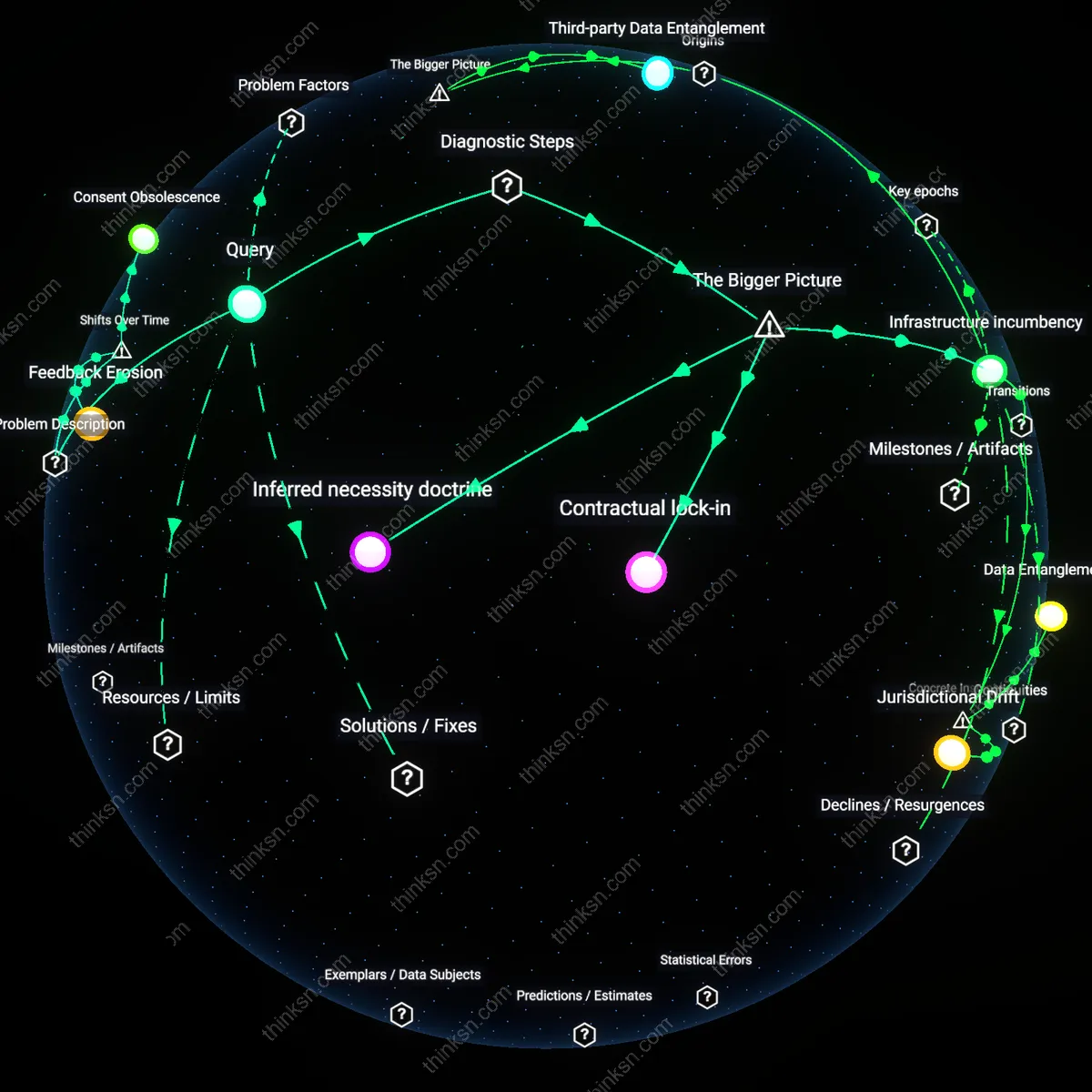
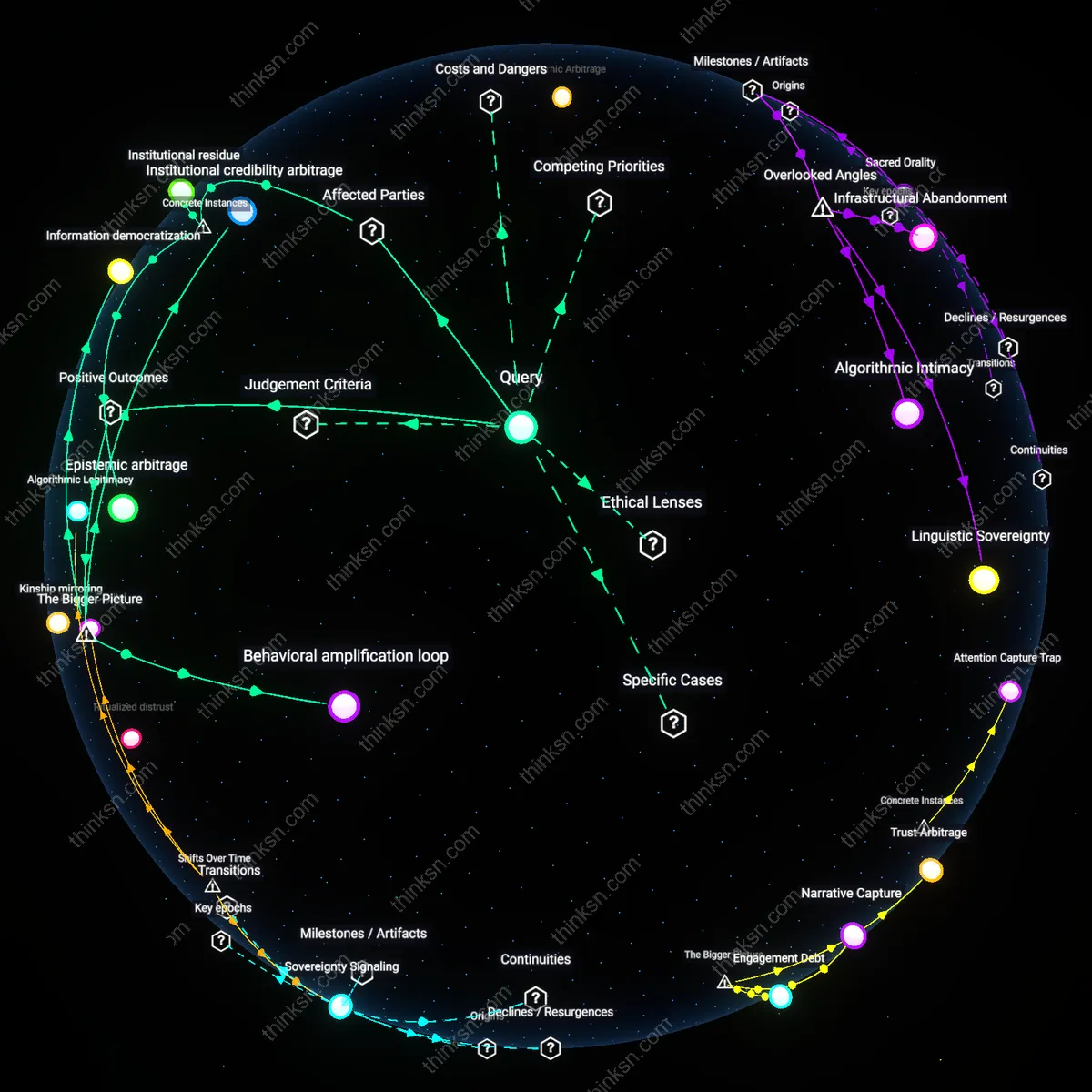
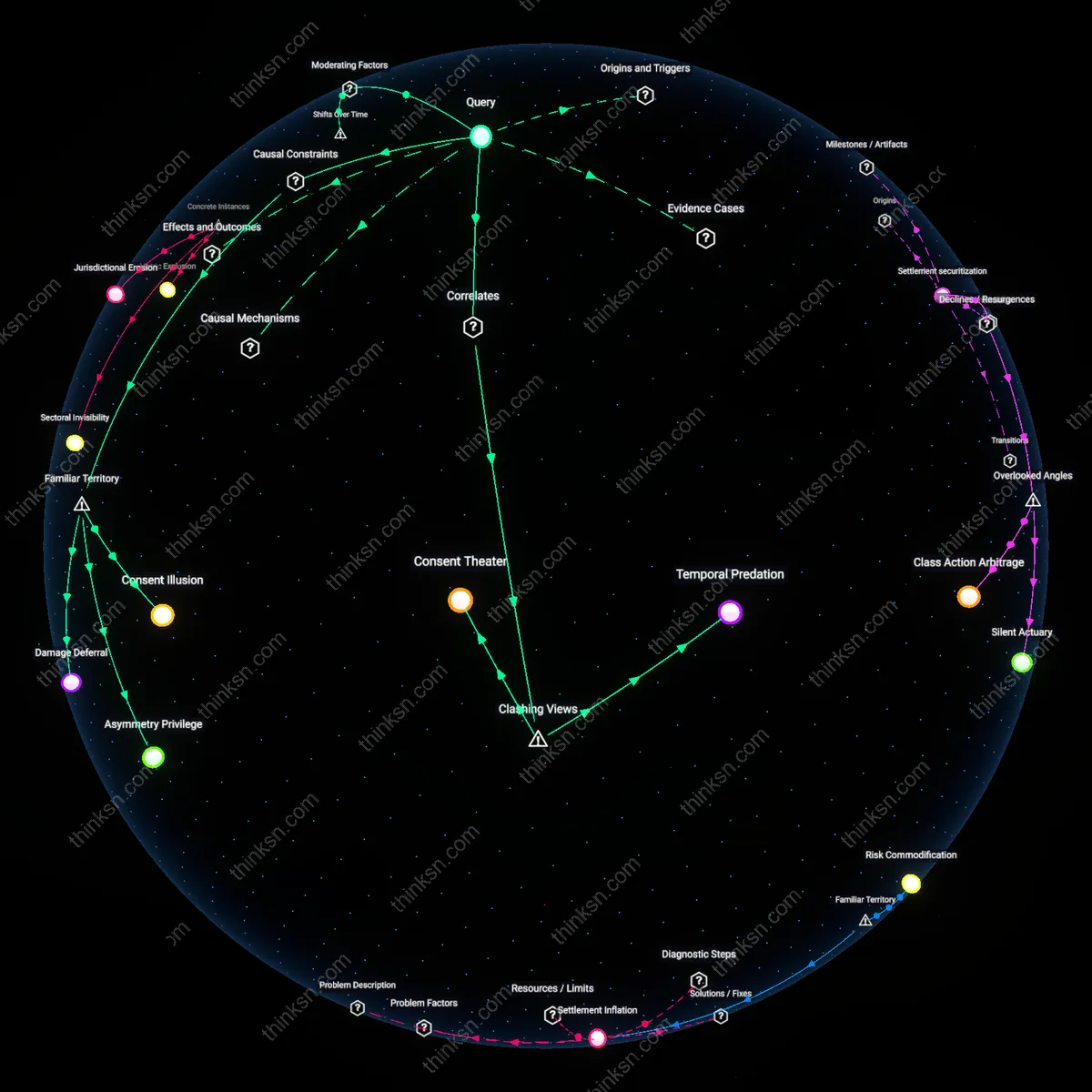
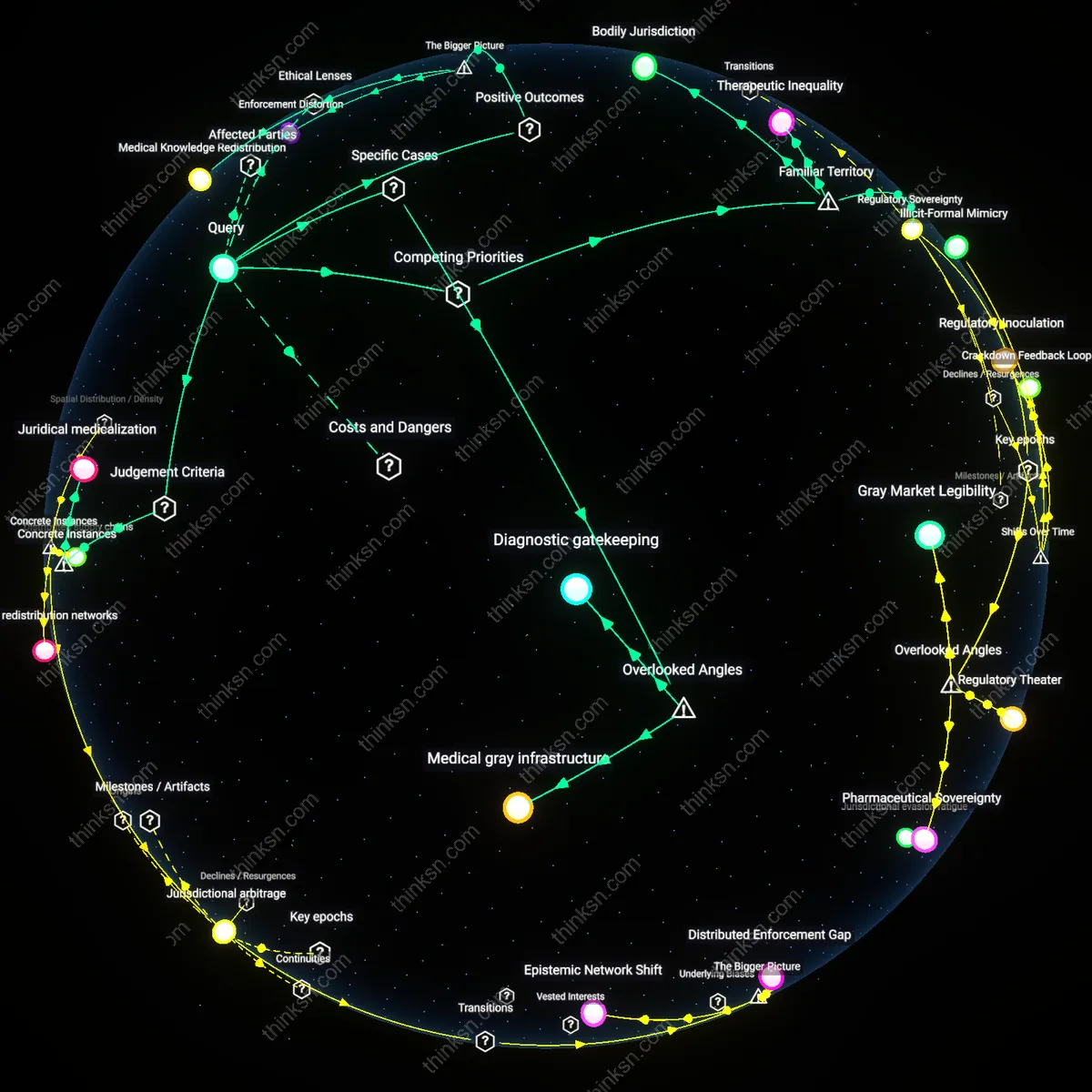
Revoking Health Data Consent in a Hybrid Cloud World?
Analysis reveals 6 key thematic connections.
Key Findings
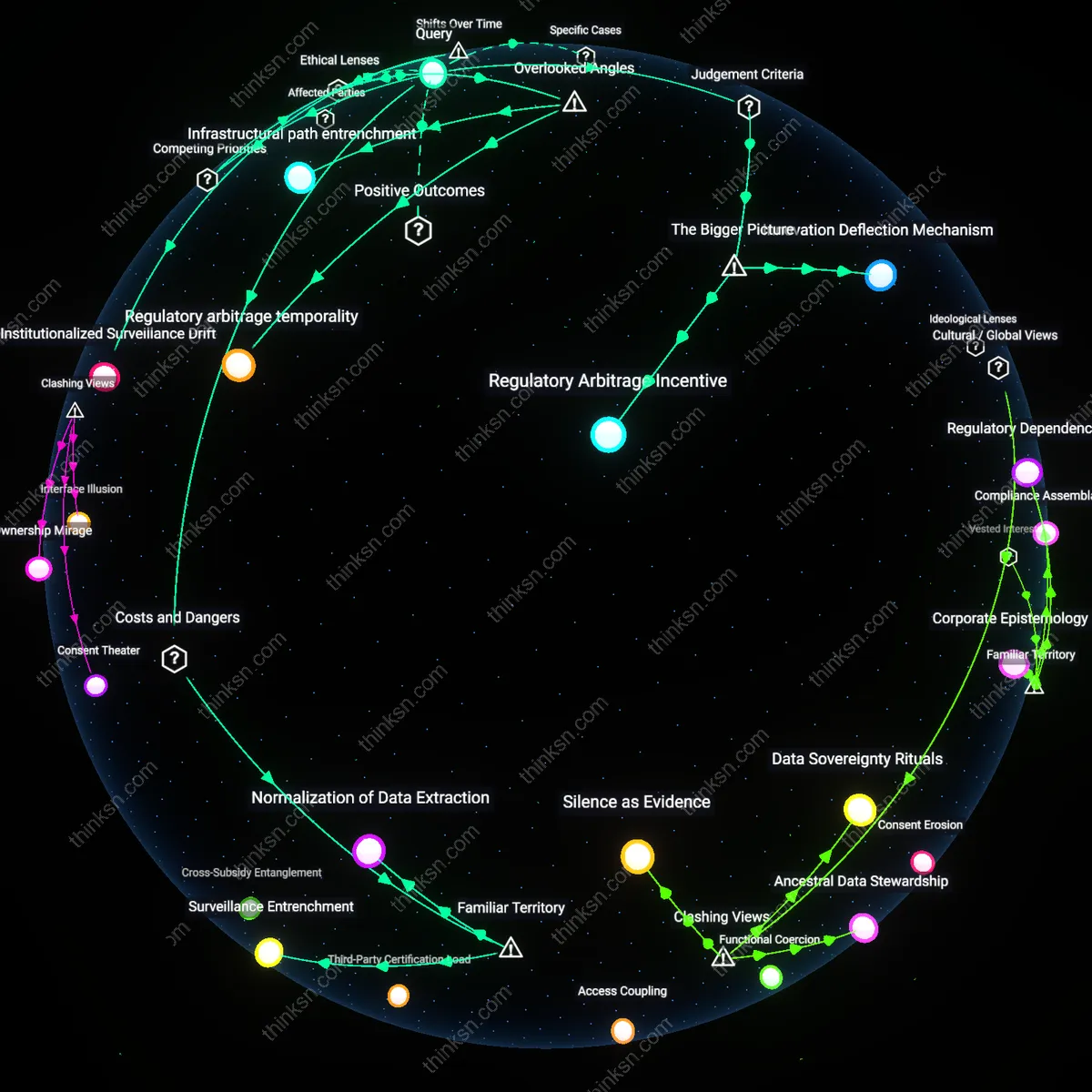
Consent Obsolescence
Individuals cannot realistically revoke consent for health-data sharing because the interoperability standards adopted post-2015—driven by public-private partnerships like those between the U.S. Office of the National Coordinator and Amazon Web Services—prioritized data liquidity over revocability, embedding irreversible data shadows in cloud architectures. Once health data is processed under Fast Healthcare Interoperability Resources (FHIR) standards and dispersed across distributed cloud nodes, the technical capacity to fully retract consent is undermined by replication, caching, and analytical derivatives that persist beyond source deletion. This shift from localized, siloed health records pre-2010 to continuous data flows in hybrid infrastructures has rendered revocation functionally obsolete, not due to policy failure alone, but because the dominant technical paradigm no longer recognizes a user-centric boundary for withdrawal.
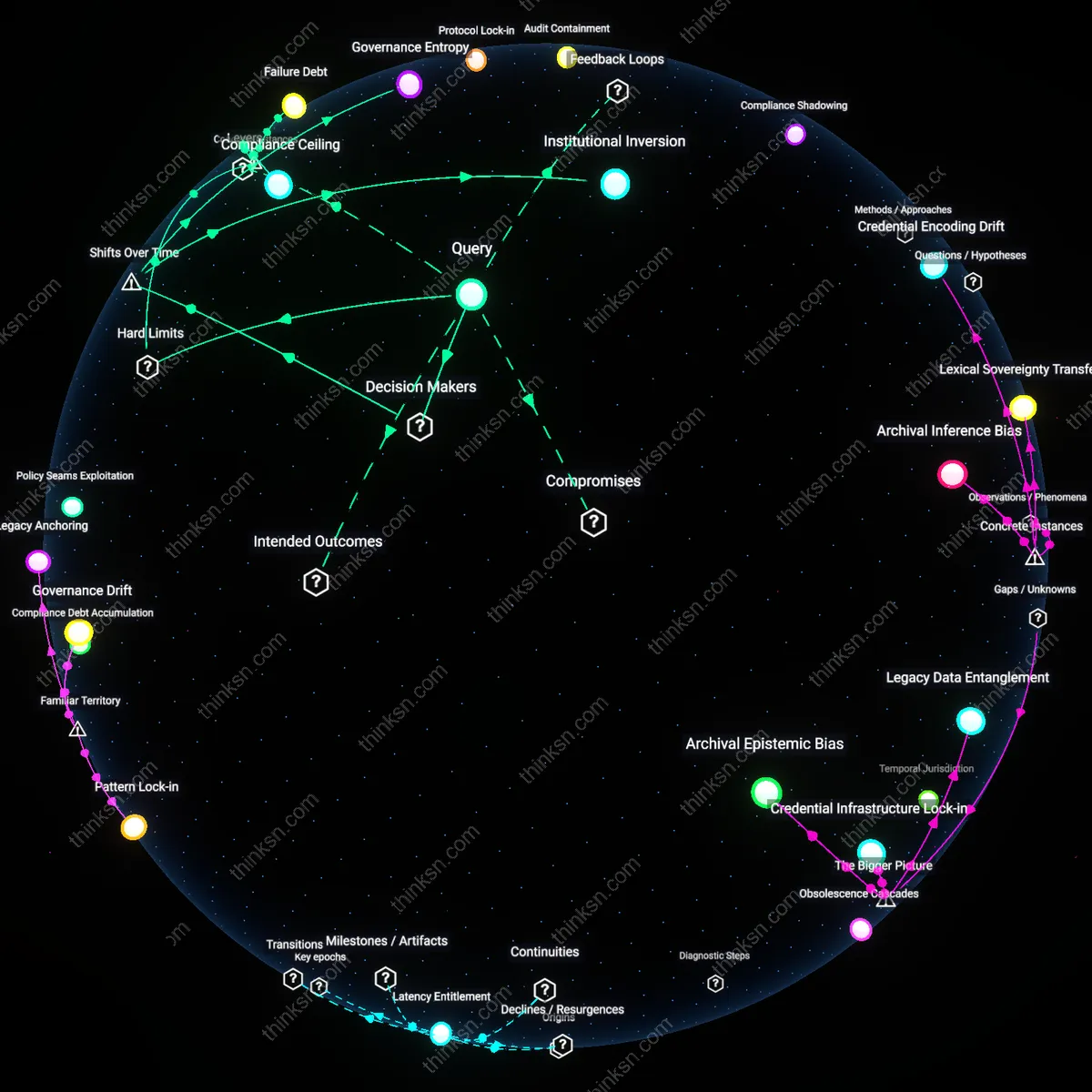
Contractual Lock-in
Revocation of consent has become practically unenforceable because the post-2018 migration of public health agencies to enterprise cloud agreements—such as the CDC’s contracts with Microsoft Azure—established data stewardship as a function of commercial terms, not patient autonomy, thereby subordinating individual rights to multi-year service-level agreements. These contracts often define data as jointly managed or agency-owned once ingested, allowing continuous secondary use for surveillance or AI training even if individuals withdraw consent, because the legal obligations run between institutions, not individuals. The shift from governmental custodianship under HIPAA-governed systems to outsourced, contractually mediated governance reveals that the locus of control has moved decisively into procurement law, where revocation lacks standing.
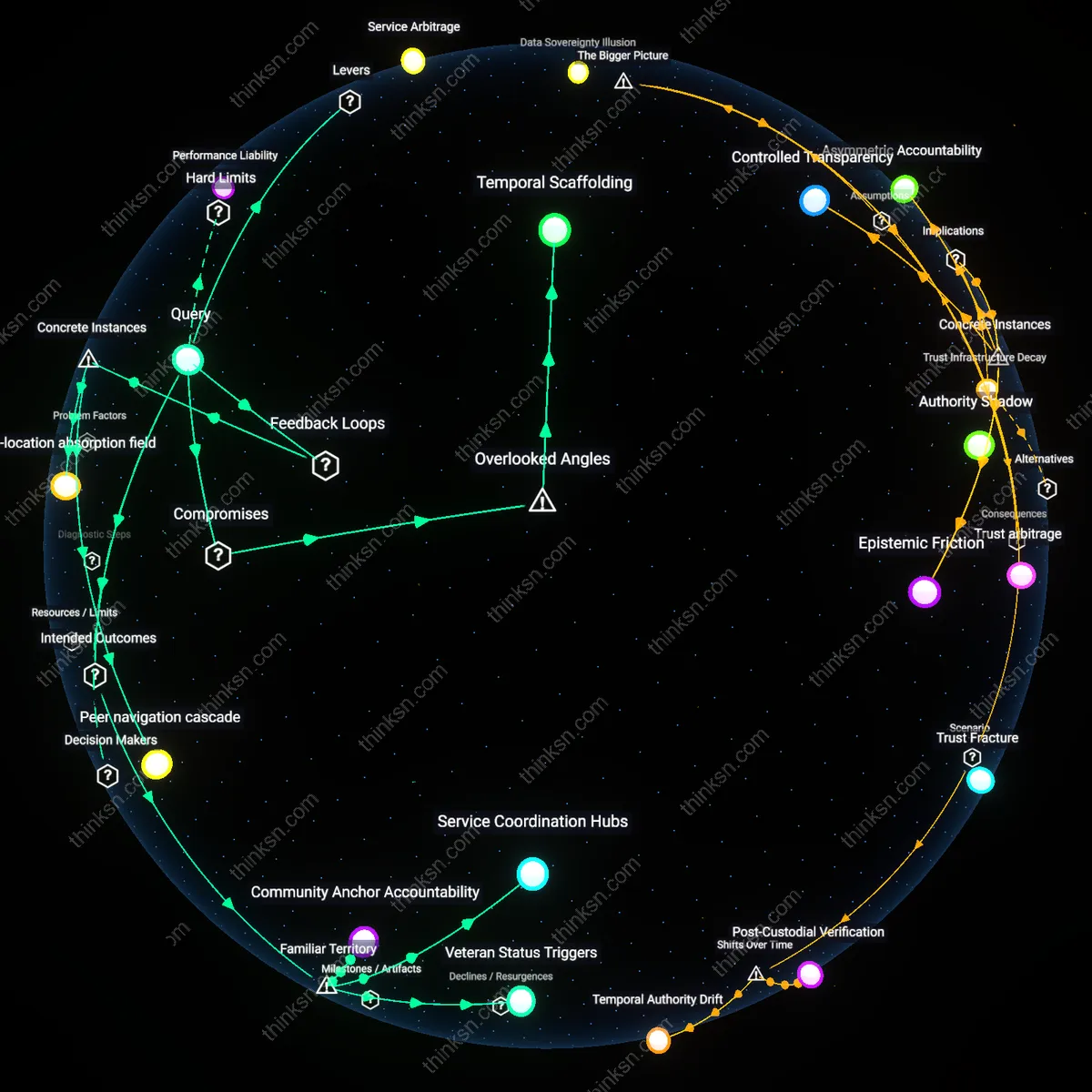
Feedback Erosion
Individuals face diminishing returns on consent revocation because the expansion of real-time epidemiological platforms since the 2020 pandemic—such as the CDC’s Data Modernization Initiative integrated with Google Cloud’s analytics pipelines—has normalized irreversible data assimilation into predictive feedback loops that no longer require identifiable inputs to retain value. Even if a person withdraws consent, their data's prior inclusion has already altered population baselines, algorithmic weights, and risk scores, making exclusion retroactively meaningless within models that treat data as cumulative and self-reinforcing. This shift from episodic, transactional data use to continuous adaptive systems erodes the epistemic relevance of revocation, transforming consent from a control mechanism into a ceremonial entry point.
Contractual lock-in
Individuals cannot realistically revoke consent for health-data sharing because cloud service agreements between public health agencies and private providers like AWS or Microsoft Azure often embed data usage rights in non-negotiable contractual terms that operate independently of patient consent. These contracts typically allow continued processing for '(operational continuity, security, or compliance)' even after individual withdrawal, enforced through binding operational practices rather than privacy policies. This creates a structural override where legal agreements between institutions preempt individual rights, a mechanism obscured by public-facing consent interfaces that suggest revocation is functional. The non-obvious core is that revocation fails not due to technical limits or user apathy, but because private contractual governance displaces public accountability in hybrid infrastructures.
Inferred necessity doctrine
Consent revocation is realistically unenforceable because public health authorities in systems like the U.S. CDC or UK NHS legitimize ongoing data use through an informal doctrine of 'inferred necessity'—where data collected for epidemic surveillance or risk modeling is treated as irrevocably required once aggregated, regardless of individual withdrawal. This doctrine operates through risk governance frameworks that prioritize population-level outcomes over personal autonomy, enabling agencies to bypass revocation by reclassifying data as 'essential public good' after initial collection. The systemic pivot occurs when public health epistemology absorbs private cloud scalability, making retraction appear technically disruptive and socially irresponsible. The underappreciated dynamic is that the moral authority of public health becomes a justificatory filter that neutralizes individual agency post-collection.
Infrastructure incumbency
Revocation fails in practice because the integration of health data into privatized cloud infrastructure—such as Google Cloud-hosted NHS databases or Epic Systems' federated networks—creates path dependency where data cannot be logically or physically isolated once processed across distributed nodes. Cloud architectures are designed for data immutability and replication, meaning that 'deletion' or 'withdrawal' cannot be authenticated across backup, caching, and machine learning inference layers managed by private vendors. The real barrier is not policy ambiguity but infrastructural non-reversibility, enforced by the technical logic of cloud platforms optimized for retention and scale, not granular user control. The overlooked reality is that cloud engineering standards have become de facto data governance regimes, making revocation a ceremonial gesture rather than an operational outcome.