When Telecom Immunity Means Consumer Rights Take a Hit?
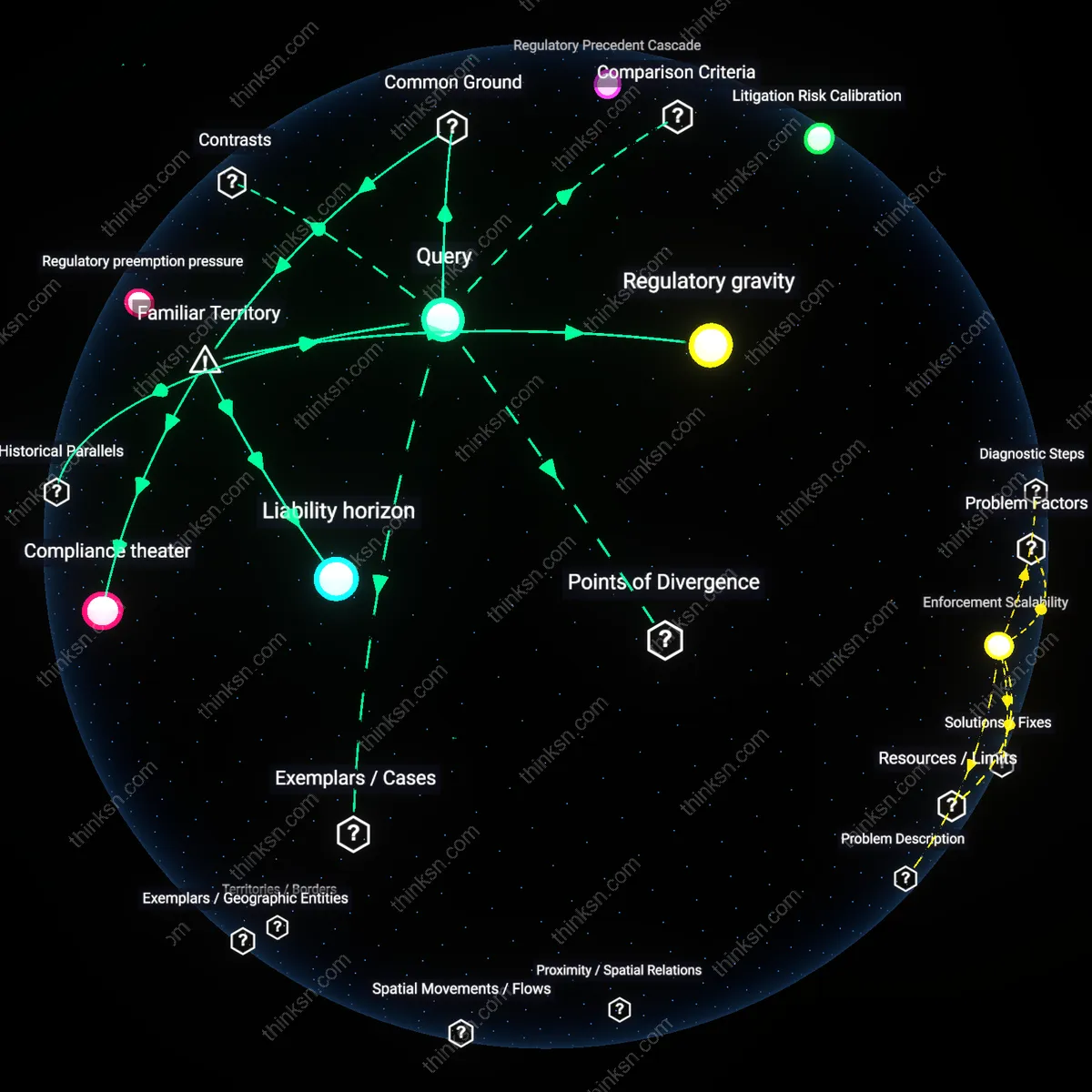
Analysis reveals 9 key thematic connections.
Key Findings
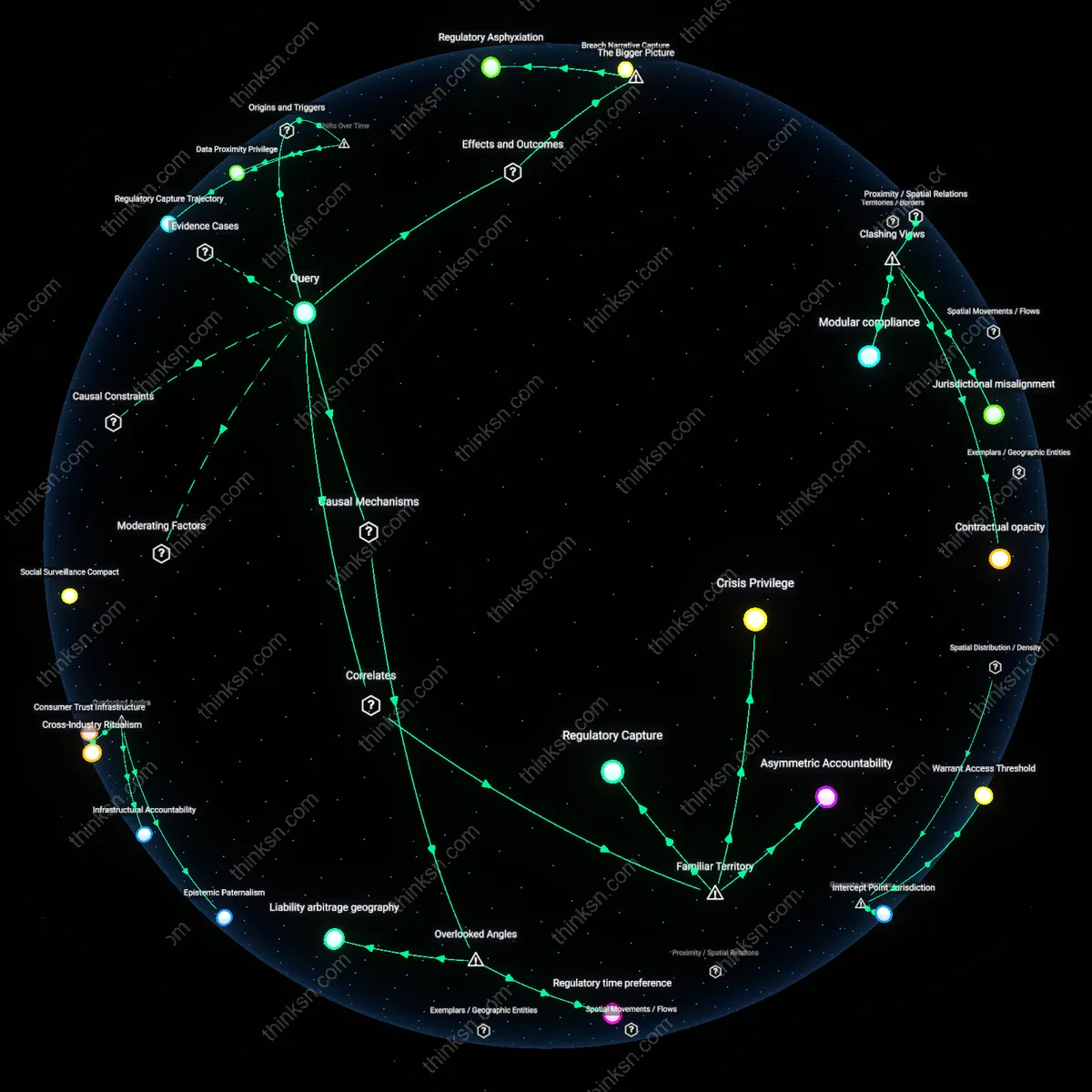
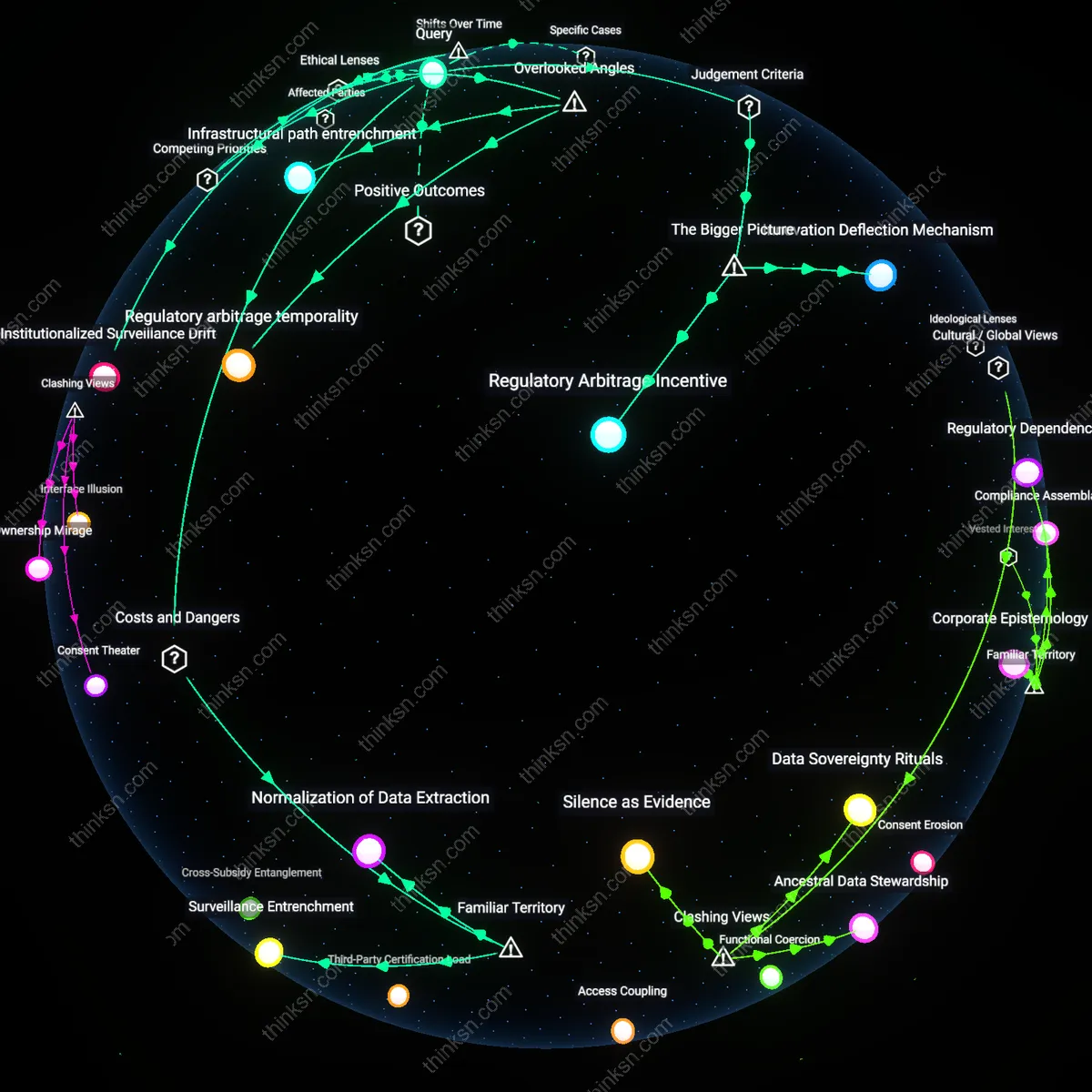
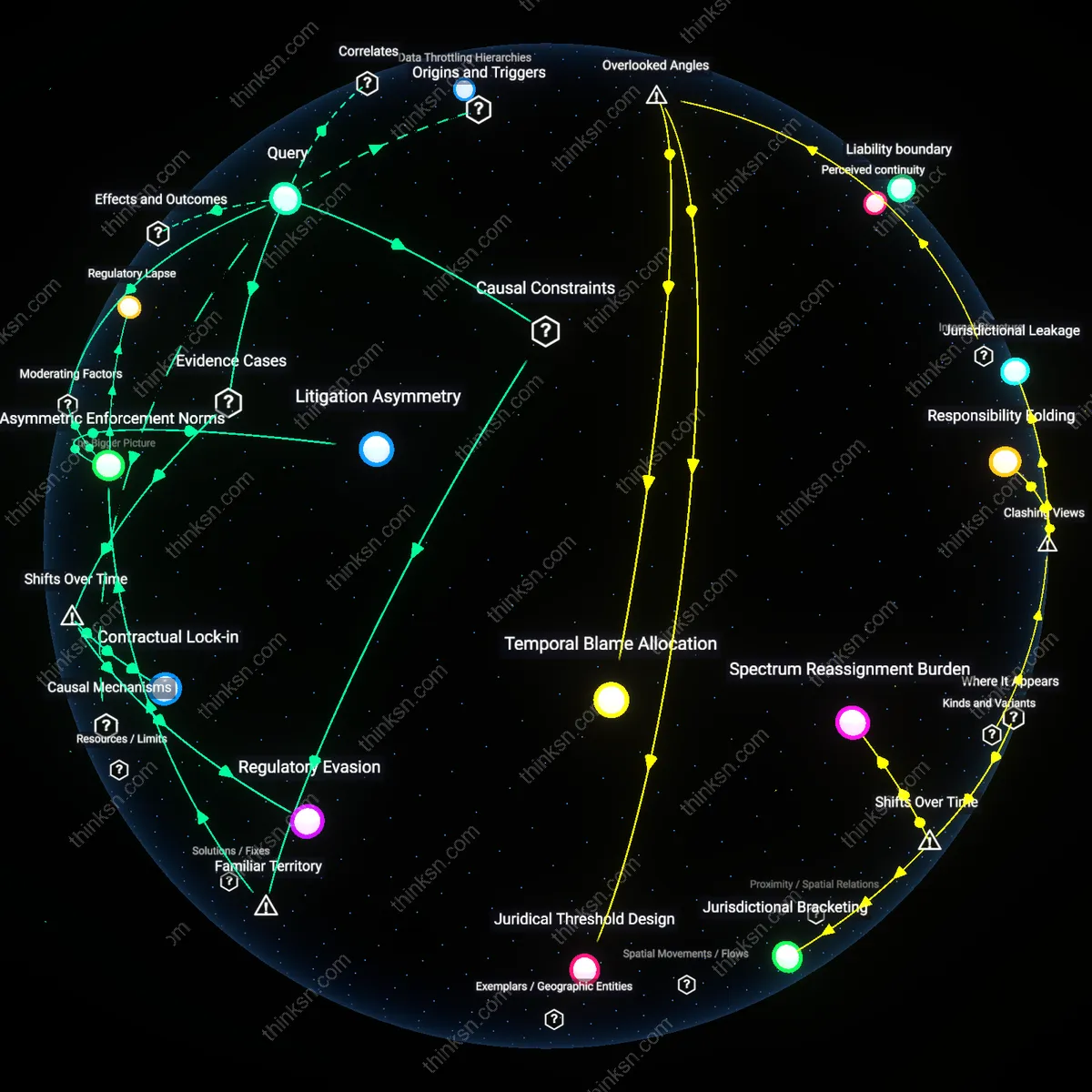
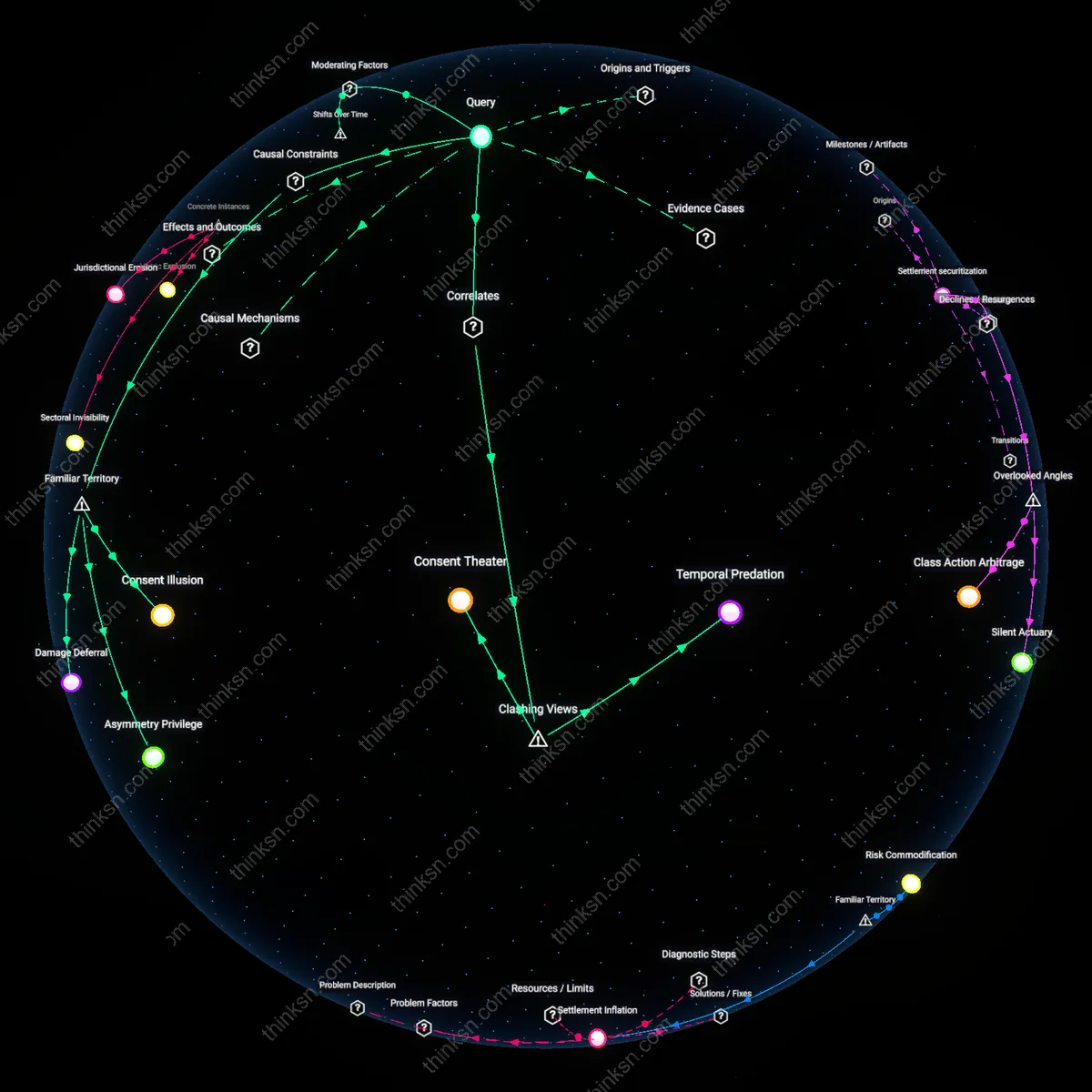
Regulatory Capture Trajectory
Fast-tracking immunity for telecom operators emerged directly from the post-9/11 expansion of state surveillance mandates, where telecoms were co-opted as de facto intelligence partners, making data-handling liabilities a secondary concern to national security continuity. This shift, cemented by the FISA Amendments Act of 2008, redefined corporate risk by legally embedding telecoms within national security infrastructure, thereby weakening consumer advocates’ ability to demand transparency. The non-obvious insight is that immunity was not a concession to industry lobbying per se, but a systemic recalibration following a security-driven rupture, where consumer rights became structurally deprioritized in lawmaking processes anchored in crisis response.
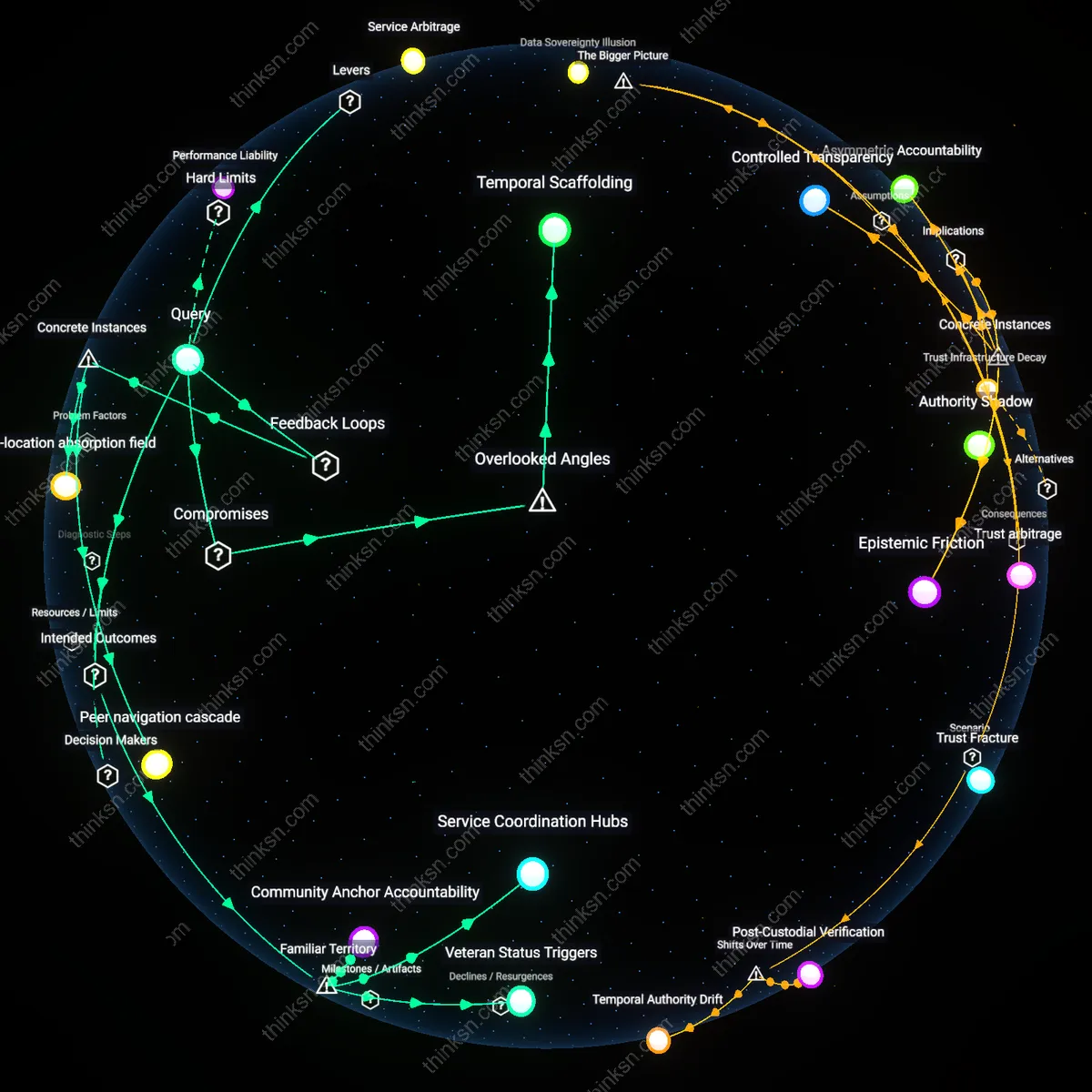
Asymmetrical Accountability Regime
The acceleration of legal protection for telecom operators in data disclosures crystallized during the 2013 Snowden revelations, when public exposure of widespread data sharing exposed a gap between corporate liability and government compulsion. In the aftermath, policymakers shielded carriers not because of static industry influence, but because the state required plausible deniability in surveillance partnerships, reframing breaches as collateral effects of state action rather than corporate failure. The underappreciated dynamic is that consumer advocates were not simply overruled—they were institutionally sidelined by a new normative framework that distributed accountability unevenly across public and private actors.
Data Proximity Privilege
The granting of expedited immunity gained momentum in the late 2010s as telecom operators became essential conduits for digital identity and real-time behavioral data, surpassing traditional service roles to function as infrastructural gatekeepers. As 5G deployment and IoT integration magnified the strategic value of network-level data access, regulatory timelines favored telecoms to ensure uninterrupted data flows favorable to both state monitoring and market scalability. The overlooked shift is that immunity is less about past breach management and more about preemptively securing proximity to data streams, privileging firms that are now structurally indispensable over consumer claims rooted in individual consent or redress.
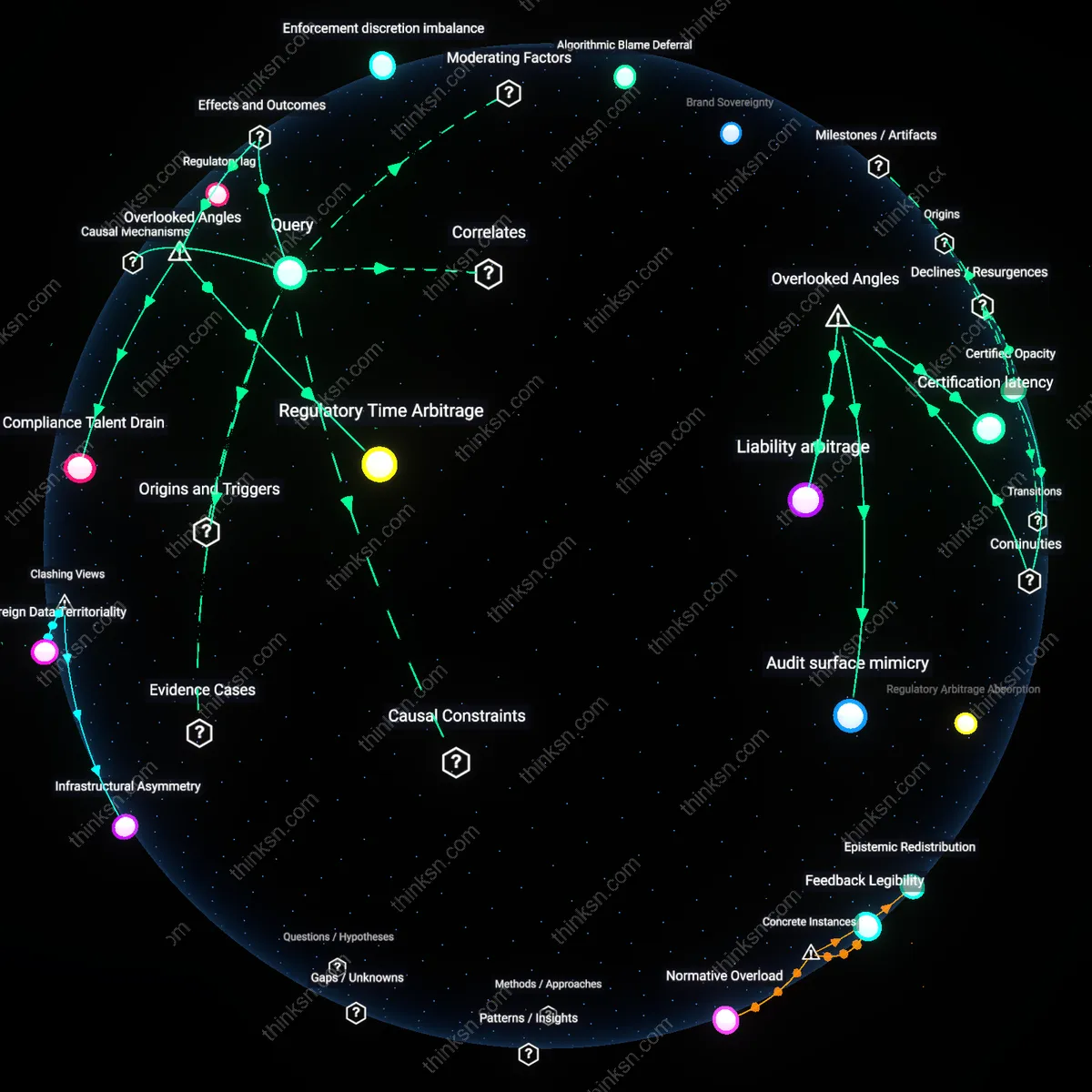
Regulatory time preference
Fast-tracking immunity for telecom operators reveals that consumer protection outcomes are shaped by the state’s implicit preference for regulatory speed over accountability. The mechanism operates through emergency framing in legislative processes, where data breach disclosures are treated as exigent events requiring immediate legal shelter for firms to preserve crisis-response coordination—this prioritization silently displaces due process and public oversight. What is overlooked is that the value of time in regulation is not neutral but reflects a systemic bias toward industry operational rhythms, effectively treating corporate liability exposure as a first-order policy constraint. This shifts power not through overt lobbying victories but by normalizing a temporal hierarchy in which regulatory action must accommodate corporate risk windows, not civic deliberation cycles.
Liability arbitrage geography
Fast-tracked immunity exposes how telecom operators exploit jurisdictional fragmentation in data governance to position themselves as cross-border liability buffers, absorbing regulatory shocks at the national level while offloading risk to users. The mechanism works through differential compliance costs across countries, where operators use the threat of scaled service withdrawal from high-regulation regions to extract concessions, including retroactive legal shields during breach disclosures. The overlooked dynamic is that immunity is less about legal protection per se and more about maintaining the spatial distribution of risk—concentrating accountability in weak regulatory zones while centralizing profit in strong ones. Consumer advocates lose leverage not because they are outspent, but because the battleground has been silently relocated to legal terrains where their presence is institutionally marginal.
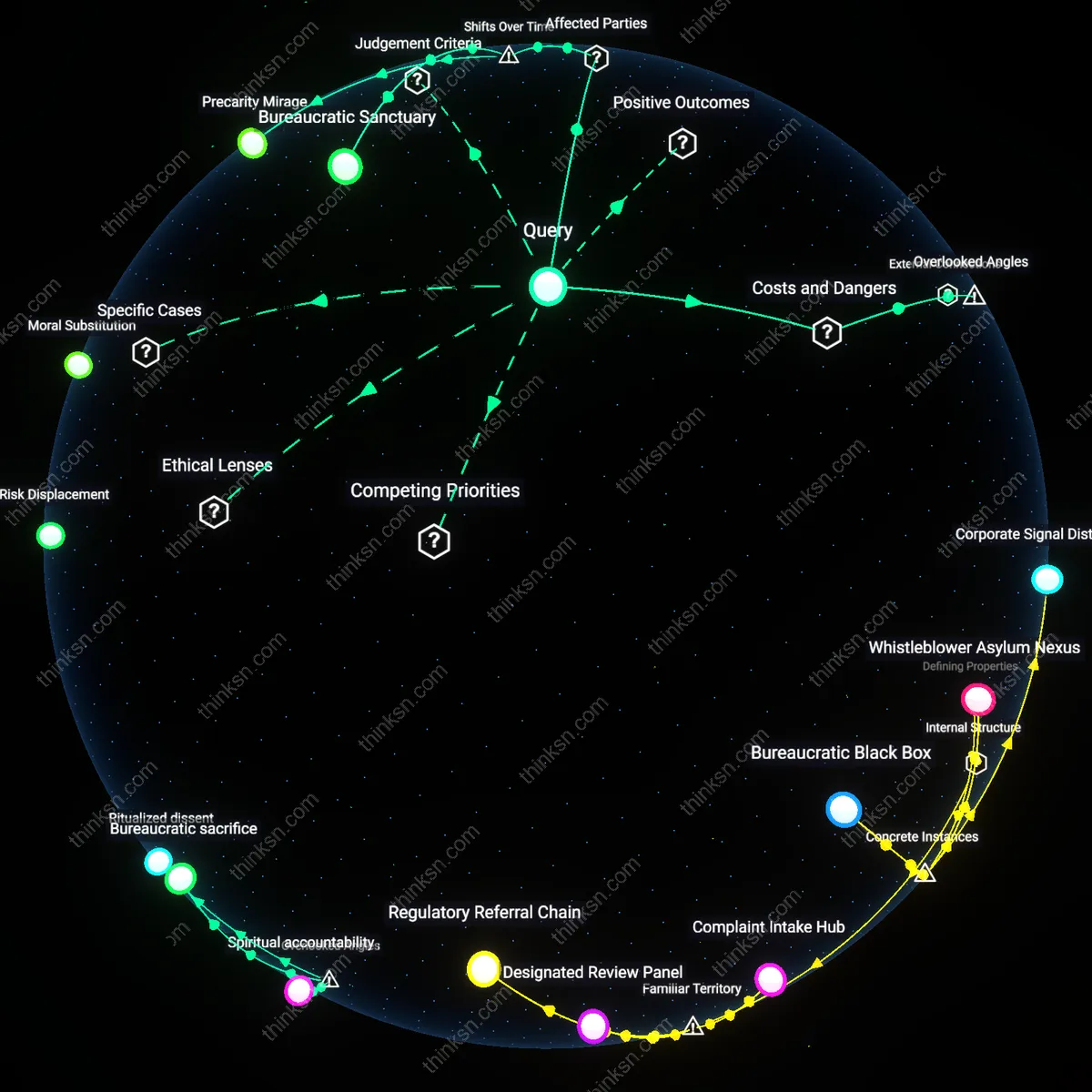
Regulatory Asphyxiation
Fast-tracking immunity for telecom operators in data-breach disclosures directly weakens regulatory enforcement capacity by insulating major infrastructure firms from liability, thereby eroding the deterrent function of privacy laws. This mechanism operates through legislative provisions—like retroactive liability shields embedded in cybersecurity bills—that are drafted in coordination between industry trade groups such as CTIA and congressional staff, effectively collapsing the enforcement frontier before breaches are even adjudicated. The non-obvious consequence is not just reduced accountability, but the systematic incapacitation of agencies like the FCC and FTC, whose authority depends on the credible threat of penalty—revealing how pre-emptive legal insulation functions as a form of institutional suffocation rather than mere favoritism.
Regulatory Capture
Fast-tracking immunity for telecom operators reveals that industry lobbying systematically shapes legal protections ahead of public oversight. Telecommunications firms, through concentrated campaign contributions and revolving-door appointments with agencies like the FCC and Congress, secure preemptive liability shields that override consumer privacy concerns. This dynamic enables firms to treat data breaches as cost-of-doing-business rather than accountability lapses, embedding corporate influence directly into legislative timing and scope. The non-obvious implication is that the speed of immunity—framed as crisis response—functions as a structural advantage for incumbents, not a neutral policy tool.
Crisis Privilege
Granting rapid immunity during data breach disclosures reflects a reflexive policy bias toward maintaining corporate operational continuity over public redress. In moments of systemic failure—such as widespread data exposure—regulators and lawmakers invoke national security and network stability to justify shielding telecoms from litigation, mirroring post-9/11 surveillance concessions. The mechanism operates through emergency framing in legislative markup and classified threat briefings inaccessible to consumer advocates. What’s underappreciated is how crisis narratives become institutionalized, allowing firms to treat temporary immunities as de facto permanent shields, eroding the leverage of public interest groups over time.
Asymmetric Accountability
The immunity fast track demonstrates that consequences for data misuse are inversely proportional to institutional scale and political alignment. Major telecom operators like AT&T, Verizon, and Comcast face minimal enforcement risk despite handling vast sensitive datasets, while individual users or small firms face stringent penalties for minor compliance errors. This imbalance is sustained through standardized reporting regimes that favor corporate legal teams’ capacity to navigate complex disclosure rules, rendering consumer complaints procedurally inert. The overlooked reality is that apparent regulatory parity masks a system where accountability is functionally reserved for the less connected, entrenching a two-tier compliance order.