Health App Convenience vs. Risk of Dual Data Exploitation?
Analysis reveals 9 key thematic connections.
Key Findings
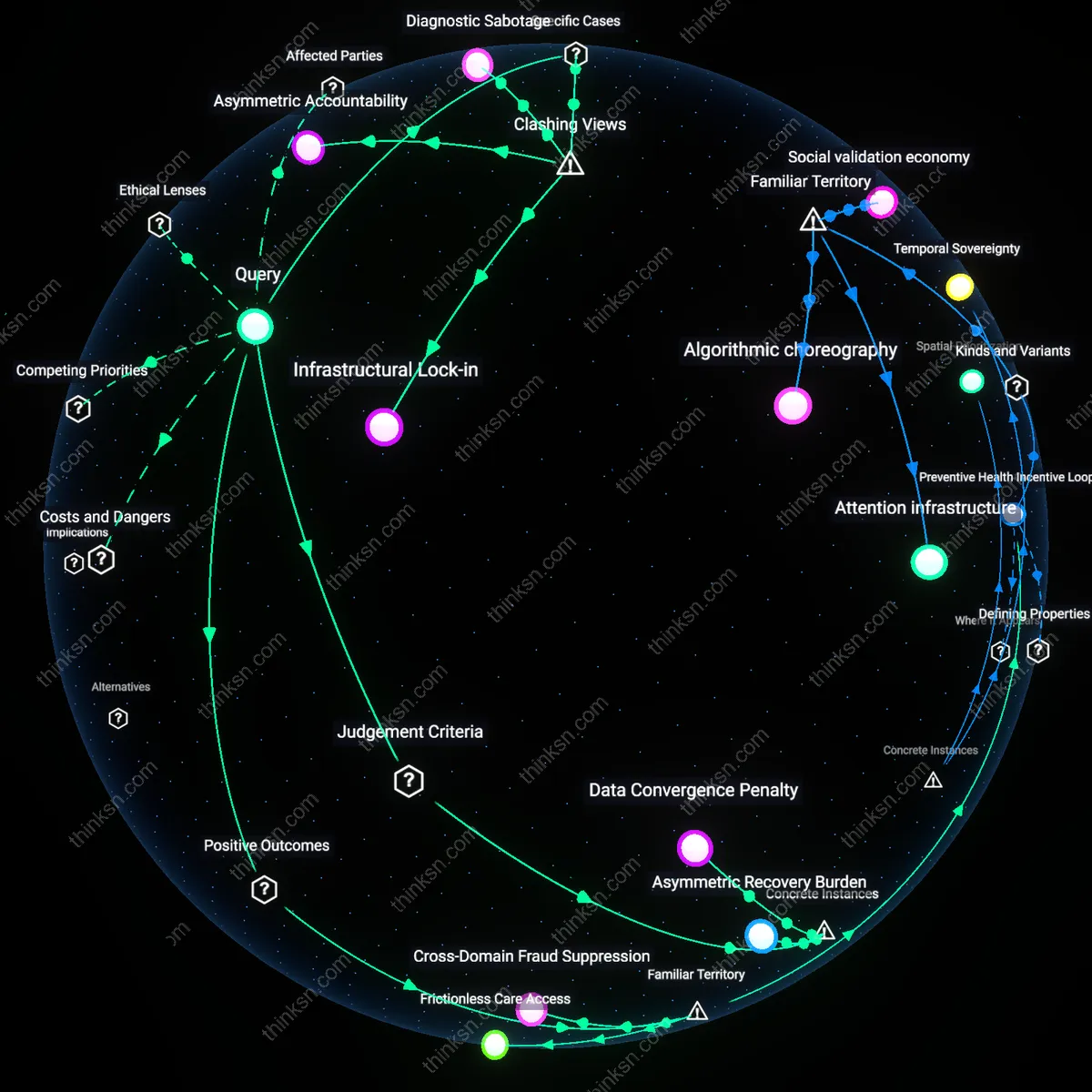
Data Convergence Penalty
The integration of health and financial data in Estonia’s national digital identity system intensifies the consequences of any single breach, as demonstrated by the 2017 security flaw that exposed over 750,000 citizen identities to potential spoofing; because authentication credentials unlock both medical records and banking functions, the attack surface is not merely additive but multiplicative, making systemic failure more severe than isolated breaches—this reveals that unified systems inherit a non-linear risk function where the combination itself becomes a vulnerability, not just the data.
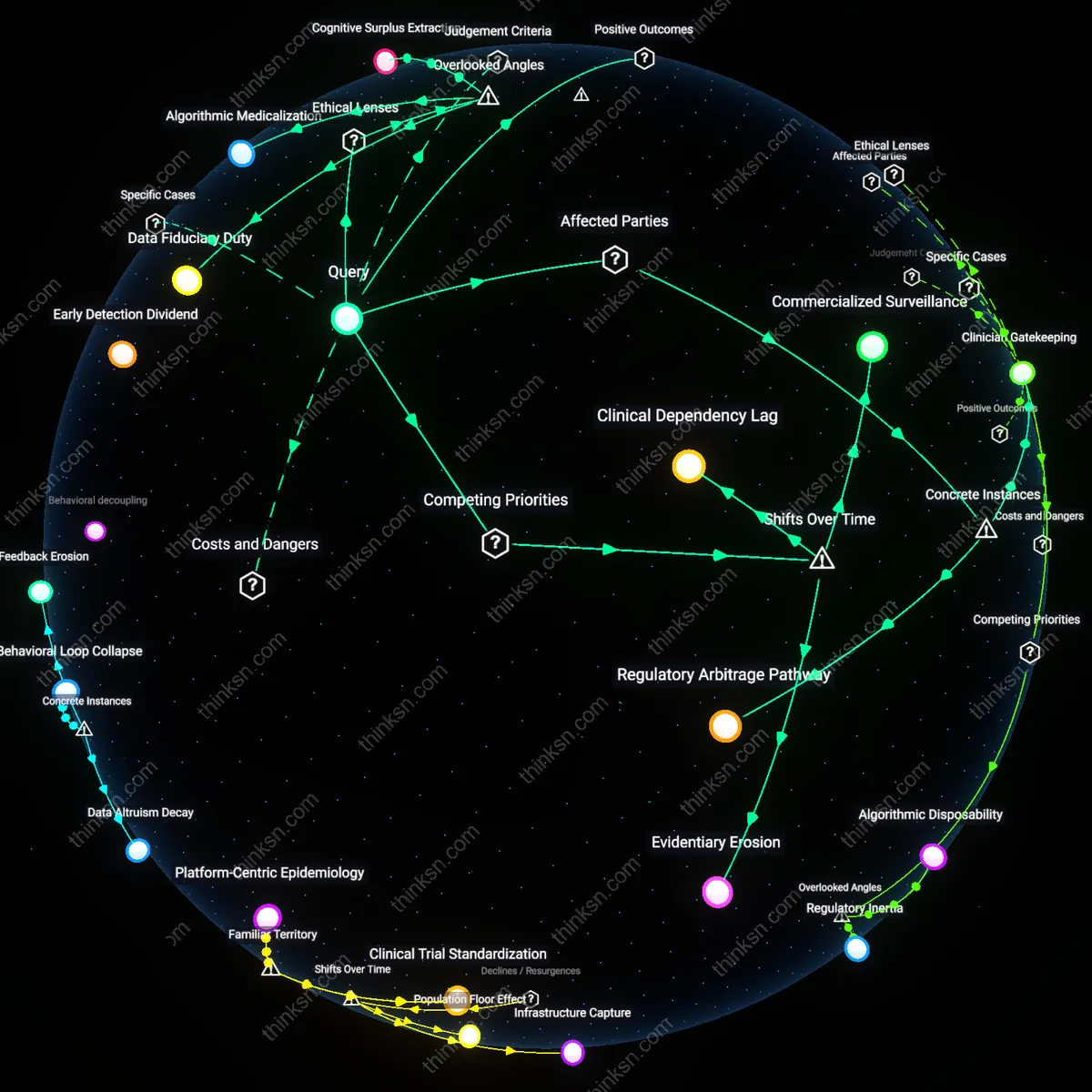
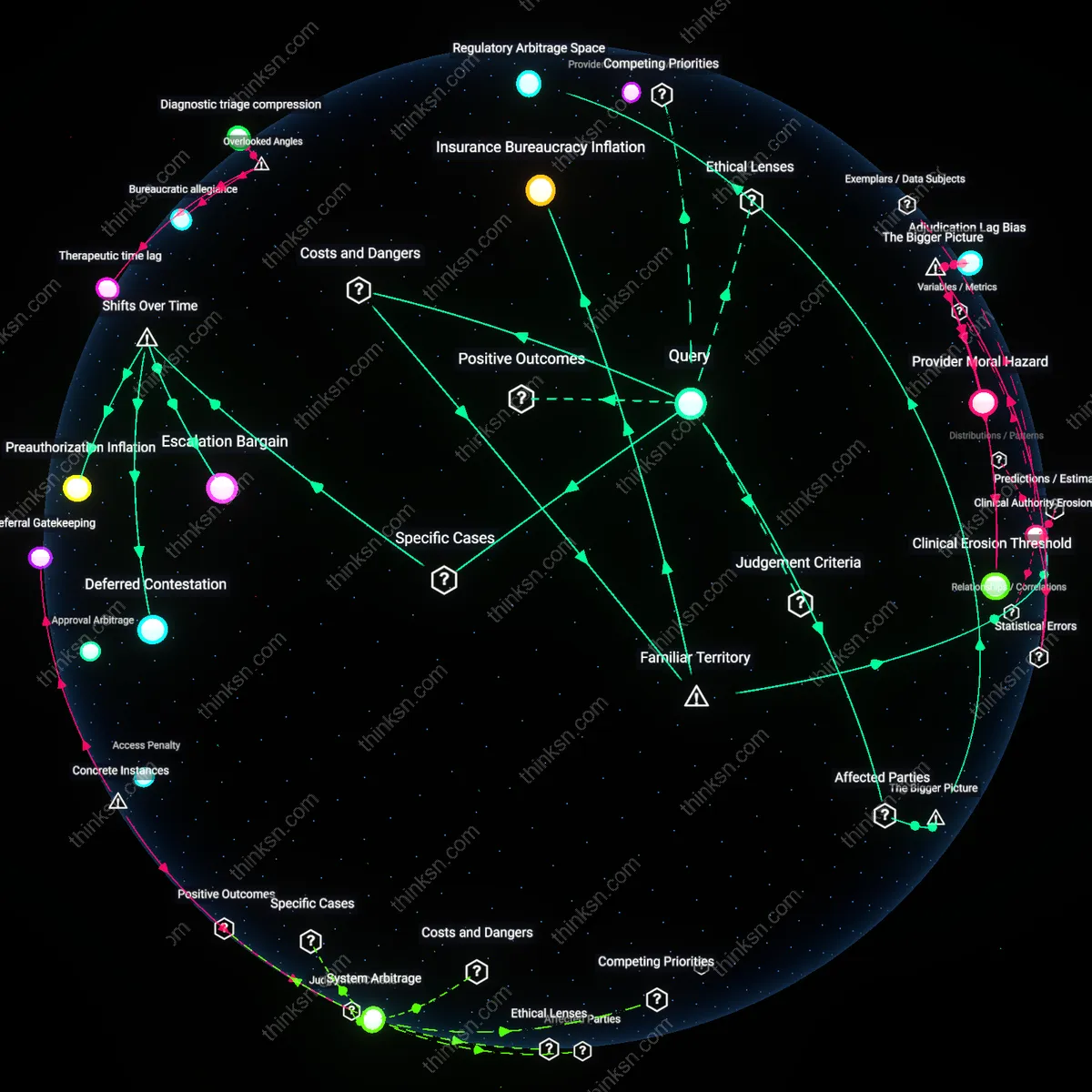
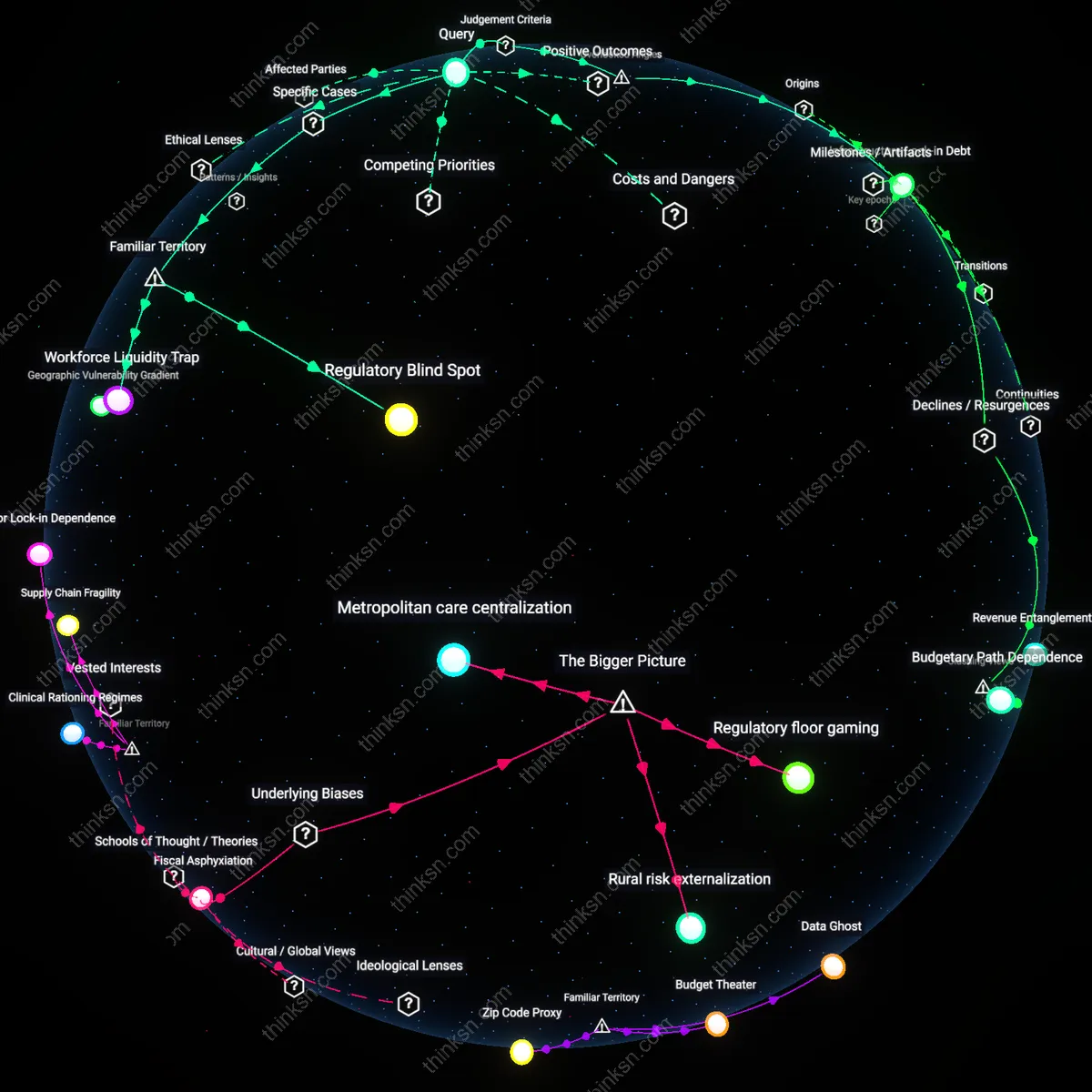
Consent Illusion
India’s Aadhaar-linked health and financial platforms create the appearance of user control through opt-in enrollment, yet the practical reality—evident in the 2018 Andhra Pradesh case where rural workers were denied wages unless biometric data was shared with private insurers—exposes how structural coercion undermines autonomy; the supposed choice to consolidate identity functions dissolves when access to essential services is conditionally tied to data centralization, revealing that procedural consent mechanisms often mask institutional compulsion.
Asymmetric Recovery Burden
When North Carolina’s Medicaid system integrated payment and clinical data in a centralized app pilot in 2022, low-income enrollees bore disproportionate costs after a 2023 breach exposed treatment histories and bank details, as they lacked resources to pursue identity recovery or credit monitoring; unlike wealthier users who could absorb remediation costs, vulnerable populations face cascading harms—from stigma to financial ruin—with limited recourse, exposing how unified systems amplify inequality in post-breach recovery, not just in breach likelihood.
Frictionless Care Access
Integrate health and financial data in a single app to immediately unlock faster medical service delivery during emergencies. When patients arrive at hospitals, authorized providers can instantly verify insurance eligibility, process payments, and retrieve critical medical history through one authenticated digital identity, reducing administrative delays that routinely worsen health outcomes—particularly in trauma or acute care settings. This integration operates through interoperable systems like HL7 FHIR APIs linked to real-time payment gateways used by U.S. healthcare networks, making time-sensitive treatment coordination significantly more reliable. While the public commonly associates app-based health tools with convenience, the underappreciated consequence is how merging identity layers transforms seconds into survivability during life-threatening episodes.
Preventive Health Incentive Loops
Use unified health-identity apps to automatically reward healthy behaviors with tangible financial benefits, driving population-wide improvements in chronic disease management. Insurers and employers in markets like Singapore and the Netherlands already deploy apps that deposit micro-savings or lower premiums when users meet fitness goals, attend screenings, or maintain medication adherence—verified through synced wearable and claims data. This feedback loop leverages familiar concepts of loyalty programs and digital banking to normalize health engagement, embedding medical responsibility into everyday financial routines. Although people readily grasp incentives tied to data sharing, the deeper shift is how these apps reframe wellness as a continuously trackable, financially tangible asset rather than episodic care.
Cross-Domain Fraud Suppression
Deploy unified health-identity apps to reduce both medical and financial fraud by creating cryptographically verified user identities that resist impersonation across hospital billing systems and banking networks. In India’s Aadhaar-linked health accounts, for example, biometric authentication has curbed duplicate insurance claims and false patient registrations, simultaneously lowering healthcare waste and preventing identity theft in linked bank accounts. This shared security infrastructure operates through national digital identity frameworks that treat personal verification as a foundational layer across services. While the public fears data aggregation as a vulnerability, the counterintuitive benefit is that centralized authentication—with strict access logs—can make unauthorized use harder than in fragmented, siloed systems that lack cross-context validation.
Infrastructural Lock-in
We should prioritize preventing unified health-identity apps not because of immediate data breach risks, but because early adoption by national programs like India’s Aadhaar-linked health stack entrenches irreversible dependency on centralized biometric and financial-identity infrastructures. The integration of Ayushman Bharat with bank accounts and hospital networks creates a path-dependent system where opting out becomes practically impossible, even after documented spoofing attacks on Aadhaar authentication—this lock-in effect makes future security reforms politically and technically infeasible. The non-obvious consequence is not breach likelihood per se, but the erosion of systemic agility to re-architect safer decentralized alternatives.
Asymmetric Accountability
The risks of combined medical and financial data breaches in unified apps should be weighed more heavily than benefits because private enforcers like UnitedHealth’s Change Healthcare—tasked with operating critical U.S. payment-clearing systems—now hold more medical-financial data than any government entity, yet face minimal liability for cascading systemic failures. When its 2024 ransomware collapse disrupted $90 billion in claims and exposed 100 million patient records, the fallout revealed how profit-driven intermediaries externalize risk while retaining control, contradicting the assumption that regulated entities inherently safeguard public data. The real danger is not the breach itself, but a structural drift toward unaccountable chokepoints masked as public utilities.
Diagnostic Sabotage
We must discount the benefits of unified health-identity apps because integration enables covert manipulation of care pathways through data linkage, as seen with Epic Systems’ widespread deployment of algorithms that prioritize payer-compatible diagnoses when financial and medical data are co-processed in its integrated Cerner platform. This fusion allows commercial logic to infiltrate clinical judgment at scale, turning supposedly neutral apps into instruments of diagnostic steering—where risk adjustment models inflate billing codes at the expense of accurate epidemiology. The underappreciated threat is not unauthorized access, but authorized, routine distortion of medical truth by embedded financial incentives.