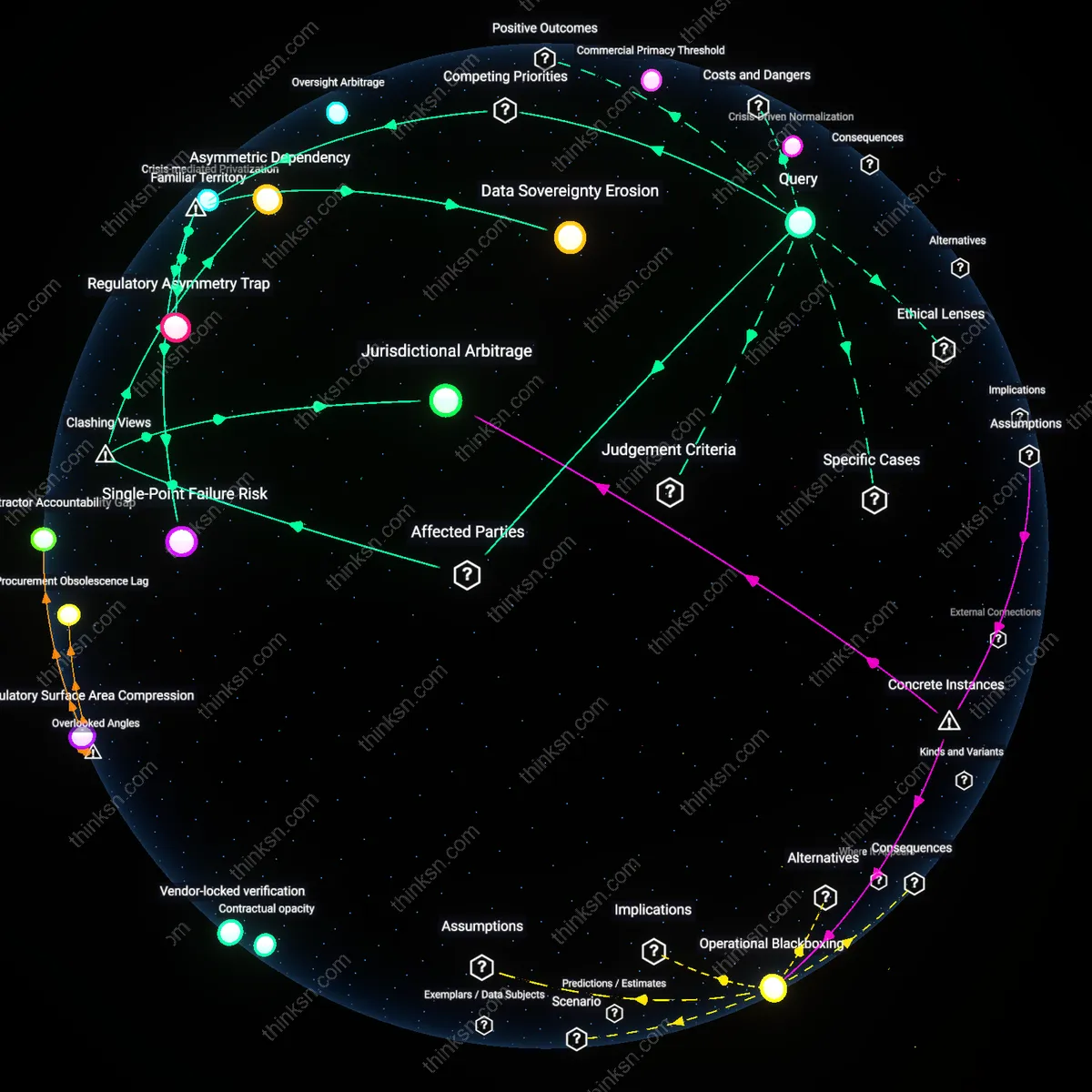
Is Voting Tech Sabotaging Fair Elections?
Analysis reveals 8 key thematic connections.
Key Findings
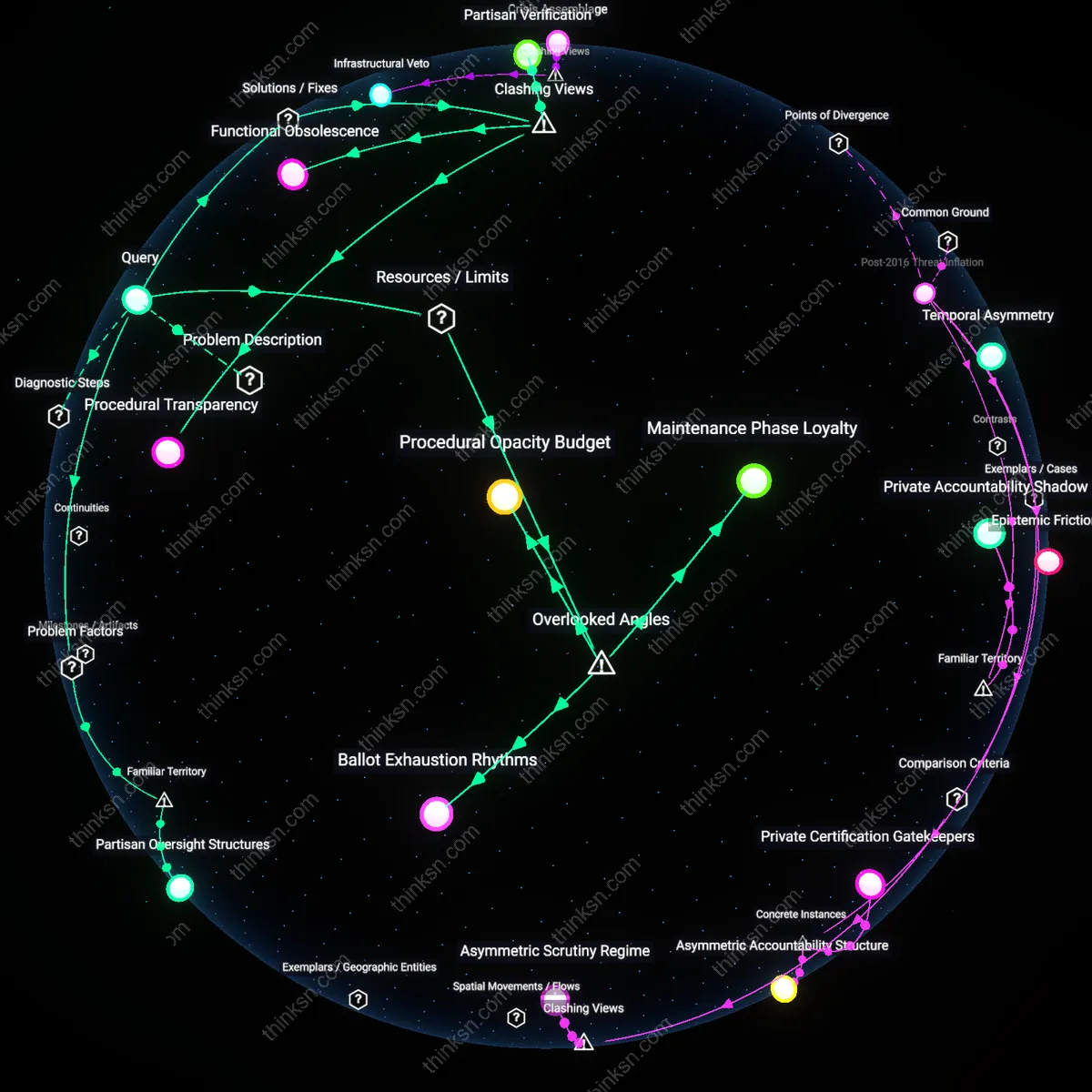
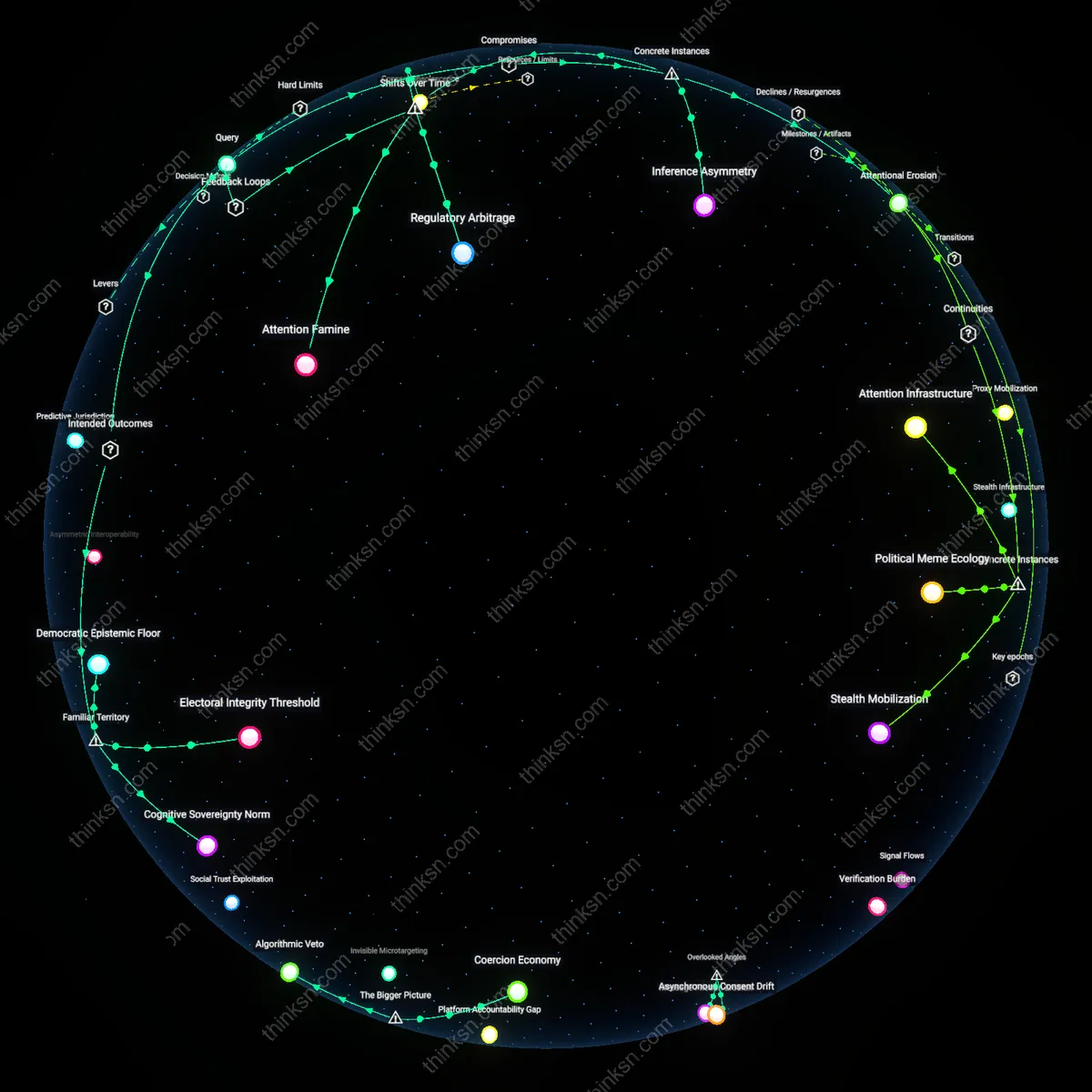
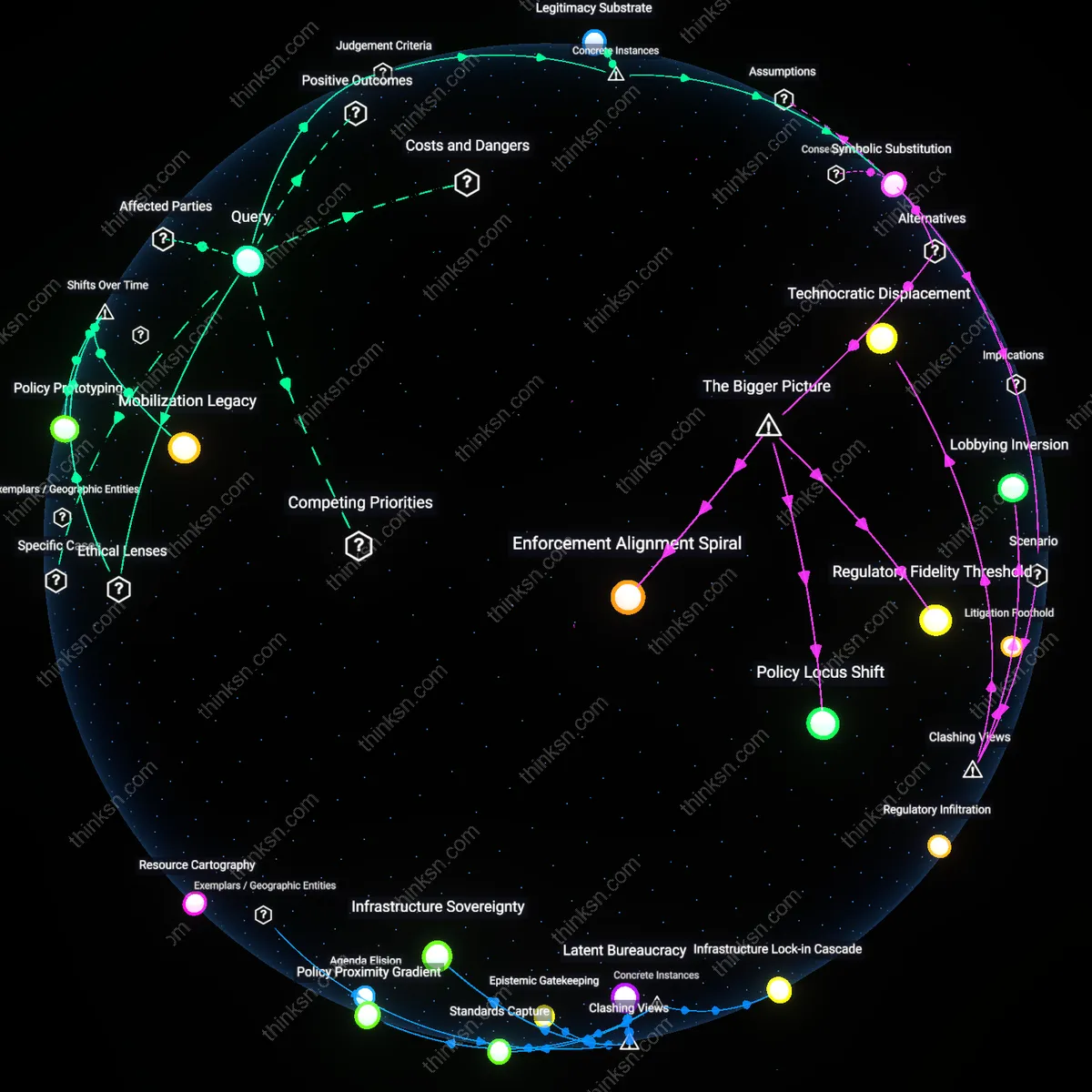
Partisan Oversight Structures
Independent election administration must be insulated from political appointment cycles to prevent weaponization of technical roles. Election technology oversight boards staffed by party-affiliated officials—such as secretaries of state elected on partisan tickets—routinely authorize voting system changes, certify vendors, and control incident response, creating built-in incentives to favor one coalition. This is not merely about corruption, but about structurally embedded discretion within roles that appear neutral but are filled through politicized processes, especially in states where election administration and party leadership overlap heavily. The underappreciated reality is that the integrity of voting technology is less about code than about who controls its interpretation and deployment.
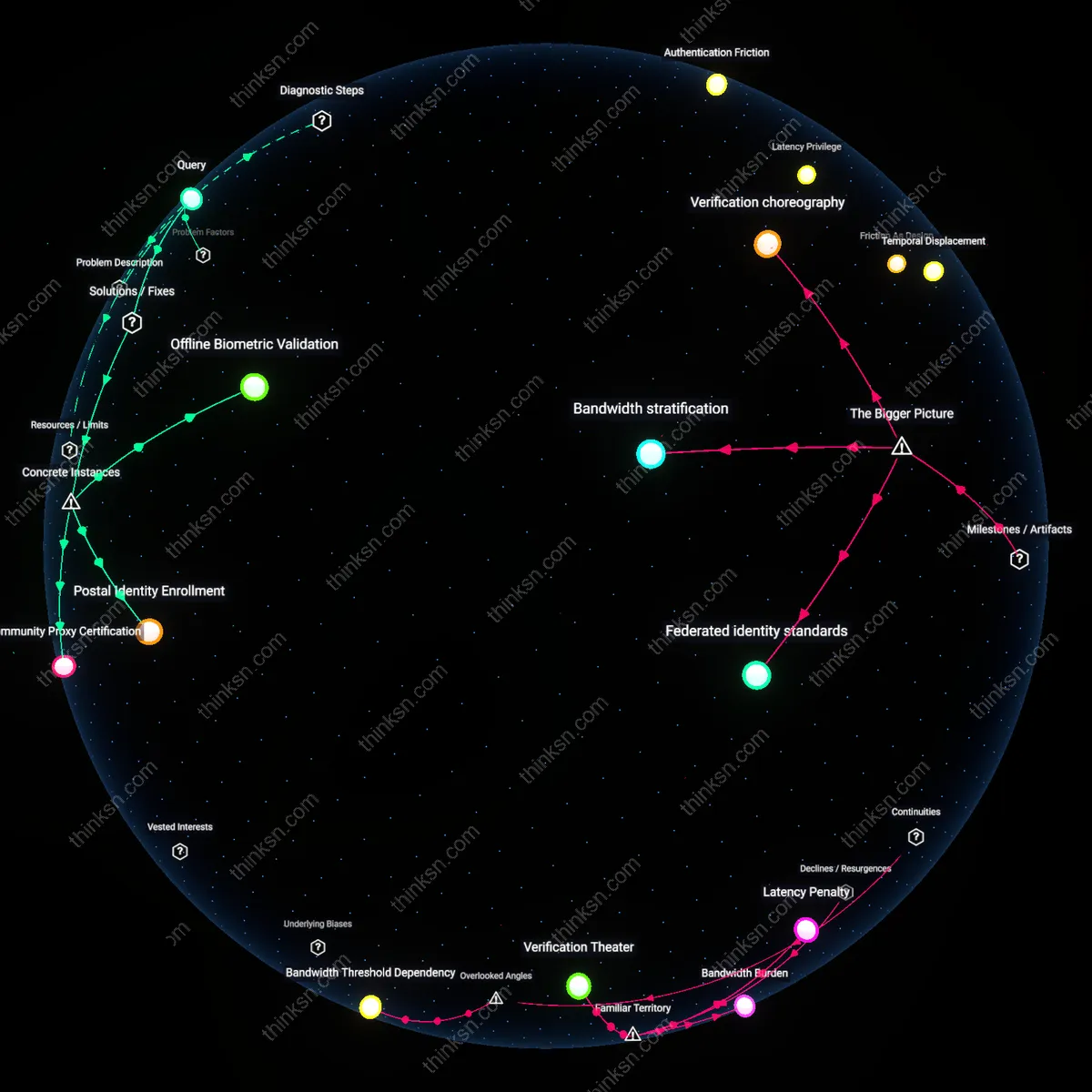
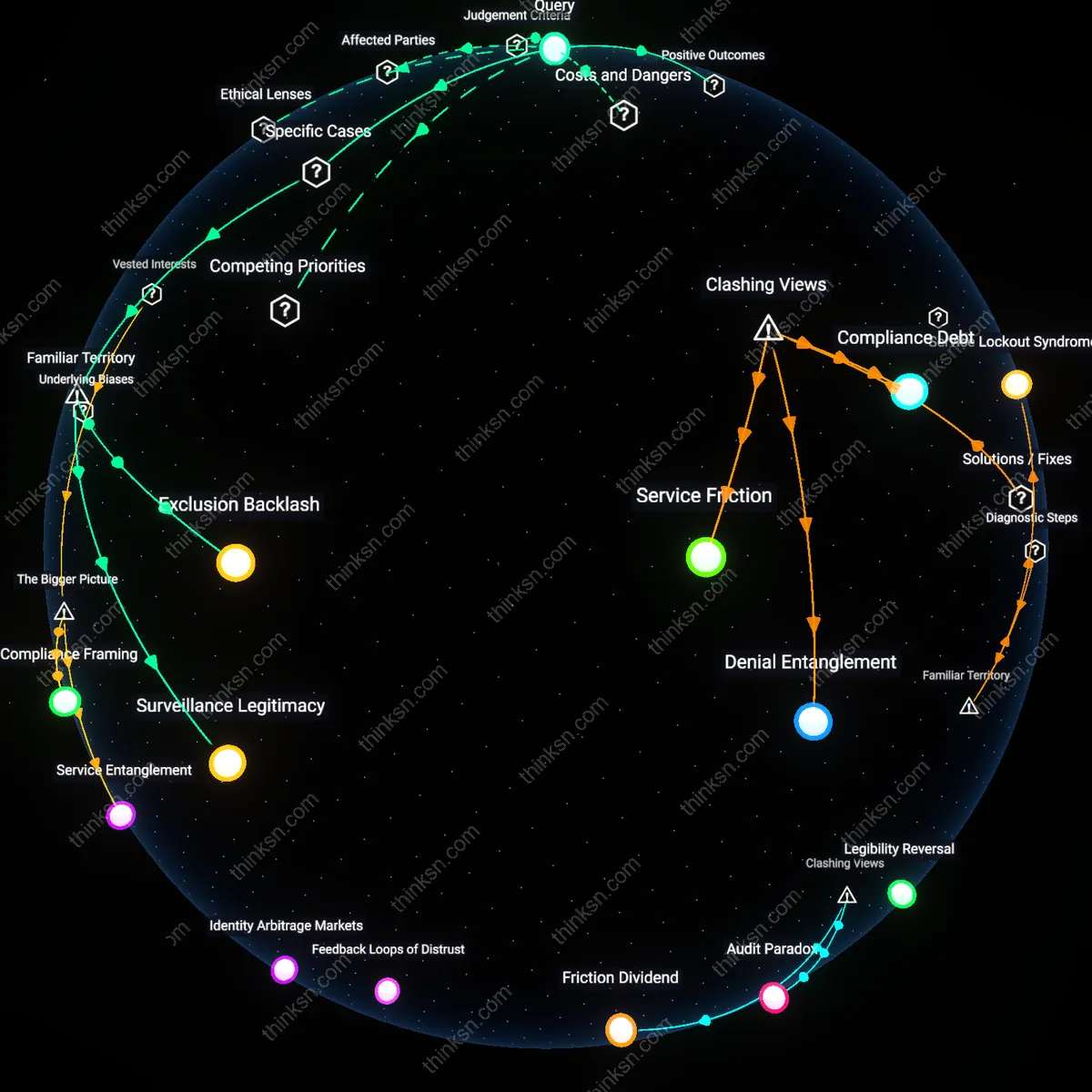
Vendor Accountability Gaps
Exclusive contracts with a small number of private voting machine vendors—like Dominion or Election Systems & Software—enable backdoor influence by allowing single points of failure to persist without competitive scrutiny. These companies operate as de facto arms of election infrastructure while remaining shielded from public oversight, often citing proprietary software as justification for opacity, even as local officials lack technical capacity to verify claims. People assume the machines are the problem, but the root vulnerability lies in the lack of enforceable public-interest obligations on private suppliers who face no consequences for poor performance or perceived bias. The overlooked issue is not just partisanship, but an accountability void where commercial secrecy undermines democratic accountability.
Procedural Transparency
Mandate real-time public audit logs of voting machine operations to preempt manipulation claims by making anomalies instantly visible. The U.S. Election Assistance Commission should require all certified voting systems to generate standardized, immutable logs accessible via anonymized public dashboards, monitored not only by officials but also partisan observers and academic researchers. This undercuts the effectiveness of partisan tampering by shifting the risk from concealment to instant exposure, reframing 'security' not as opacity but as collective scrutiny—directly challenging the assumption that secrecy underpins election integrity.
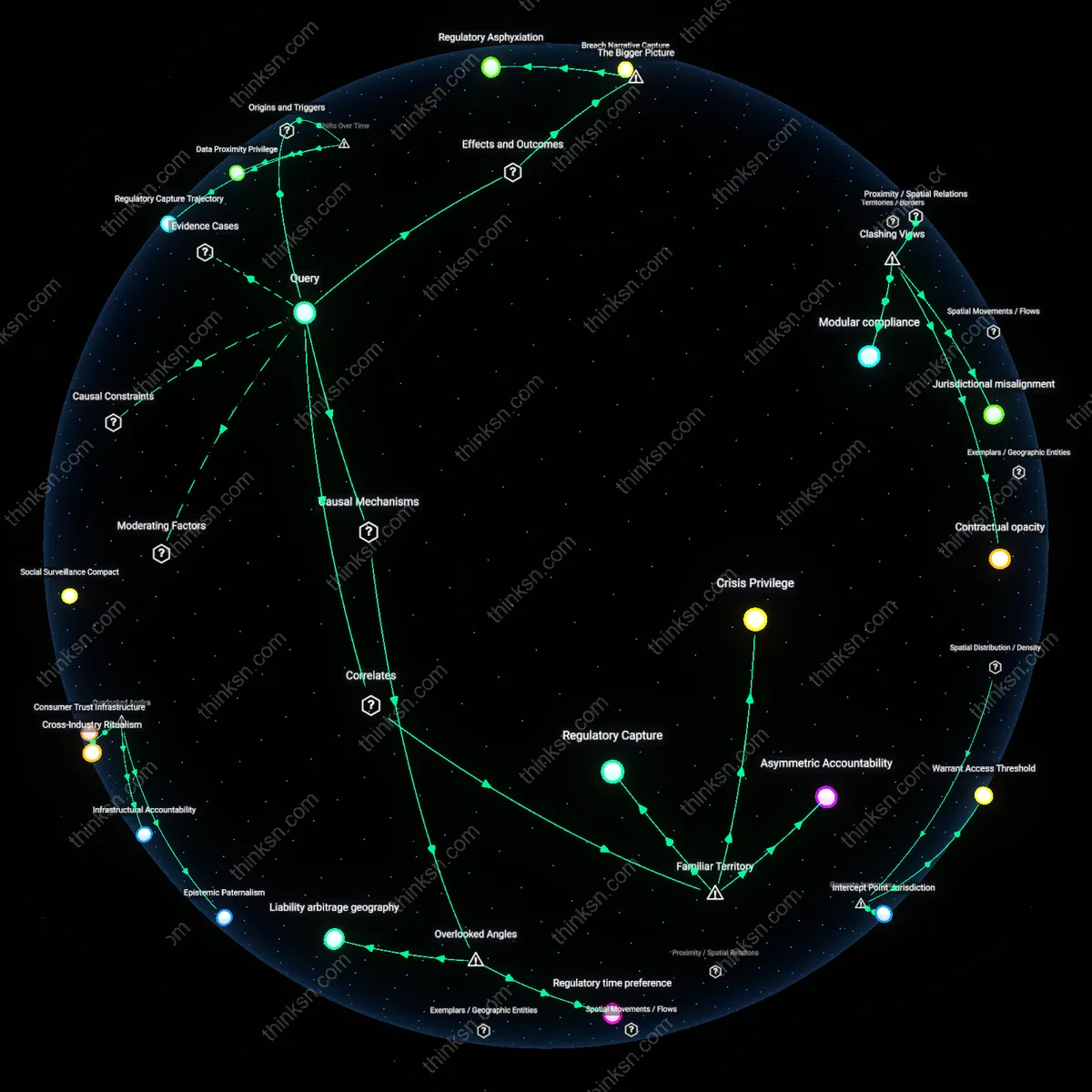
Functional Obsolescence
Decouple election legitimacy from software fidelity by mandating the use of outdated, intentionally low-capability voting machines that lack network connectivity and modern programmable features. Jurisdictions like Virginia have already reverted to pre-2010 machines not because of nostalgia but to eliminate attack surfaces that scale with technological sophistication. This counters the prevailing belief that improved technology increases trust; instead, legitimacy is preserved through deliberate technological regression, exposing how innovation in voting systems often introduces rather than resolves vulnerabilities.
Partisan Verification
Institutionalize cross-party control over voting technology by requiring bipartisan teams to jointly configure and certify machines before elections, as practiced in some Florida counties where Republican and Democratic appointees must sign off on firmware hashes. This transforms partisan actors from potential subverters into co-guarantors, leveraging their mutual distrust as a stabilizing mechanism—contradicting the standard view that partisanship inherently undermines legitimacy, revealing instead that symmetric suspicion can be systematized into enforcement.
Procedural Opacity Budget
Audit trail transparency must be selectively restricted to non-partisan technical overseers to prevent manipulation of public doubt. Election legitimacy depends not only on accurate results but on the controlled release of process details that, if fully public, could be weaponized by actors with computational resources to simulate plausible fraud narratives—such as through synthetic ballot distribution modeling—thereby eroding trust regardless of actual integrity. This limitation on information diffusion, enforced by statutory caps on audit data access, counters the assumption that full procedural transparency strengthens legitimacy, revealing instead that unlimited access to granular voting data creates a vulnerability when adversaries can exploit asymmetries in interpretation capacity. The overlooked dynamic is that some procedural transparency becomes a liability when the cost of decrypting meaning from data is unevenly distributed across partisan actors.
Maintenance Phase Loyalty
Election legitimacy is preserved by vesting firmware update authority in state-certified technicians whose job security and professional recognition derive from cross-partisan oversight boards, not from election officials subject to political turnover. These technicians operate during non-election periods—when scrutiny is low and incentives to compromise systems are less immediate—making their allegiance more likely to align with institutional continuity than with transient electoral outcomes. Most analyses focus on election-day integrity or pre-election certification, but the residual vulnerability lies in the sustained, mundane stewardship of hardware between cycles, where small deviations in calibration or logging can accumulate into systemic drift that evades forensic detection. The underappreciated factor is that technological integrity depends not on momentary checks but on the inertial loyalty cultivated during periods of procedural boredom.
Ballot Exhaustion Rhythms
Legitimacy can be stabilized by aligning voting machine replacement cycles with the natural attrition of voter cohorts whose expectations are calibrated to specific interface behaviors. When new technology introduces subtle changes in ballot layout, feedback timing, or error recovery—such as touch-screen debounce intervals or audio ballot navigation—it risks misrecording intent not through malice but through interaction mismatch, particularly among elderly or disabled voters who rely on learned motor patterns. These usability-induced errors are rarely investigated as threats to legitimacy because they appear as individual mistakes, but aggregated across precincts with older machines, they create systematic skew that partisans can later allege as targeted suppression. The overlooked dependency is that technological consistency preserves legitimacy not by preventing hacking, but by maintaining behavioral synchrony between voters and machines across electoral cycles.