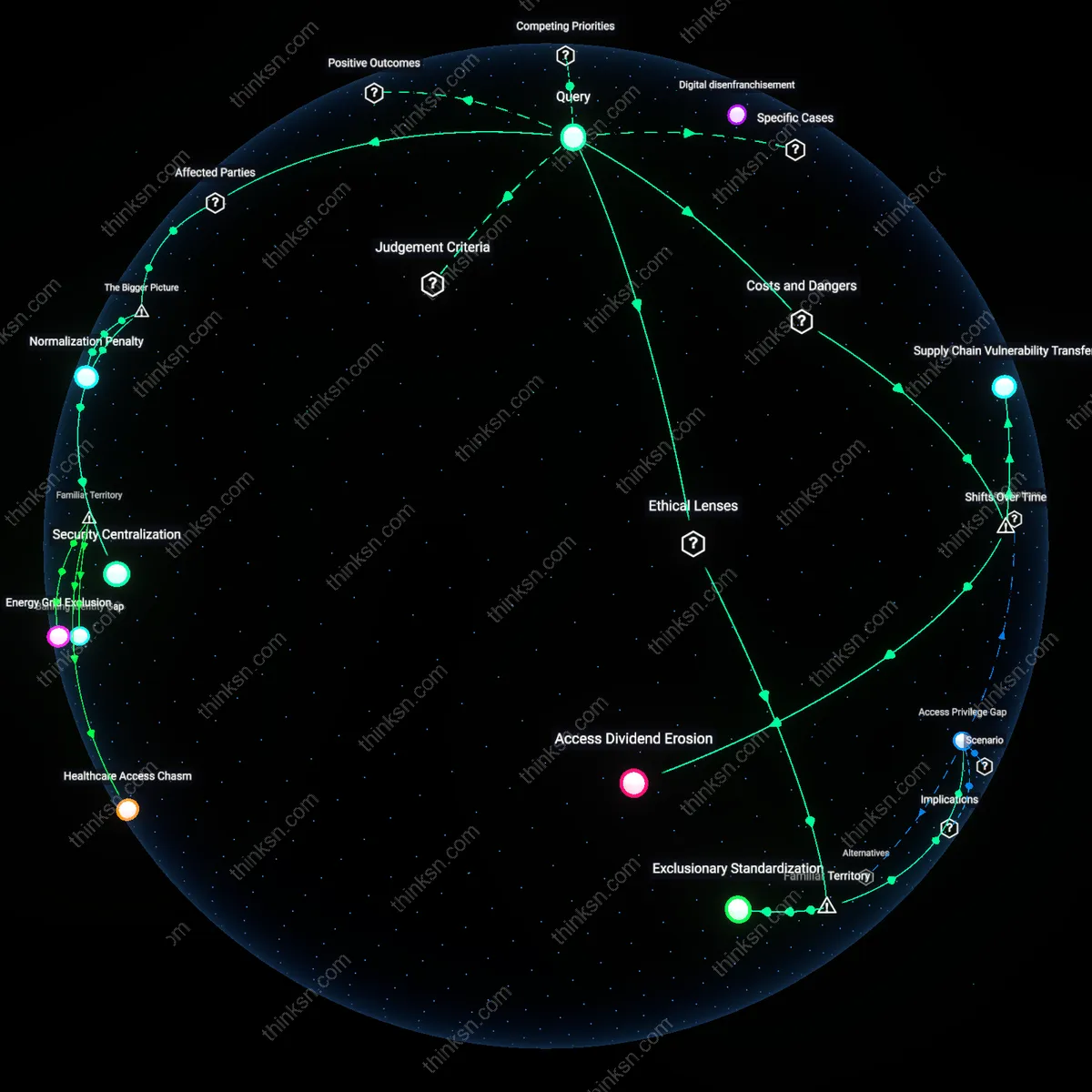
Passwordless Auth: When Hardware Tokens Harm Security Equity?
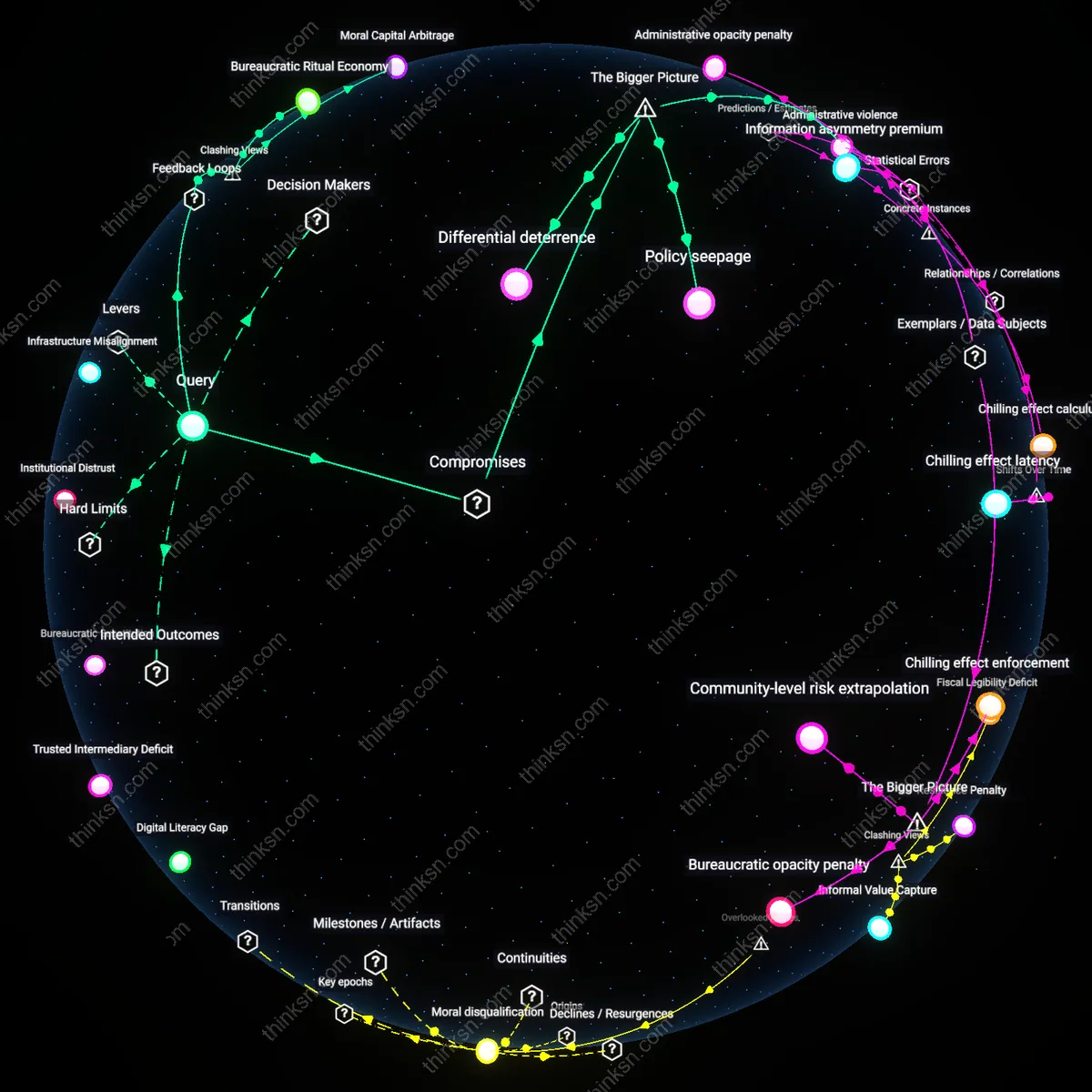
Analysis reveals 8 key thematic connections.
Key Findings
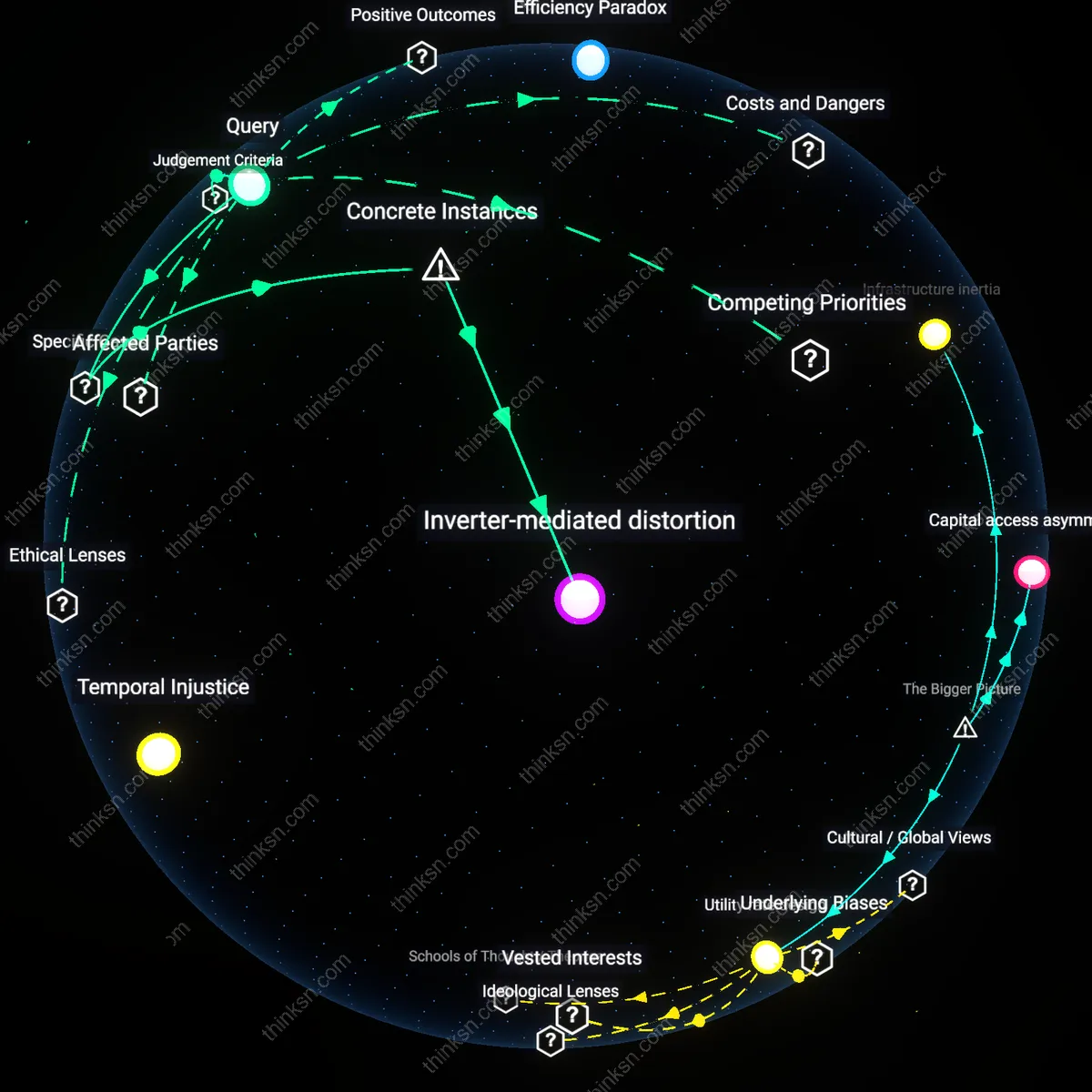
Access Friction
When password-less systems mandate hardware tokens, users without access face immediate exclusion from essential digital services, particularly in low-income or rural populations where device ownership and technical infrastructure are limited. Governments and private service providers implementing token-based systems often overlook distributional inequities, assuming universal device availability, which embeds socioeconomic stratification into authentication architecture. This creates a systemic barrier not due to user incompetence but institutional underestimation of access gaps—what appears as user disadvantage is in fact institutionalized digital redlining shaped by infrastructure neglect.
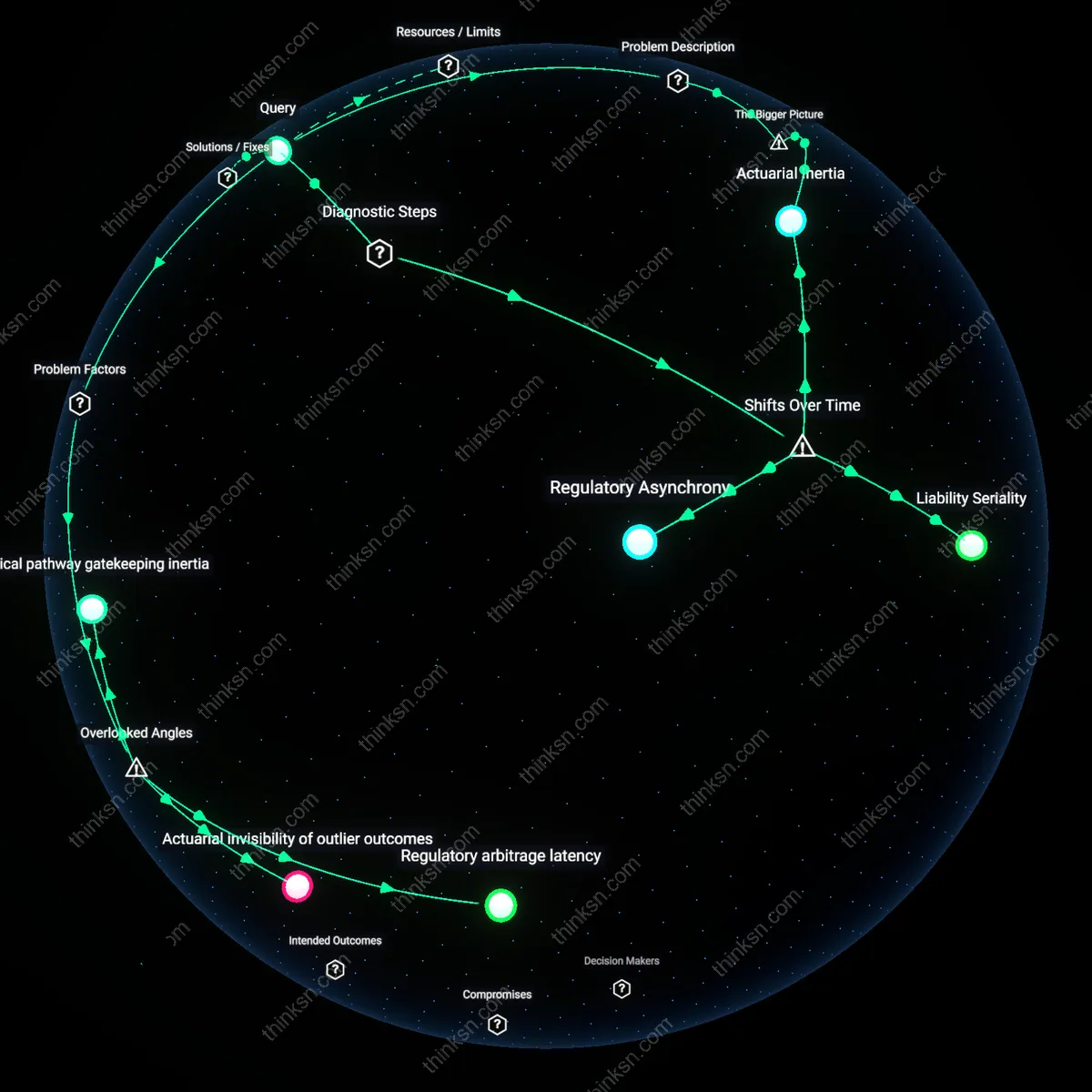
Security Centralization
Hardware token mandates concentrate authentication authority within a narrow set of manufacturers and issuing institutions, such as tech corporations or federal agencies, which then determine who qualifies for token issuance and under what conditions. This shifts the point of failure from individual password hygiene to institutional gatekeeping, where bureaucratic inertia, surveillance concerns, or supply chain bottlenecks can delay or deny token access—particularly affecting marginalized groups like refugees or the unhoused who lack verifiable identities. The resulting security model appears stronger technically but weakens democratically, privileging system control over user autonomy in ways rarely visible in mainstream security discourse.
Normalization Penalty
As organizations adopt hardware tokens as the new standard, legacy password-based access is deliberately degraded or removed, penalizing users who rely on older, more accessible methods—not because they are inherently insecure, but because maintaining parallel systems is deemed inefficient by centralized IT operations. This systemic preference for uniformity over inclusivity disadvantages populations with intermittent internet access, limited technical literacy, or reliance on public computing resources, such as elderly users or incarcerated people. The resulting exclusion is not accidental but baked into modernization logic that treats accessibility as an afterthought rather than a design imperative.
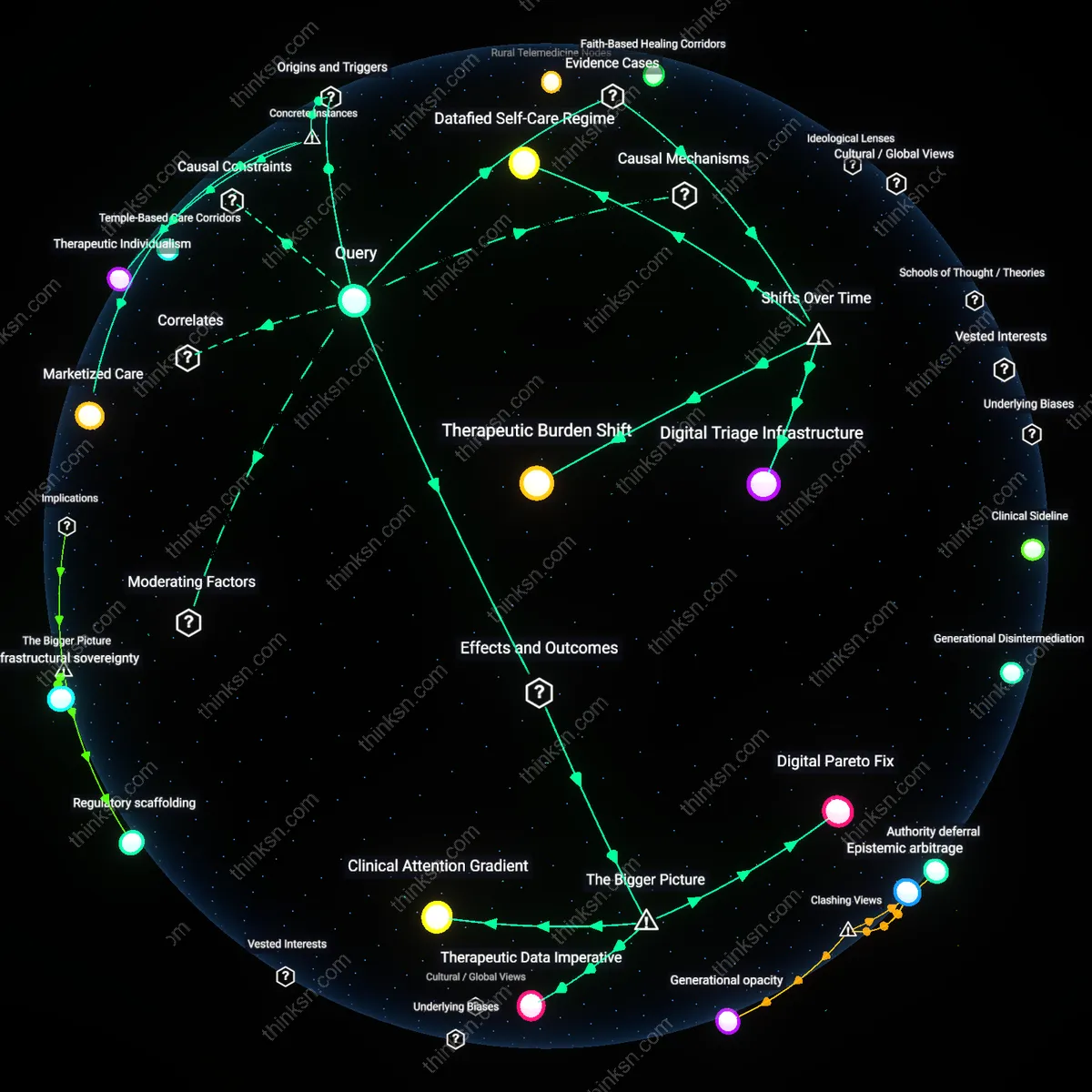
Access Dividend Erosion
When password-less authentication marginalizes users without hardware tokens, it creates a security disadvantage by converting universal access into a tiered system where only those with prior technological capital can benefit—this shift became pronounced after 2015, when major tech platforms like Google and Microsoft began standardizing FIDO U2F tokens, transforming authentication from a universally accessible password model into a device-dependent regime; as institutional trust shifted from knowledge-based to possession-based credentials, the residual barrier stranded low-income, elderly, and rural users who could not afford or operate physical tokens, revealing a systemic inequity that was previously masked under broad password accessibility. The non-obvious consequence is that security centralization in hardware increases aggregate protection for some while actively degrading access security for others, not by accident but by design trajectory.
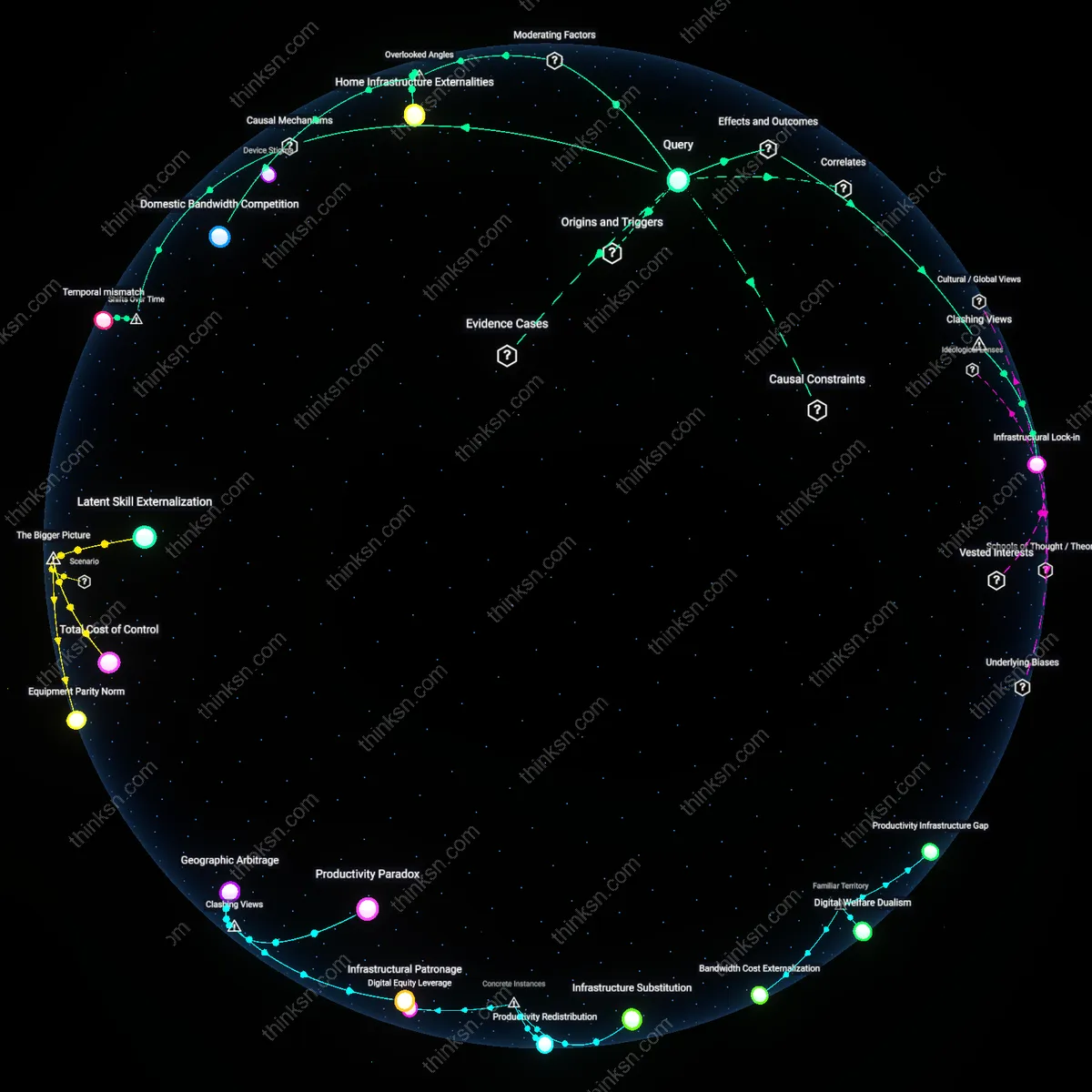
Legacy System Entanglement
The adoption of hardware tokens disadvantages users who rely on legacy systems that cannot support them, a risk that intensified after the 2020 shift toward remote access during the pandemic, when governments and enterprises accelerated token-based login while leaving public kiosks, library computers, and healthcare portals on outdated infrastructure; these users—who depend on shared or non-upgradable terminals—are forced into fallback password systems that are now less maintained, less supported, and more vulnerable due to diverted development resources. The critical shift lies in how password systems, once universally supported, became technical debt in a token-dominant ecosystem, making fallback mechanisms inherently riskier over time and exposing users without tokens to greater surveillance and exploitation through neglected channels.
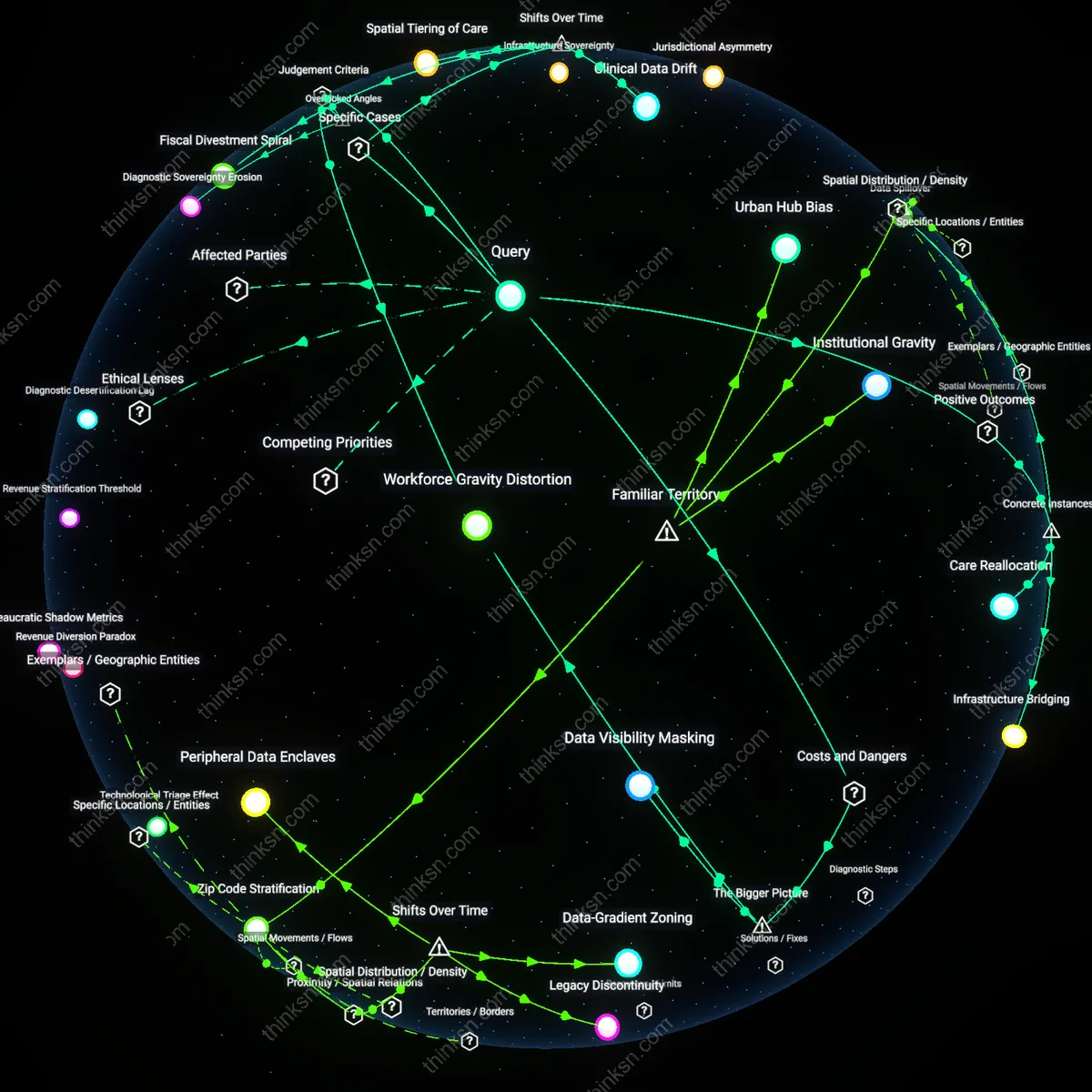
Supply Chain Vulnerability Transfer
After 2017, when high-profile phishing attacks drove widespread adoption of hardware tokens by financial and defense sectors, the security burden shifted from user knowledge to physical device integrity, disadvantaging users in regions with limited access to authentic hardware due to global supply bottlenecks or counterfeit markets; in nations with restricted tech imports or weak logistics networks, users either face prolonged exposure waiting for tokens or resort to unverified third-party devices that introduce backdoors. The underappreciated transformation is that authentication security became geographically contingent not at the software level, but at the material level—where geopolitical trade flows and manufacturing monopolies now dictate individual access risk, turning a local authentication decision into a global supply chain dependency.
Access Privilege Gap
Hardware tokens create a security disadvantage when users without device ownership are forced into weaker authentication systems. This occurs in enterprise environments where privileged staff receive company-issued tokens, while contractors or lower-tier workers rely on password-based access, creating a tiered security model enforced by IT policy. The asymmetry isn’t merely logistical—it entrenches differential risk exposure based on institutional hierarchy, a dynamic rarely acknowledged when discussing ‘universal’ security upgrades. What feels like a neutral tool rollout becomes a vector of access stratification.
Exclusionary Standardization
Mandating hardware tokens without alternative methods disadvantages users in regions with unstable supply chains or restricted import controls, such as rural clinics in low-bandwidth areas of Sub-Saharan Africa relying on donated or legacy devices. Global standards bodies like FIDO Alliance promote token-based login as best practice, but their one-size-fits-all framing ignores infrastructural pluralism, turning ethical commitments to security into de facto exclusion. The unspoken assumption—that all users inhabit a plug-and-play digital world—masks how standardization can penalize those operating outside dominant technological ecosystems.