Identity Anchors
Regulated gatekeepers function as the official issuers of verifiable credentials that link legal identities to decentralized identifiers. These entities—such as national governments issuing digital IDs or financial institutions complying with KYC/AML regulations—generate cryptographically signed data that serves as a trust bridge between an individual’s real-world identity and their on-chain persona. This mechanism is non-obvious because, despite the decentralized nature of self-sovereign identity systems, access to foundational trust ultimately depends on centralized authorities whose credentials are widely recognized, revealing that decentralization does not eliminate gatekeeping but relocates it to the point of identity issuance.
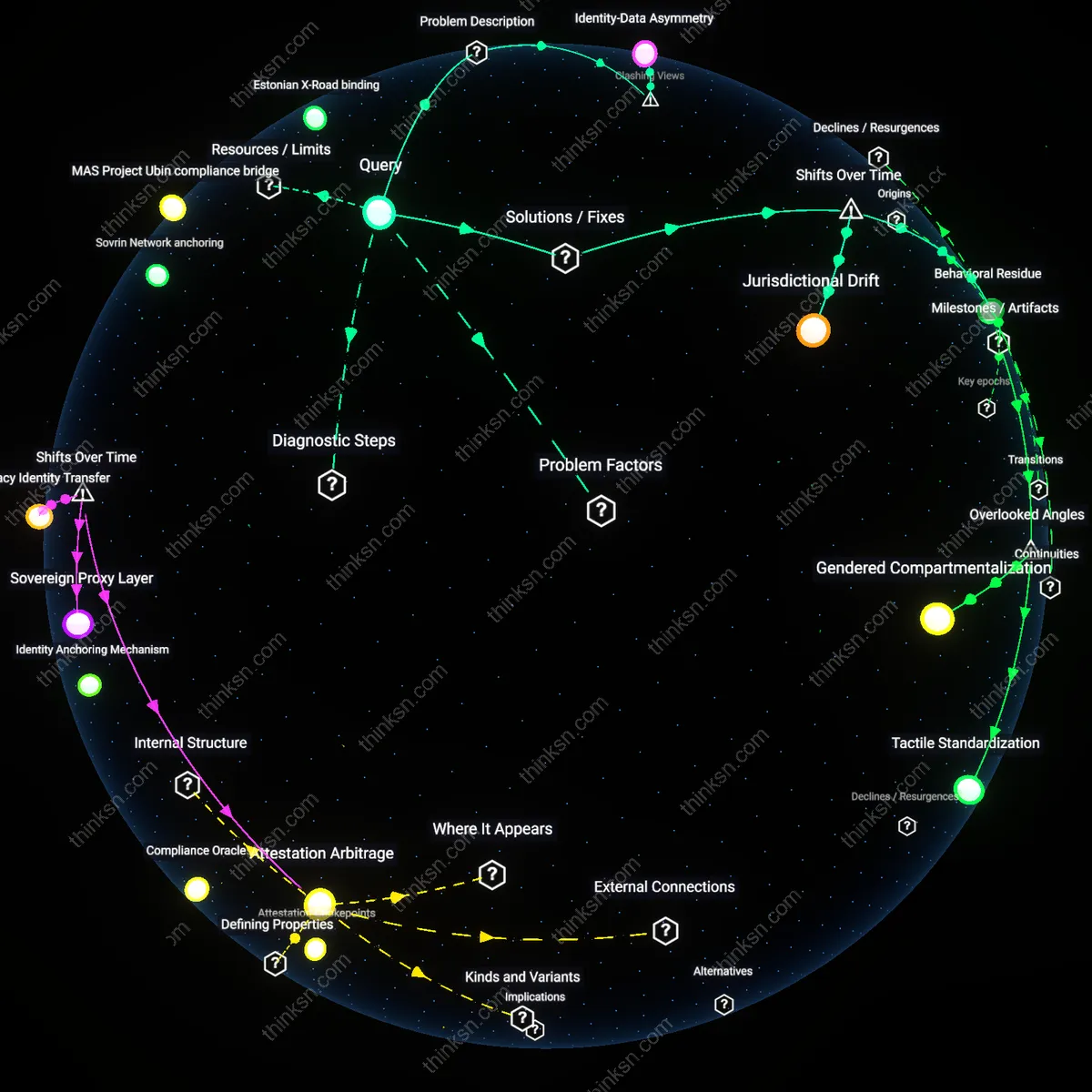
Attestation Chokepoints
Regulated gatekeepers sit at the threshold where off-chain accountability meets on-chain activity by providing signed attestations that enable or restrict access to decentralized applications. Entities like certified auditing firms or regulated exchanges validate real-world actions—such as proof of address or tax compliance—and issue digital stamps that smart contracts can verify, thereby translating legal or regulatory compliance into executable on-chain conditions. The underappreciated reality is that while blockchain networks distribute data storage, they concentrate trust in the few recognized entities authorized to produce valid attestations, making these gatekeepers de facto validators of legitimacy within supposedly permissionless systems.
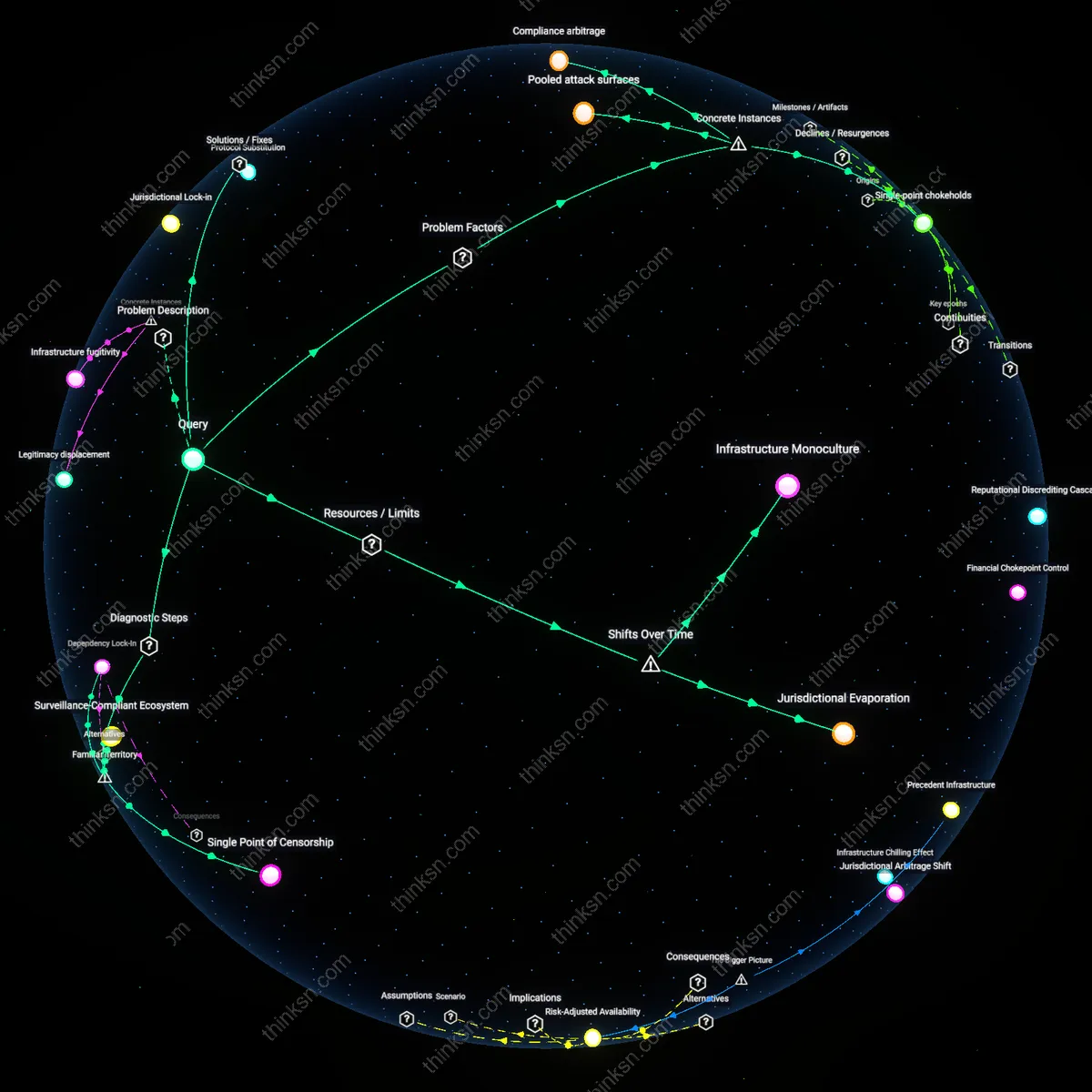
Compliance Oracles
Regulated gatekeepers operate as compliance oracles, feeding verified real-world data into decentralized networks through trusted API endpoints monitored by regulatory bodies. Institutions like central banks or securities regulators supply signed data feeds—such as accredited investor status or corporate registration details—that directly influence on-chain behaviors, including token sale eligibility or governance voting rights. The overlooked significance is that these oracles do not merely interface between worlds; they preemptively shape blockchain functionality by embedding regulatory constraints into the logic of smart contracts, turning legal compliance into an embedded architectural feature rather than an external enforcement layer.
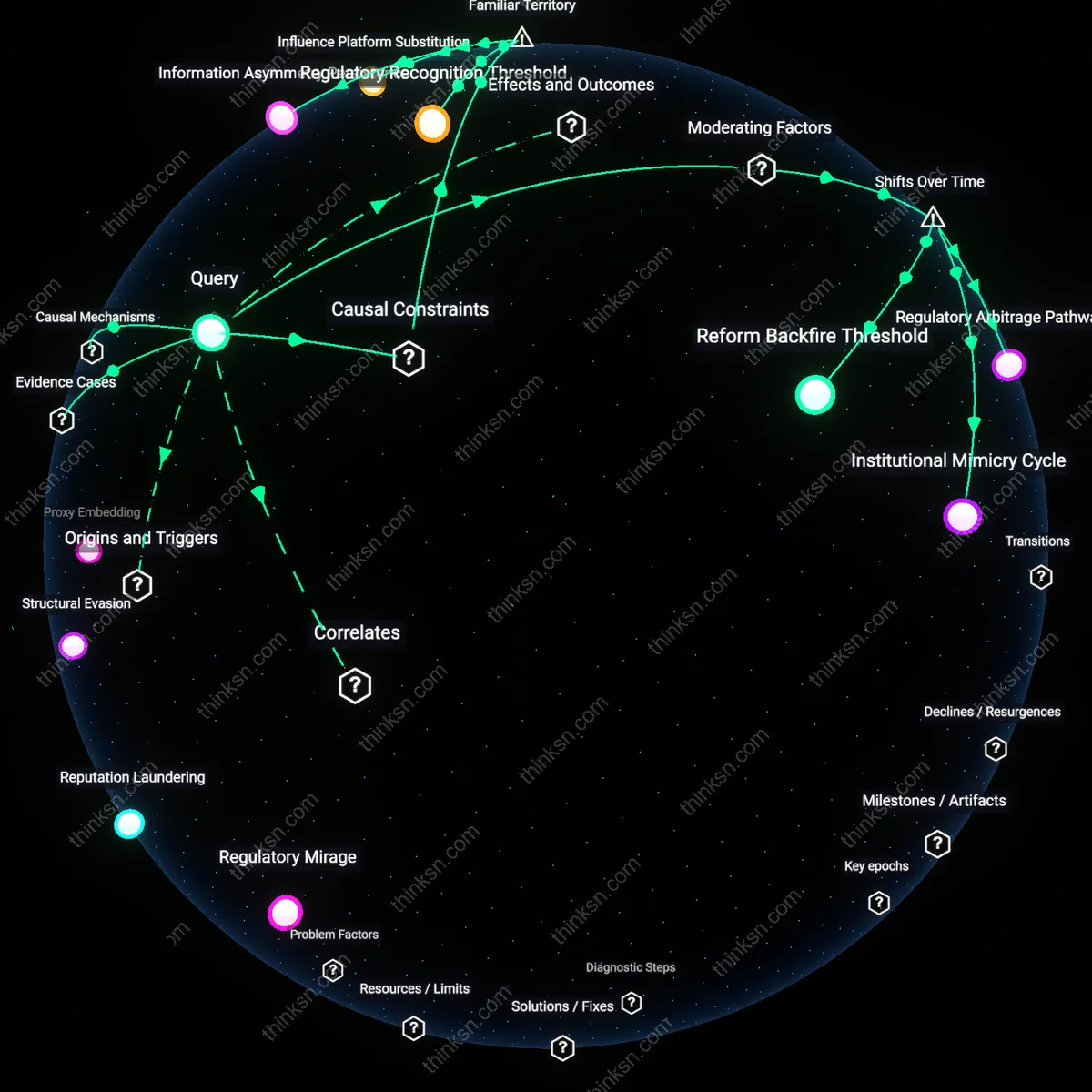
Legacy Identity Transfer
Regulated gatekeepers now function as translation layers that retrofit centralized identity credentials into decentralized identity systems through verifiable credential issuance. National identity providers like Germany’s IDNow or Estonia’s e-Residency program inject state-issued attributes—passport scans, tax IDs—into blockchain-based identifiers via OAuth-style credentialing hubs, effectively porting analog legal personhood onto digital wallets. This mechanism crystallized after 2020, when EU digital identity frameworks began recognizing decentralized identifiers (DIDs) as valid endpoints, shifting gatekeepers from custodians of standalone identity stores to brokers of identity fragments—revealing that interoperability depends not on decentralization eroding state control, but on regulated entities strategically re-encoding it.
Attestation Arbitrage
Regulated gatekeepers have transitioned from acting as primary validators of identity to becoming arbiters of attestation relevance in decentralized identity ecosystems, determining which real-world actions qualify as meaningful on-chain events. Financial institutions like JPMorgan’s Onyx or regulated KYC providers such as Chainalysis now tag wallet addresses with contextual metadata—source of funds, jurisdictional exposure, behavioral risk—through compliance oracles that feed risk-scoring models into smart contract environments. This shift emerged distinctly post-2021, following the FATF’s ‘Travel Rule’ enforcement on VASPs, which forced gatekeepers to operationalize selective data disclosure mechanisms, exposing how trust in decentralized systems is not abolished but redistributed through jurisdictional choke points that filter legitimacy ex post.
Sovereign Proxy Layer
Regulated gatekeepers now occupy a position as sovereign proxy layers, embedding state enforcement logic into decentralized identity through mandated interface points that anchor pseudonymous addresses to legal identities at moments of value conversion. Central banks operating digital currency sandboxes—like the People’s Bank of China with its e-CNY system or the Bundesbank’s Project Stella—require designated intermediaries to log, tag, and report DID-linked transactions when crossing thresholds, transforming private wallets into conditional sovereign peripherals. This configuration solidified after 2022, as G20 nations adopted FATF-aligned DLT guidance, revealing that decentralized identities never escaped state oversight but were instead restructured to activate compliance only at liquidity gates, where value exits the chain.
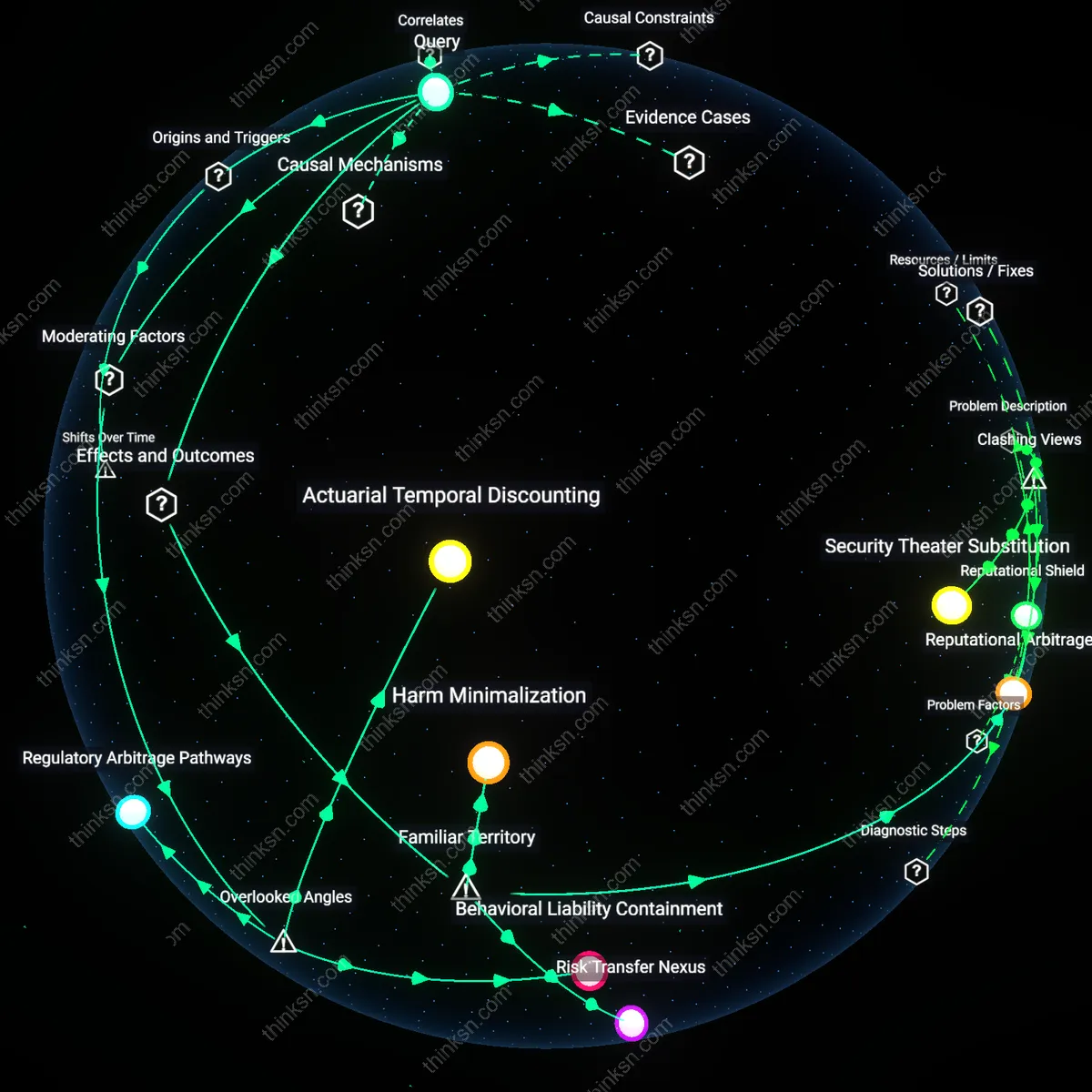
Reputation arbitrage
Gatekeepers enable reputation arbitrage by selectively disclosing attestations that bridge on-chain behavior with off-chain credibility systems, such as credit scoring or professional licensing, without standardizing the underlying data provenance. For instance, a regulated identity provider might issue a verifiable credential certifying an individual has passed a Know Your Customer (KYC) check, which is then used to unlock higher transaction limits on a decentralized finance (DeFi) platform—yet the same credential could be repurposed across unrelated domains like housing rentals or gig work platforms. The non-obvious mechanism here is not verification itself, but the asymmetrical reuse of trusted claims across contexts where the original validation criteria are no longer relevant or transparent, creating covert reputation spillovers. This dynamic undermines the assumption that decentralized identities empower user sovereignty, when in fact they can enable silent consolidation of behavioral capital across ecosystems by gatekeepers who control credential issuance.
Data jurisdiction proxies
Regulated gatekeepers function as de facto data jurisdiction proxies by determining where and how identity-related data is stored, accessed, and contested, even when the blockchain ledger itself is jurisdictionally agnostic. For example, a European Qualified Trust Service Provider issuing electronic signatures tied to a decentralized identifier must ensure compliance with eIDAS regulations, meaning that disputes over identity authenticity are resolved through national courts and certification authorities, not smart contract logic. This embedding of legal process into the operational layer of digital identity systems creates a hidden dependency on legacy administrative geographies—despite the network’s technical decentralization. Standard models focus on cryptographic ownership or interoperability standards, but overlook how enforcement venues and procedural rights are reintroduced through these gatekeepers, making them spatial fixpoints in an otherwise borderless architecture.
Identity Anchoring Mechanism
Regulated gatekeepers function as legally recognized validators who bind cryptographic identities to state-issued credentials through regulated know-your-customer (KYC) procedures, creating an anchor point between self-sovereign identity systems and jurisdictional authority. Financial institutions, licensed crypto exchanges, and identity verification firms like Onfido or Jumio perform biometric and document checks that link a decentralized public key to a verified real-world individual, enabling compliance with anti-money laundering (AML) frameworks. This mechanism is non-obvious because it reveals that decentralization does not eliminate intermediaries but shifts their role from data custodians to accreditation nodes—where trust is not in the data itself but in the provenance of its linkage to legal persons. The anchoring persists because regulators condition market access on this bridge, making gatekeepers de facto co-architects of identity legitimacy in Web3 ecosystems.
Sovrin Network anchoring
The Sovrin Network in Canada and the U.S. connects regulated financial institutions like Northern Trust to self-sovereign identities through verifiable credentials anchored to a public permissioned blockchain. Here, regulated gatekeepers act as trusted issuers who validate real-world identities and behaviors—such as corporate governance or accredited investor status—then issue tamper-proof digital credentials linked to on-chain identifiers, thus binding off-chain legal accountability to on-chain data without central intermediaries. This reveals the non-obvious role of regulated entities not as blockchain operators but as authoritative root nodes in decentralized identity ecosystems, where legitimacy flows from legal jurisdiction rather than cryptographic consensus.
Estonian X-Road binding
In Estonia, the national digital identity system tied to e-Residency binds real-world legal actions—like business registration or tax filing—to blockchain-secured logs through the KSI Blockchain operated by Guardtime. Regulated gatekeepers such as the Estonian Tax and Customs Board authenticate identity and authorize transactions via X-Road, a data exchange layer that connects physical documentation to digital signatures cryptographically verified on-chain. This illustrates how state institutions function as anchoring authorities that certify the ontological status of digital actions, revealing that decentralization relies on centralized sources of truth for initial identity provenance.
MAS Project Ubin compliance bridge
Under Singapore’s Project Ubin led by the Monetary Authority of Singapore (MAS), commercial banks including DBS and OCBC used Corda-based networks to issue digital currency while enforcing KYC/AML checks before onboarding participants into a partially decentralized ledger system. These regulated gatekeepers validated real-world corporate identities and financial standing prior to granting access to blockchain-mediated transactions, meaning identity and compliance occurred off-chain but determined on-chain permissions. This uncovers how financial regulatory bodies design identity gatekeeping as a pre-condition for network participation, positioning decentralization not as an escape from oversight but as its distributed enforcement mechanism.