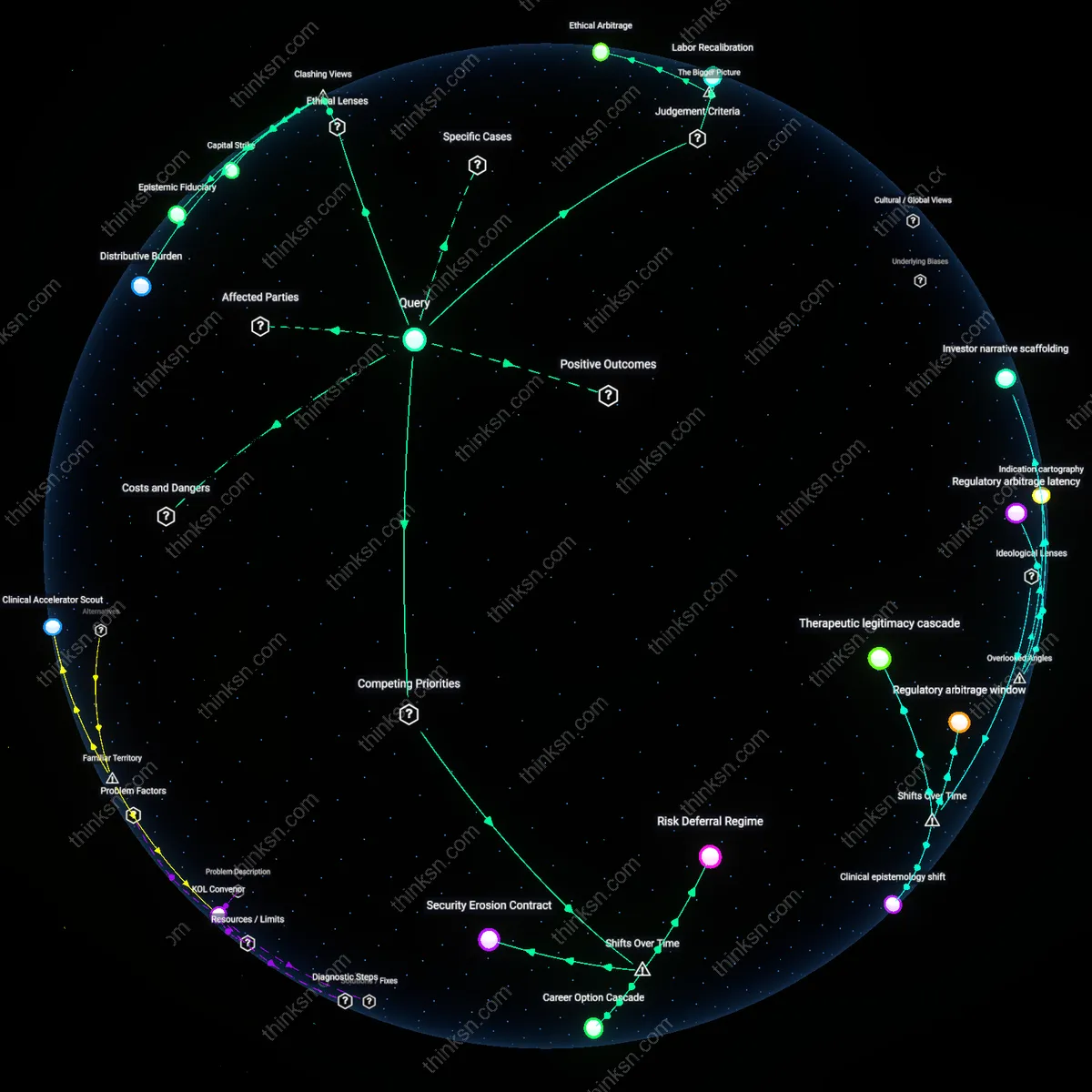
Biometric Login Convenience vs State Backdoor Risks?
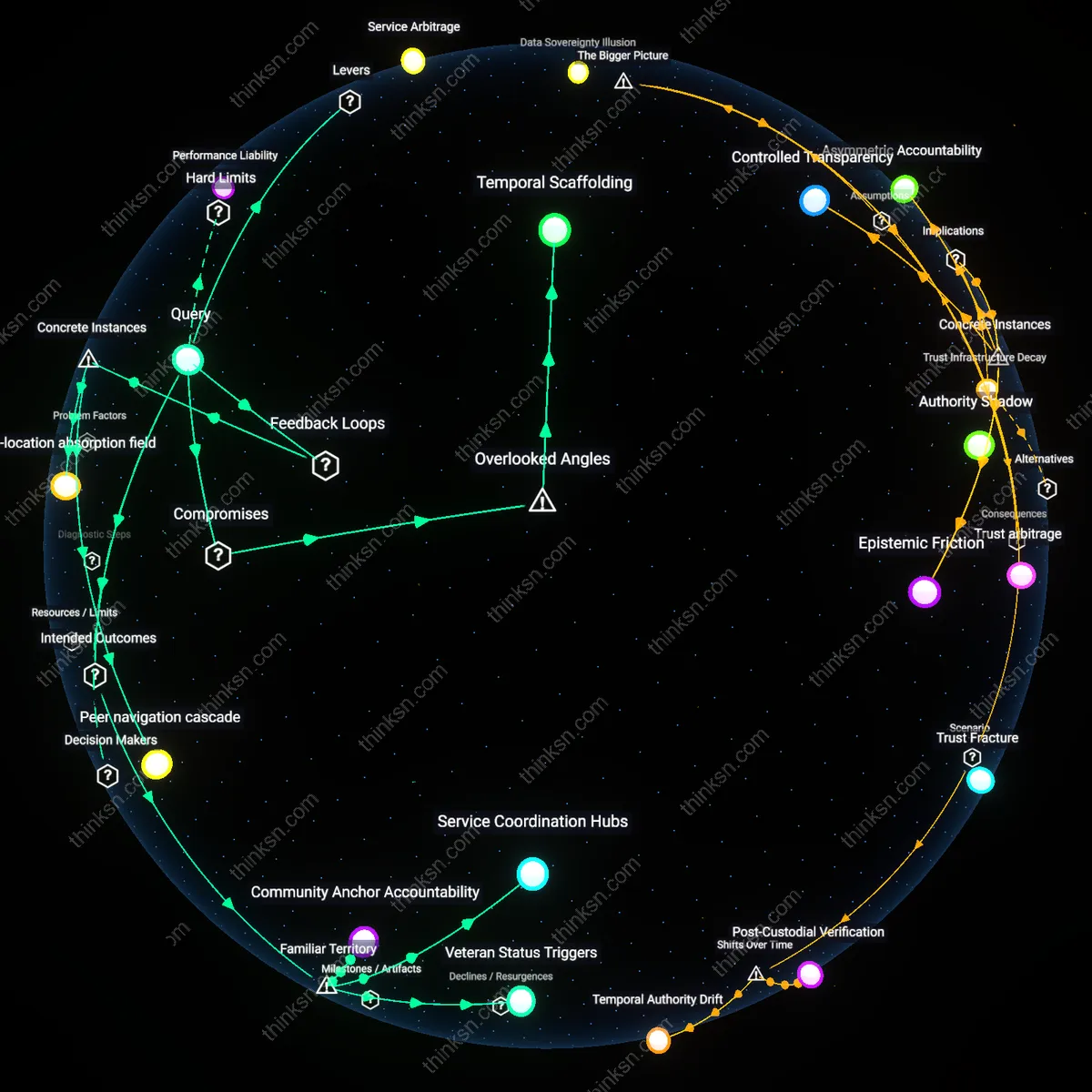
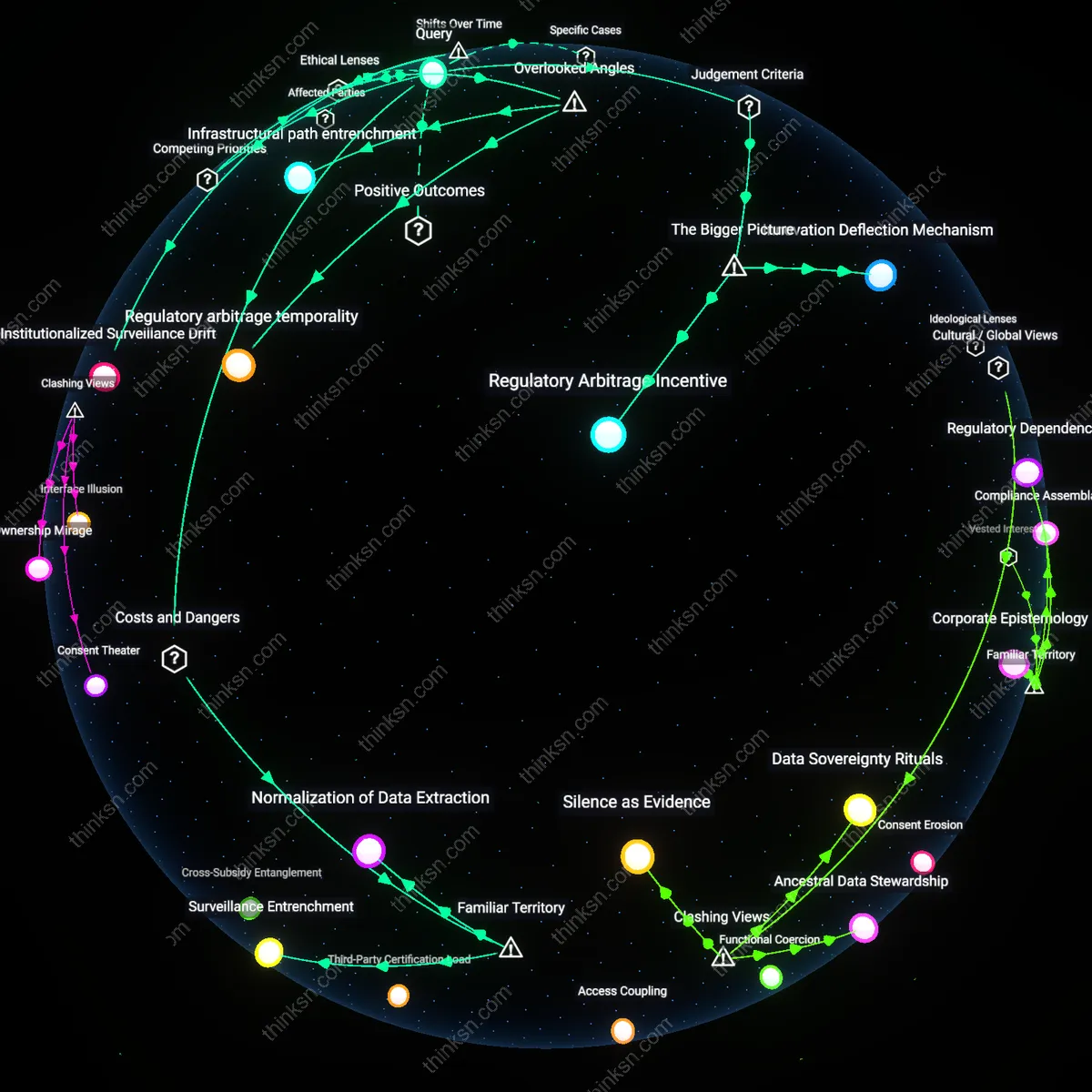
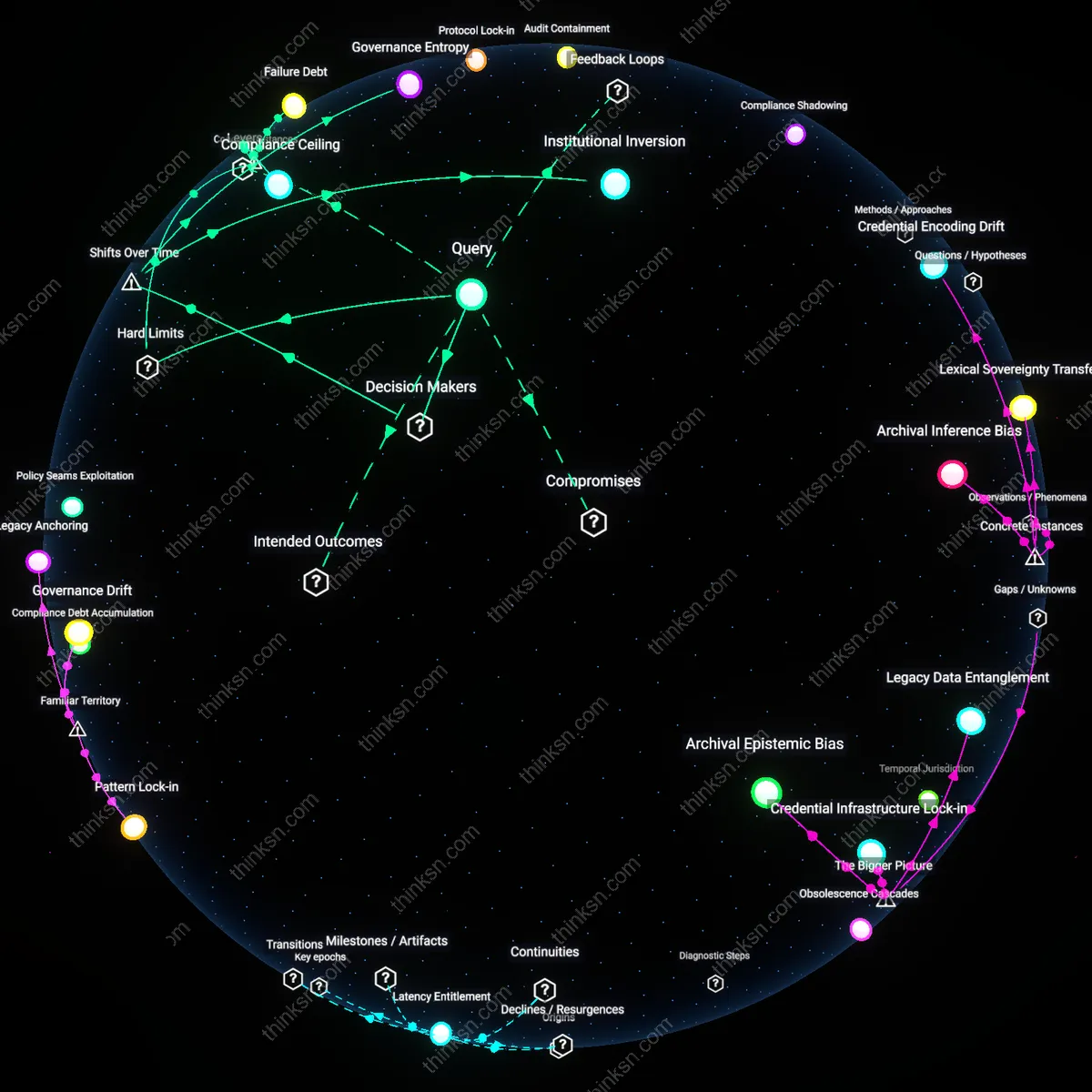
Analysis reveals 12 key thematic connections.
Key Findings
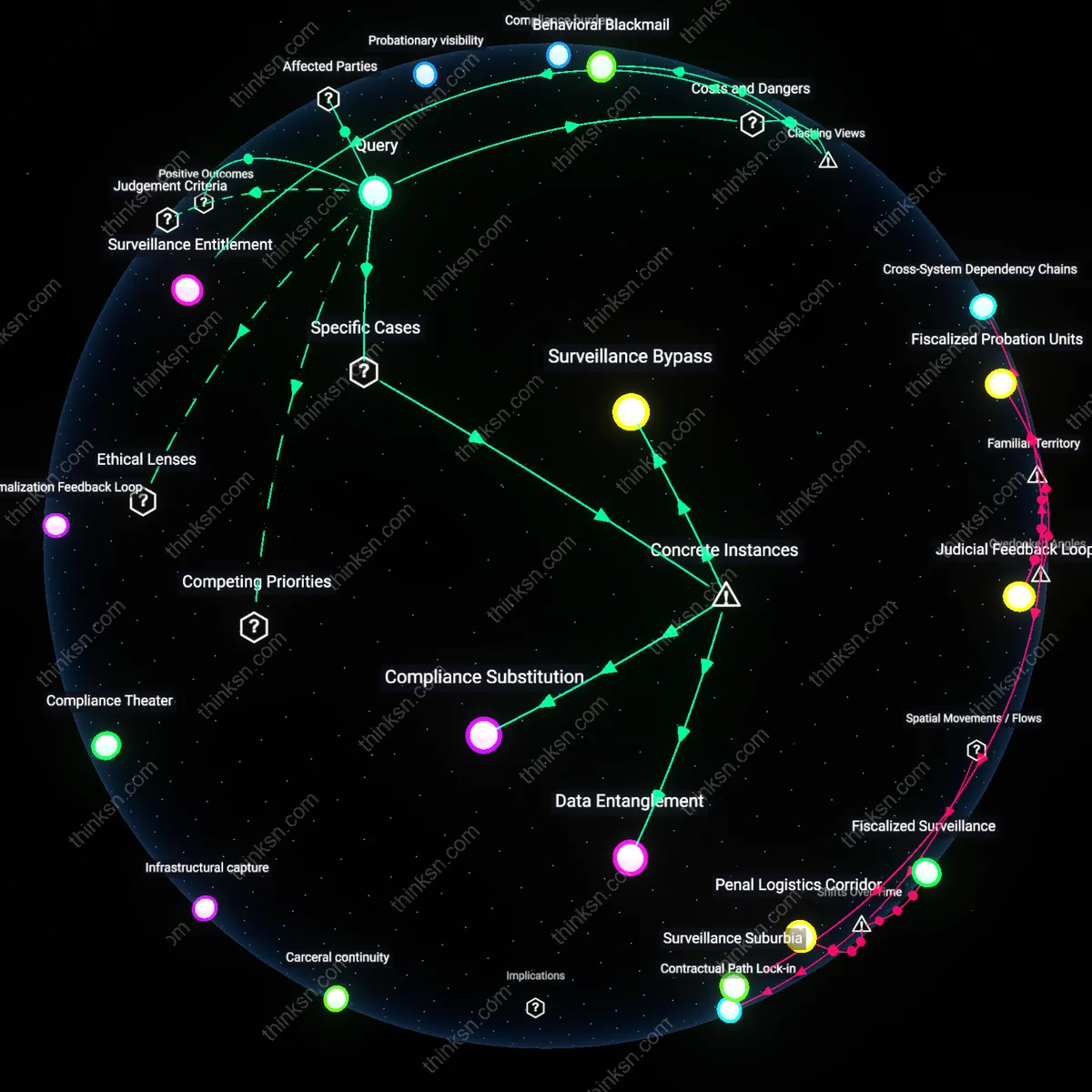
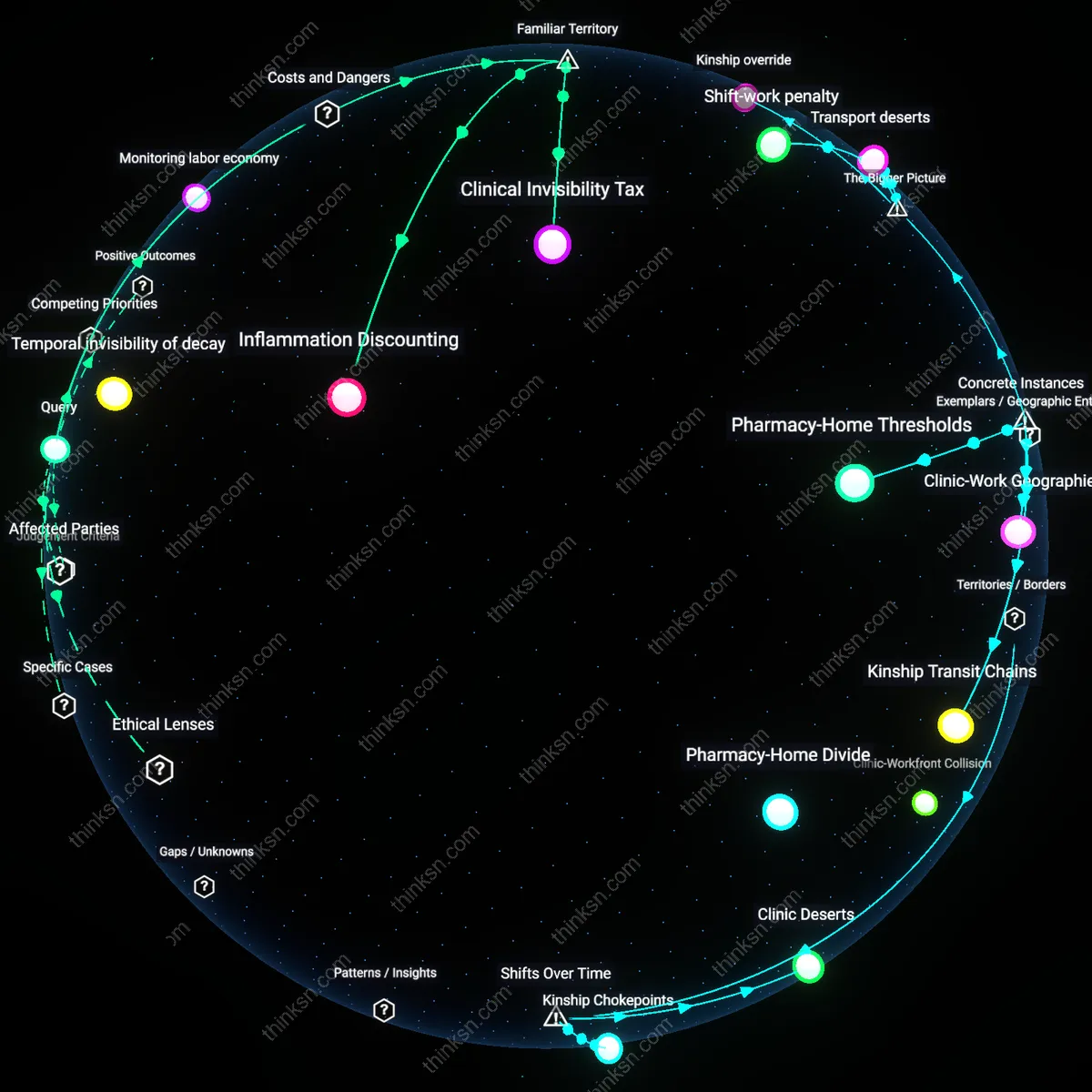
User Autonomy Erosion
Prioritize personal control over biometric data by rejecting default enrollment in state-linked authentication systems. Individuals surrender irrevocable bodily identifiers to platforms where opting out is structurally difficult, especially when governments integrate facial or fingerprint recognition into national ID, welfare distribution, or voting access—systems that marginalize those without digital fluency or stable documentation. The non-obvious risk under familiar concerns about hacking is not data theft alone, but the normalization of continuous identity verification as a condition of civic participation.
Institutional Trust Asymmetry
Rely on independent oversight bodies to audit biometric systems used by law enforcement and border agencies. The public commonly fears ‘big brother’ surveillance, yet fails to distinguish between data collection and operational access—critical because agencies like the FBI or EU member state police often possess legal authority to compel tech firms to alter authentication protocols during emergencies. What remains underappreciated is that trust is not in the technology but in the procedural durability of institutions meant to constrain its misuse.
Technological Lock-In
Resist widespread deployment of biometric infrastructure in developing economies funded by foreign tech partnerships. Governments in regions like Southeast Asia or East Africa are incentivized by convenience and modernization branding to adopt turnkey systems from firms like Clearview AI or Huawei, embedding proprietary algorithms that later become indispensable to public services. The overlooked consequence is not immediate abuse but the long-term inability to enforce accountability, as switching costs and data dependency neutralize regulatory sovereignty.
Security Paradox
Mandating biometric backdoors in India’s Aadhaar system compromises individual privacy under the guise of national security, exposing how state-controlled authentication infrastructures prioritize surveillance efficiency over citizen autonomy. The Unique Identification Authority of India (UIDAI) links biometric data to over 1.3 billion residents for seamless service access, yet court-sanctioned exceptions for intelligence agencies create irreversible exposure to function creep. This reveals the non-obvious reality that convenience-enabled scale becomes a vulnerability vector when legal safeguards lag behind technical deployment, making centralized biometrics a tool of control rather than protection.
Trust Centralization
Apple’s refusal to unlock the 2015 San Bernardino shooter’s iPhone illustrates that corporate custodianship can serve as a check against state overreach in biometric access, anchoring security in decentralized device-level encryption. By resisting FBI demands to create a software backdoor—even for terrorism investigations—Apple upheld a principle where user trust depends on the irreversibility of technical barriers. This case underscores the underappreciated role of private firms as de facto privacy institutions, where market reputation becomes a stronger deterrent against abuse than legislative oversight in digital identity ecosystems.
Informed Inaccessibility
In Estonia’s e-Residency program, widespread adoption of digital ID cards with biometric elements persists despite public awareness of state-mandated access protocols, revealing that perceived administrative efficiency can suppress critical scrutiny of privacy trade-offs. The Estonian government maintains legal authority to access encrypted identities during ‘national emergencies,’ yet civic trust in digital governance dilutes resistance to potential surveillance. This exposes the non-obvious dynamic that high-functioning digital states don’t need coercive enforcement—habitual convenience fosters passive consent, making transparency less effective than structural accountability in preserving autonomy.
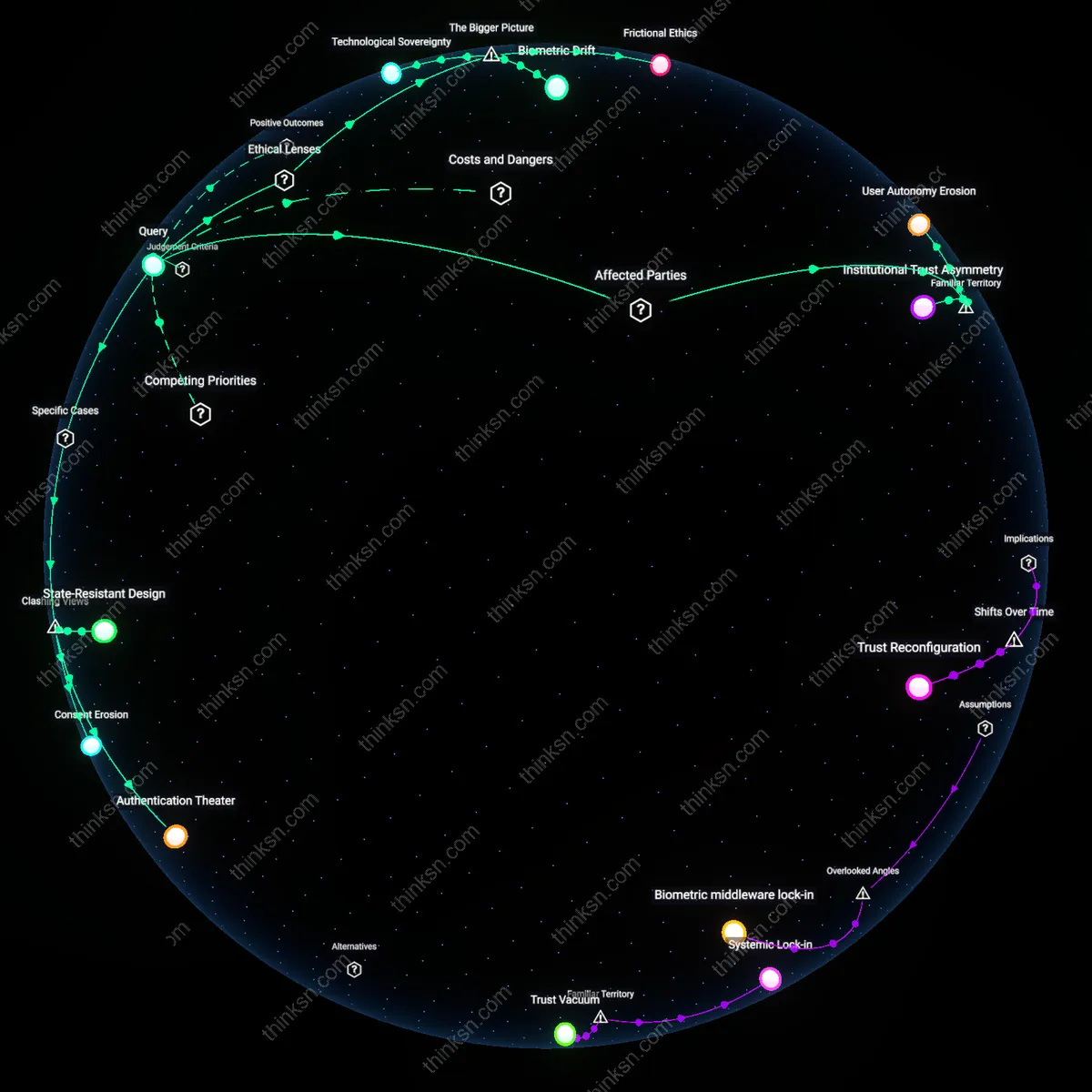
Technological Sovereignty
One should prioritize resistance to password-less biometric systems when states assert control over authentication infrastructure because such mandates enable systemic surveillance through centralized identity monopolies, exemplified by India’s Aadhaar-linked digital coercion where state actors compel biometric enrollment to access basic services. The state’s claim to secure identity authentication becomes a mechanism of exclusion and social control, not merely a security enhancement, which reveals the underappreciated risk that biometric convenience becomes an instrument of political compliance enforced through infrastructural dominance rather than explicit legislation.
Frictional Ethics
One should preserve intentional inefficiencies in authentication by rejecting frictionless biometric systems because the very inconvenience of passwords functions as a privacy-preserving social norm supported by liberal theories of negative liberty and the right to anonymity. As seen in post-Snowden EU data protection reforms, deliberate friction counters the normalization of constant authentication, disrupting the data aggregation that fuels state and corporate profiling—highlighting the non-obvious reality that usability and security are not inherently aligned, but often exist in moral tension when systemic power favors seamless surveillance.
Biometric Drift
One should reject long-term reliance on biometric authentication because immutable biological identifiers become permanently compromised across generations of state data systems, as demonstrated by China’s expansion of its Social Credit System using repurposed public security biometrics, where initial convenience enables unforeseen downstream policy applications. This creates a path dependency in which revocation becomes impossible, not due to technical failure but institutional inertia, exposing the underappreciated reality that biometric data, once collected, acquires a political afterlife beyond its original context.
State-Resistant Design
Biometric backdoors should be treated as inevitable, not hypothetical, making the best defense a technical architecture that denies centralized extraction, as seen in Apple’s refusal to create a custom iOS build for the FBI in the 2016 San Bernardino case; the mechanism here is not legal resistance but the strategic placement of cryptographic trust in-device, which prevents even the manufacturer from complying with state access demands, revealing that the real privacy safeguard is not policy but unyielding technical constraint—this flips the intuitive view that legal or procedural safeguards are primary by showing that only designs immune to state coercion offer lasting protection.
Authentication Theater
The convenience of biometrics falsely equates security with legitimacy, as demonstrated by India’s Aadhaar system, where biometric authentication enables mass service delivery but has been routinely bypassed via spoofing or insider access, yet the state continues to expand its use despite known vulnerabilities; the system operates through institutional inertia and perceived control, not actual security, exposing that biometrics often serve as performative assurance rather than robust protection—this challenges the dominant narrative that biometric adoption reflects technological progress by revealing it as a ritual of governance that prioritizes visibility over integrity.
Consent Erosion
Once biometric data is embedded in critical infrastructure, opting out becomes functionally impossible, as seen in Estonia’s digital state ecosystem where e-residency and biometric ID are prerequisites for banking, voting, and healthcare, effectively nullifying consent under the guise of efficiency; the mechanism is infrastructural lock-in, where convenience creates dependency that preempts future refusal, turning privacy into a transient choice rather than an ongoing right—this contradicts the liberal assumption that users retain agency over their data by showing that consent is structurally dissolved through seamless integration.