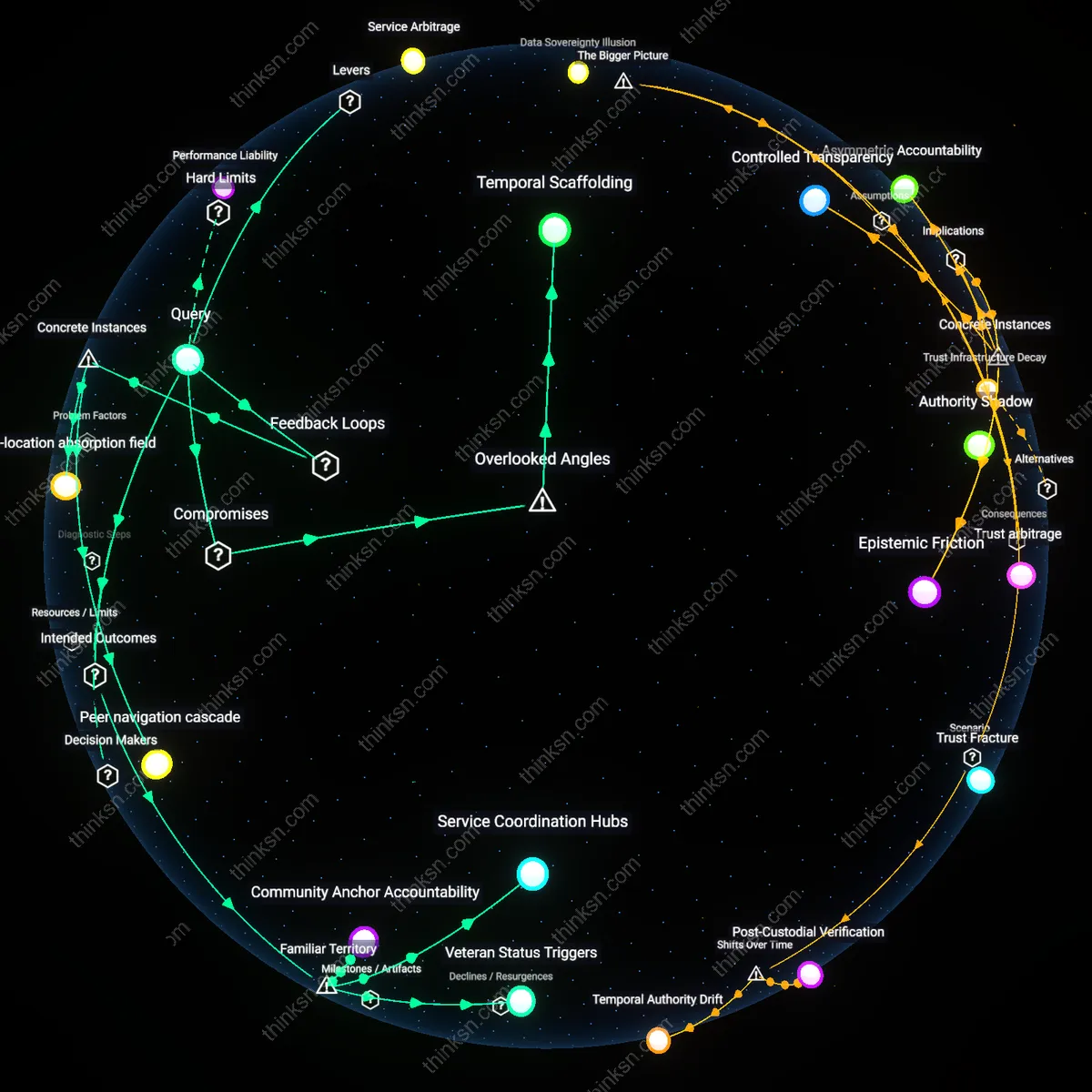
Credential Sovereignty
Organizations can decouple authentication ownership by adopting decentralized identity frameworks, such as blockchain-based verifiable credentials, where employees hold and present proof of affiliation without exposing raw identity data. This operates through standards like W3C DID, enabling employers to verify access rights without storing credentials—a break from centralized directories like Active Directory. The overlooked shift is that efficiency no longer demands data custody; it can emerge from trustless verification.
Authentication Sovereignty
Professionals gain ethical leverage when single-sign-on systems are structured to allow employee-controlled revocation of data-sharing permissions with employers, because this shifts the balance of digital identity from organizational dominance to individual agency. This mechanism operates through granular, user-managed consent layers in federated identity protocols like OIDC, where employees—not just IT admins—can audit and terminate access to specific service integrations. What’s overlooked is that SSO does not inherently centralize control in employers; its architecture can embed decentralized exit rights, transforming authentication from a surveillance tool into a negotiated, dynamic boundary—a shift few governance frameworks consider when assessing workplace data ethics.
Credential Portability
When professionals can carry verified authentication histories across employers via portable digital credentials in SSO ecosystems, they accumulate long-term reputational capital independent of any single organization. This functions through blockchain-anchored, verifiable credentials issued within enterprise identity providers that remain under employee custody, allowing secure, selective disclosure in future roles. The underappreciated dynamic is that SSO systems, typically seen as lock-in mechanisms, could instead become infrastructures for labor market liquidity—enabling professionals to build persistent, trustable digital identities that reduce onboarding friction and elevate negotiation power, a structural possibility rarely modeled in HR technology ethics debates.
Inter-Organizational Trust Arbitrage
Professionals benefit ethically when SSO platforms enable cross-employer identity verification without full data disclosure, leveraging zero-knowledge proofs to let third parties confirm attributes like employment history or skill certifications without exposing raw data. This works through decentralized identity networks such as Sovrin or Microsoft ION, where professionals serve as identity hubs across multiple organizational relationships. The overlooked dimension is that SSO can function not just as an intra-organizational control system but as a trust-minimized coordination layer between competing firms—reconfiguring employer data dominance into a competitive marketplace for verifiable credentials, thereby reducing information asymmetry in professional mobility.
Authentication Overreach
Professionals cannot ethically reconcile single-sign-on systems with employer-controlled authentication because centralized identity management enables covert behavioral surveillance under the guise of access efficiency. IT departments deploy SSO not merely to streamline logins but to instrument employee digital activity across platforms, converting authentication into a persistent tracking infrastructure that persists beyond work hours when personal devices are enrolled. This transforms login events into data points for productivity scoring, creating a feedback loop where access rights are implicitly tied to behavioral compliance, a mechanism rarely disclosed in onboarding. The non-obvious consequence is that SSO ceases to be a neutral tool and instead becomes an operational arm of workplace discipline—something that undermines the assumed neutrality of technical convenience by embedding governance within the architecture of access itself.
Credential Asymmetry
The reconciliation fails structurally because employers hold unilateral revocation power over SSO credentials, rendering employee access contingent and existentially precarious regardless of contractual terms. When a single identity provider governs entry to email, project management, and communication tools, termination of access—even if procedurally justified—erases an employee’s digital presence instantaneously, including personal records, testimonials, and professional networks accumulated during employment. This asymmetry is masked by framing SSO as a mutual efficiency, but in practice it centralizes power over professional identity in the employer’s IT policies, which are neither transparent nor appealable. The underappreciated reality is that SSO doesn’t just manage access—it instantiates a form of digital disenfranchisement, where the termination of a login equates to the erasure of professional continuity, exposing a power imbalance that technical safeguards cannot neutralize.
Audit Inflation
Following the 2020 SEC guidance on cybersecurity disclosures and the rise of zero-trust models at firms like JPMorgan Chase, single-sign-on systems evolved from convenience tools into continuous surveillance infrastructures, where every login becomes a compliance artifact. The change over time—from authentication as access gate to authentication as audit log—means that SSO no longer merely grants entry but accumulates evidentiary data used in internal investigations, performance monitoring, and regulatory reporting, with Okta and Azure AD logs now treated as legal records. This transformation renders employee authentication data not just controlled by employers but structurally overproduced, revealing how efficiency gains were achieved not by streamlining identity but by inflating its evidentiary value, making disentanglement ethically and technically impossible post-adoption.