Non-Compete Firewall
Establish a strict legal separation by ensuring no engineer signs or remains bound by enforceable non-compete agreements with the prior employer. This requires conducting jurisdiction-specific contract audits upon hiring, prioritizing engineers from regions like California where such clauses are void, and rebuilding teams around legally unencumbered personnel. The mechanism operates through labor law asymmetries across states, particularly leveraging California Labor Code §16600 to immunize mobility, which makes litigation risk transferable to the departing firm rather than the individual engineer—what’s underappreciated is that most legal threats are not about IP theft but contract breach, and preventing exposure at the employment boundary negates the most common leverage point.
Clean Room Development
Structure engineering work using a clean room protocol where former employees only interact with abstract functional specifications created by a neutral third party, not internal code or design documents from their prior firm. This mimics the legal strategy used in the 1980s Phoenix BIOS case, where reverse engineering was defensible because developers never saw proprietary code. The process isolates intent from implementation, making it impossible to claim subconscious copying—what’s overlooked in popular discourse is that intent matters less than procedural insulation, and courts weigh methodological purity more heavily than individual affiliations when infringement is alleged.
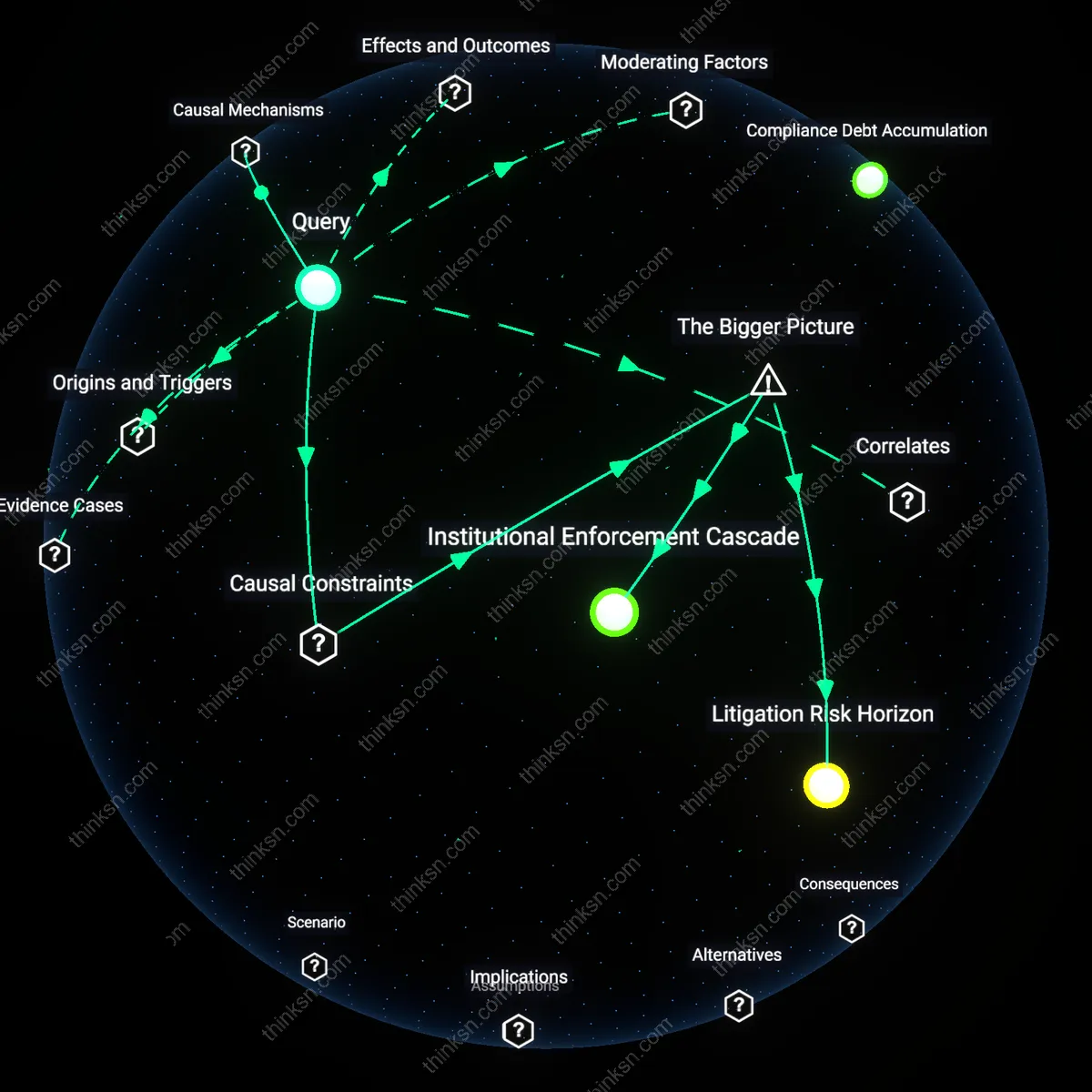
Innovation Safe Harbor
Register the venture’s core R&D activities under federal small business innovation programs like SBIR, which provide legal shielding through government-backed intellectual property frameworks and procedural legitimacy. By embedding early development within federally sanctioned research tracks, the company shifts the burden of proof onto accusers to demonstrate willful infringement, not just similarity. These programs create a de facto safe harbor by aligning the startup’s trajectory with public policy goals for technological decentralization—what’s rarely acknowledged is that legal threat deterrence often stems not from technical defensibility but from making litigation politically and rhetorically costly for dominant firms.
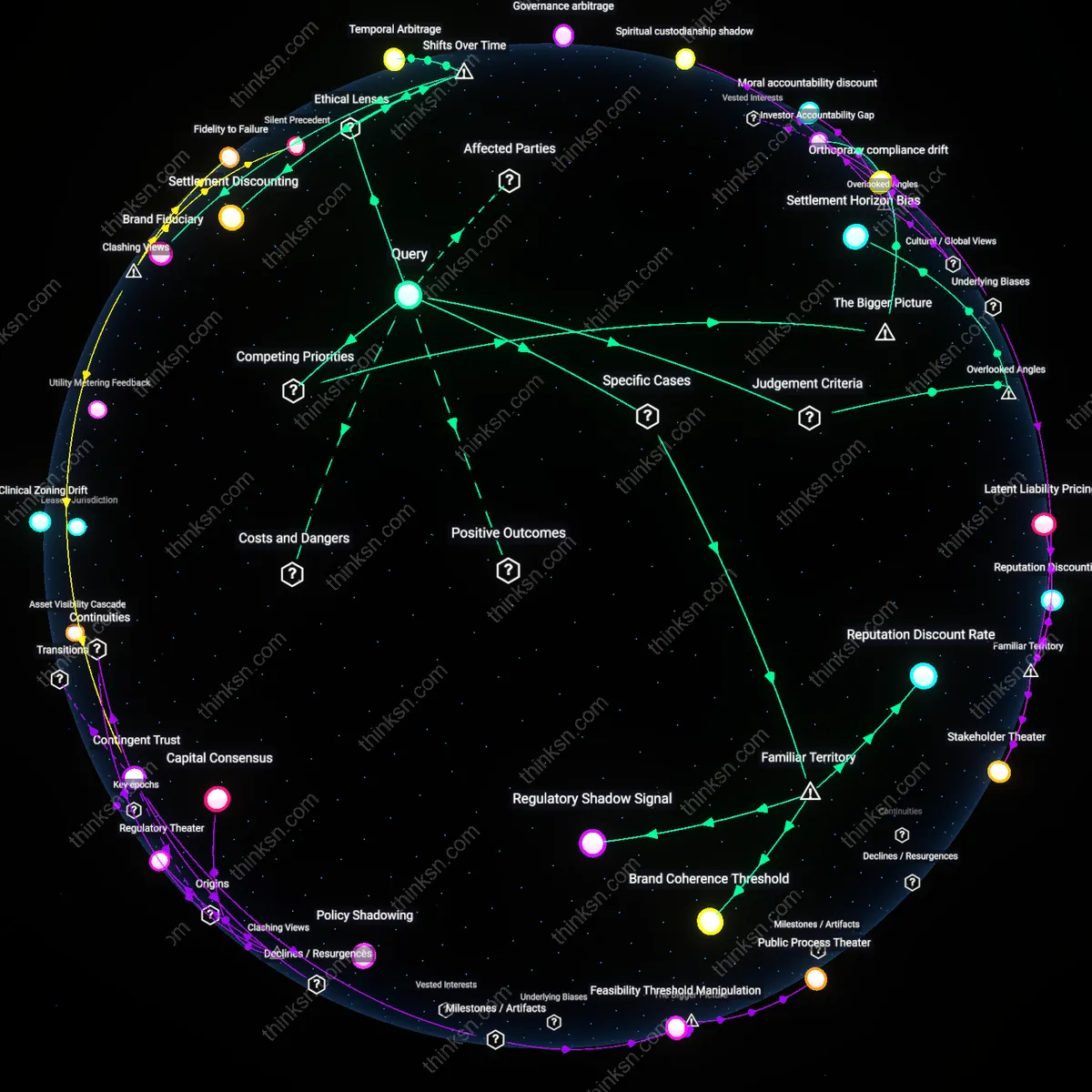
Litigation Shield Structure
A small tech company can establish a Delaware-based limited liability holding entity to isolate engineering teams from personal liability, as seen when ex-Google engineers at Niantic Labs spun out to launch Pokémon Go under a legally ring-fenced subsidiary during their transition from Alphabet; this structure absorbed early intellectual property disputes while shielding individual developers from direct litigation, revealing how jurisdictional corporate form can be weaponized defensively rather than merely as a tax or fundraising tool.
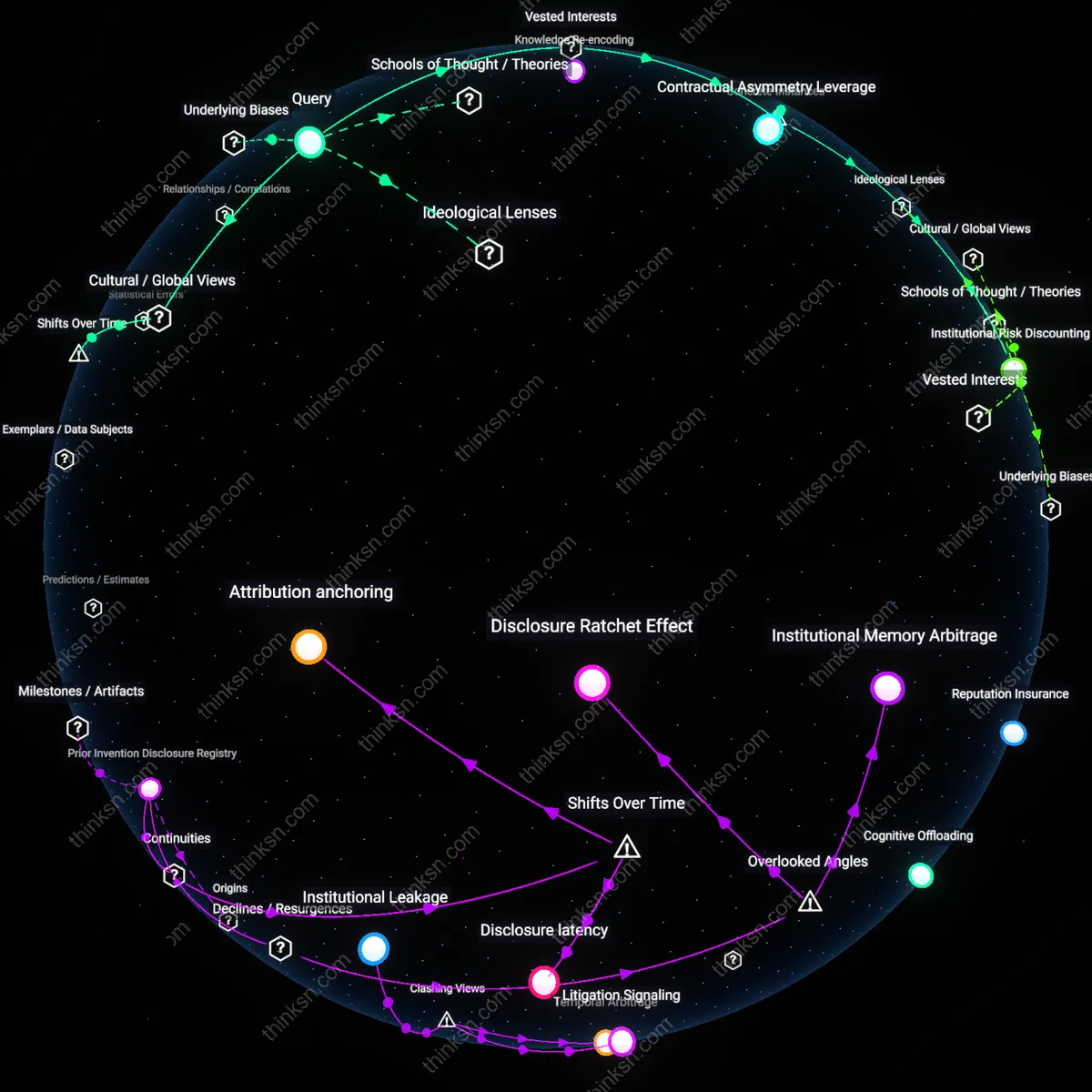
Prior Invention Disclosure Registry
Engineers can preemptively file documented, timestamped disclosures of pre-existing or independently developed concepts with third-party registries like IP.com before engaging in new ventures, as demonstrated by former Intel engineers at startup company Ayar Labs who used public disclosure logs to neutralize Broadcom’s claims of trade secret misappropriation; this created a verifiable chain of provenance that shifted the burden of proof onto the dominant firm, exposing how asymmetric transparency can disrupt legal aggression based on ambiguity.
Collective Legal Escrow
Startups can join sector-specific legal defense pools like the Open Invention Network (OIN), where members such as ex-Microsoft engineers at Reactivated Corp contributed patented tools in exchange for mutual indemnification, effectively dissuading litigation from dominant players like Oracle in post-employment ventures; this mutualized risk mechanism transforms legal exposure into a shared infrastructure, illustrating how collective ownership models can invert power asymmetries in IP enforcement.
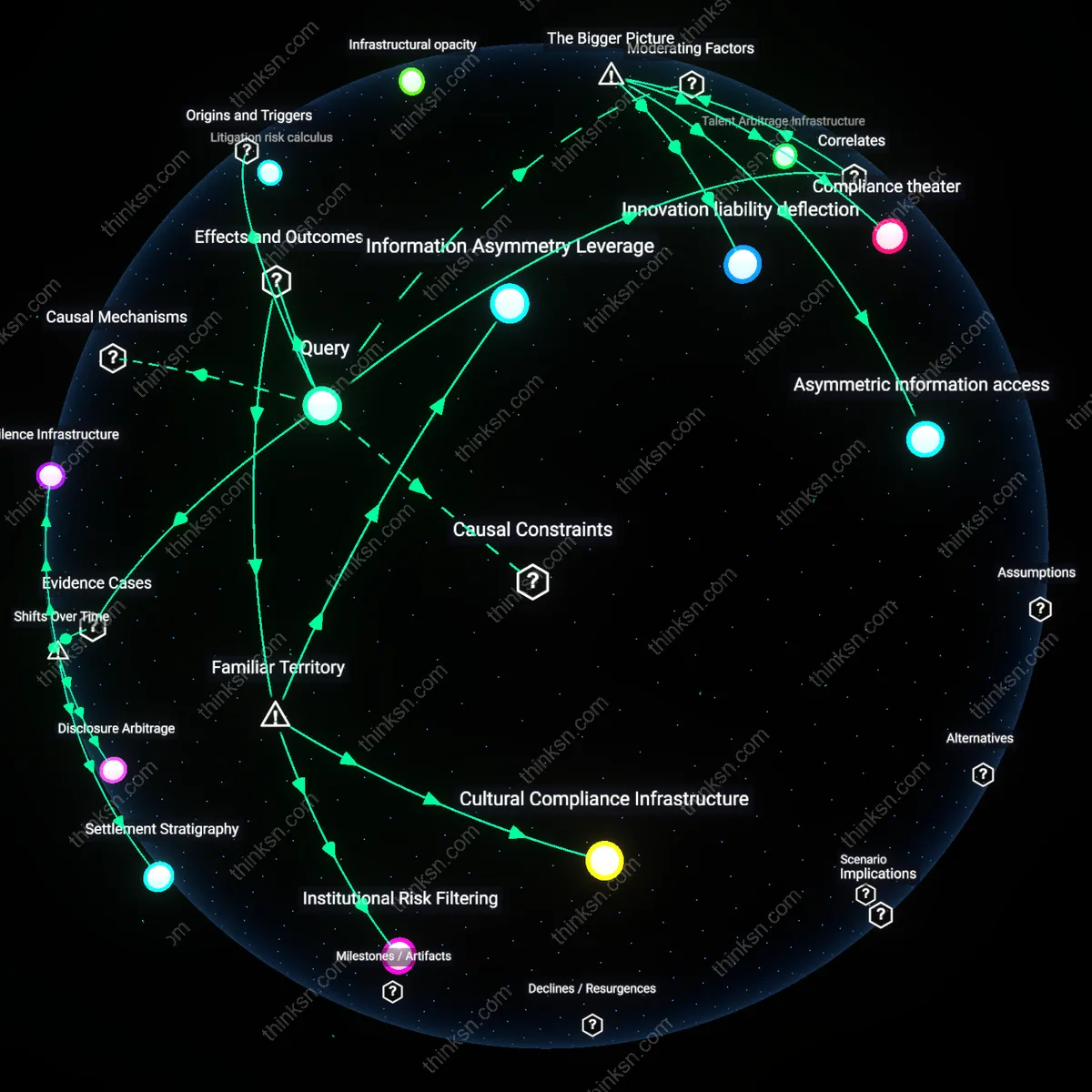
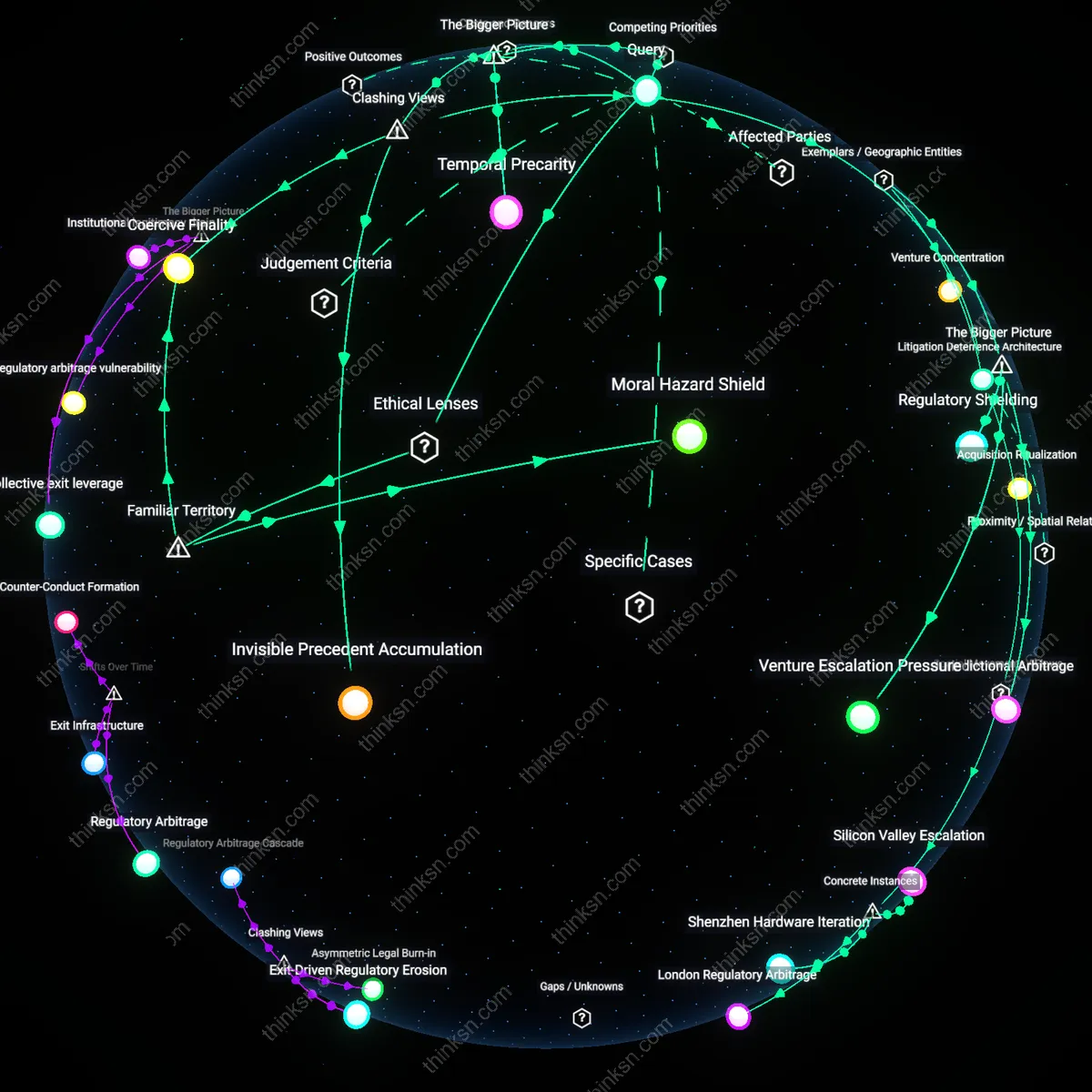
Litigation Arbitrage
A small tech company should relocate engineering teams to jurisdictions with favorable whistleblower and anti-SLAPP protections to shield them from legal threats after departing dominant firms. This strategy became viable only after the early 2000s expansion of state-level anti-SLAPP laws in the U.S., particularly in California and New York, which created asymmetric legal terrain where speech in the public interest could be defended at early stages of litigation, reducing the cost of being targeted by former employers. The mechanism operates through jurisdictional forum selection and preemption of intellectual property claims that lack public harm, exploiting a historical shift from uniformly plaintiff-friendly IP enforcement to a more fragmented legal landscape where defensive posture can be engineered spatially. What is underappreciated is that geographic location now functions as a de facto legal shield—not just for free speech, but as a structural workaround to power imbalances in innovation ecosystems.
Temporal Discontinuity
A small tech company should delay the integration of any pre-existing technical knowledge into new products until at least one major architectural shift in the dominant firm’s platform has occurred, thereby creating plausible deniability around trade secret use. This approach leverages the historical shift in software development cycles post-2010, where the acceleration of cloud-based deployment and microservices has fragmented platform coherence, making it analytically possible to distinguish between general skill and specific implementation. The mechanism functions through temporal lag—intentionally designing around post-transition states of the incumbent’s tech stack, not the one the engineers actually worked on—turning the rhythm of technological change into a protective buffer. The non-obvious insight is that time itself, structured by industry-wide upgrade cycles, has become a legal asset rather than just an operational constraint.
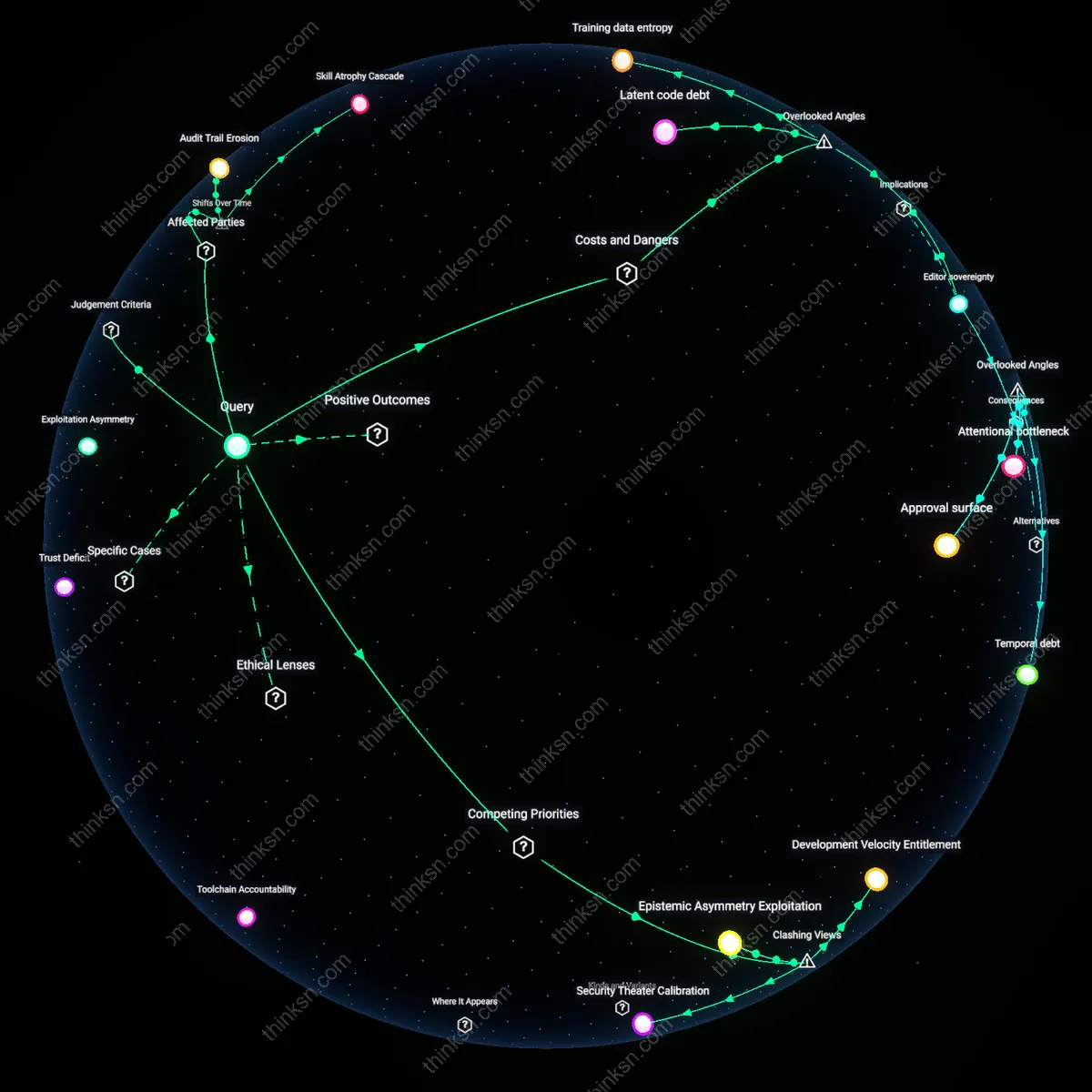
Knowledge Re-encoding
A small tech company should institutionalize a process where all departing engineers’ expertise is re-expressed through open-source simulations or synthetic training environments before being applied in new development. This emerged as a strategic possibility only after the mid-2010s maturation of model-based design tools like Jupyter, Git, and CI/CD pipelines, which allow the transformation of tacit, experience-born knowledge into auditable, version-controlled artifacts with documented provenance. The system operates by converting memory-dependent engineering decisions into traceable algorithmic workflows that can be legally distinguished from stolen trade secrets, exploiting a shift from knowledge-as-possession to knowledge-as-process. The underappreciated reality is that the legal value of engineering insight now depends less on its origin than on the form in which it is re-embedded into new technical systems.