Do Decentralized Blockchains Really Shift Power from State Surveillance?
Analysis reveals 8 key thematic connections.
Key Findings
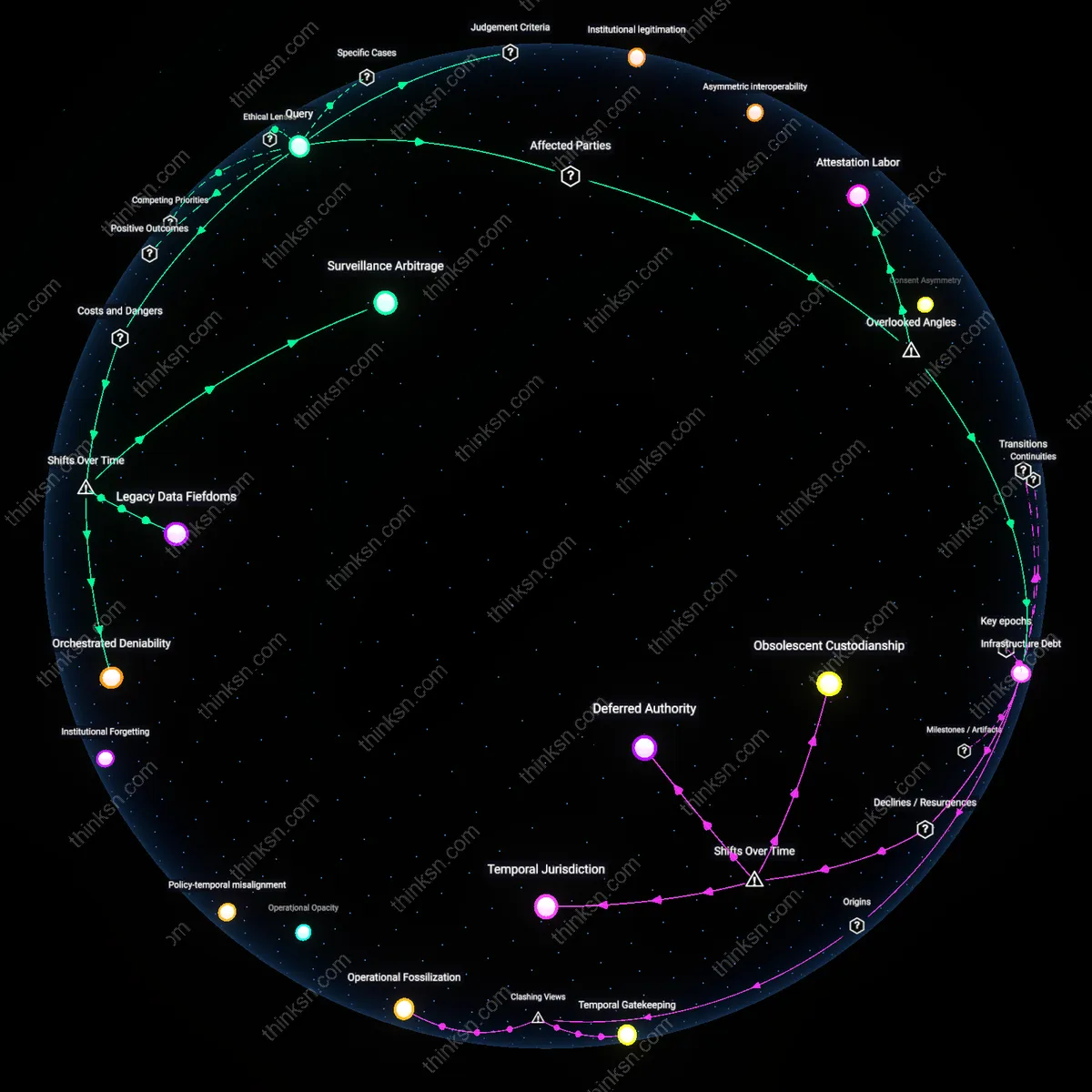
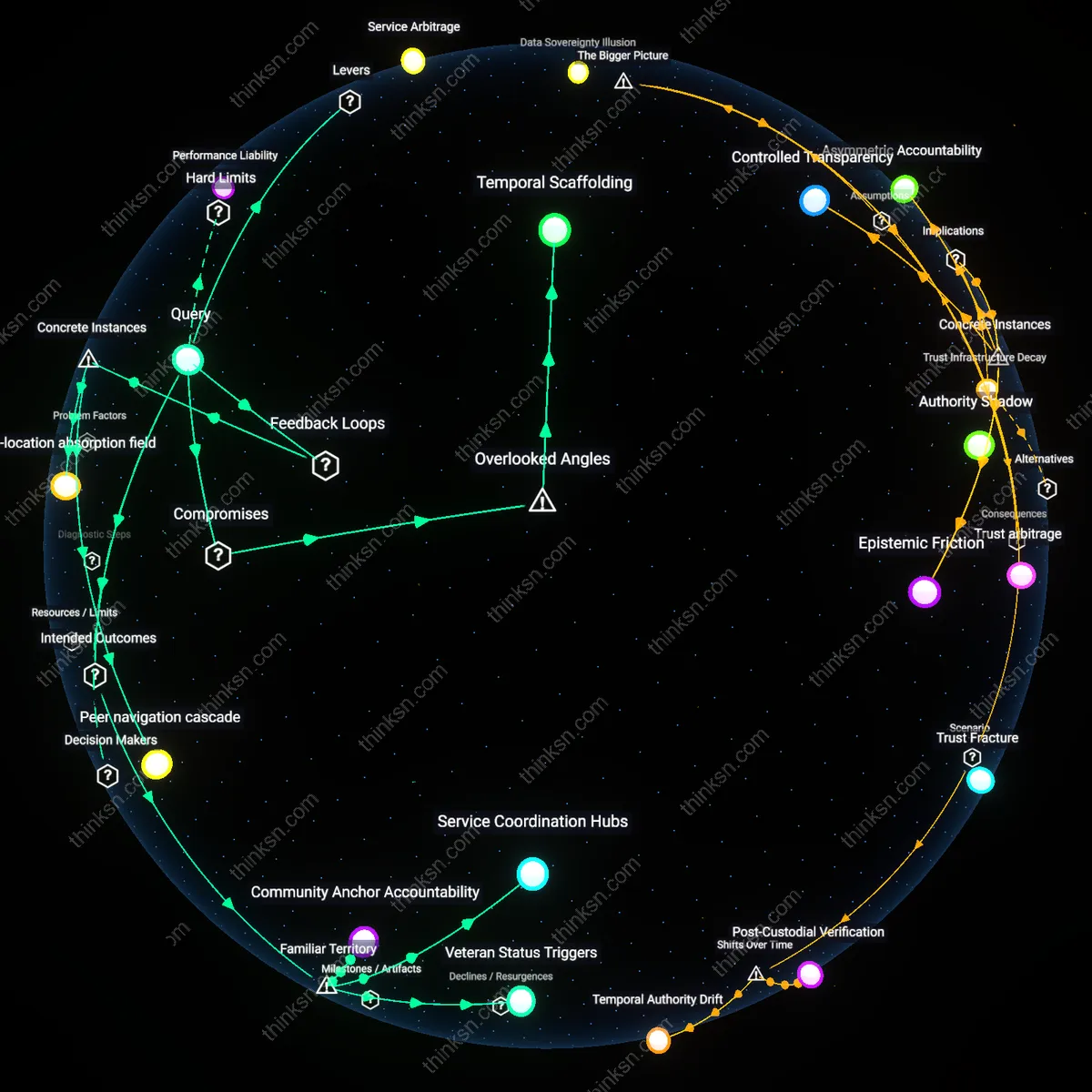
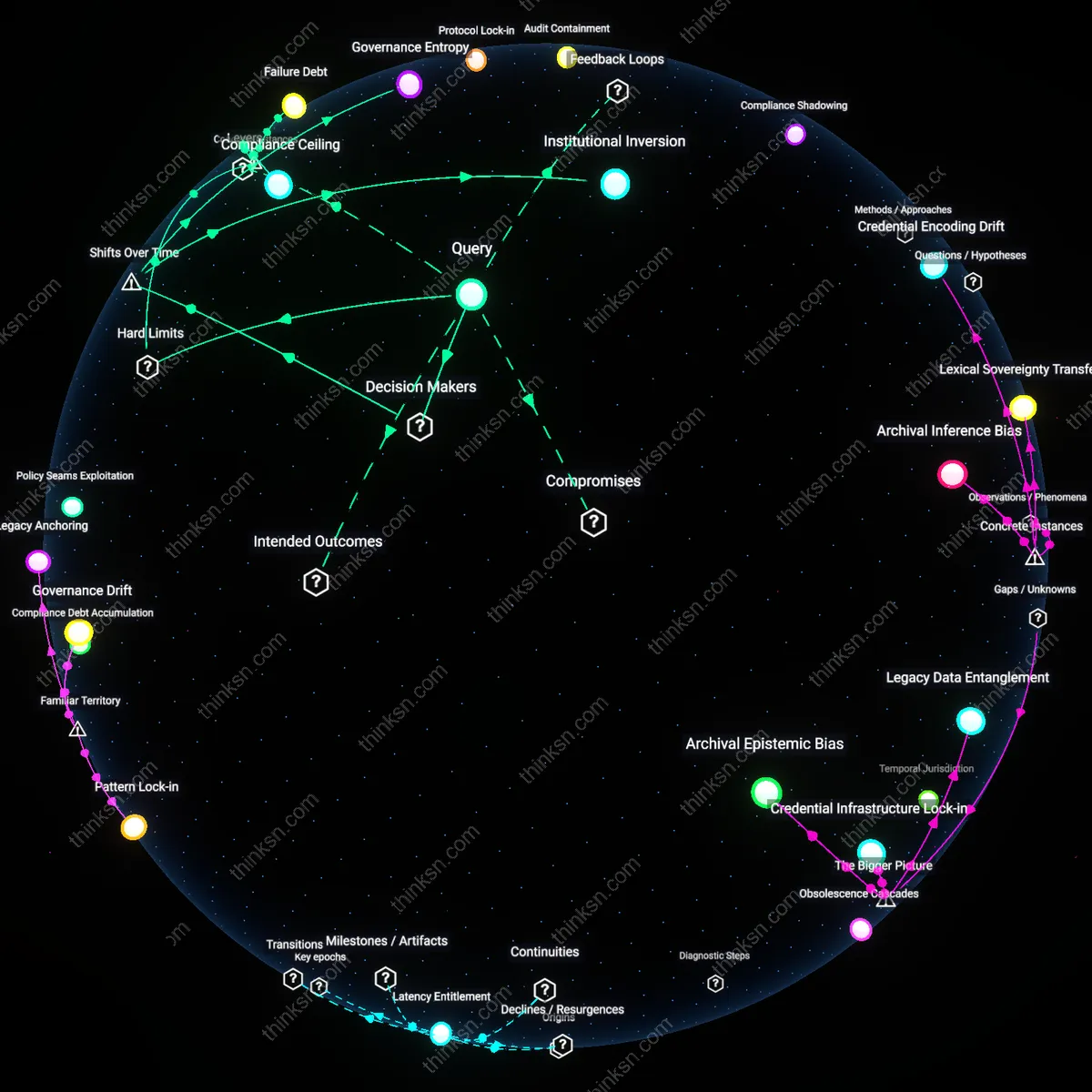
Infrastructure Debt
Surveillance power shifts not to new intermediaries but to maintenance collectives managing legacy blockchain infrastructure in post-deployment environments. In Estonia and India, for instance, long-term operation of national digital identity systems relies on semi-formal teams of aging engineers and outsourced maintenance firms who possess irreplaceable tacit knowledge about system quirks and failure modes. These groups gain discreet authority to shape data access pathways during downtime, upgrades, or breaches — a form of quiet control absent from governance frameworks. The overlooked dynamic is that blockchain persistence creates 'infrastructure debt', where operational continuity depends on informal human networks whose influence grows over time, distorting formal accountability structures designed at rollout.
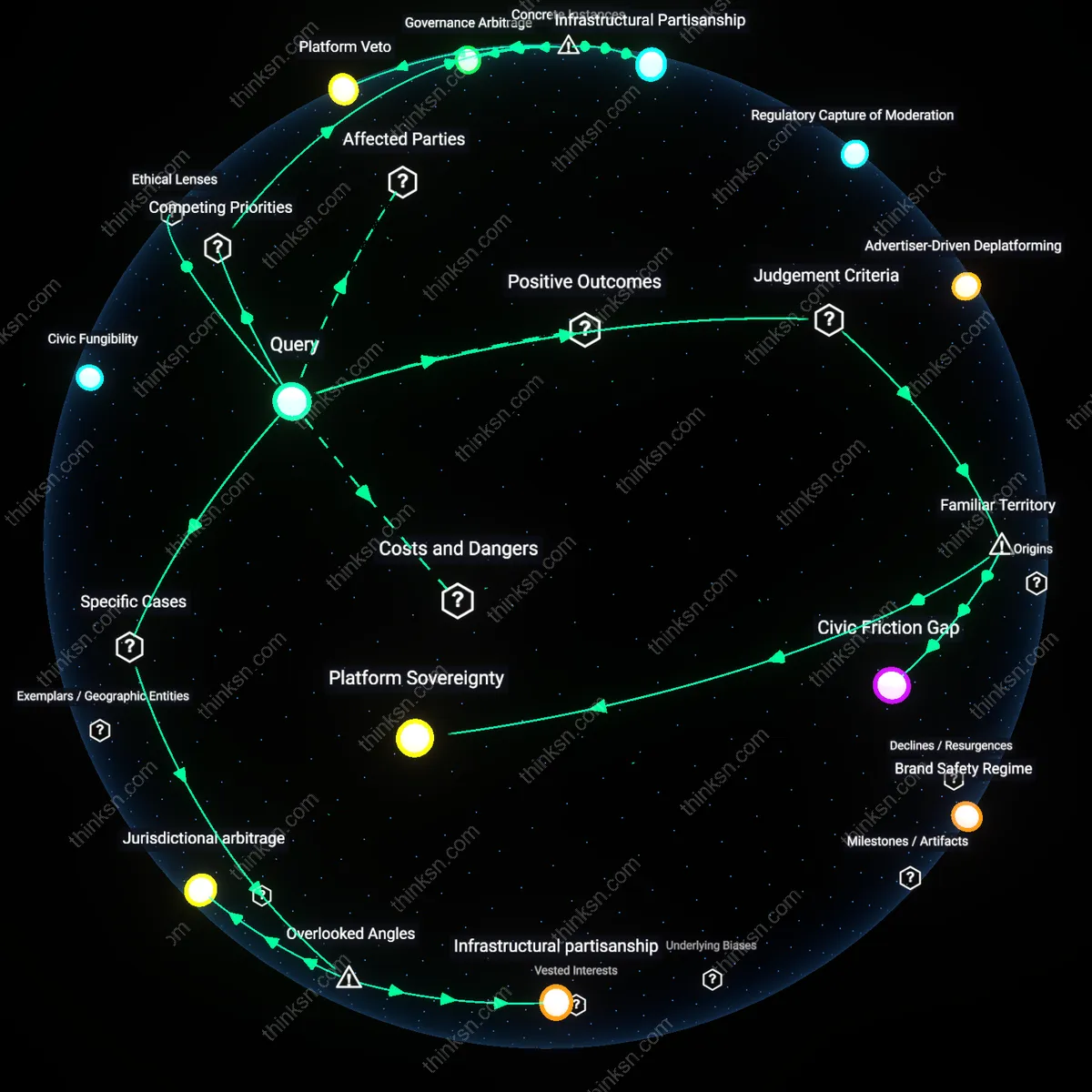
Attestation Labor
The burden of proving one's identity in decentralized systems falls disproportionately on marginalized users who must repeatedly solicit verifiable credentials from scattered institutions, turning identity maintenance into a form of unpaid cognitive and logistical labor. For homeless populations in Berlin or undocumented migrants in Barcelona, acquiring time-stamped attestations from shelters, clinics, or aid groups consumes scarce bandwidth and trust capital, while privileged users auto-renew credentials via employer or bank integrations. The overlooked dimension is that blockchain-based identity doesn't reduce verification work — it redistributes its performance, making the poor responsible for assembling their own surveillance legibility. This repositions compliance as a personal duty rather than a systemic obligation, masking structural exclusion through procedural fairness.
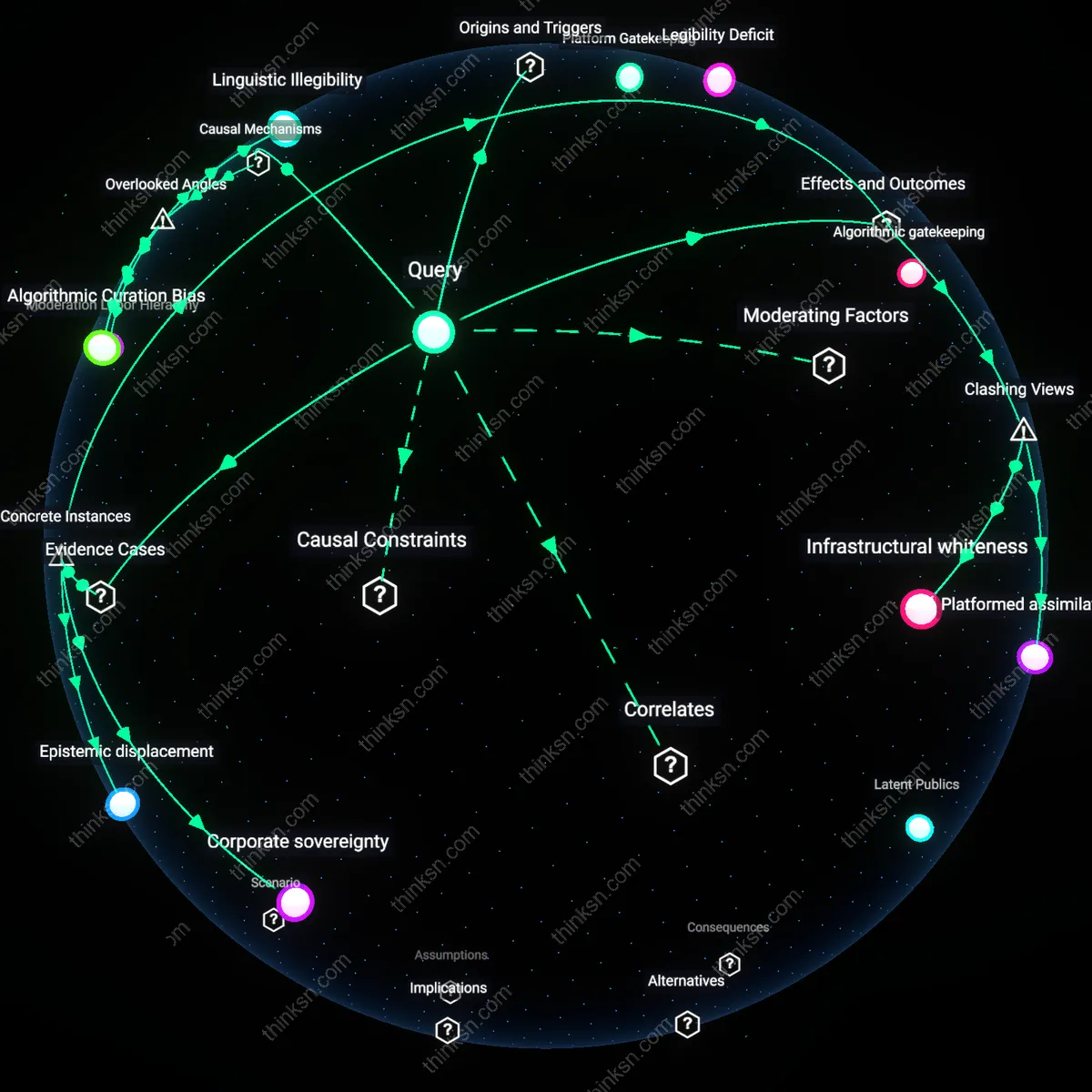
Institutional legitimation
Decentralized identity blockchains in state surveillance do not fairly redistribute power because their adoption functions primarily as a technological legitimation of existing state authority, not its dissolution; states selectively endorse blockchain systems that comply with legal intercept mandates and data retention laws—such as Estonia’s KSI-backed e-Residency program—thereby co-opting decentralization as a tool of digital sovereignty expansion rather than citizen empowerment, revealing that technological architecture alone cannot override institutional path dependency. This mechanism matters because it exposes how the perceived neutrality of cryptographic verification is exploited to reinforce trust in state-backed digital identities, masking continuity of control under the guise of innovation.
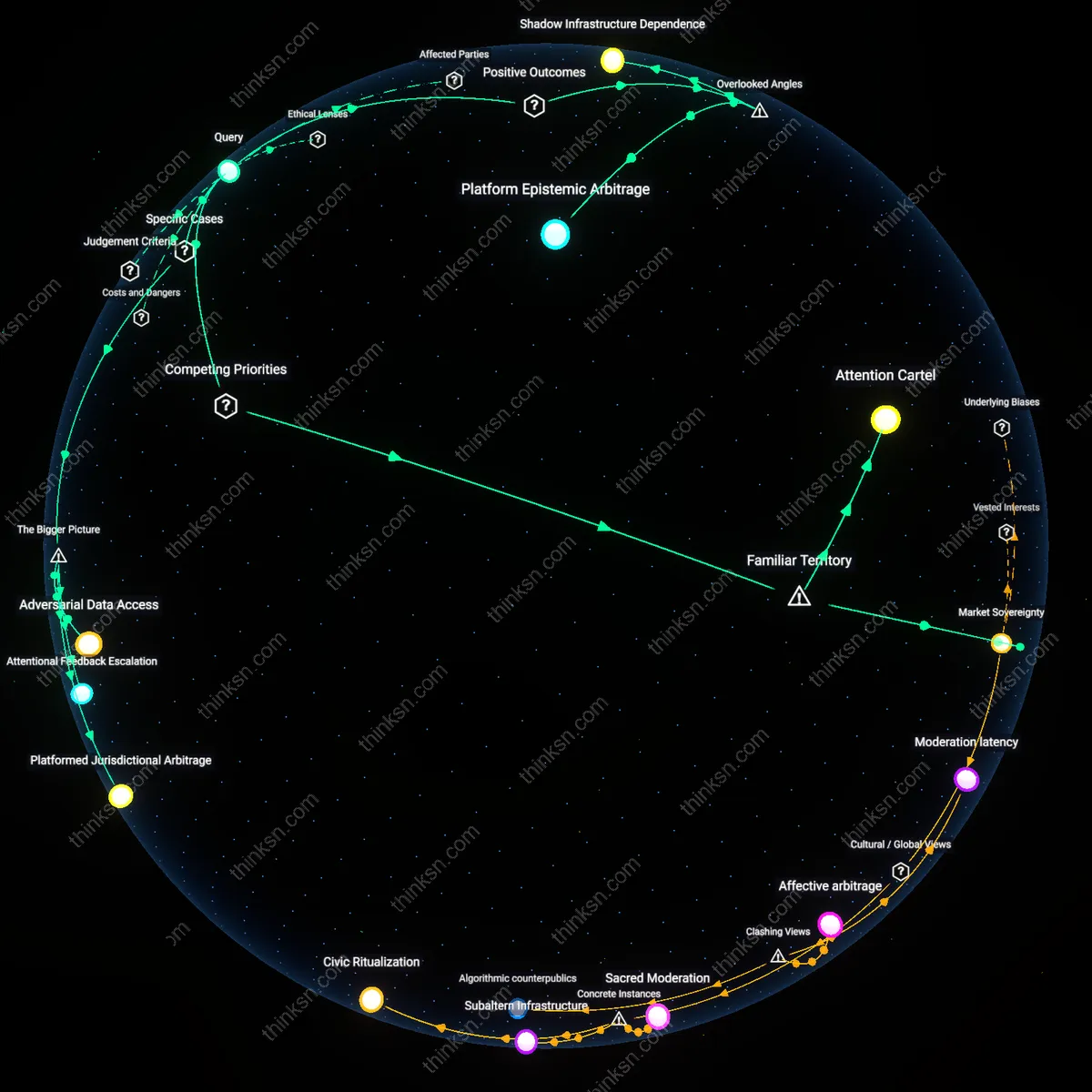
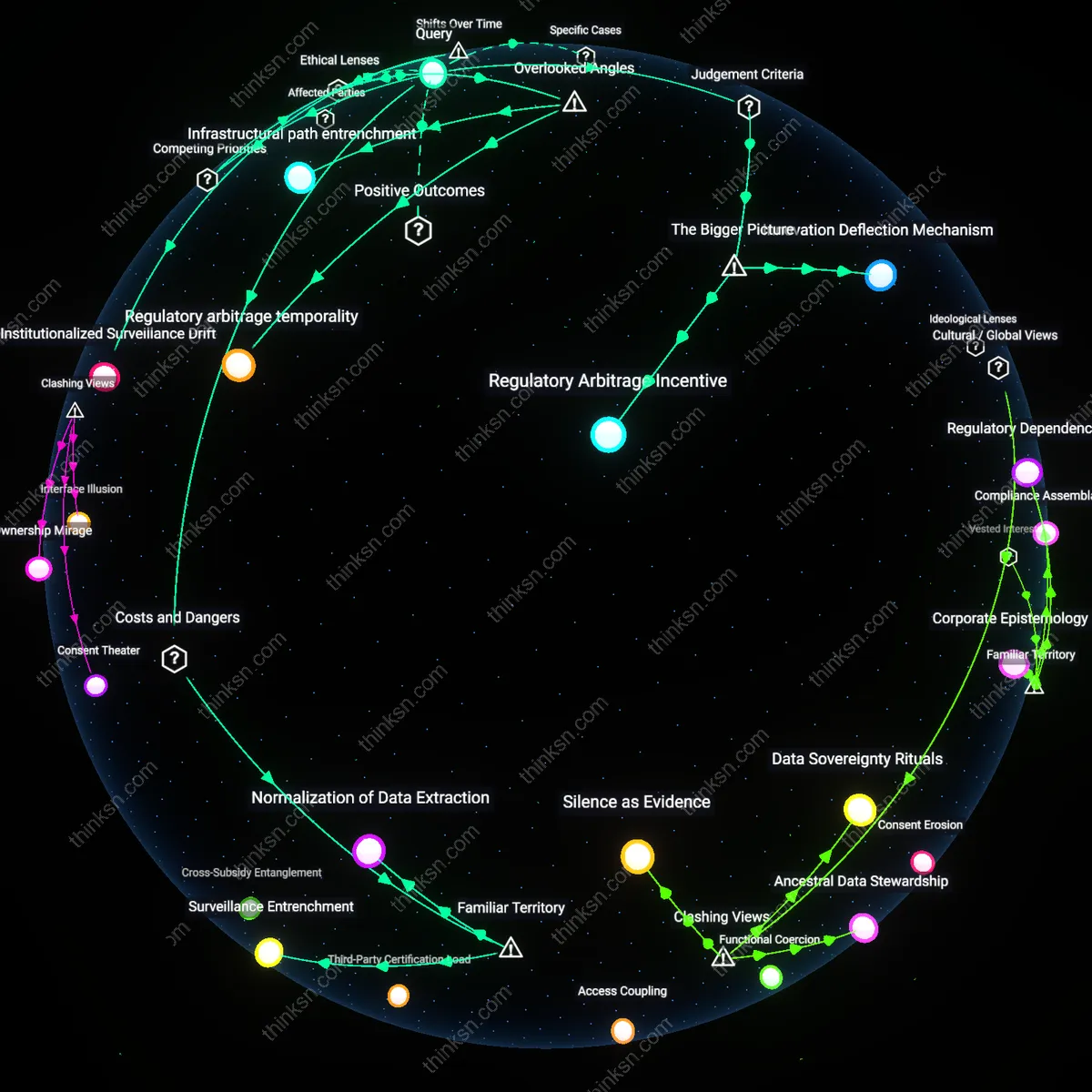
Infrastructural capture
The deployment of decentralized identity blockchains in surveillance contexts transfers power to new technical intermediaries who control critical layers of identity infrastructure, such as node operators, protocol maintainers, and cryptographic standard setters—exemplified by consortia like the Sovrin Network, where governance is concentrated among accredited stewards largely tied to multinational tech firms or NGOs; these actors wield de facto veto power over identity issuance and revocation, creating a new center of gravity for exclusion and access. This shift is significant because it reframes surveillance not as a state monopoly but as a function of modular, permissioned ecosystems where geopolitical influence is re-inscribed through technical governance rather than direct coercion.
Asymmetric interoperability
Using decentralized identity blockchains in state surveillance entrenches power imbalances by enabling selective interoperability—governments can link sovereign identity systems to global blockchain networks while retaining gatekeeping authority over authentication, as seen in India’s proposed integration of Aadhaar-linked verifiable credentials with public blockchains for welfare delivery; private entities and citizens cannot reciprocate this access, making data flows unidirectional and extractive. This dynamic is pivotal because it demonstrates how technical standards, framed as liberatory, become instruments of asymmetry when embedded in contexts of unequal regulatory capacity and digital literacy.
Legacy Data Fiefdoms
Decentralized identity blockchains in state surveillance reconfigure centralized bureaucratic control into privatized data enclaves, where authority shifts not from state to citizen but from one dominant administrative class to another technocratic elite with deeper access to behavioral metadata. The 2008–2015 post-financial-crisis era saw governments outsource identity infrastructure to ‘secure’ private-sector ledgers under the guise of efficiency, transforming state sovereignty into a permissioned network architecture; this moment of transition disguised enclosure as liberation, naturalizing surveillance continuity under new custodians. What was once an opaque but accountable state monopoly over identity records has become a less transparent, interoperable web of technical dependencies where nodes are held by vendors whose code becomes policy—revealing that decentralization does not dissolve power but redistributes its granularity.
Orchestrated Deniability
The integration of blockchain-based identity systems into state surveillance since the mid-2010s enabled states to offload political liability for monitoring populations onto decentralized protocols while retaining ultimate access and influence, thereby institutionalizing plausible deniability as governance strategy. As national digital ID programs like India’s Aadhaar began incorporating blockchain layers around 2016, the shift allowed governments to attribute technical failures, biases, or breaches to ‘neutral’ consensus algorithms rather than policy choices, masking intentional surveillance expansion behind the rhetoric of transparency and trustlessness. This moment of operational abstraction did not reduce control but relocated its visibility, making oversight more difficult by embedding state power in ostensibly autonomous systems—revealing that the blockchain era did not decentralize authority so much as it choreographed evasion of accountability.
Surveillance Arbitrage
From the late 2010s onward, states began exploiting decentralized identity blockchains not to democratize identity but to fragment jurisdictional responsibility across borders and layers, enabling regulatory evasion through deliberate ambiguity about where control actually resides. By adopting multi-chain or cross-chain identity frameworks like Sovrin or Verifiable Credentials, governments outsourced core identity functions to ostensibly global, permissionless networks while maintaining covert bilateral agreements with node operators or protocol foundations—creating a system where compliance is performative and enforcement impossible. This pivot from territorial sovereignty to protocol gaming transformed privacy into a variable cost, where oppressive regimes can now access granular personal data via backdoor interoperability while presenting themselves as compliant with human rights standards—exposing an emerging regime of jurisdictional dissonance masked as innovation.