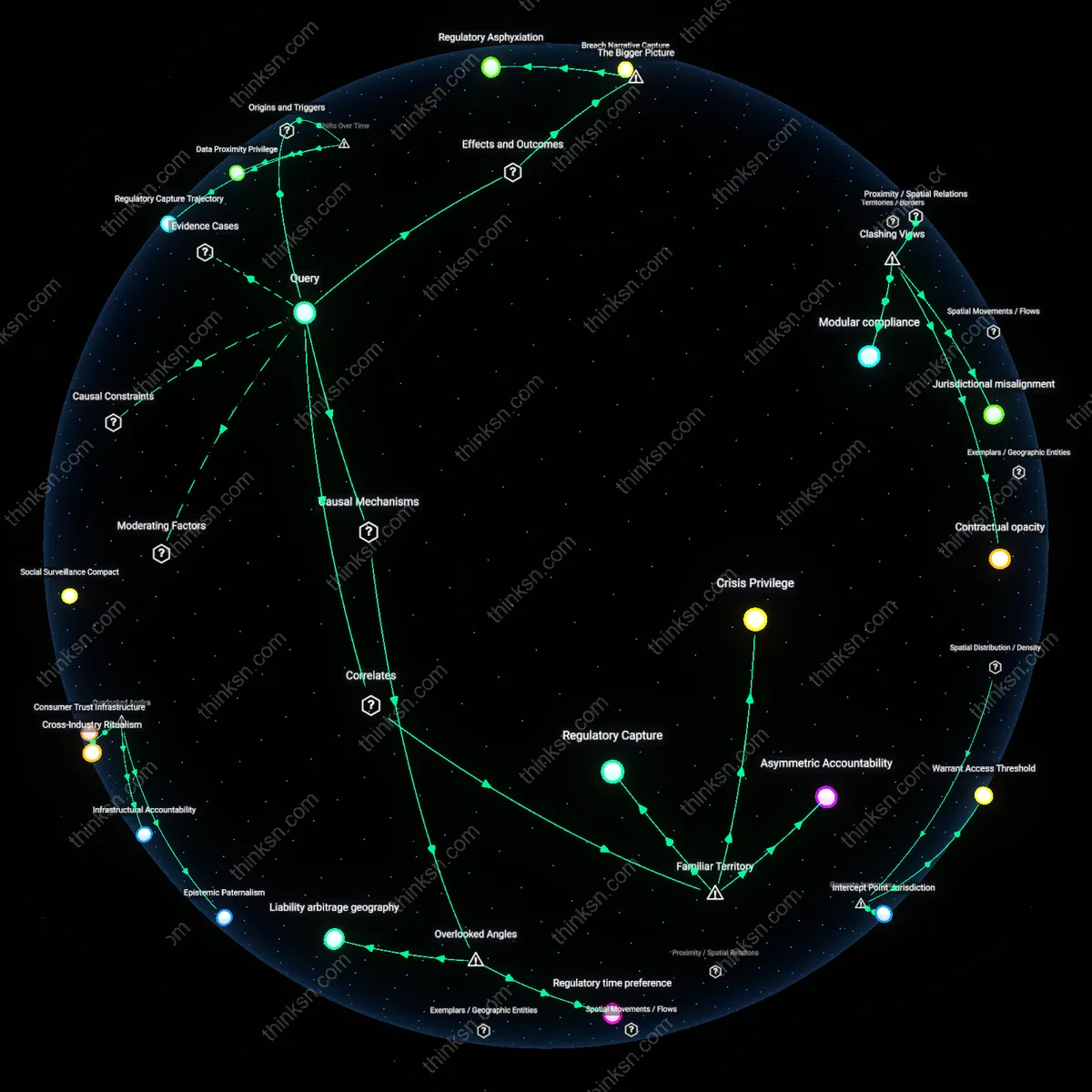
Institutional capture
Bringing standard-writing in-house would dismantle entrenched contractor influence over military specifications. Defense contractors have long shaped technical standards to favor proprietary systems, ensuring continued dependency and cost escalation; by reclaiming this function, the Department of Defense would disrupt a feedback loop in which contractors design standards to lock in future procurements, thereby reducing the systemic advantage granted to incumbent firms. This shift would expose how deeply private actors have usurped sovereign technical authority—an underappreciated form of regulatory capture that operates not through lobbying, but through embedded expertise and path-dependent design choices.
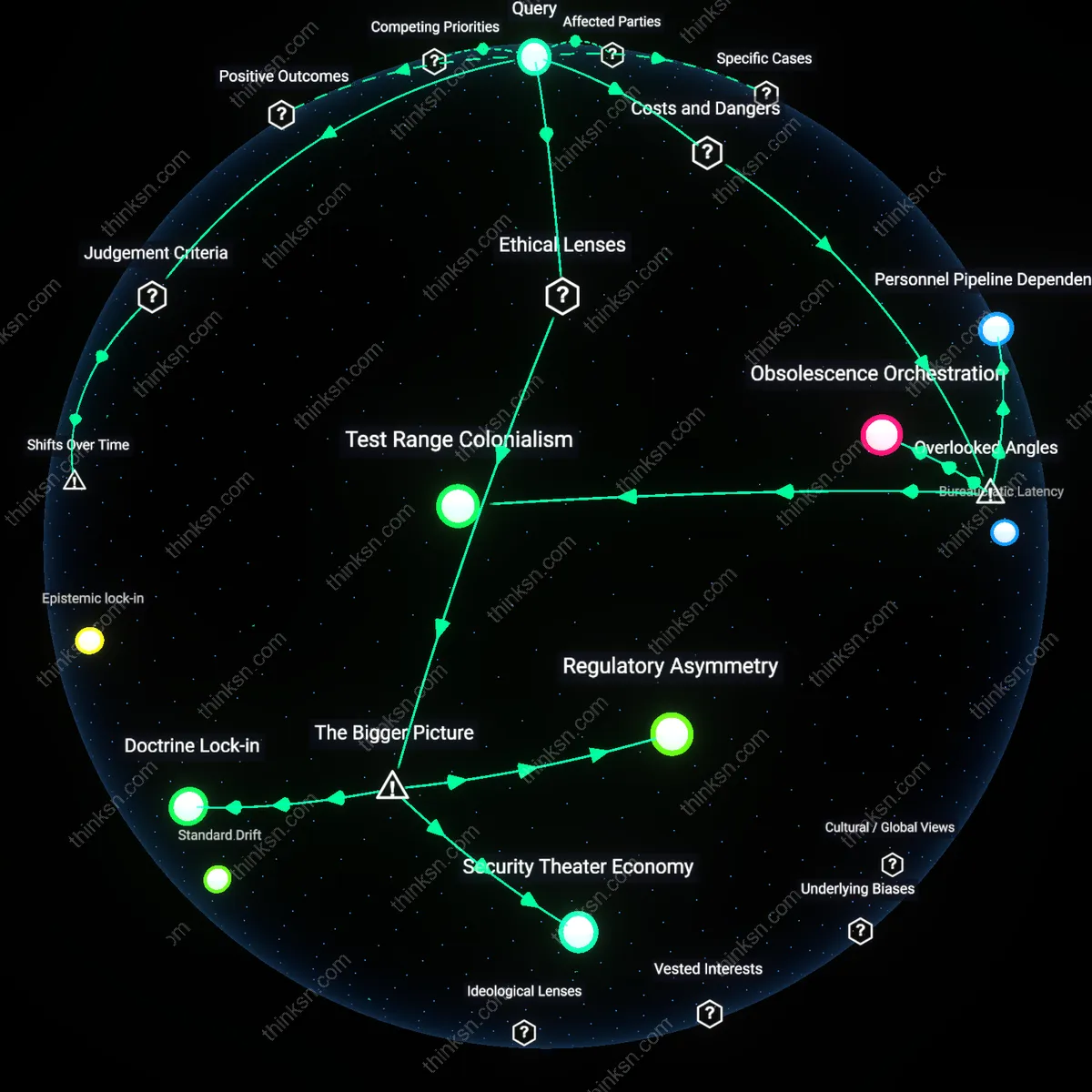
Bureaucratic latency
Internal standard-writing would slow innovation cycles due to the government’s lack of embedded systems for rapid technical iteration. Unlike agile defense contractors who integrate user feedback and prototyping into ongoing development, federal engineering bureaus operate under rigid personnel and procurement rules that delay responsiveness; this structural inertia means that in-house standards would lag behind emerging threats and technologies. The non-obvious consequence here is not inefficiency per se, but a mismatch between bureaucratic time and operational tempo—revealing how privatization of technical design has been enabled not just by profit motives, but by genuine gaps in state capacity to iterate at scale.
Interoperability fracture
Shifting standard-writing to government agencies would create compatibility ruptures across NATO and allied defense systems. U.S. military standards shape the de facto global baseline for coalition interoperability; redefining them internally, without contractor-mediated coordination across transnational supply chains, risks misaligning with partner capabilities developed under existing specifications. The deeper dynamic is that defense contractors function as informal international standards brokers—neutralizing this role risks fragmenting joint operational capacity, an effect invisible when viewing standard-setting as merely a national administrative function rather than a node in a distributed alliance architecture.
Bureaucratic Lag
Government absorption of standard-writing would institutionalize slower innovation cycles by replacing contractor-driven agility with centralized, risk-averse rulemaking. Civilian and military agencies historically offloaded standard-setting post-Vietnam to firms like Raytheon and Lockheed Martin, which developed technical benchmarks in tandem with weapons systems; this shift enabled rapid adaptation during the Cold War arms race, but reintegrating those functions would reintroduce interagency review delays and freezing of specifications long before deployment. The underappreciated outcome is that formalized control over standards produces higher compliance but at the cost of real-time technological responsiveness, particularly in software-defined systems where updates outpace bureaucratic timelines—unlike the 1980s, when hardware lifespans justified durable standards.
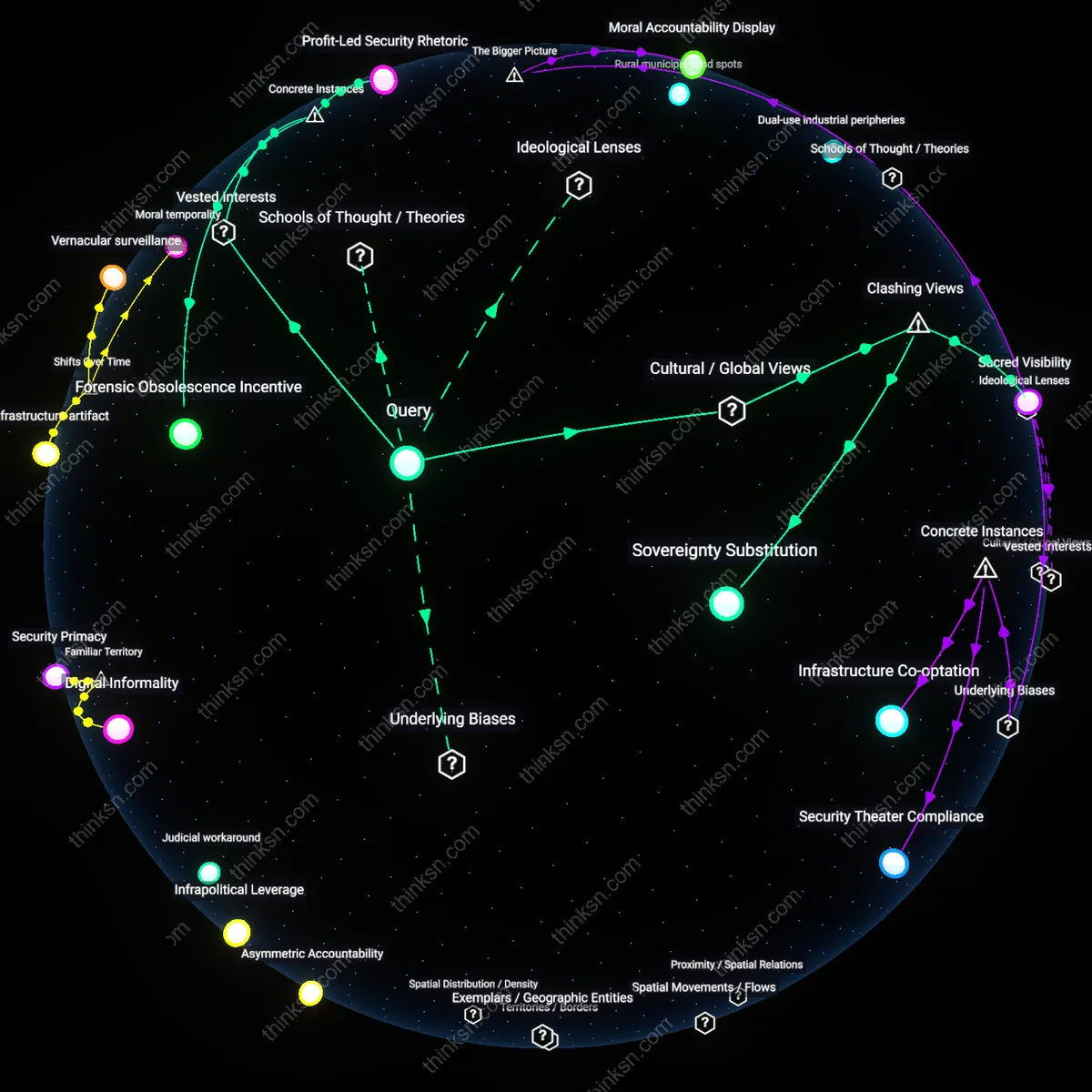
Contractor Exaptation
Defense contractors have repurposed their role in standard-writing into a form of regulatory capture through accumulated technical path dependency. Since the 1994 Base Realignment and Closure reforms, firms like Boeing and Northrop Grumman embedded proprietary standards into logistics and interoperability protocols, turning what began as delegated technical work into de facto control over military architecture; returning standard-setting to federal agencies would force a rupture in systems designed around corporate norms, revealing how contractors evolved beyond service providers into silent legislators. The non-obvious insight is that standards themselves became the product, not merely the framework—making their reclamation a political dismantling of decades-long integration rather than a simple administrative shift.
Standard Drift
Internalizing standard-writing would halt the progressive divergence between public accountability and technical specificity that emerged after the 2001 Patriot Act expanded contractor access to classified system design. In the 1990s, standard-setting was coordinated through the Department of Defense’s Military Specifications Reform program, which aimed to reduce over 36,000 military-unique specs in favor of commercial standards; the reversal of this policy through in-house retrenchment today would freeze a legacy of hybrid public-private norms that allowed simultaneous compliance with federal law and proprietary advantage. The overlooked consequence is that reclaiming standards reinscribes state authority over technical consensus, exposing how drift—once incremental and invisible—now masks fundamental jurisdictional ambiguity in digital warfare systems.
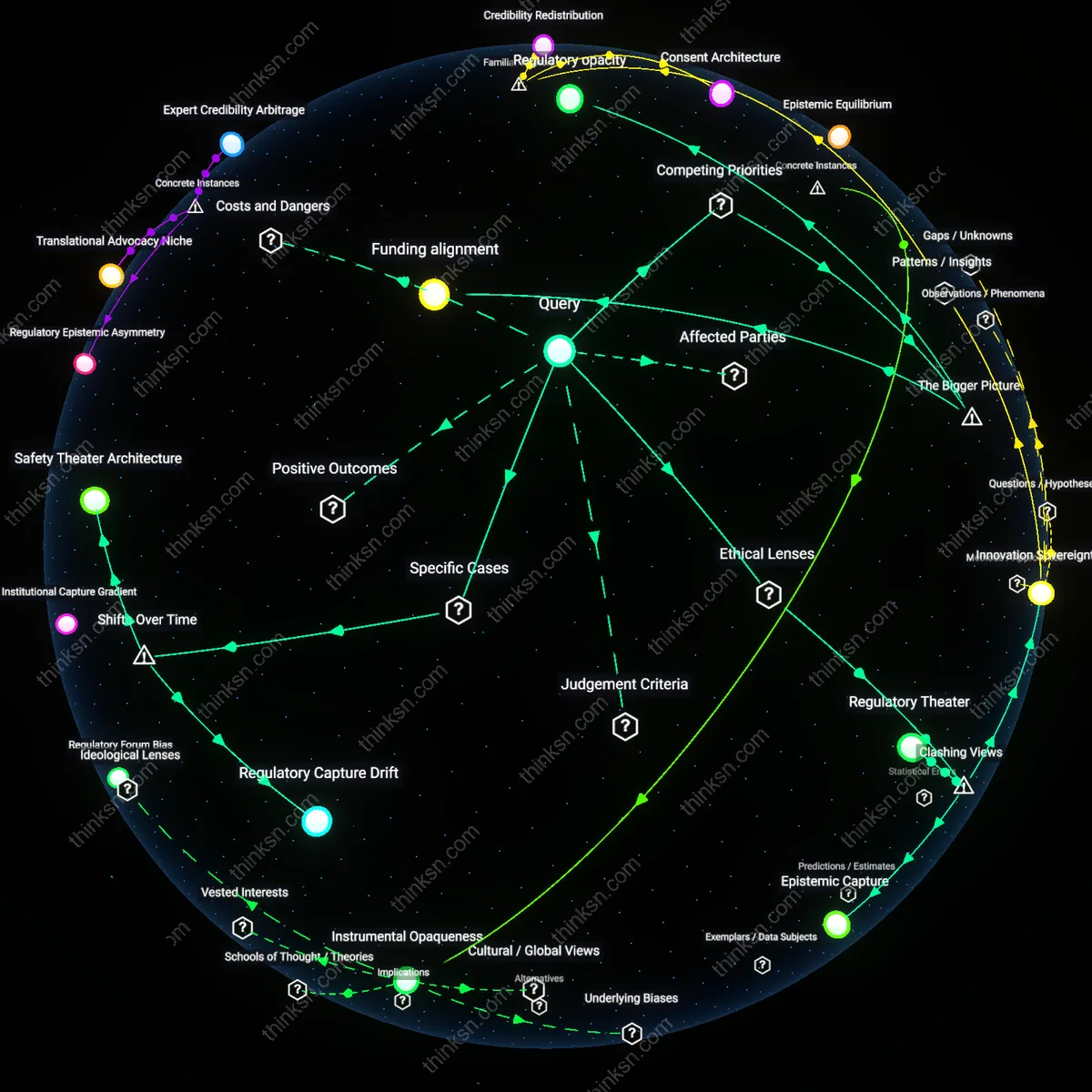
Innovation Cartel
The government absorbing standard-writing would collapse the de facto innovation cartel maintained by major defense contractors through proprietary control of technical baselines. By centralizing standards development within entities like the Defense Acquisition University or the Office of the Under Secretary of Defense for Acquisition, the DoD would strip contractors of their ability to encode preferential advantages into foundational specifications—advantaging incumbents through labyrinthine compliance paths. This creates analytical friction because the intuitive view assumes contractor-driven standards accelerate innovation, whereas in reality, they often entrench vendor lock-in under the guise of technical necessity, revealing a hidden mechanism of market control masked as engineering rigor.
Bureaucratic Latency
Bringing standard-writing in-house would trigger bureaucratic latency, where inter-departmental review cycles within OSD, Joint Requirements Oversight Council, and service-specific commands replace contractor-driven agility with hierarchical consensus, delaying critical fielding timelines. Unlike the assumption that internal control increases accountability, the shift would amplify coordination costs across military branches and civilian oversight bodies, exposing a latent tension between democratic oversight and operational tempo—particularly in near-peer conflict scenarios where speed of adaptation determines battlefield outcomes. The non-obvious insight is that decentralized, contractor-mediated standardization functions as a shadow agile system, bypassing sclerotic civil service processes under national security exceptions.
Specification Frontloading
Internalizing standards would force the government to assume full technical frontloading responsibility, requiring permanent civilian engineering cadres at places like Picatinny Arsenal or the Naval Sea Systems Command to define requirements before RFP issuance—something currently offloaded to industry. This inversion reveals that contractors don’t just implement standards—they de-risk the government’s own uncertainty about what is technically feasible, acting as epistemic proxies. The dissonance lies in the assumption that bringing work in-house increases public control, when in fact it exposes the state’s chronic underinvestment in technical foresight, making Specification Frontloading a liability rather than a lever of sovereignty.
Institutional Inertia
The U.S. Air Force’s attempted internalization of weapons systems documentation during the F-22 Raptor program stalled due to entrenched contractor-led standard-writing practices at Lockheed Martin, which had developed proprietary formats incompatible with military workflows, revealing that once technical authorship is ceded to contractors, internal reabsorption fails not from lack of expertise but from systemic resistance to restandardization. This case demonstrates how bureaucratic path dependence—in this instance, the Air Force’s inability to repatriate control over system specifications despite owning the platform—becomes a self-enforcing barrier when contractors shape the technical epistemology of the state. The non-obvious insight is that standard-writing is not merely administrative but constitutes a form of cognitive sovereignty, and its loss reshapes the state’s capacity to govern technical change.
Knowledge Arbitrage
When India’s Defence Research and Development Organisation (DRDO) began drafting indigenous technical standards for missile systems in the 2000s, developers discovered that reliance on Russian-origin documentation had created a hidden dependency where canonical performance metrics were tied to Soviet-era testing protocols, forcing DRDO engineers to reverse-engineer assumptions embedded in contractor-supplied standards to ensure compatibility with domestic production cycles. This shift revealed that standard-writing functions as a covert site of technological rent extraction, where contractors embed procedural lock-ins that persist even after formal knowledge transfer. The significance lies in how standards act not as neutral templates but as vectors of contextual knowledge that, when externally authored, enable contractors to retain operational leverage over sovereign capabilities.
Normative Drift
The European Space Agency’s effort to centralize technical standards for Ariane launch vehicles in the 1990s led to prolonged conflicts with Aerospatiale and later ArianeGroup, as contractor-developed reliability protocols from earlier models were found to prioritize rapid prototyping over auditable traceability, undermining ESA’s safety governance framework and forcing compromises that diluted both innovation speed and oversight rigor. This case illustrates how contractor-written standards encode operational values—here, expediency over accountability—that become normatively sticky once institutionalized, such that state reinternalization risks not only technical discoordination but cultural friction in decision-making logic. The underappreciated consequence is that bringing standard-writing back in-house is not a technical relocation but a normative reclaiming of risk tolerance.
Epistemic lock-in
Bringing standard-writing in-house would entrench outdated operational assumptions by severing feedback loops with emergent contractor innovation. Military bureaucracy prioritizes procedural continuity, so internal standard-setting would amplify path dependency, freezing technical requirements around legacy platforms like the F-35 or Aegis—systems contractors now optimize around. This rigidity is non-obvious because reformers assume in-house control increases adaptability, but it actually diminishes exposure to competitive problem-solving from firms like Anduril or Palantir, who experiment beyond doctrinal boundaries. The real shift isn’t about ownership of standards, but the suppression of heterodox technical imagination.
Requirement entropy
Internalizing standard development would accelerate the decay of specification precision due to bureaucratic mission creep within agencies like the OASD(NII) or DISA. Without external contractor pushback during standard formation—where profit risk forces clarity—internal stakeholders (e.g., service branches, acquisition councils) would overload standards with political compromises and overlapping authorities. This inflation of vague, unenforceable mandates is rarely acknowledged because analysis focuses on technical content, not how the absence of adversarial refinement degrades epistemic discipline. The overlooked mechanism is that contractor resistance previously acted as a constraint on bureaucratic vagueness.
Interstitial innovation
Eliminating contractor-led standard-setting would collapse the niche spaces where dual-use technologies from non-traditional vendors get assimilated into military systems. Firms like SpaceX or Shield AI gain footholds not by winning full contracts, but by shaping auxiliary standards—e.g., data-link protocols or power interfaces—during early phases. When the Pentagon internalizes these, it cuts off backdoor entry points, reinforcing reliance on Tier 1 integrators like Lockheed or Raytheon. This hidden function of standards—as on-ramps for disruption—is absent from reform debates, which fixate on ownership rather than ecosystem permeability.