Digital Drivers License: Convenience or Surveillance Risk?
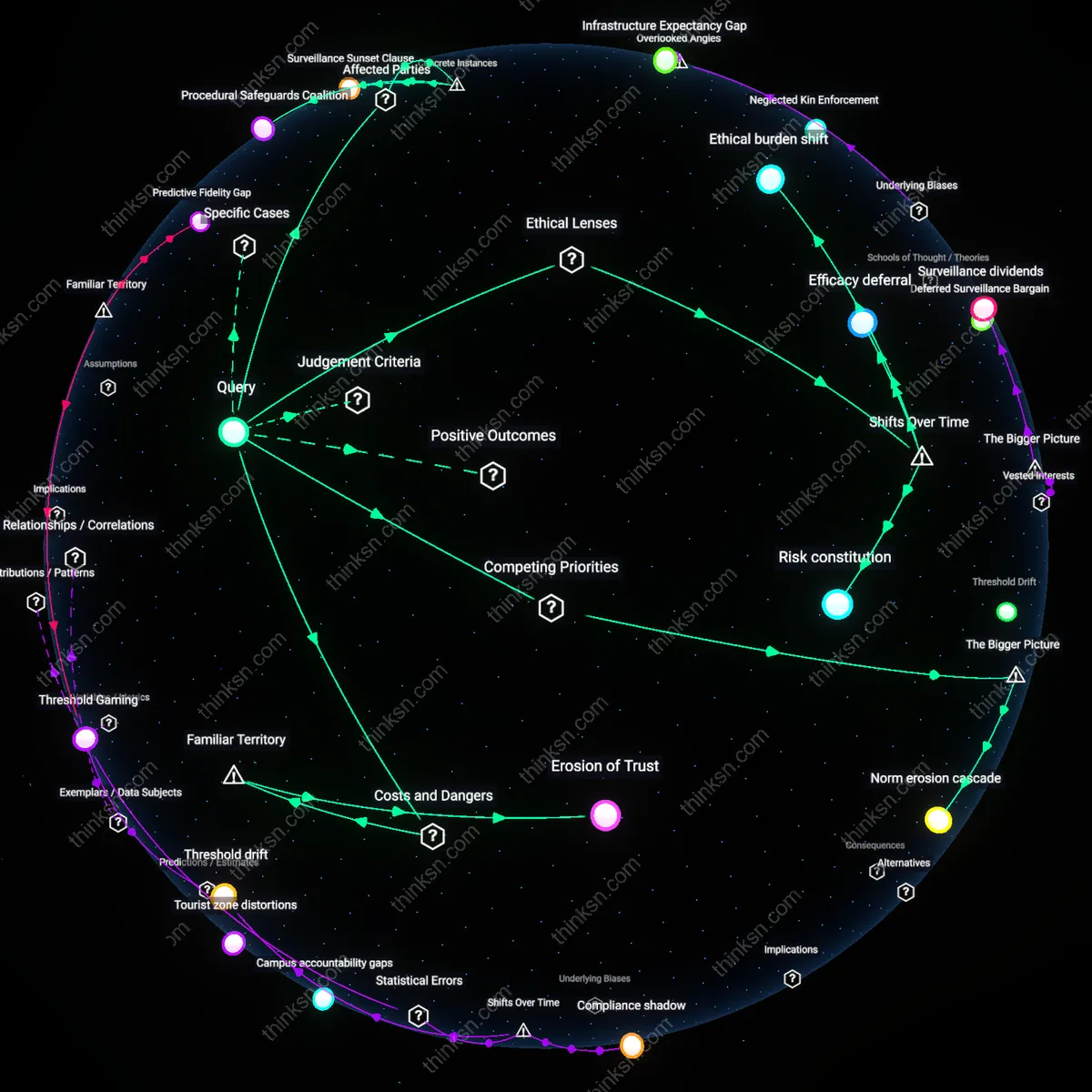
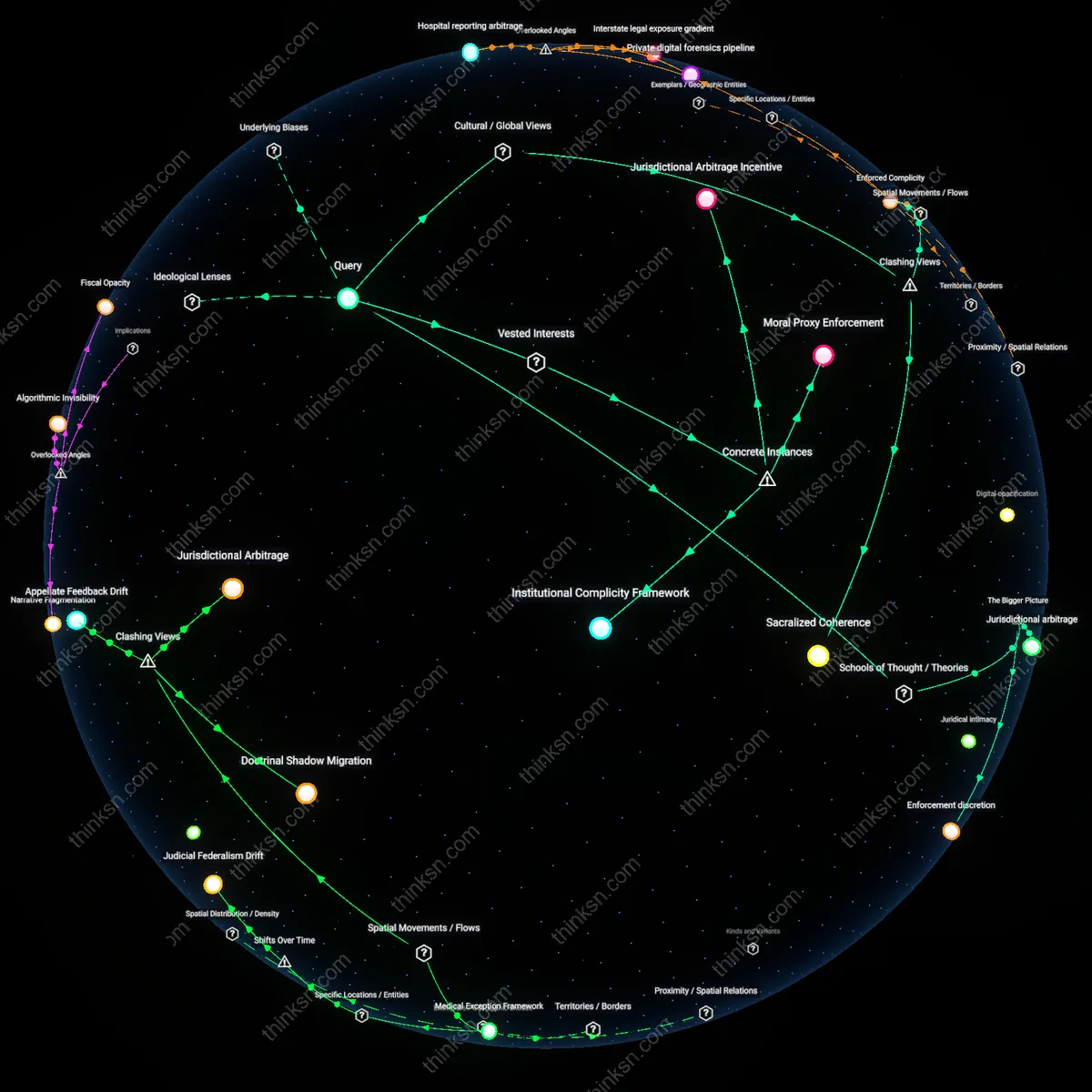
Analysis reveals 9 key thematic connections.
Key Findings
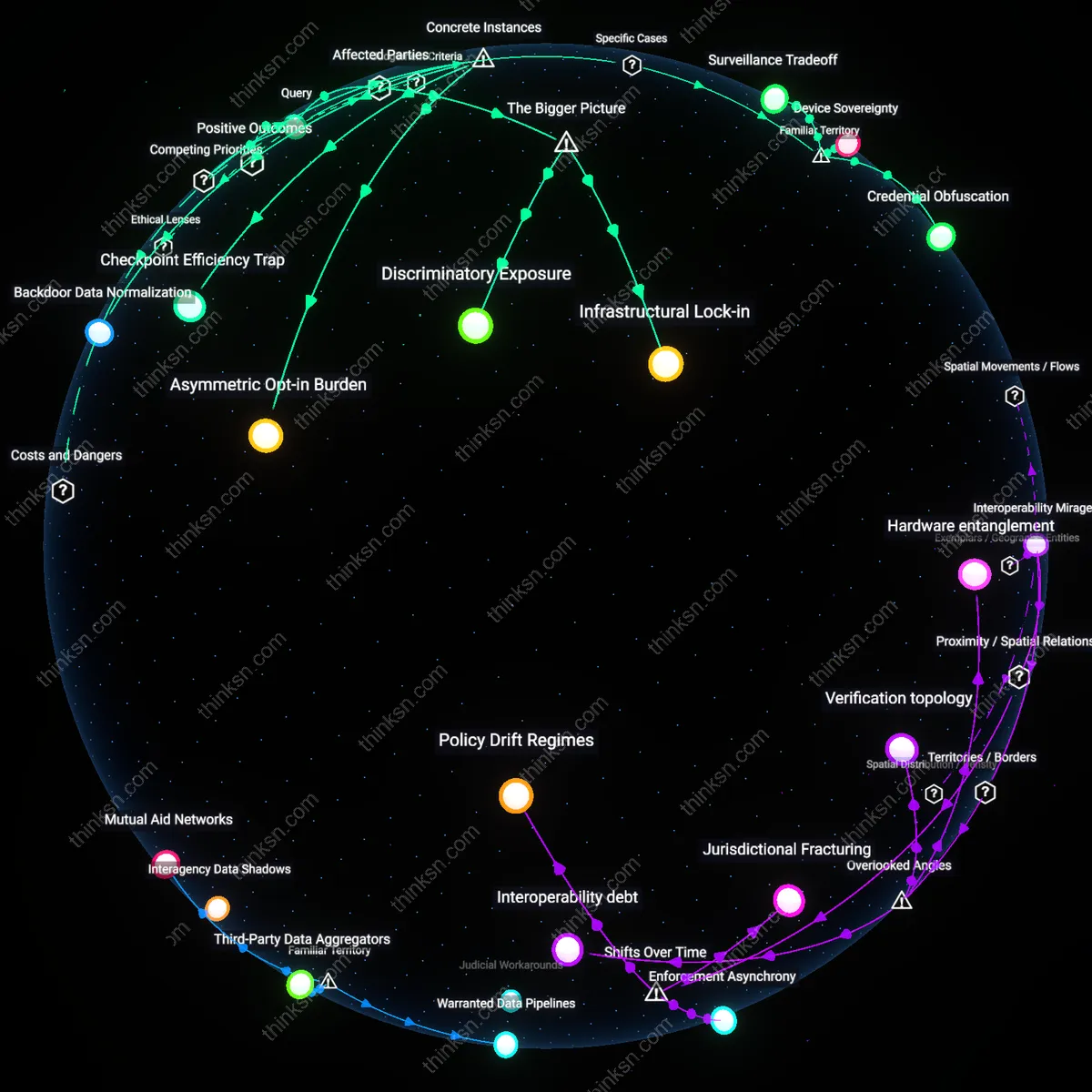
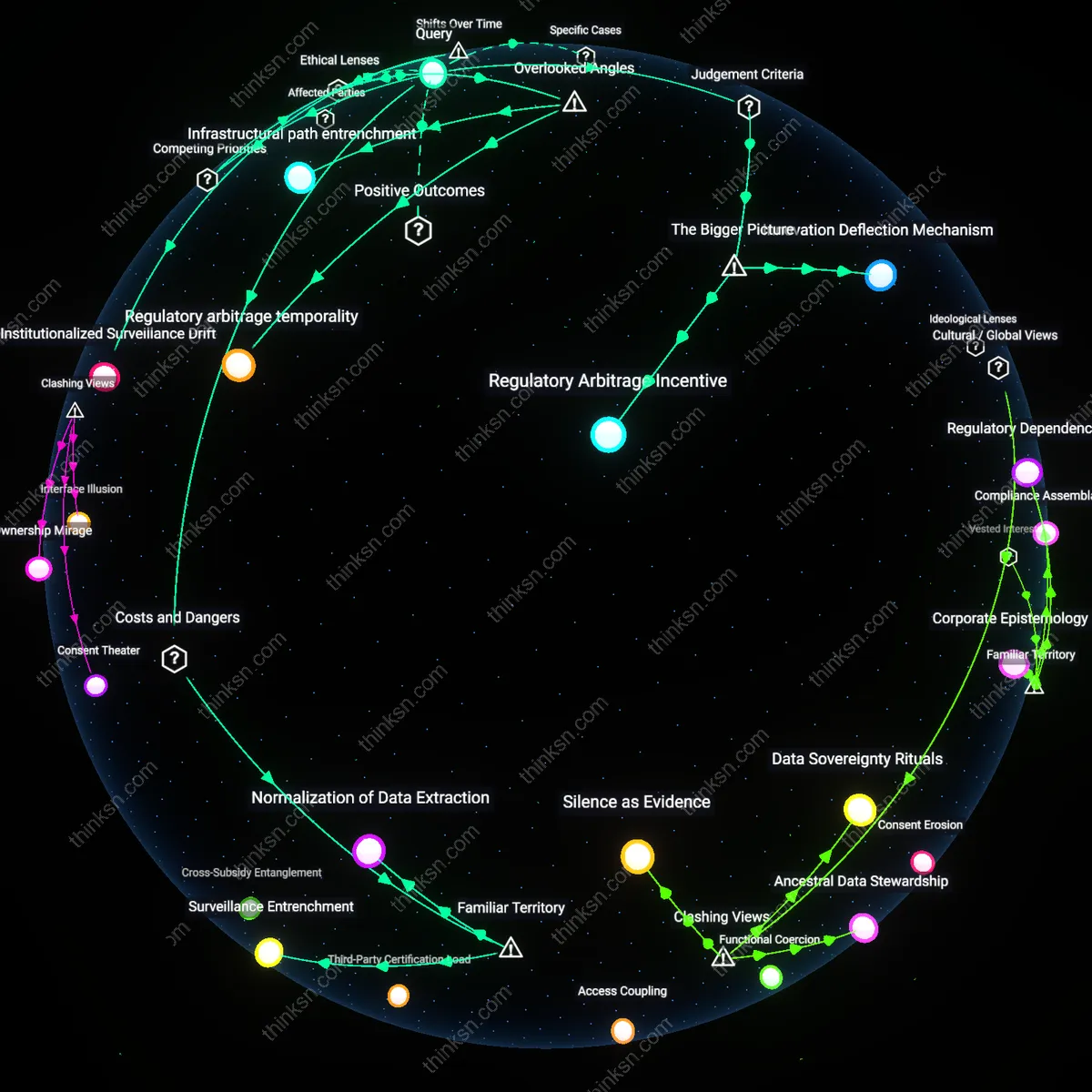
Infrastructural Lock-in
Individuals can balance digital driver's licenses against surveillance risks by collectively demanding interoperability standards that limit data centralization, because public adoption fuels long-term dependence on backend systems controlled by state-technology partnerships; this creates path dependency where opt-out becomes practically impossible as transportation, banking, and age verification services integrate with the same infrastructure, privileging convenience over privacy in ways that are rarely reversible once institutional momentum solidifies.
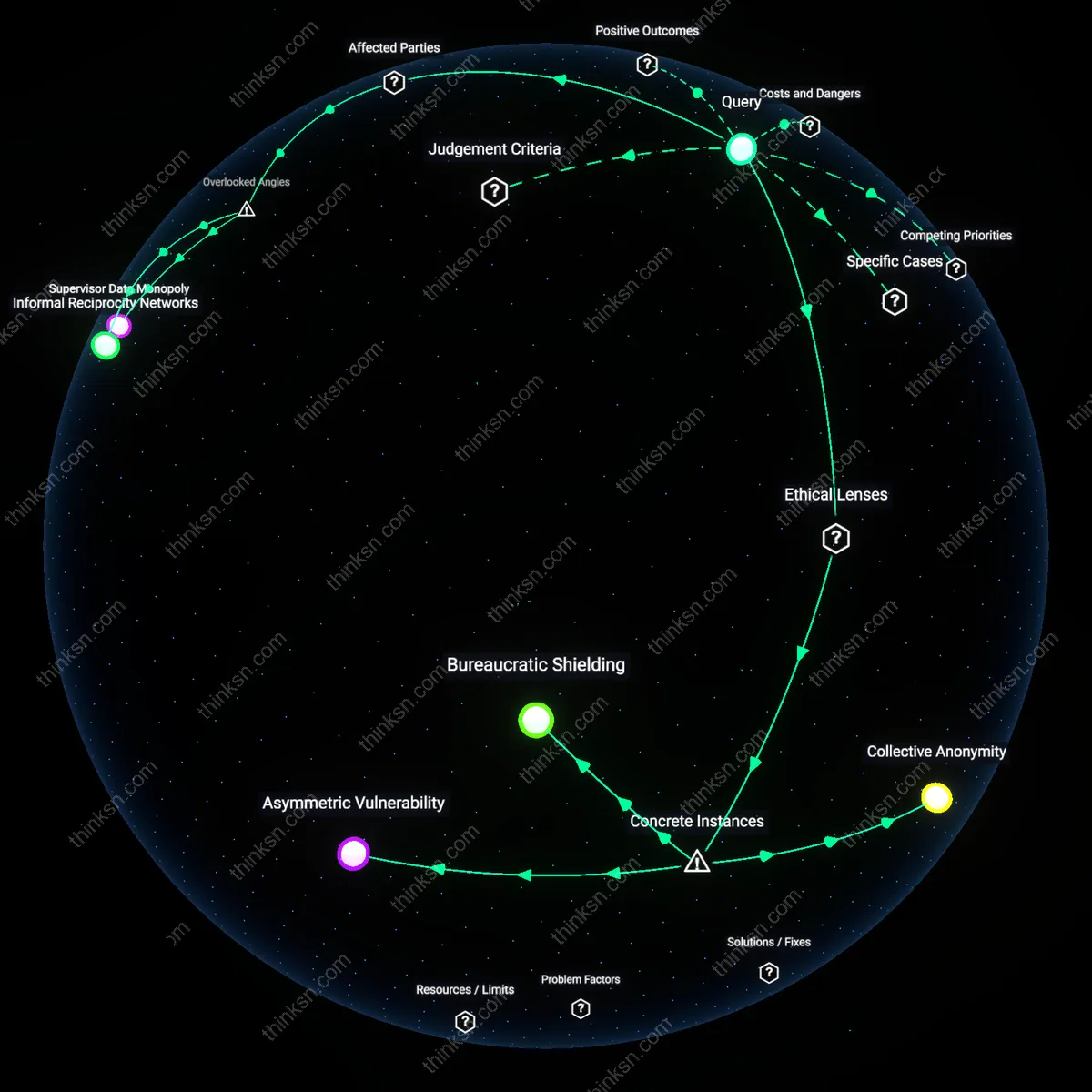
Discriminatory Exposure
Marginalized communities, particularly undocumented migrants and people of color, face disproportionate tracking risks with digital licenses due to pre-existing policing patterns and immigration enforcement collaboration, meaning their adoption of state digital IDs intensifies systemic surveillance without reciprocal protections; this imbalance persists because law enforcement agencies leverage statutory ambiguities in data access laws to justify expanded monitoring under public safety rationales, normalizing intrusion in communities already over-policed.
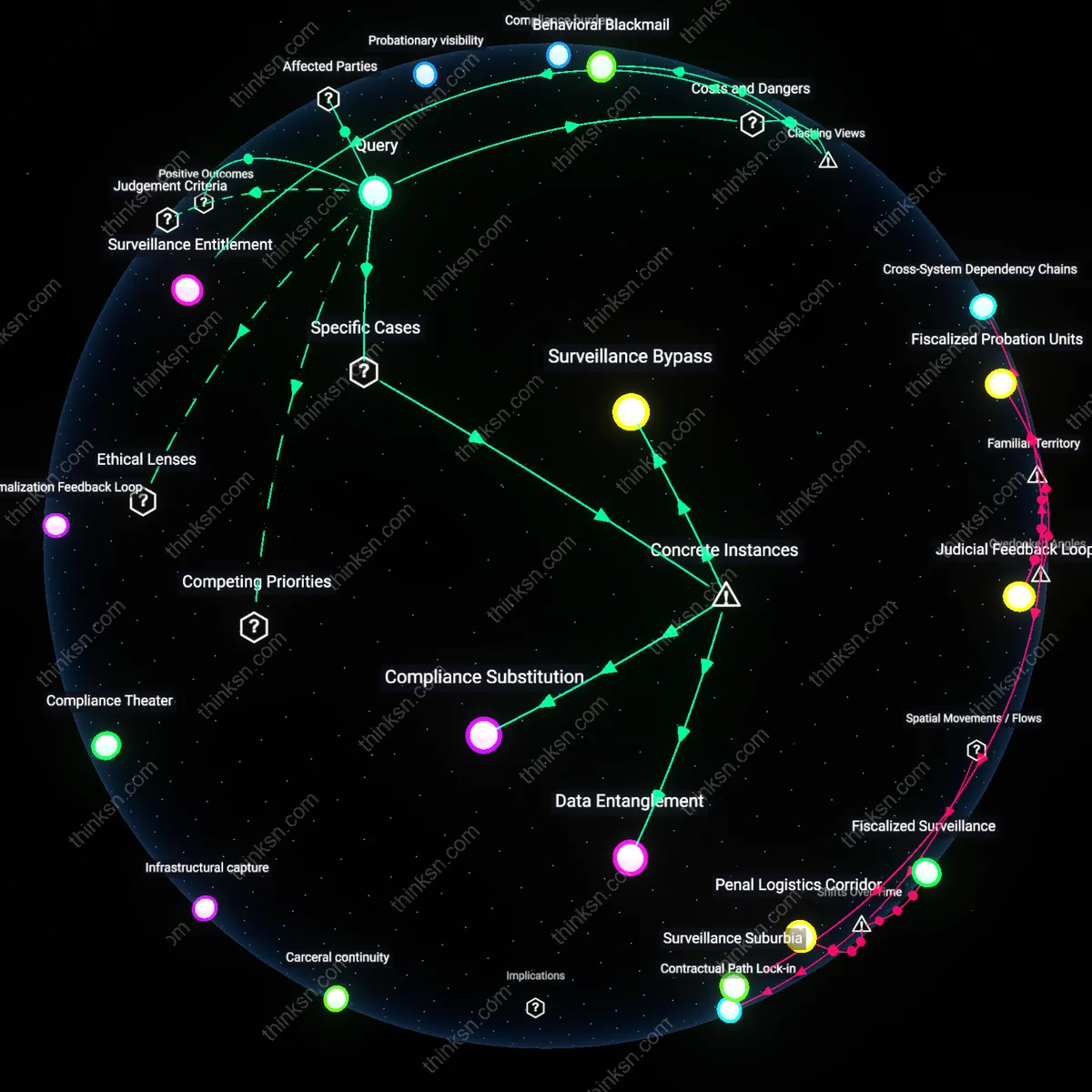
Compliance Theater
Privacy safeguards in digital license programs often serve symbolic rather than operational functions because government agencies and tech vendors co-produce transparency reports and audit frameworks that emphasize procedural compliance over enforceable limits on data reuse, allowing tracking capabilities to expand beneath the surface of public accountability; this dynamic is sustained by legislative reliance on industry self-certification and the absence of private rights of action for misuse, rendering individual consent functionally meaningless.
Asymmetric Opt-in Burden
In California’s 2022 pilot of Apple Wallet-integrated digital driver’s licenses, state officials framed participation as voluntary, yet law enforcement agencies in Los Angeles began prioritizing faster ID checks for digital license holders at checkpoints, creating a de facto incentive structure that pressured individuals to adopt the technology despite unclear data retention safeguards; this mechanism reveals how convenience is not neutral but systematically amplified at the institutional level, making refusal functionally costly. The non-obvious insight is that voluntariness collapses not through coercion but through operational asymmetry—where institutions reward one choice with efficiency while allowing the alternative to decay in usability.
Backdoor Data Normalization
When Arizona implemented its digital license system via the CLEAR app in 2021, biometric authentication was required for access, and although the state claimed data remained on-device, forensic analysis by the Electronic Frontier Foundation later revealed that facial recognition templates were routinely uploaded to cloud servers maintained by IDEMIA, a private contractor also supplying FBI systems; this integration created an invisible pipeline where opt-in personal data contributed to law enforcement databases without judicial oversight. The core revelation is that privacy erosion occurs not at the moment of state surveillance, but at the point where commercial authentication infrastructure absorbs public identity systems.
Checkpoint Efficiency Trap
In Florida’s I-Drive safety corridor program launched in 2023, highway patrol units used mobile readers to scan digital licenses during routine traffic stops, reducing average interaction time by 40 percent compared to physical checks, which led to increased stop frequency under performance quotas—effectively turning time savings into expanded surveillance capacity. The underappreciated dynamic is that efficiency gains in administrative processes can directly fuel mission creep, transforming convenience into a force multiplier for policing, particularly in jurisdictions with quota-driven enforcement cultures.
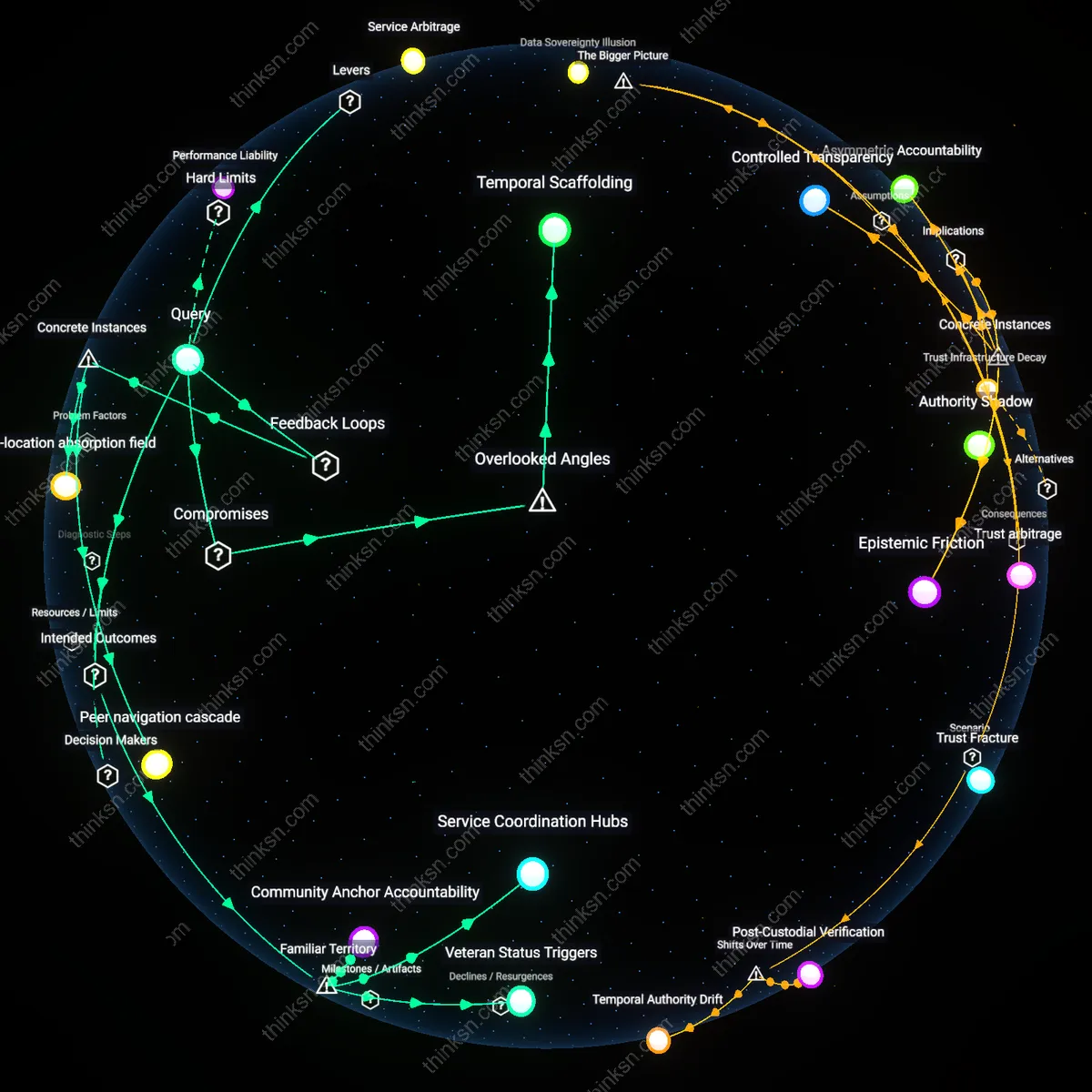
Surveillance Tradeoff
Limit access to digital driver's licenses through state-controlled verification systems to restrict real-time law enforcement queries. State motor vehicle departments—like the Louisiana OMV, which suspended its digital license program after public backlash over police surveillance—act as gatekeepers by requiring judicial approval or audit logs for officer-initiated scans, leveraging their role as credential issuers to slow unwarranted tracking. This mechanism is significant because it embeds procedural friction in credential verification, countering the default assumption that digital IDs inherently enable seamless surveillance by making each data access a traceable administrative act rather than an instantaneous scan.
Device Sovereignty
Store digital driver's licenses in user-controlled mobile wallets that require explicit, one-time consent for data release, such as Apple Wallet’s implementation in Arizona and Maryland, where the license remains encrypted and only visible when the user unlocks it. This approach leverages the smartphone as a personal trust boundary—already familiar as a private communication device—shifting the locus of control from government infrastructure to individual devices, a non-obvious defense because it repurposes consumer technology habits to resist institutional overreach, making tracking contingent on physical access and user cooperation rather than networked databases.
Credential Obfuscation
Design digital licenses to transmit only minimal, context-specific attributes during verification—such as age instead of full identity—using privacy-preserving technologies like zero-knowledge proofs, as piloted in the state of Wyoming’s blockchain-based mobile ID project. This approach exploits the gap between public fear of 'tracking everything' and the technical feasibility of selective disclosure, making it possible to verify eligibility without exposing linkable identity data, a counterintuitive yet functional solution that reshapes the familiar tradeoff between convenience and privacy by decoupling verification from surveillance at the data-layer.