Is App Store Interoperability Worth Security Risks?
Analysis reveals 7 key thematic connections.
Key Findings
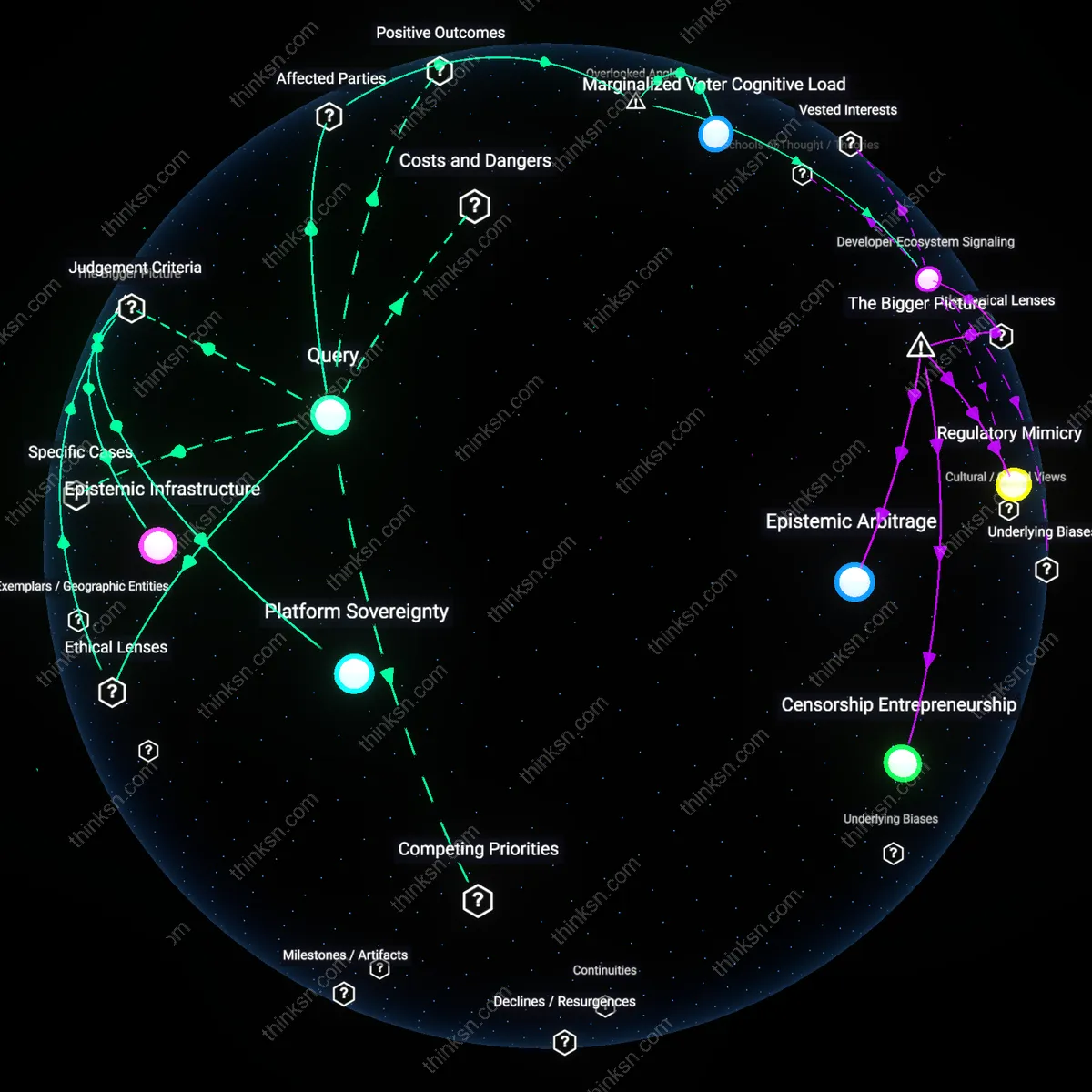
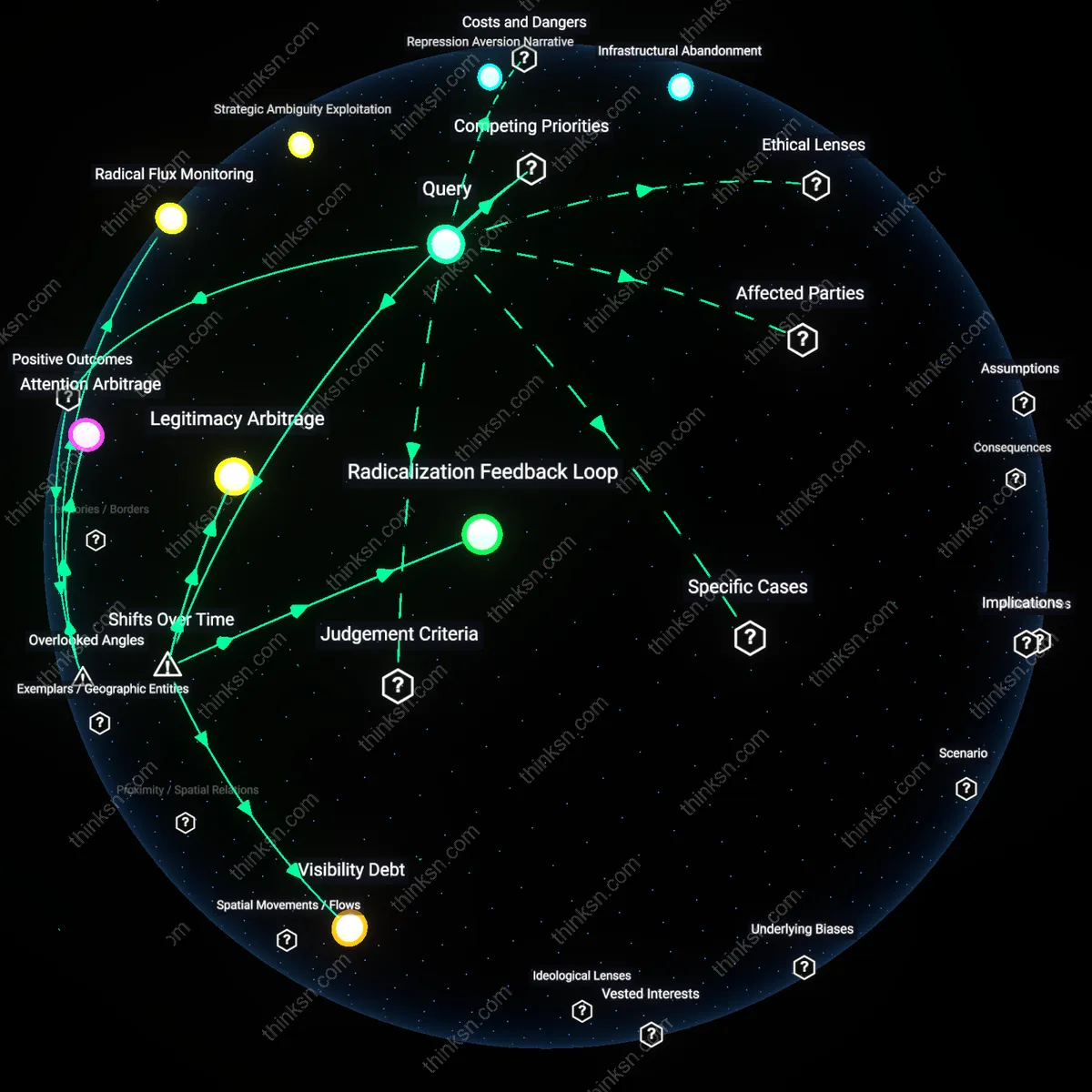
Developer Sovereignty
Requiring interoperability erodes developer sovereignty by shifting control from app creators to platform gatekeepers during the post-2010 mobile platform consolidation era. As dominant app stores like Apple’s App Store and Google Play centralized distribution after the iPhone’s 2007 launch, they institutionalized restrictive SDKs and review processes under security pretexts—mechanisms that previously did not exist when mobile software was distributed openly. This transition reveals how security arguments now mask power asymmetries, diminishing developers’ ability to control their own code in production—an erosion that was neither inevitable nor visible in the earlier, fragmented mobile landscape of the 2000s.
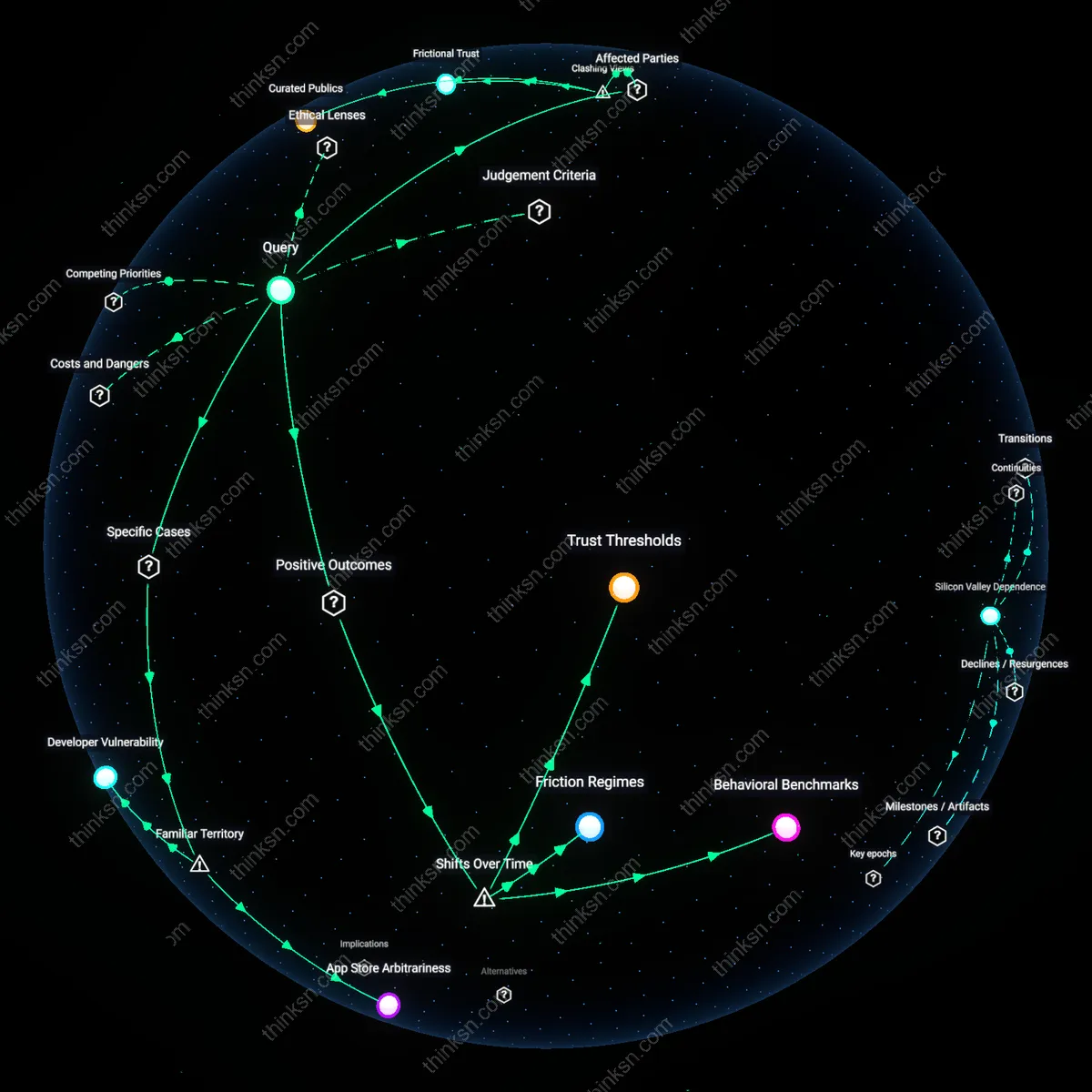
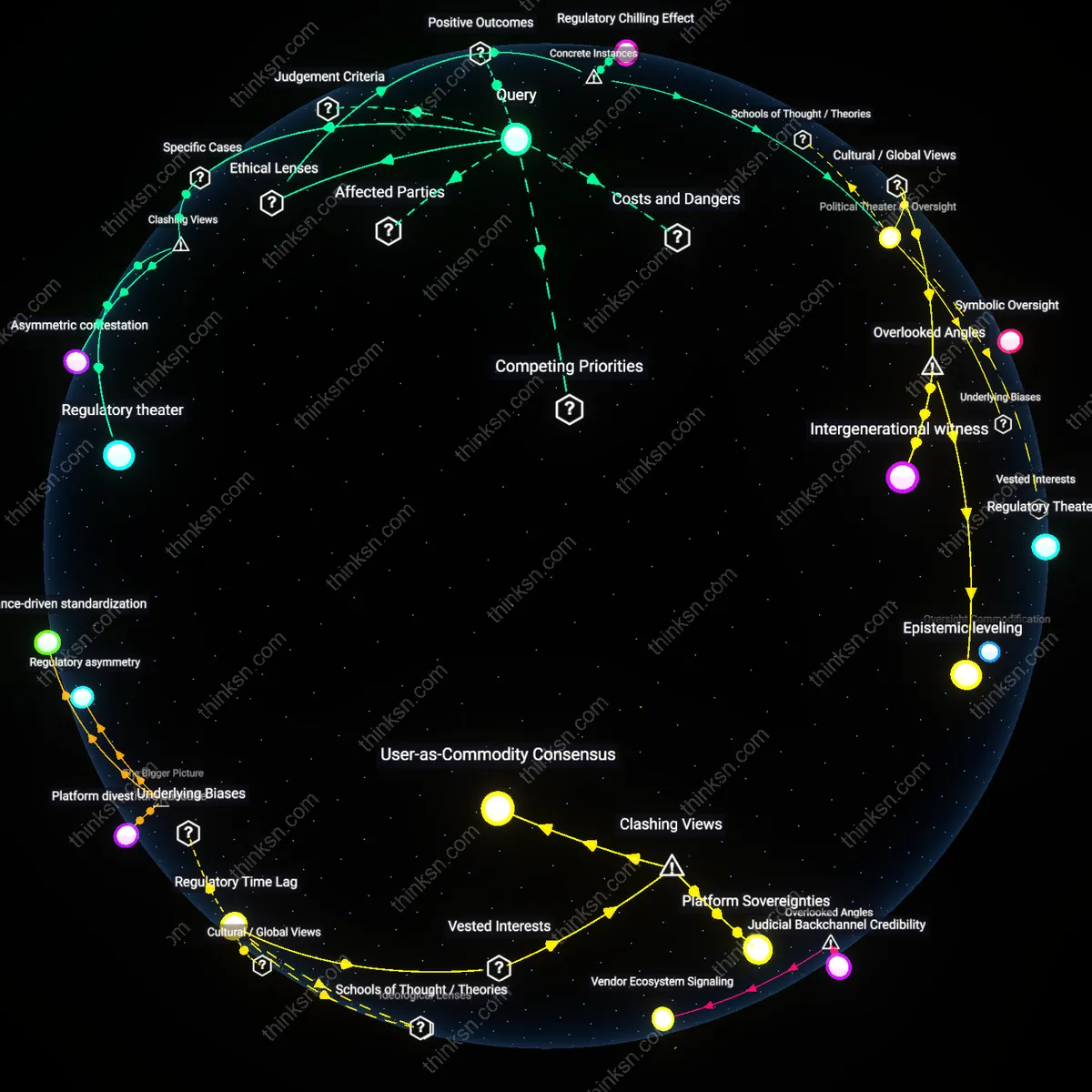
Platformized Trust
The mandated interoperability-security trade-off reflects a historical shift from user-managed to platform-mediated trust, crystallized after the 2013 Snowden revelations intensified consumer reliance on curated ecosystems. Before this turning point, security was primarily a user-side responsibility involving patching and permissions; now, dominant app stores function as de facto trust brokers by enforcing sandboxing and code review, promising protection at the cost of openness. This reconfiguration benefits risk-averse consumers and institutions like banks that depend on predictable runtime environments, but it makes interoperability seams appear as existential threats rather than design choices—revealing how security has become a justification for platform control, not just a technical requirement.
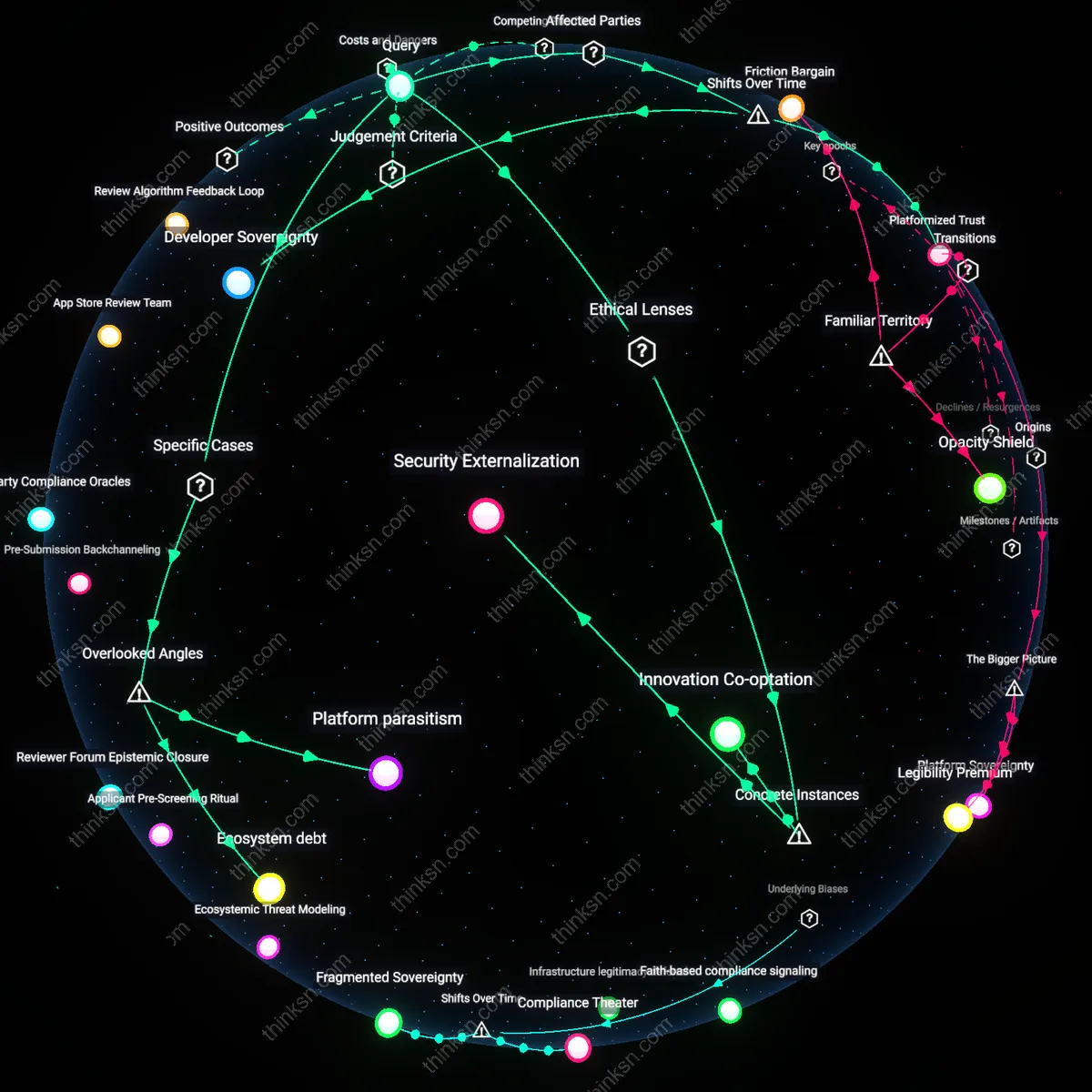
Security Externalization
Mandating interoperability for Apple’s App Store under the EU’s Digital Markets Act transfers the burden of verifying software integrity from a centralized gatekeeper to individual developers and peripheral app distribution channels, increasing systemic exposure to malware without proportional accountability mechanisms. This shift enables regulatory compliance with competition goals while displacing security risks onto less-resourced actors who lack Apple’s capacity for threat detection—revealing how normative design power in digital markets can be reconfigured without corresponding liability reallocation. The non-obvious consequence is that regulatory enforcement against gatekeeping may inadvertently legitimize risk decentralization under the guise of openness.
Innovation Co-optation
The 2023 implementation of South Korea’s Telecommunications Business Act, which compelled Google Play to accept alternative billing systems, demonstrated that interoperability mandates can be exploited by dominant platforms to absorb competitive threats while preserving core control vectors—Google simply incorporated third-party billing into its own audit framework, reinforcing compliance as a surface-layer concession. This case exposes how ethical frameworks prioritizing consumer choice, such as libertarian paternalism, fail to constrain platform power when procedural openness substitutes for substantive structural change. The underappreciated dynamic is that interoperability can function as a regulatory safety valve, allowing dominant firms to neutralize antitrust pressure without ceding strategic autonomy.
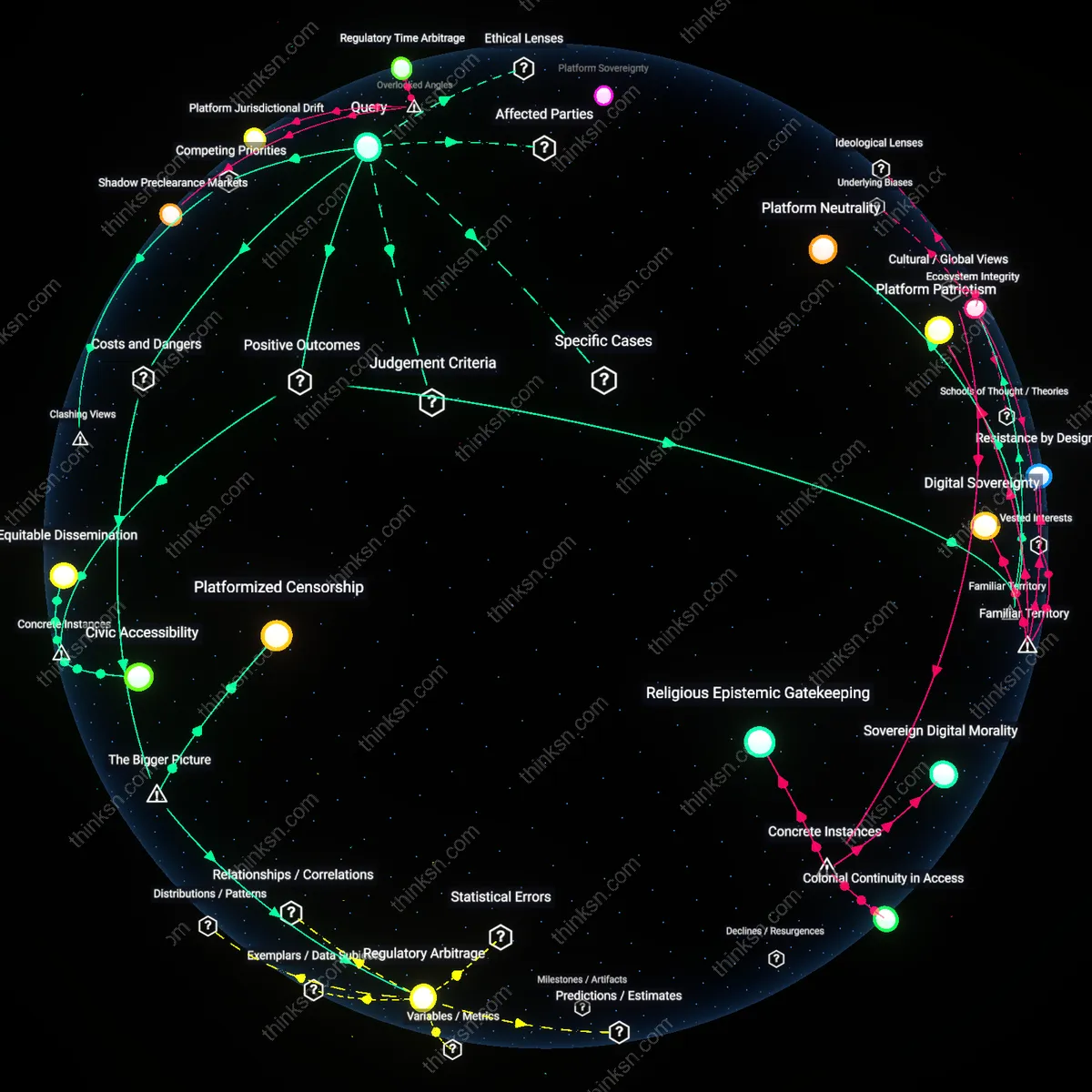
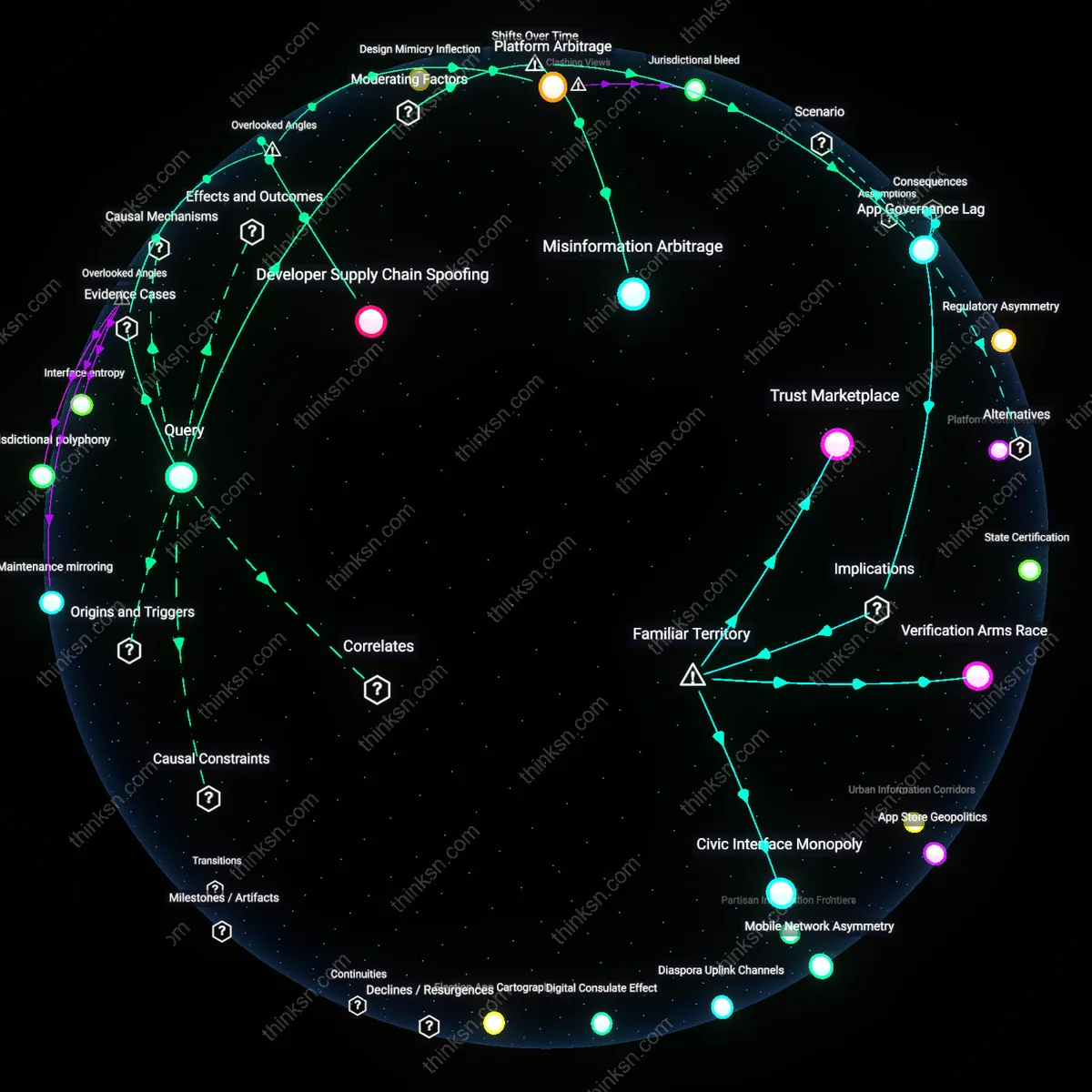
Jurisdictional Arbitrage
When Epic Games leveraged California’s legal environment to challenge Apple’s App Store policies in *Epic Games v. Apple* (2021), it highlighted how interoperability demands emerge selectively within jurisdictions that prioritize market fairness over ecosystem integrity, creating divergent compliance paths that platforms can exploit to maintain global control. Apple responded by limiting sideloading to the EU under the DMA while reinforcing closure elsewhere, illustrating how dominant actors calibrate security rationales to regional legal thresholds rather than universal standards. This reveals that security arguments are not absolute technical constraints but negotiable justifications whose weight shifts according to the political ideology of the regulatory forum—particularly between technocratic regulation and ordoliberal interventionism.
Platform parasitism
Requiring interoperability from Apple’s App Store incentivizes superficial compliance through reverse-engineered API mimics that replicate functionality without security coordination, as seen in third-party iOS storefronts emerging under the Digital Markets Act. These workarounds depend on undocumented behaviors and exploit gaps in entitlement validation, forcing developers to adopt brittle integration methods that increase attack surface without Apple’s mitigation tools. This dimension is overlooked because regulators focus on market access rather than how shadow systems emerge at runtime, revealing that the most critical risk is not direct breaches but erosion of coherent defense logic across duplicated platforms. The unaccounted dependency is the integrity of shared execution semantics between official and mandated interoperable layers.
Ecosystem debt
Mandating interoperability for Google Play increases long-term vulnerability accumulation by fragmenting security update pathways across alternate Android distribution channels, as evidenced by OEM-specific app stores in India that delay critical patches to maintain compatibility with custom billing middleware. These delays stem from unaligned incentives between Google, device manufacturers, and resellers, where security becomes a secondary constraint to revenue integration. The overlooked mechanism is not the act of opening distribution but the compounding cost of sustaining secure convergence across divergent forks—an invisible liability that grows with each added interoperable node. This shifts the frame from acute risk to chronic degradation of the update substrate.