Do Data Portability Standards Empower Users or Benefit Big Tech?
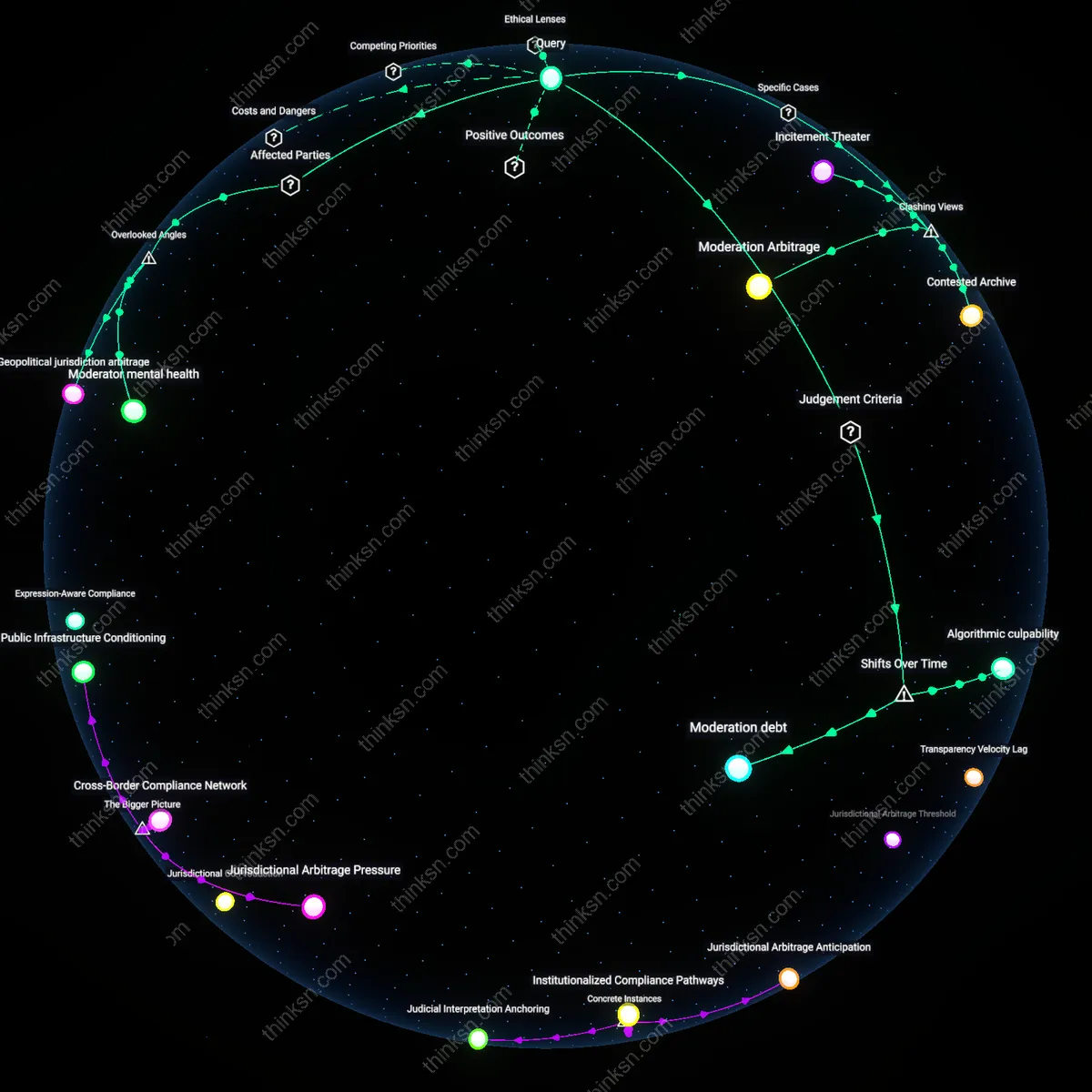
Analysis reveals 6 key thematic connections.
Key Findings
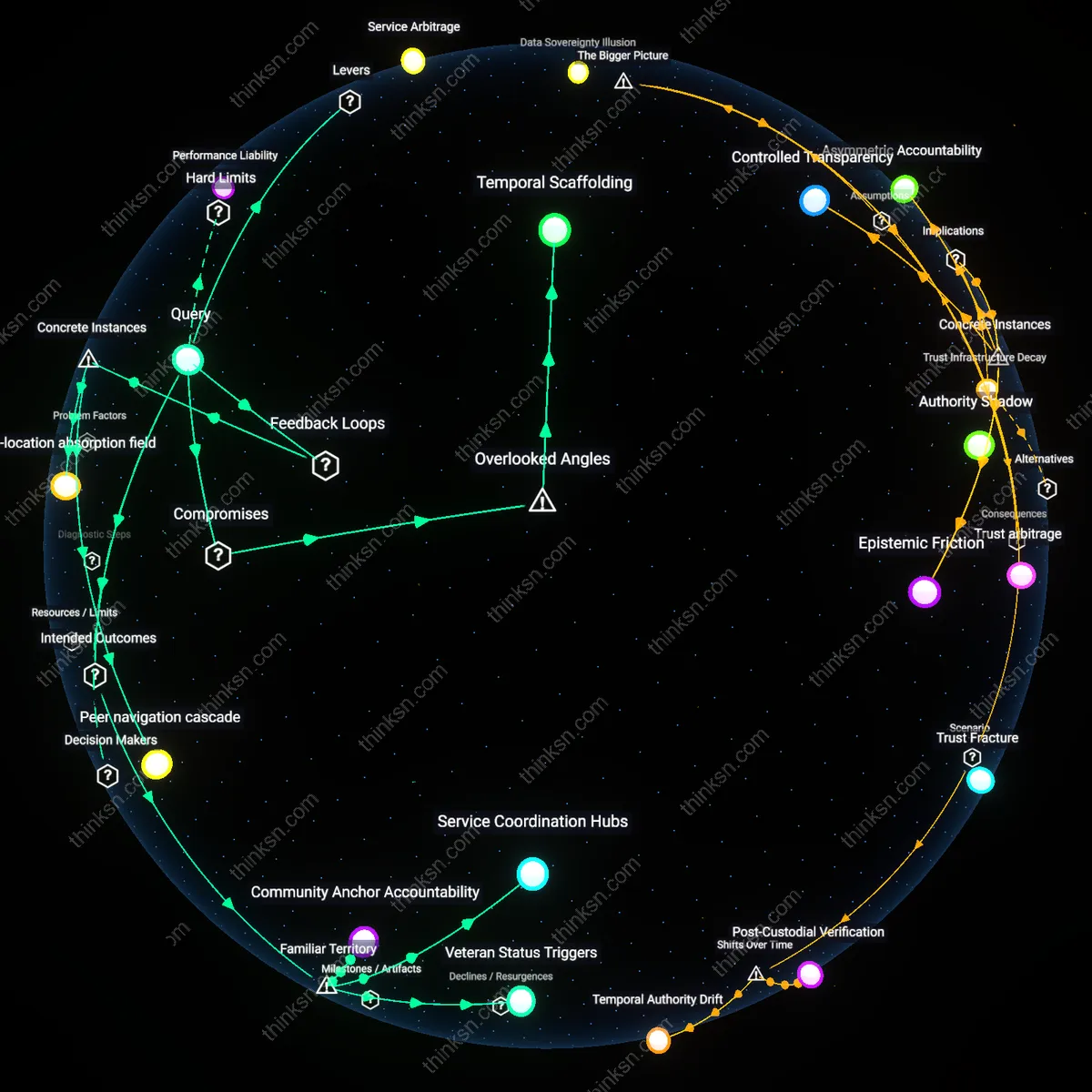
User Sovereignty Emergence
Individual users gained primary benefit from platform-enforced data portability standards as these emerged after the mid-2010s shift from closed-platform dominance to interoperability mandates, particularly following the GDPR's 2018 enforcement, which transformed personal data from a trapped asset into a transferable entitlement. Before this era, users effectively forfeited control once data entered siloed ecosystems like Facebook or Google; the legal codification of portability created a new structural condition where users could exit, repurpose, or reassign their data trails, enabling practical rather than theoretical autonomy. The non-obvious outcome is that this legal-administrative turn elevated users from passive subjects to actionable agents in data economies, not through market power but through regulated procedural rights, marking a pivot from extraction to circulation.
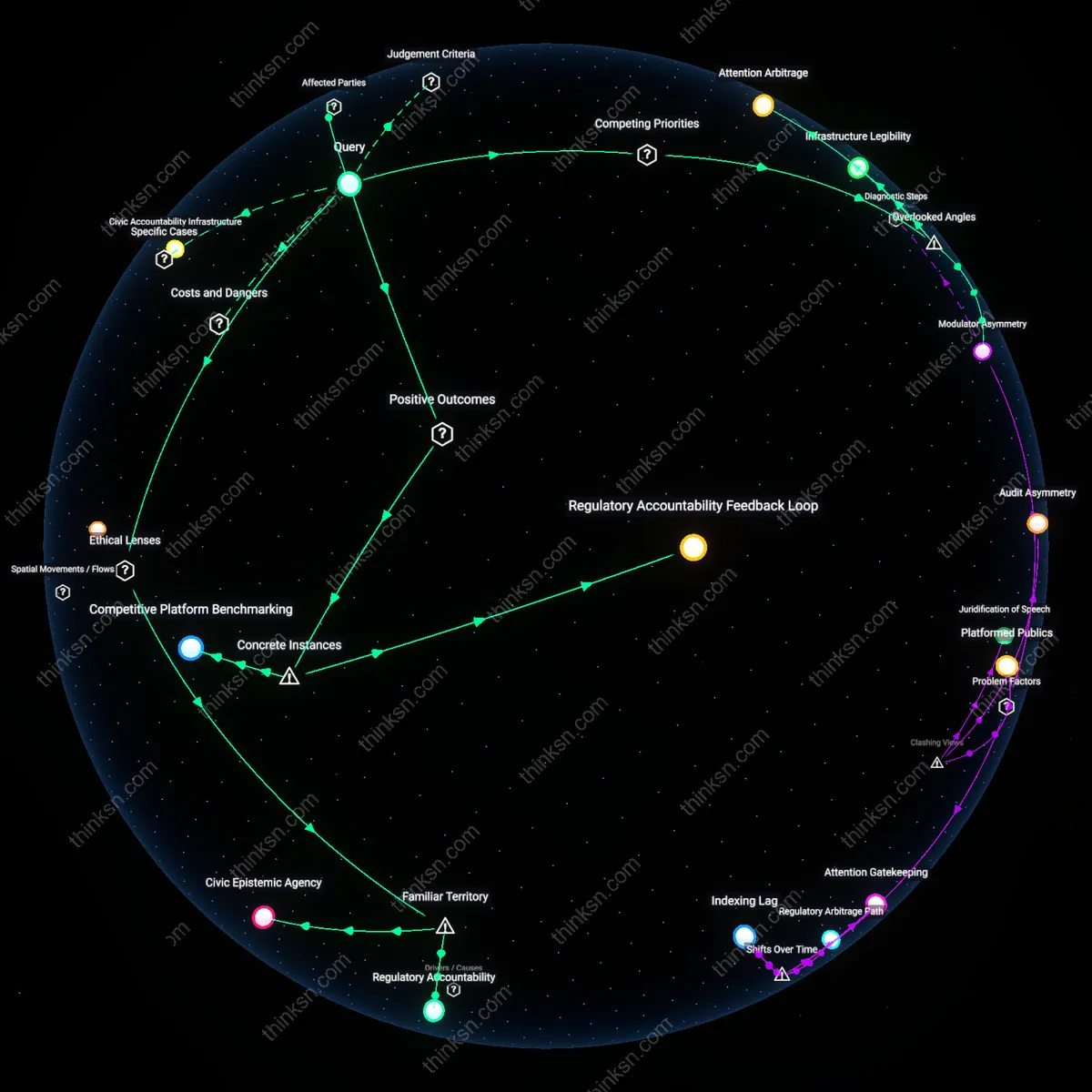
Interoperability Infrastructure Regime
Technology regulators and standards bodies became the most consequential beneficiaries as data portability evolved from ad hoc API arrangements in the early 2010s into mandated technical architectures after 2020, exemplified by the EU’s Digital Markets Act designating gatekeepers and prescribing common data formats. This shift transformed portability from a symbolic user right into an enforceable systemic requirement that realigned platform incentives around compliance-first engineering, privileging institutions capable of shaping protocols over those leveraging data hoarding. The overlooked dynamic is that the power to define portability standards—such as schema, authentication, and transfer speed—now concentrates more influence in regulatory and consortial bodies than in individual choice, revealing a transition from user empowerment to infrastructural governance.
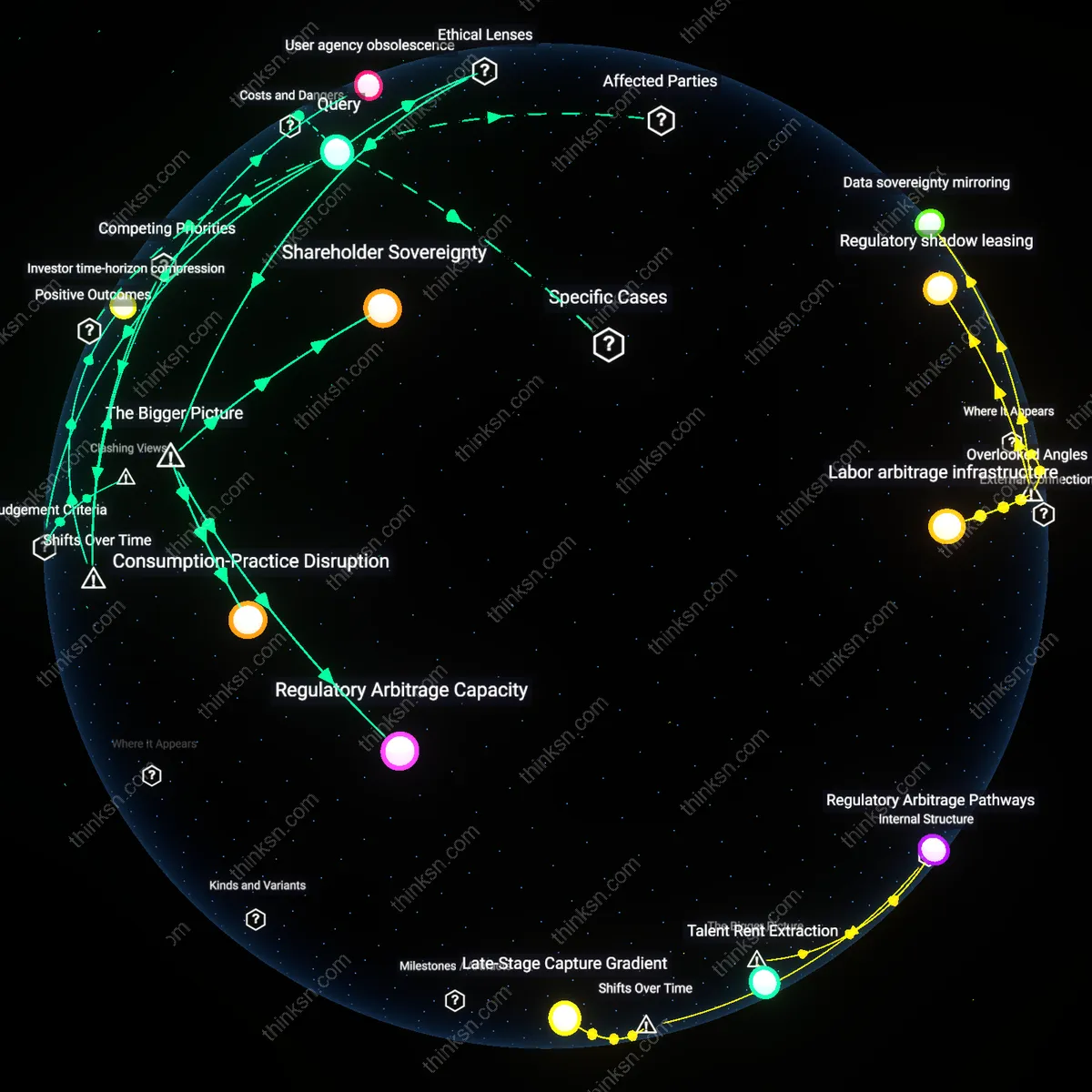
Second-Market Innovation Corridor
Nascent competitors and data-receiving platforms benefited most during the 2018–2023 window when portability requirements disrupted first-mover advantages held by dominant platforms, enabling startups like Meeco and ThinkFolio to acquire onboarding data from users migrating under GDPR or CCPA mandates. Prior to this period, new entrants faced prohibitive costs in reconstructing behavioral profiles; standardized portability lowered that barrier by enabling direct import of activity histories and identity metadata, creating a narrow but strategic corridor for innovation outside incumbent ecosystems. The underappreciated effect was not stronger user choice per se, but the creation of a de facto seedbed for alternative platforms that exploited portability as a form of data arbitrage — revealing how regulatory friction can unintentionally subsidize ecosystem diversification.
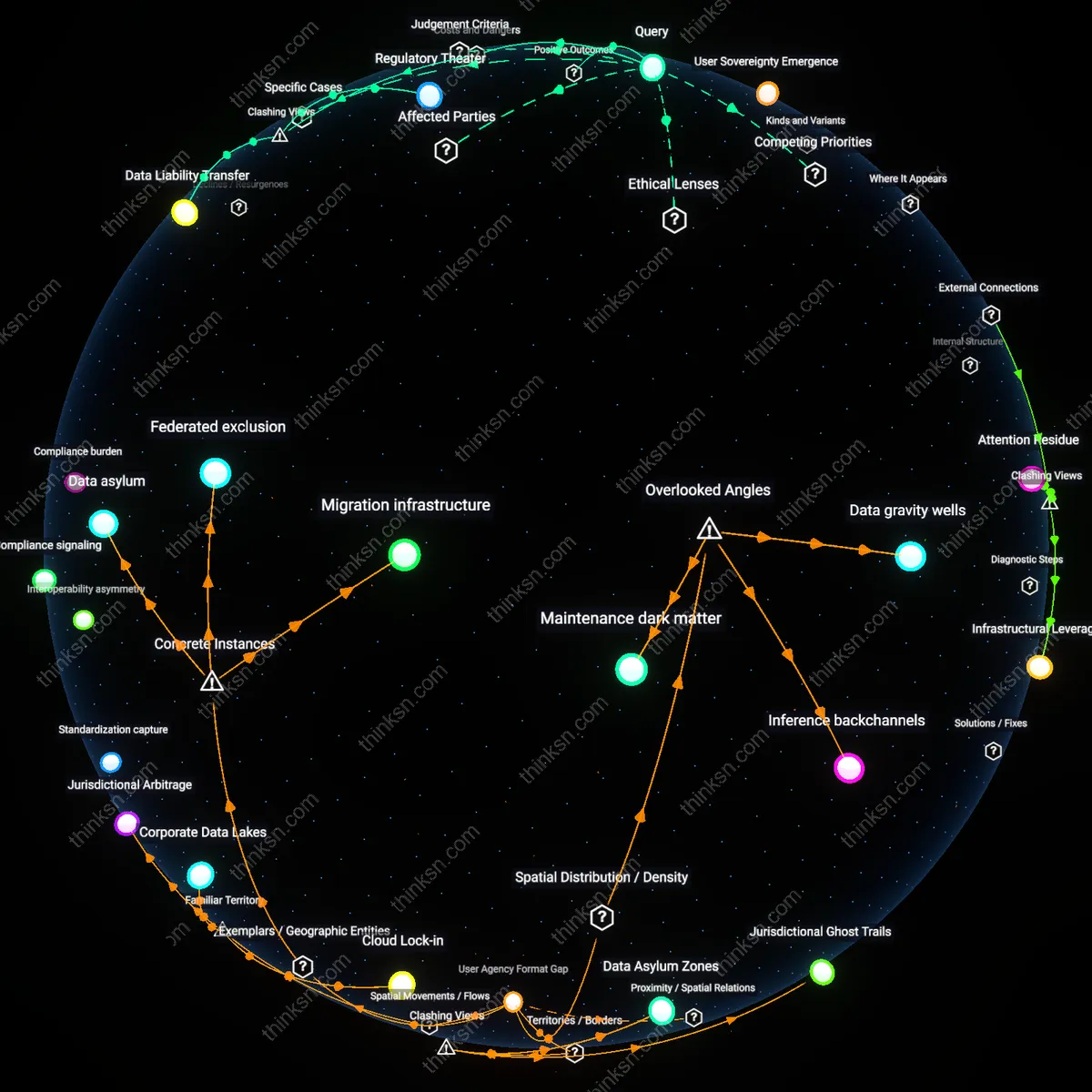
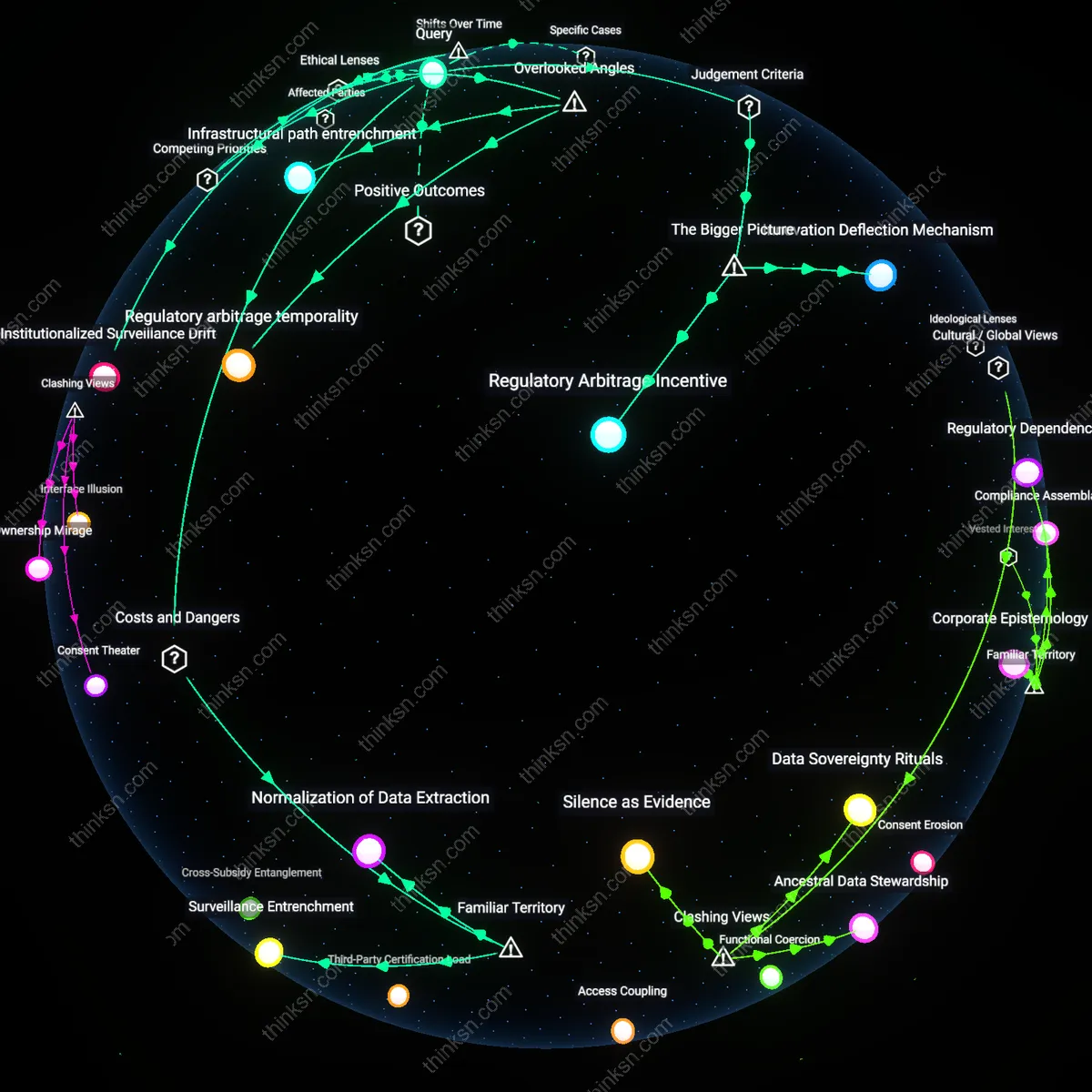
Regulatory Theater
Platform-enforced data portability standards primarily benefit regulators and large tech firms by simulating user empowerment without altering underlying data monopolies. These standards create a facade of accountability, allowing platforms to comply with minimal technical changes while deflecting structural scrutiny—such as interoperability mandates or break-up orders—through performative transparency. This dynamic entrenches incumbent advantage, as only well-resourced platforms can absorb compliance costs, thereby raising barriers to entry for true competitors. The non-obvious consequence is that user agency becomes a bureaucratic metric rather than a lived reality, serving political appeasement over material change.
Data Liability Transfer
Individual users are most harmed by platform-enforced data portability standards because they become de facto carriers of liability when required to manage, store, and transmit sensitive personal data across platforms. By shifting the operational burden of data security onto individuals—through downloadable data dumps or API-mediated transfers—platforms externalize the risks of exposure, breach, and misuse onto the least equipped actors. This reversal turns 'empowerment' into a form of coercive self-reliance, where users must navigate complex technical ecosystems without institutional support. The underappreciated danger is that portability becomes a mechanism of risk displacement, not liberation.
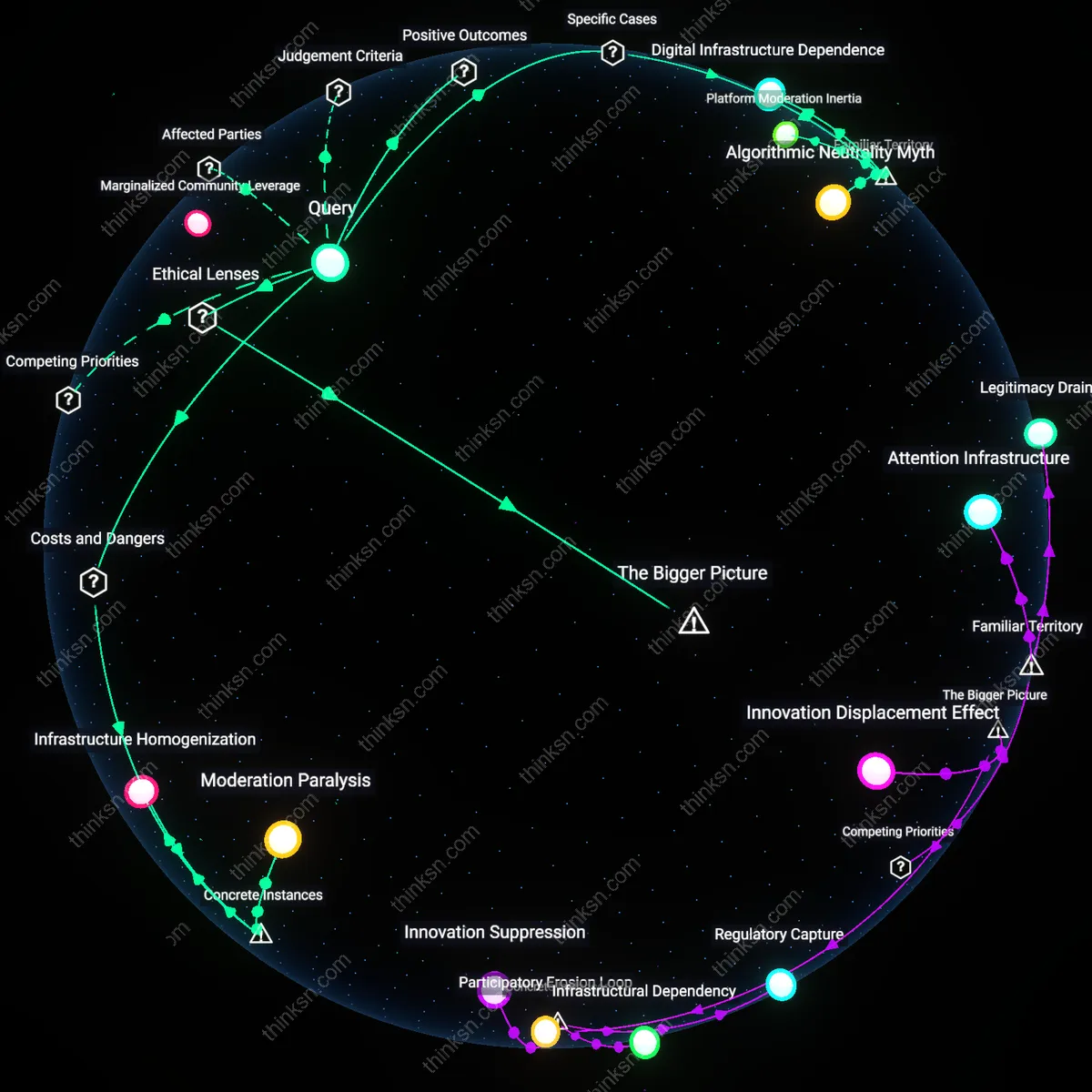
Interoperability Sabotage
Dominant platforms benefit most from narrow data portability standards because they enable selective, incomplete data sharing that mimics openness while preserving strategic control over core network effects. By releasing sanitized, non-actionable data sets—such as static message archives instead of real-time messaging access—platforms satisfy regulatory requirements without enabling true competition or user migration. This calculated incompleteness prevents emergent platforms from achieving functional parity, ensuring user lock-in persists despite formal compliance. The obscured reality is that portability, when weaponized as partial disclosure, functions as a shield against disruptive innovation.