Who Controls the Web, Silencing Online Dissent?
Analysis reveals 11 key thematic connections.
Key Findings
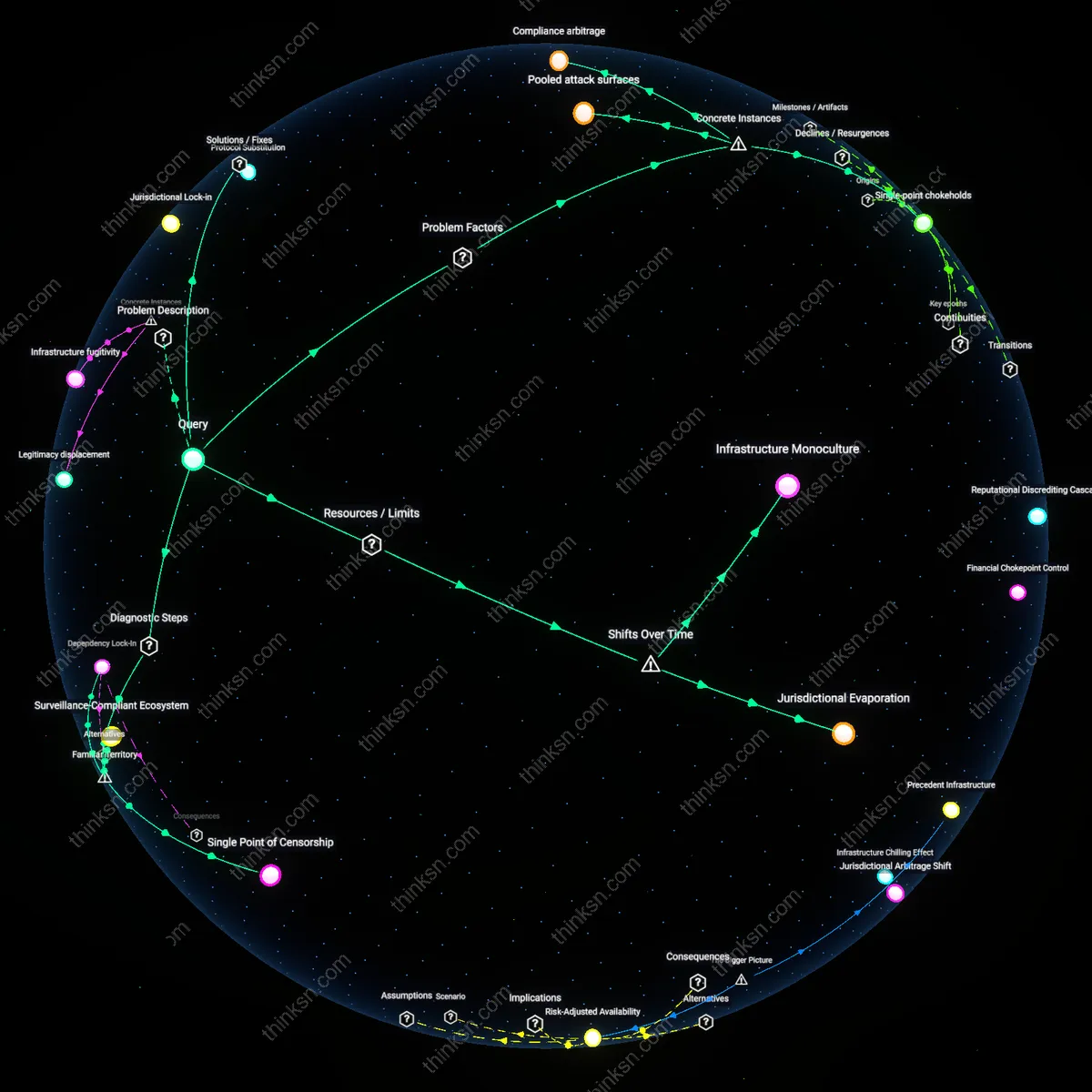
Single-point chokeholds
When ICANN and Verisign control over 70% of the domain name registration market, dissident websites like WikiLeaks face abrupt takedowns not through legal rulings but through corporate non-renewal, as occurred when Dynadot canceled WikiLeaks’ domain in 2010 without judicial oversight. This mechanism operates through contractual discretion rather than legal process, embedding enforcement in private service terms rather than public law, which makes corporate risk assessment the de facto arbitration of political speech. The non-obvious consequence is that technical infrastructure curation, not government action, has become the decisive layer of censorship for high-risk dissidents.
Pooled attack surfaces
In 2021, a single penetration of GoDaddy’s internal admin panel enabled mass domain hijacking of Palestinian advocacy sites hosted under shared reseller accounts, revealing that concentration creates densely stacked custodial dependencies where one breach cascades across ideologically isolated entities. The systemic risk lies not in individual domain weakness but in the aggregation of adversarial targets under uniform administrative access controls, enabling state or state-aligned actors to exploit market dominance as an efficient attack vector. This shows that homogenized domain supply chains amplify the yield of cyber operations targeting political minority presence online.
Compliance arbitrage
When Namecheap voluntarily suspended domains used by Hong Kong pro-democracy activists in 2020 citing U.S. sanctions compliance—despite no legal requirement to do so—it demonstrated how concentrated registrars internalize geopolitical risk through preemptive policy enforcement to avoid regulatory friction with powerful states. The mechanism is not legal coercion but self-regulatory overreach, where market leaders set universal standards that bind all users, effectively exporting the regulatory environment of one jurisdiction globally. This reveals that corporate concentration enables regulatory capture not by state mandate, but by competitive incentive to preemptively align with dominant powers to secure market position.
Single Point of Censorship
Corporate concentration in domain registration enables state coercion of political dissent by forcing registrars to suspend domains under legal or extralegal pressure. Major registrars like GoDaddy or Google Domains, concentrated in jurisdictions with strong state oversight such as the United States, comply with government takedown requests that disproportionately affect marginalized or opposition voices. Because no alternative registration ecosystems exist at comparable scale, the closure of one account or revocation of one domain can silence entire networks overnight, making the infrastructure itself a chokepoint for expression. This effect is underappreciated because public discourse assumes domain registration is a commoditized service, ignoring its role as a jurisdictionally tethered gatekeeper function.
Surveillance-Compliant Ecosystem
Dominant domain registrars standardize user verification through systems like WHOIS enforcement and mandatory email/ID validation, creating a uniformly traceable environment that mirrors state expectations of accountability. As ICANN-mandated compliance procedures are uniformly implemented by the few firms controlling the majority of domain sales — such as GoDaddy, Namecheap, and Tucows — anonymous or pseudonymous registration becomes practically impossible, undermining the operational security of dissidents. Most people associate domain registration with privacy settings like 'private listing,' not realizing that core identity collection precedes privacy layers, encapsulating users in a surveillance-ready framework regardless of opt-outs.
Dependency Lock-In
Political dissident groups relying on mass-market domain services inherit infrastructural dependencies that prioritize uptime and accessibility over resilience under attack, binding them to corporate continuity models that deprioritize adversarial robustness. Because organizations like the Electronic Frontier Foundation or independent journalists use the same registrars as commercial websites — rather than decentralized or jurisdictionally diverse alternatives — their digital presence inherits the risk calculus of profit-driven firms that avoid controversy to preserve reputation and customer base. The non-obvious insight is that 'resilience' is mistakenly equated with technical reliability rather than political autonomy, obscuring how dependence on mainstream infrastructure undermines long-term survivability during crises.
Jurisdictional Lock-in
Mandate decentralized domain registration through sovereign-backed public utilities to break monopolistic control by private registrars. National digital infrastructure agencies—such as Germany’s DENIC or Finland’s TRAFICOM—can operate non-profit, censorship-resistant domain registries under strict legal immunities, making takedowns of dissident domains subject to judicial oversight rather than corporate policy enforcement. This counters the current system where a single entity like GoDaddy or Cloudflare, responding to opaque legal threats or market pressures, can collapse the online presence of entire movements. The non-obvious implication is that corporate concentration amplifies extralegal state power by outsourcing suppression to compliant intermediaries, turning domain registration into a vector of governance bypass.
Protocol Substitution
Adopt blockchain-based domain systems like Handshake to eliminate centralized accreditation authorities in domain name resolution. By replacing ICANN-rooted DNS with a permissionless, distributed ledger, political dissidents can register domains immune to seizure by nation-states or corporate registrars colluding with governments. The mechanism works through cryptographic ownership and peer-to-peer resolution, removing the chokepoint at registrars like Namecheap or Google Domains. What’s underappreciated is that the technical centralization of DNS—not just corporate ownership—is the deeper vulnerability, allowing coordinated deplatforming even when content is hosted resiliently.
Normalization of Takedown
Regulate domain registrars as essential speech intermediaries to halt the routine compliance with takedown requests lacking due process. Imposing public utility obligations—such as mandatory transparency reporting, appeals mechanisms, and delay periods before domain suspension—forces registrars like Tucows or Amazon Route 53 to treat political content differently from copyright infringement. This intervenes in the systemic drift where corporate risk aversion, driven by liability fears and investor pressure, incentivizes preemptive deplatforming of controversial speech. The overlooked dynamic is how normalization of rapid takedowns erodes resilience not through isolated events, but by accustoming both companies and users to automatic compliance as the default regime.
Infrastructure Monoculture
Corporate consolidation of domain registrars after the 2000s privatization wave has reduced redundancy in naming systems, forcing political dissenters to rely on a shrinking set of platforms that comply with state-backed takedown requests. As national governments formalized cooperation with ICANN-accredited registrars—especially post-9/11 and after the 2012 DNSSEC rollout—dissident groups lost access to diverse, jurisdictionally dispersed registration pathways that once allowed domain persistence through legal arbitrage. The non-obvious consequence of this shift is not censorship per se, but the collapse of fallback options during acute political crisis, as the same security and standardization measures meant to stabilize DNS also eliminated loosely governed entry points.
Jurisdictional Evaporation
The migration from country-code top-level domains (ccTLDs) to global commercial registrars between 2010 and 2020 dissolved geofenced regulatory refuges, as once-autonomous national registries like .is (Iceland) or .to (Tonga) outsourced backend services to U.S.-based providers such as Amazon Route 53. This technical integration erased de facto sanctuary domains that previously resisted extraterritorial pressure due to weak enforcement treaties or political neutrality. The overlooked shift is not the loss of privacy but the disappearance of administrative latency—the time delay in cross-border legal enforcement—that once permitted dissident platforms to rehost, re-register, or reconstitute before takedown orders could be executed.