Is a Unified App Ecosystem Riskier Than Its Benefits?
Analysis reveals 11 key thematic connections.
Key Findings
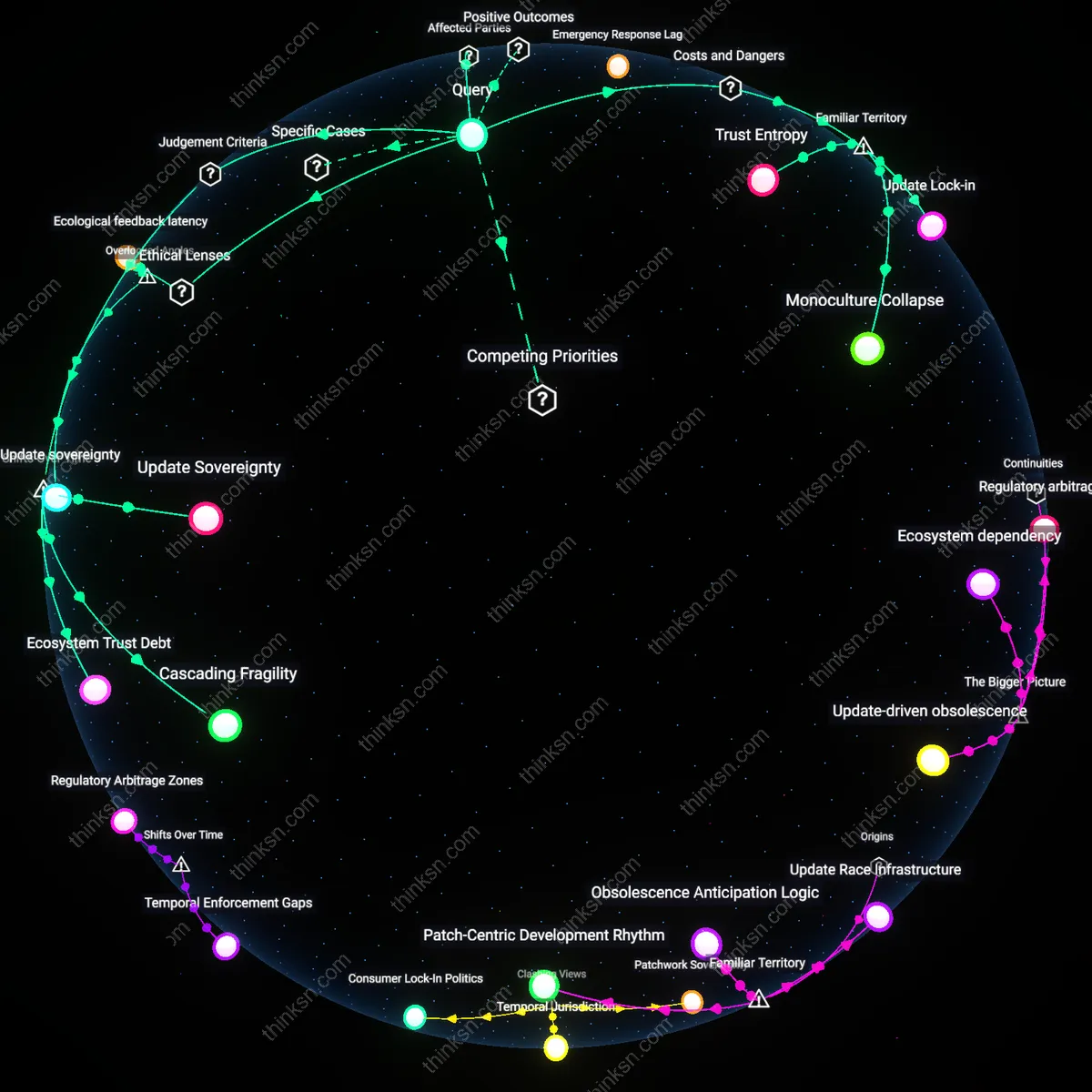
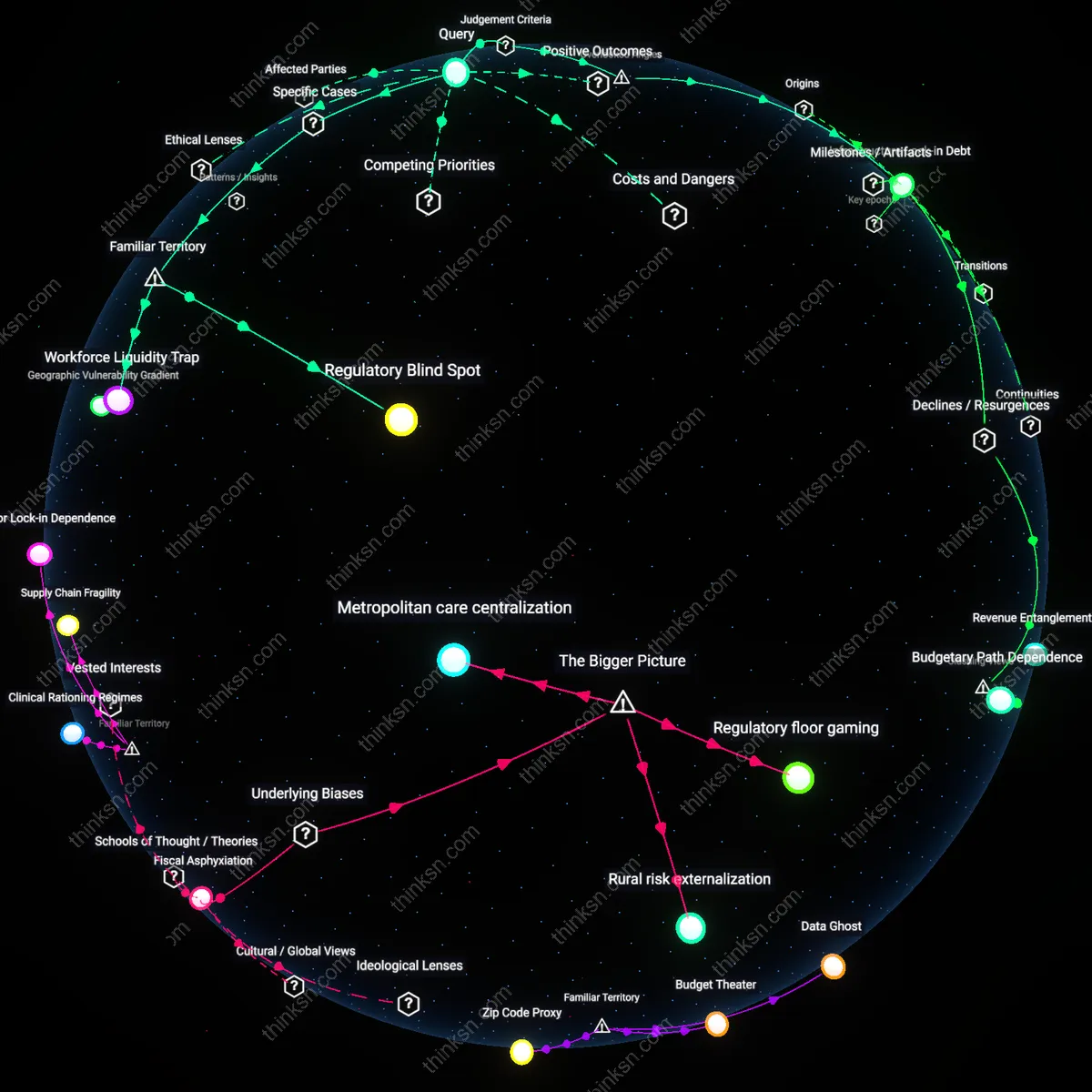
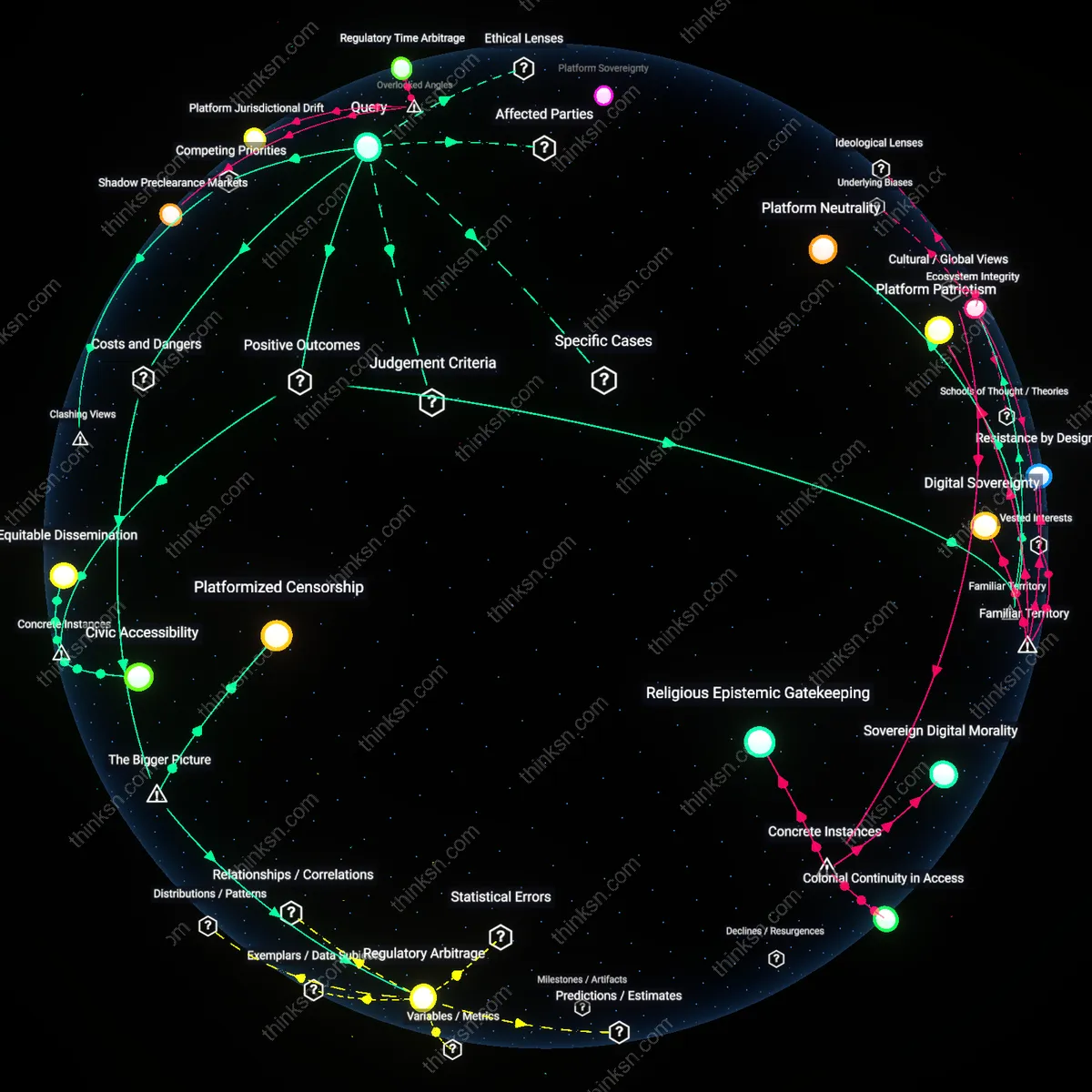
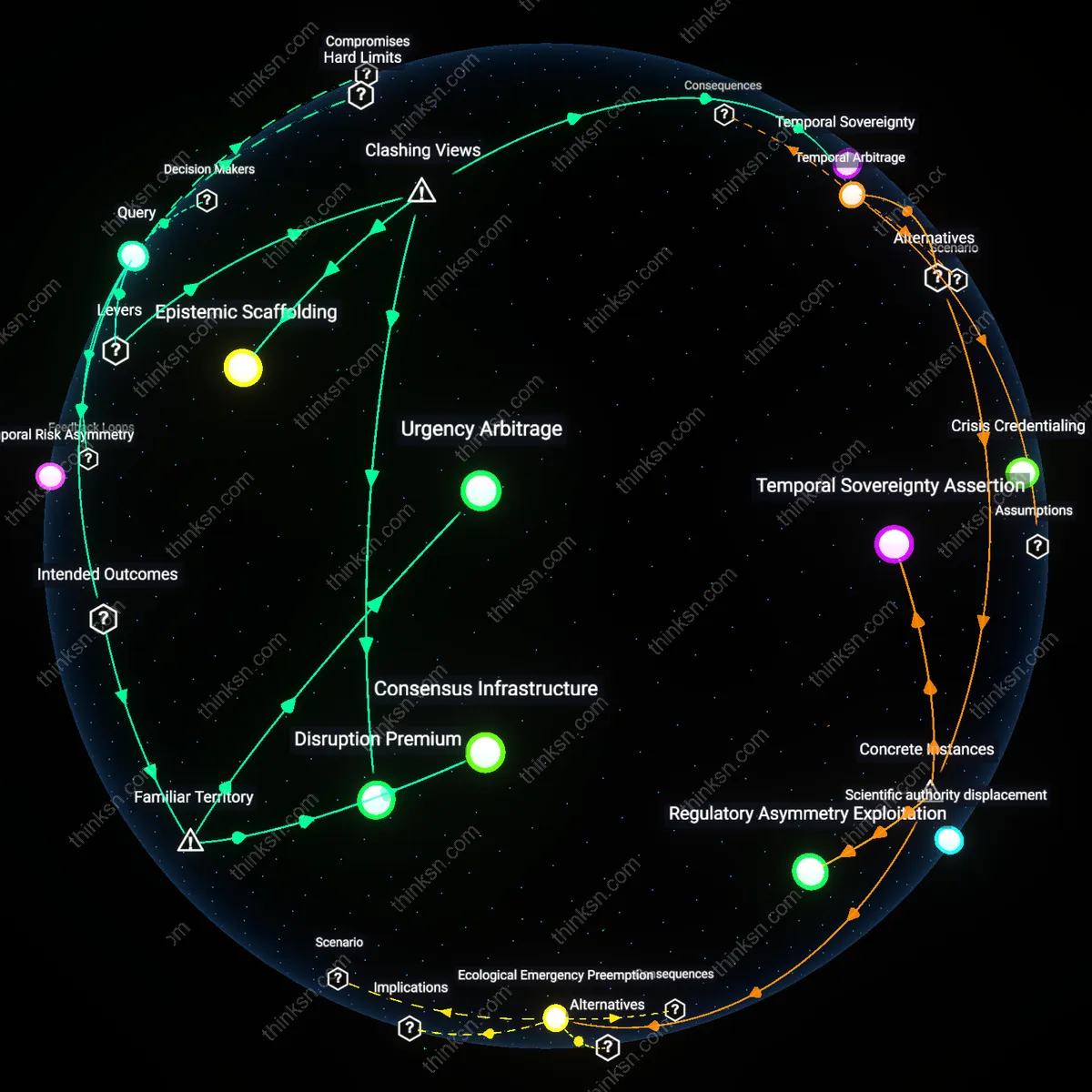
Regulatory Asymmetry
U.S. consumers benefited from Apple’s tightly integrated iOS ecosystem through seamless app interoperability and security, but the 2021 FBI report on the iOS 14.5 update delaying child exploitation detection tools revealed how a single update cycle hindered law enforcement access across state and federal agencies—exposing a critical imbalance where corporate update timelines can override public safety mandates, which is non-obvious because regulatory enforcement assumes technical responsiveness, not dependency on private release schedules.
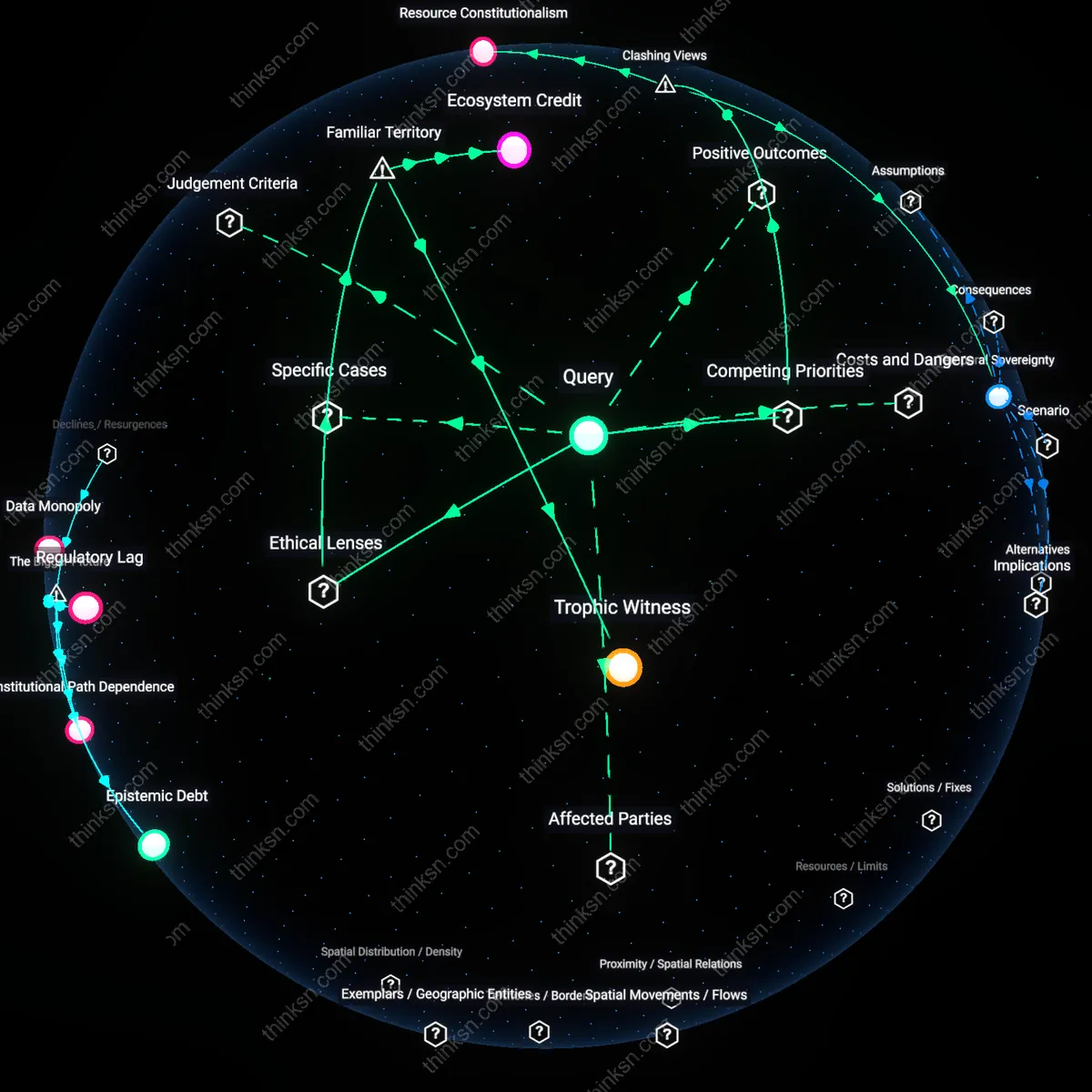
Infrastructural Lock-in
Indian street vendors using the Unified Payments Interface (UPI) via Google Pay faced systemic disruption during the April 2023 out-of-sync update rollout, where patch incompatibilities blocked transaction confirmations for 36 hours—highlighting how marginalized economies become structurally vulnerable when a single app platform mediates essential financial services, a risk that remains underappreciated because digital inclusion initiatives often ignore backend consolidation risks.
Emergency Response Lag
During Japan’s 2019 Typhoon Hagibis, the national warning system pushed emergency alerts through the Y! Alert app, part of Yahoo Japan’s unified ecosystem, but a delayed security patch caused 11% of downstream city-level systems to fail synchronization—demonstrating how centralized update protocols can propagate technical failures into public safety breakdowns, a dynamic rarely accounted for in disaster preparedness planning that assumes app-level reach equals operational reliability.
Update Sovereignty
Consumers gainUpdateSovereignty when app ecosystems shift from fragmented platforms to centralized control structures, as seen after the 2010s consolidation of mobile operating systems; this centralization enables coordinated security patches and feature parity but transfers update authority from users to platform gatekeepers like Apple and Google, who now enforce mandatory updates through proprietary app stores—revealing an underappreciated trade-off where user protection is achieved not through consent but systemic coercion, altering the historical norm of user-managed software maintenance.
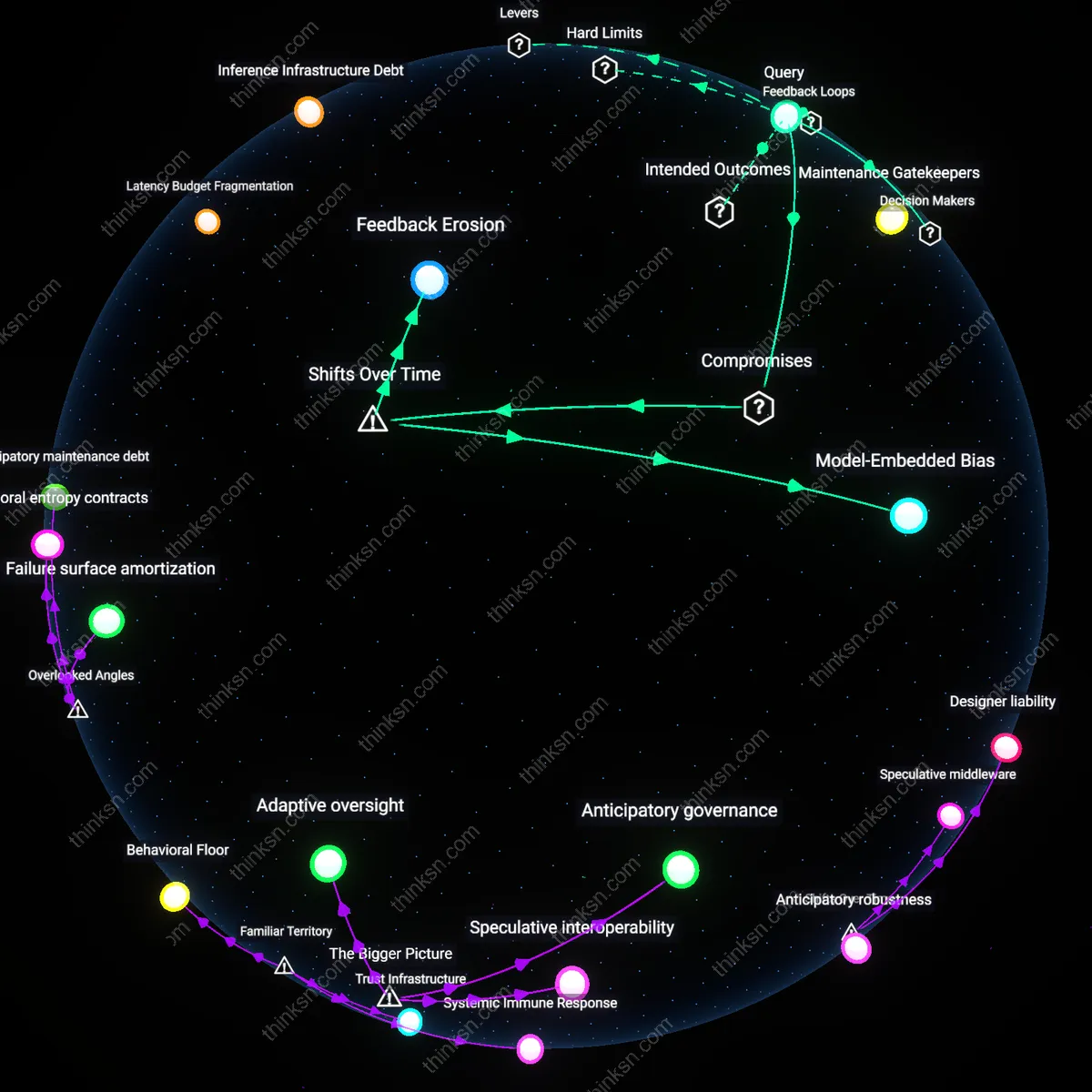
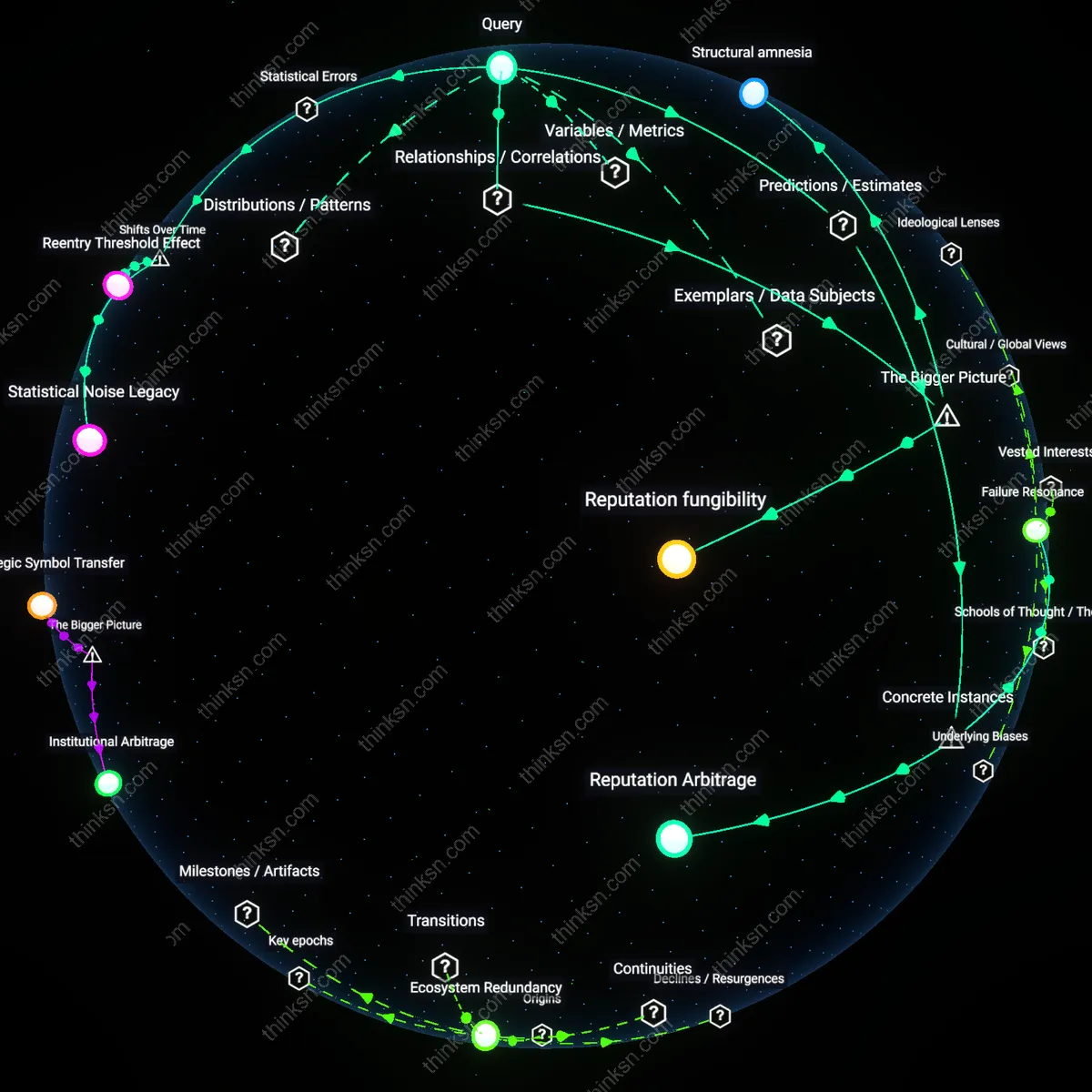
Cascading Fragility
The risk ofCascadingFragility emerged distinctly after the 2021 SolarWinds breach, which demonstrated how centralized update mechanisms—once designed for efficiency—can become systemic hazards; as enterprise and consumer software converged on trusted distribution hubs (e.g., Microsoft Update, Apple SUS), a single compromised binary could propagate globally within hours, transforming what was historically a localized failure mode into a geopolitical vulnerability, exposing that the very architectures optimized for rapid patching now amplify unintended consequences across interdependent infrastructures.
Ecosystem Trust Debt
Platform operators incurEcosystemTrustDebt when they prioritize seamless integration over user agency, a shift accelerated after the transition from open web apps to closed app economies post-2012; by bundling critical functions (payments, identity, communications) into monolithic systems like iOS and Android, firms reduced consumer friction but accumulated implicit obligations to maintain uptime and integrity—this debt becomes evident during forced updates that break third-party apps or disable devices, revealing a historically novel dependency where public trust is silently leveraged as infrastructure, akin to utility providers but without equivalent regulatory accountability.
Update Lock-in
Centralized app ecosystems create single-point update dependencies that force consumers to accept all updates or lose functionality, as seen in Apple’s mandatory iOS updates disabling older app versions. This mechanism prioritizes ecosystem-wide security and compatibility but eliminates user agency in update adoption, quietly entrenching vendor control over device usability. The non-obvious risk is that routine updates can inadvertently phase out critical third-party apps or accessibility features, not through malice but systemic rigidity—something most users associate with ‘forced upgrades’ yet underestimate as a form of soft coercion.
Monoculture Collapse
A unified app ecosystem propagates identical software across millions of devices, making it a prime target for cascading failure when a single update contains critical flaws, as occurred with Microsoft’s 2022 Windows Update that bricked enterprise systems. The uniformity users rely on for seamless experience becomes a systemic vulnerability, where debugging delays at the vendor level translate directly into widespread immobilization. Though people readily cite ‘one bug that breaks everything’ in hindsight, they rarely recognize how ecosystem cohesion actively suppresses technical diversity—the very buffer that historically contained digital outbreaks.
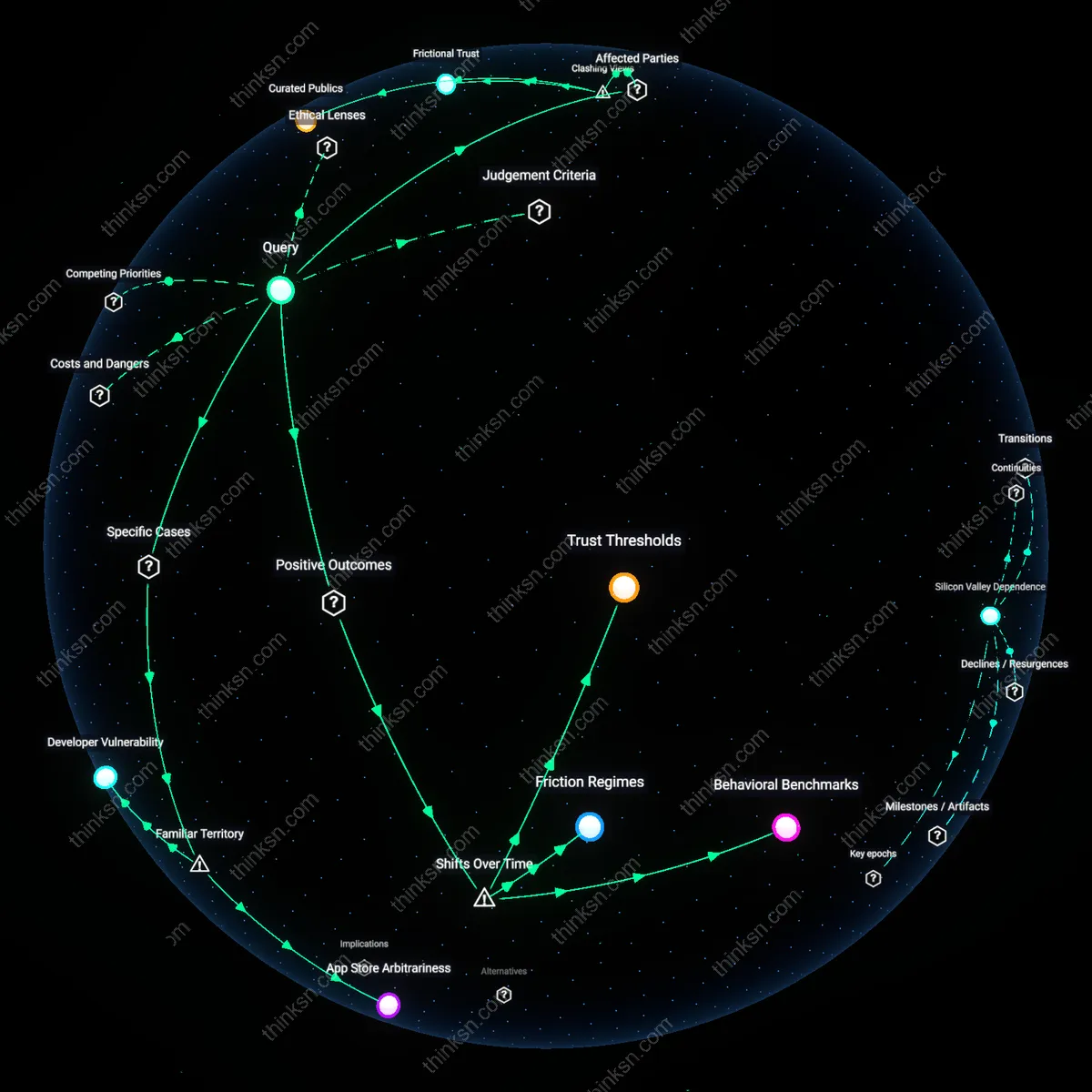
Trust Entropy
Consumers must place blind trust in a single gatekeeper to vet and deliver secure updates without exploitation, a dynamic made tangible when Huawei faced U.S. sanctions restricting Google’s ability to provide timely Android security patches. This dependency erodes over time with geopolitical shifts or corporate policy changes, yet users persistently treat platform trust as static because the interface feels consistent. The underappreciated reality is that public confidence in software safety is not built on technical audits but on uninterrupted routine—a psychological inertia that masks growing fragility in the update pipeline.
Update sovereignty
Consumers should retain update sovereignty by legally mandating user-controlled staging of critical software updates within unified app ecosystems. This means users—not platforms—decide when and how updates propagate to core functionalities, enforced through regulatory requirements modeled on network neutrality principles. The mechanism operates via firmware-level user consent gates that delay automatic enforcement of updates for a defined period, allowing individual or institutional users to assess risks, a practice already emerging in medical device regulations under FDA premarket clearance rules. Most analyses assume centralized update authority is necessary for security, but this overlooks how democratic control over timing can reduce systemic fragility without sacrificing patch integrity—shifting the balance from platform accountability to user agency.
Ecological feedback latency
Regulators must account for ecological feedback latency by embedding real-time anomaly rollback protocols in app ecosystem update pipelines, triggered by behavioral deviation rather than user reports. This dynamic leverages machine learning models trained on baseline usage patterns across millions of devices to detect downstream disruptions—like payment failures or emergency service inaccessibility—within minutes of update deployment, as seen in limited form in industrial IoT systems governed by ISO/IEC 30141. Standard treatments focus on pre-deployment testing, but the underappreciated variable is the time lag between a faulty update’s release and its destabilizing effects on interdependent services, which this feedback loop compresses, transforming ecosystems from rigid hierarchies into adaptive networks.