Commercial Primacy Threshold
Cloud providers began infiltrating government functions in 2010–2014 when U.S. federal agencies like the Department of Homeland Security adopted Amazon Web Services and Microsoft Azure to modernize IT infrastructure, bypassing traditional procurement channels through Technology Transformation Services—this shift was enabled not by explicit policy but by chronic underfunding of public tech capacity, which made private scalability and speed structurally irresistible despite oversight gaps. The non-obvious consequence is that once cloud platforms became the only viable option for deploying high-stakes systems like border biometrics, the state effectively outsourced architectural sovereignty, locking in dependence before regulatory frameworks could evolve, thereby normalizing private control over public authority through logistical necessity rather than democratic delegation.
Crisis-Driven Normalization
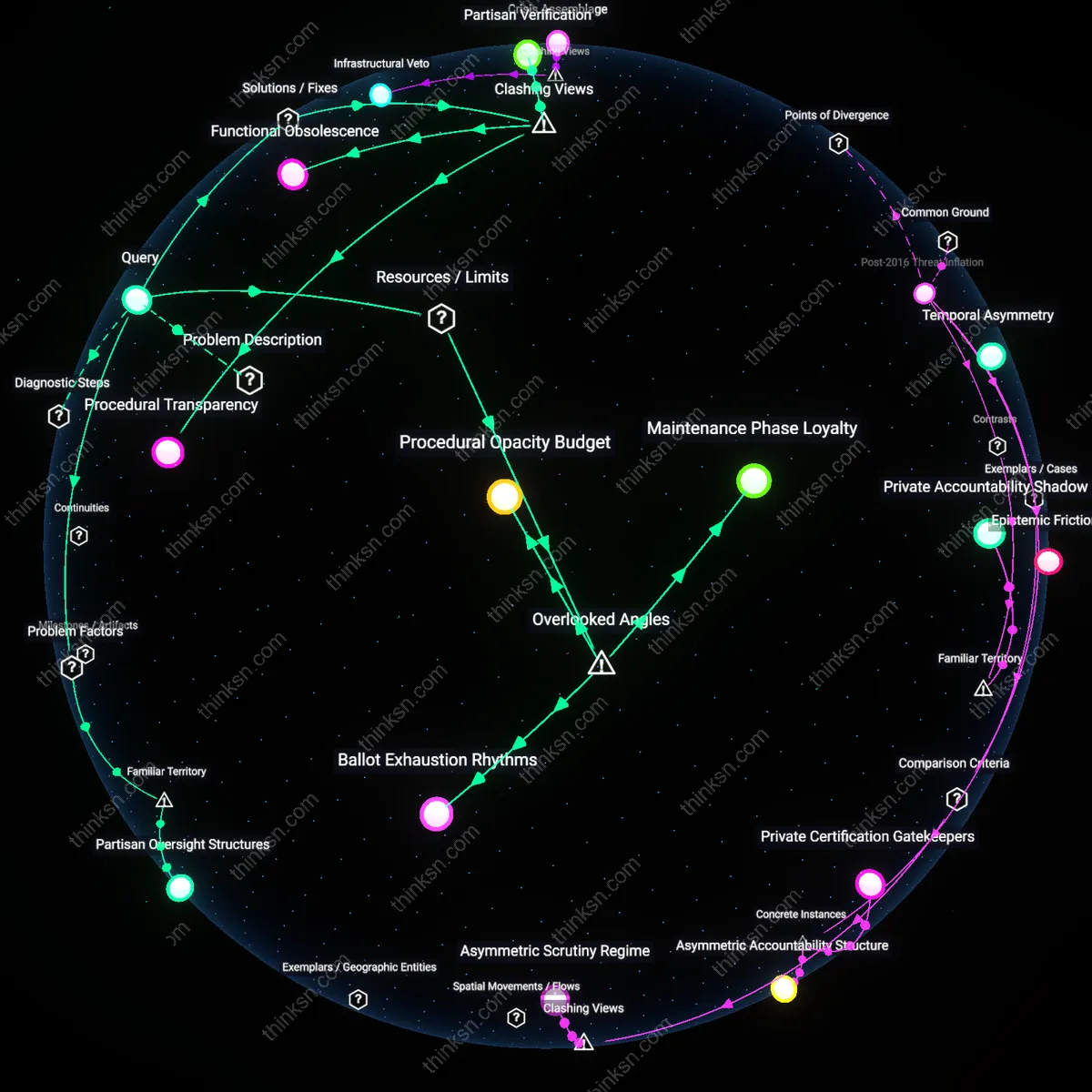
The migration of election logistics to cloud platforms accelerated after the 2016 U.S. presidential election, when state and local election officials, responding to federally reported Russian cyber intrusions, rapidly adopted Microsoft’s Election Code and Google’s voter information APIs to stabilize voter registration and ballot distribution systems—this emergency-driven adoption circumvented standard accountability protocols because cybersecurity preparedness was treated as an urgent technical fix rather than a governance issue. The systemic dynamic is that repeated threat narratives around election integrity and border security have created a standing state of exception, allowing private platforms to become embedded in sovereign processes by positioning their involvement as risk mitigation, not governance substitution, thereby institutionalizing their role without requiring legislative or judicial ratification.
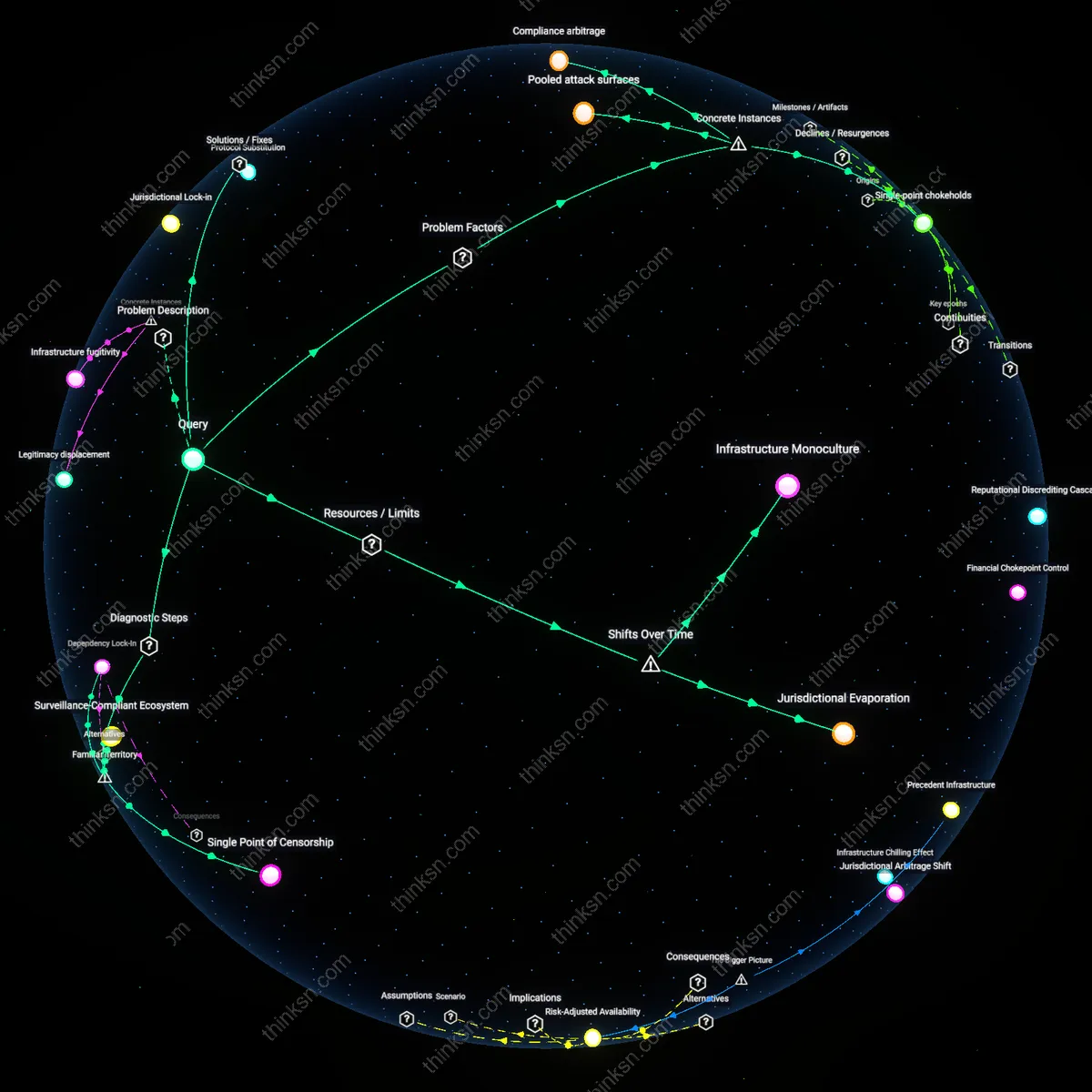
Infrastructural Sovereignty Deferral
Cloud dominance in border control emerged concretely in 2019 when U.S. Customs and Border Protection contracted Palantir and Amazon to operate the Homeland Advanced Recognition Technology (HART) system, storing biometric data on millions at the southern border—this was possible because the procurement was framed as a 'data storage upgrade' rather than a delegation of surveillance authority, exploiting procurement rules that exempt infrastructure from the same scrutiny as operational decision-making. The overlooked mechanism is that government oversight frameworks are structured around human discretion and rule application, not the automated, back-end processing of data flows, allowing cloud providers to assume de facto public authority by controlling the infrastructure where decisions are anticipated, scored, and executed, rendering sovereignty contingent on systems no public body fully understands or governs.
Infrastructural Legibility
Cloud providers absorbed border control functions by redesigning data-sharing protocols between national and local agencies during the EU’s Schengen Information System upgrades from 2010–2018, where Amazon Web Services and Microsoft tailored backend architectures that determined which data fields could be queried, retained, or cross-referenced—thereby shaping enforceable definitions of 'suspicious movement' without legislative input; this technical standardization pre-empted policy deliberation, making oversight impossible because no law could address systems whose operational logic was defined in proprietary code and server configurations that governments did not audit or fully understand. What is overlooked is that cloud providers, by formatting the machine-readable ontology of migration, now govern through infrastructural legibility—the capacity to make certain realities computationally visible and actionable, while rendering others invisible.
Contractual Invisibility
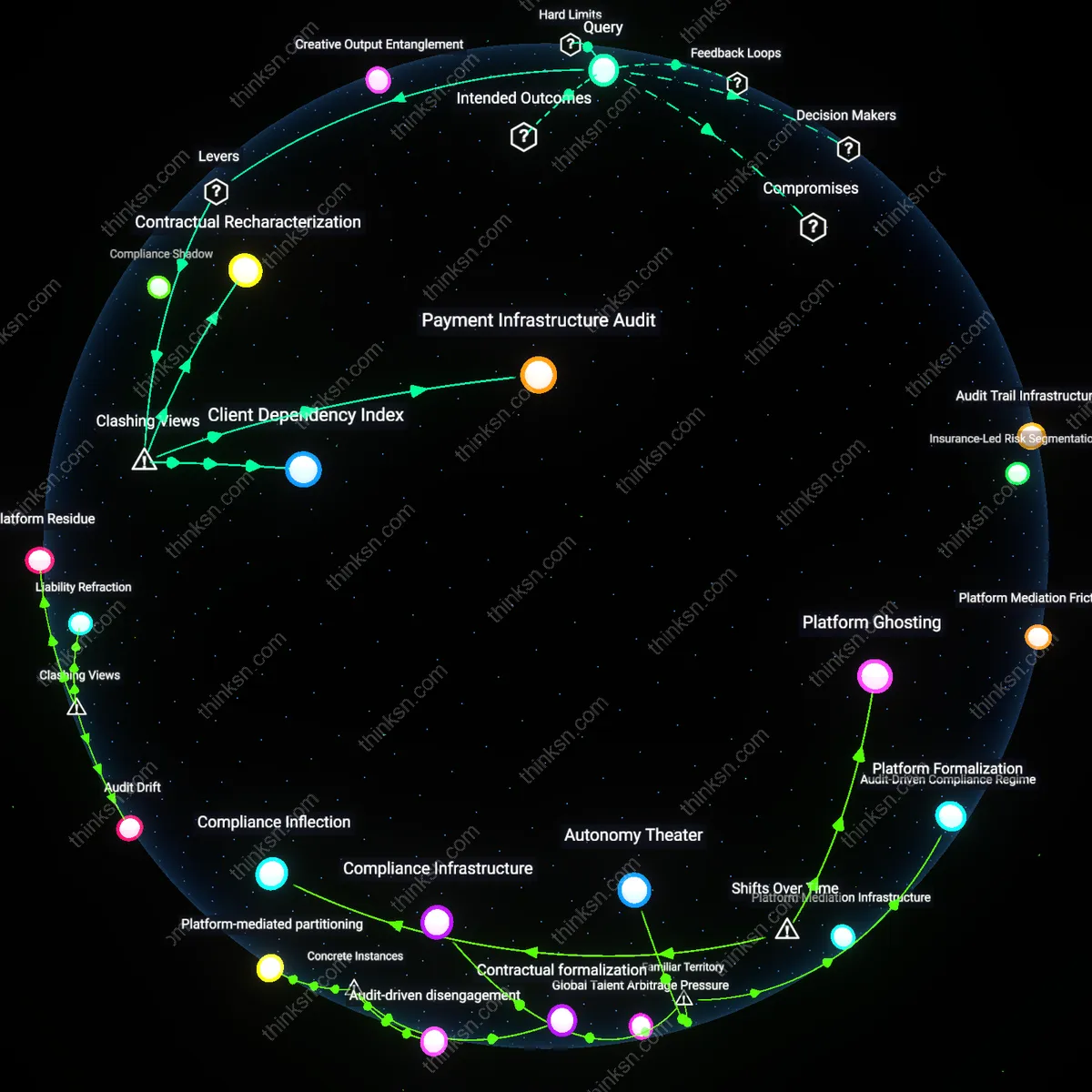
During the 2020 U.S. election cycle, Dominion Voting Systems subcontracted vote-tabulation data transfers to Google Cloud, embedding classified chain-of-custody decisions into service-level agreements that specified uptime, encryption standards, and data replication—but omitted public accountability clauses such as third-party access, forensic audit trails, or algorithmic transparency; these omissions were not regulatory gaps but deliberate contractual choices framed as technical necessities, shielding cloud operators from scrutiny because no 'function' was formally delegated, only infrastructure provision. The overlooked dynamic is that sovereignty can be operationally transferred not through visible delegation but via contractual invisibility—the systematic excision of democratic safeguards from the legal microstructure of procurement, where governance shifts occur in clauses optimized for liability limitation, not civic function.
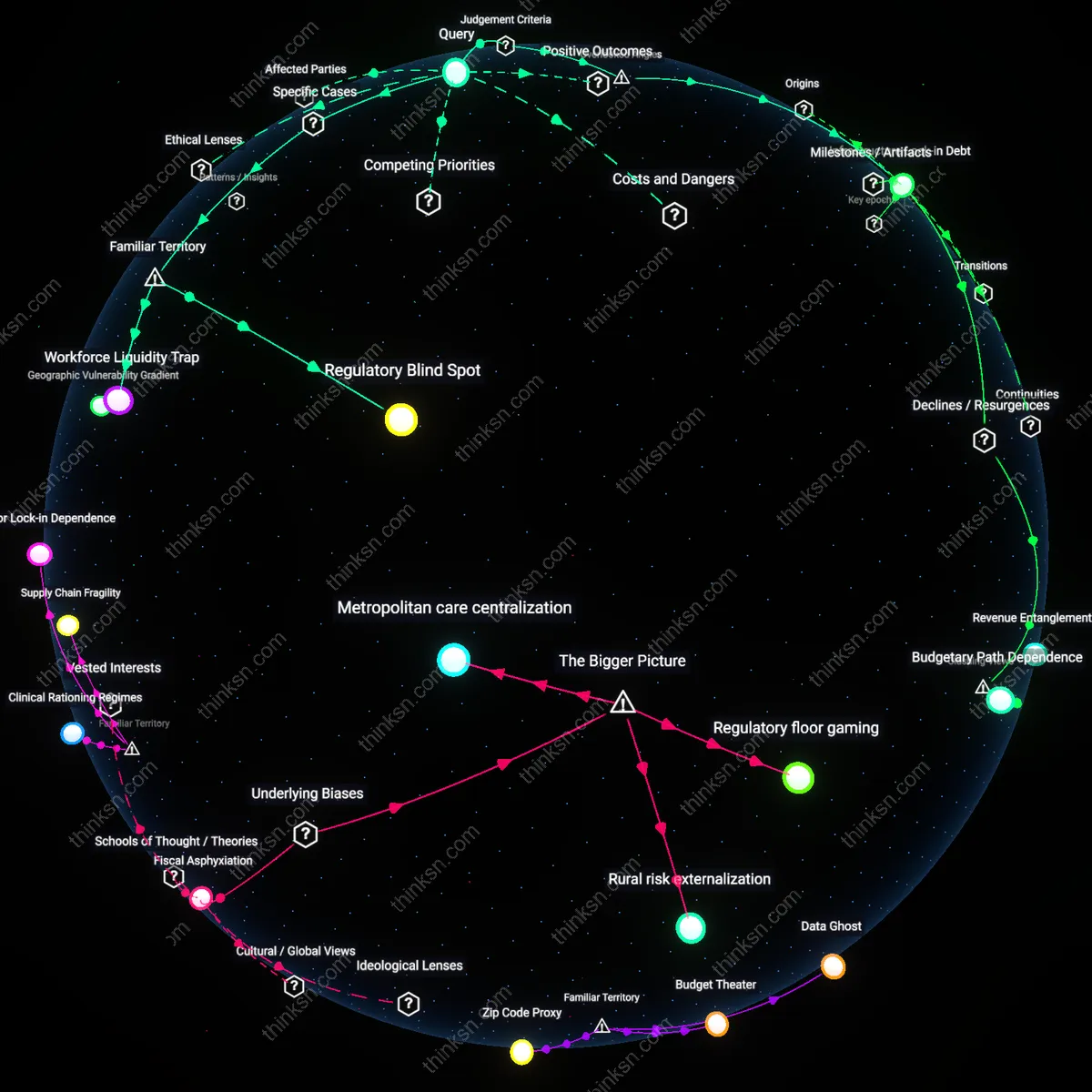
Temporal Preemption
India’s Aadhaar biometric system, when migrated to AWS in 2016, adopted real-time authentication workflows requiring sub-second response times, forcing electoral and welfare distribution systems to align with cloud platform update cycles and outage schedules rather than parliamentary timelines or civic calendars, thereby shifting the rhythm of state operation to match platform availability; this created a de facto dependency where policy reversals or audits became technically infeasible during platform-mandated maintenance windows, placing critical civic processes at the mercy of cloud uptime priorities. The underappreciated factor is temporal preemption—the way cloud providers, by controlling the pace and reliability of digital state functions, colonize not just space or data but political time, making oversight asynchronous and therefore ineffective, as legislatures meet too slowly to respond to system failures or drifts that occur in seconds.
Infrastructural Sovereignty
Cloud providers have not taken over government functions but have become indistinguishable from the state through the monopolization of mission-critical digital infrastructure, where companies like AWS operate classified government clouds (AWS GovCloud) that host sensitive border and election systems without public procurement transparency. This integration bypasses traditional oversight not through subversion but by becoming the de facto technical embodiment of state capacity—where the provider’s architecture becomes the state’s operational surface. The non-obvious reality is that oversight has not weakened; it has become technically infeasible, as auditing requires expertise embedded within the provider’s proprietary systems, which few public agencies possess. This reveals that sovereignty increasingly resides in technical control over infrastructure, not legal delegation.
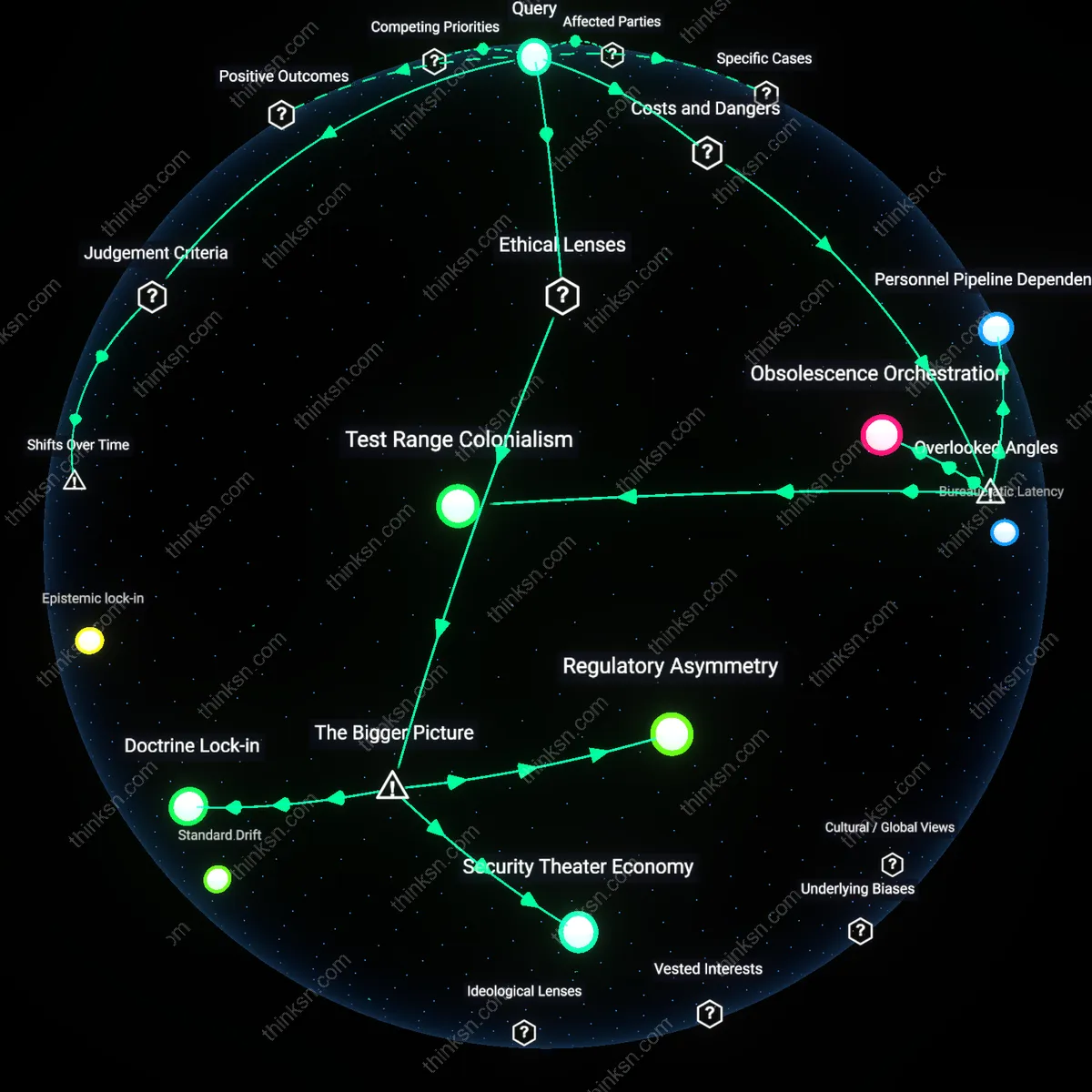
Opacity by Designation
Governments have reclassified core public functions as 'technical logistics' to legally outsource border enforcement algorithms and election data processing to providers like Microsoft Azure and Google Cloud, shielding these activities from scrutiny under the guise of commercial confidentiality and IT procurement rules. By framing surveillance infrastructure and voter roll management as mere 'cloud migration projects,' officials evade legislative debate and public accountability that would accompany policy changes. The obscured mechanism is jurisdictional laundering—where functional oversight is negated not by corporate overreach but by deliberate bureaucratic misclassification within interagency procurement frameworks. This challenges the assumption that privatization is inherently contested, revealing it instead as an administrative convenience that exploits categorization gaps in public law.
Performance Legitimacy
Cloud providers gain de facto authority over state functions by delivering measurable performance gains in election processing and border monitoring—such as faster biometric matching at ports of entry via Palantir-hosted systems on AWS—that create political incentives to sustain their role despite lacking democratic accountability. The state rewards technical efficacy over procedural transparency, treating cloud platforms as performance partners rather than contractors, thus legitimizing their control through outcomes rather than mandates. This shift replaces oversight with a feedback loop where continued renewal of contracts depends on operational success, not audit or public review. The non-intuitive consequence is that public legitimacy is now partially outsourced to the perceived reliability of private system outputs, supplanting institutional checks with outcome-based justification.
Infrastructural Substitution
Amazon Web Services' deployment of cloud infrastructure to host the U.S. Customs and Border Protection’s biometric entry-exit system at Hartsfield-Jackson Airport in 2019 replaced legacy public IT systems without new legislative authority, operating through classified procurement loopholes that treat vendors as neutral tools rather than policy actors, thereby obscuring operational control under the guise of technical maintenance—what appears as mere modernization conceals the quiet transfer of sovereign decision logic into privately governed architectures.
Crisis-mediated Privatization
During the 2020 U.S. election cycle, Microsoft’s rapid provision of Azure-based secure voting portals to multiple state election boards—particularly in Georgia and Pennsylvania—was legitimized by pandemic-induced emergency declarations that suspended normal oversight vetting, enabling the embedding of corporate cloud governance structures into ballot distribution and authentication systems under temporary mandates that never sunsetted, revealing how acute public emergencies create irreversible footholds for private administrative permanence.
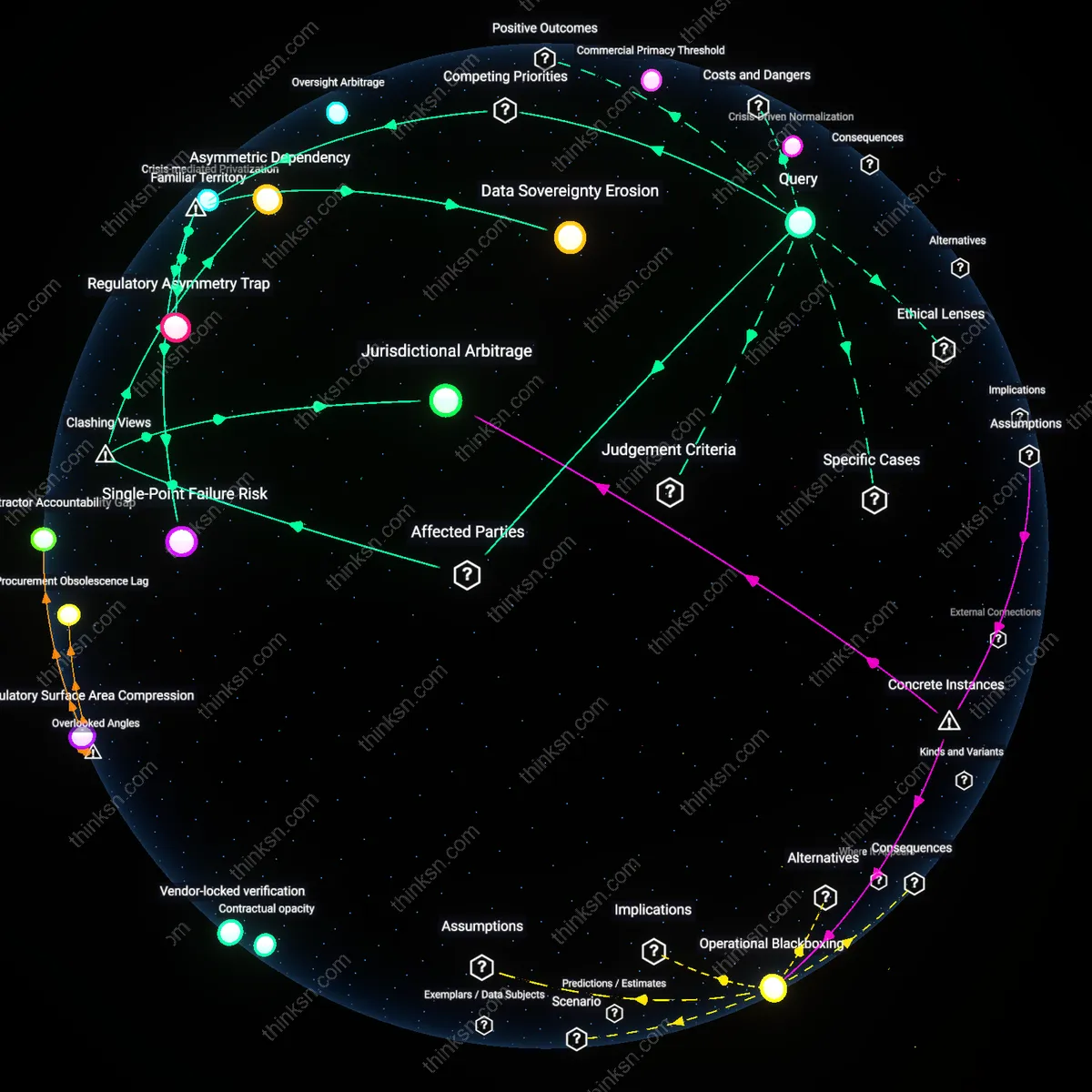
Oversight Arbitrage
Palantir’s implementation of the Gotham platform within the UK Home Office’s asylum processing operations in 2022 leveraged differential audit standards between public agencies and contracted software developers to avoid subjecting algorithmic decision pathways to the same freedom-of-information requirements as civil servants, functioning through modular data pipelines that obscure state responsibility by design—demonstrating how jurisdictional gaps in digital service delivery become deliberate operational features for evading democratic accountability.
Contractual Sovereignty
Cloud providers assumed border control functions through classified procurement agreements like the 2018 DHS contract with AWS to process biometric data at major ports of entry. This mechanism bypassed legislative scrutiny by nesting sensitive operations within existing acquisition frameworks designed for logistics, not rights-bearing systems, allowing real-time algorithmic filtering of travelers without public oversight bodies. The non-obvious reality is that these contracts are structured as extensions of commercial service-level agreements, making them invisible to transparency laws that expect public agency reporting.
Infrastructure Capture
Election systems in states like Georgia migrated to cloud-based case management platforms such as AWS-hosted voter registration databases after the 2020 election cycle, transferring core electoral logistics to backend architectures maintained by private engineers. These systems operate under terms of service rather than statutory mandates, meaning their stability and access controls derive from uptime guarantees, not constitutional requirements. Most voters assume elections are run by local clerks, not realizing the cloud layer that governs data flow has become the de facto administrator.
Crisis-Justified Integration
Cloud providers entered federal emergency response systems through FEMA’s adoption of Microsoft Azure during hurricane recovery efforts in Puerto Rico in 2017, where disaster rationing algorithms were deployed without public consultation. The perceived neutrality of technology during emergencies allowed rapid deployment of backend systems that later became permanent fixtures in civil management. The familiar association with humanitarian aid masks the long-term delegation of distributive authority to code maintained in private data centers.