Is a Single Cloud Risky for Election Security?
Analysis reveals 6 key thematic connections.
Key Findings
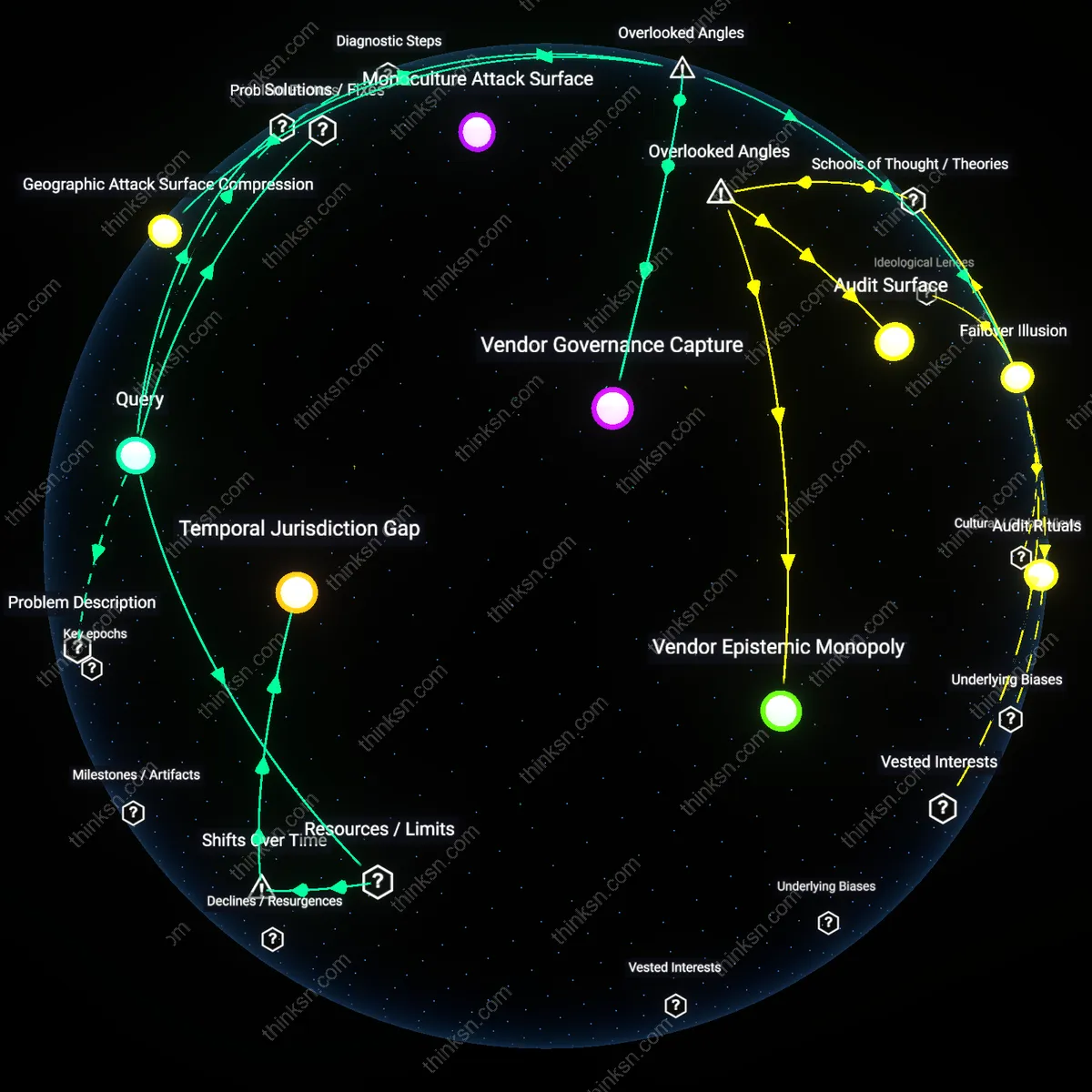
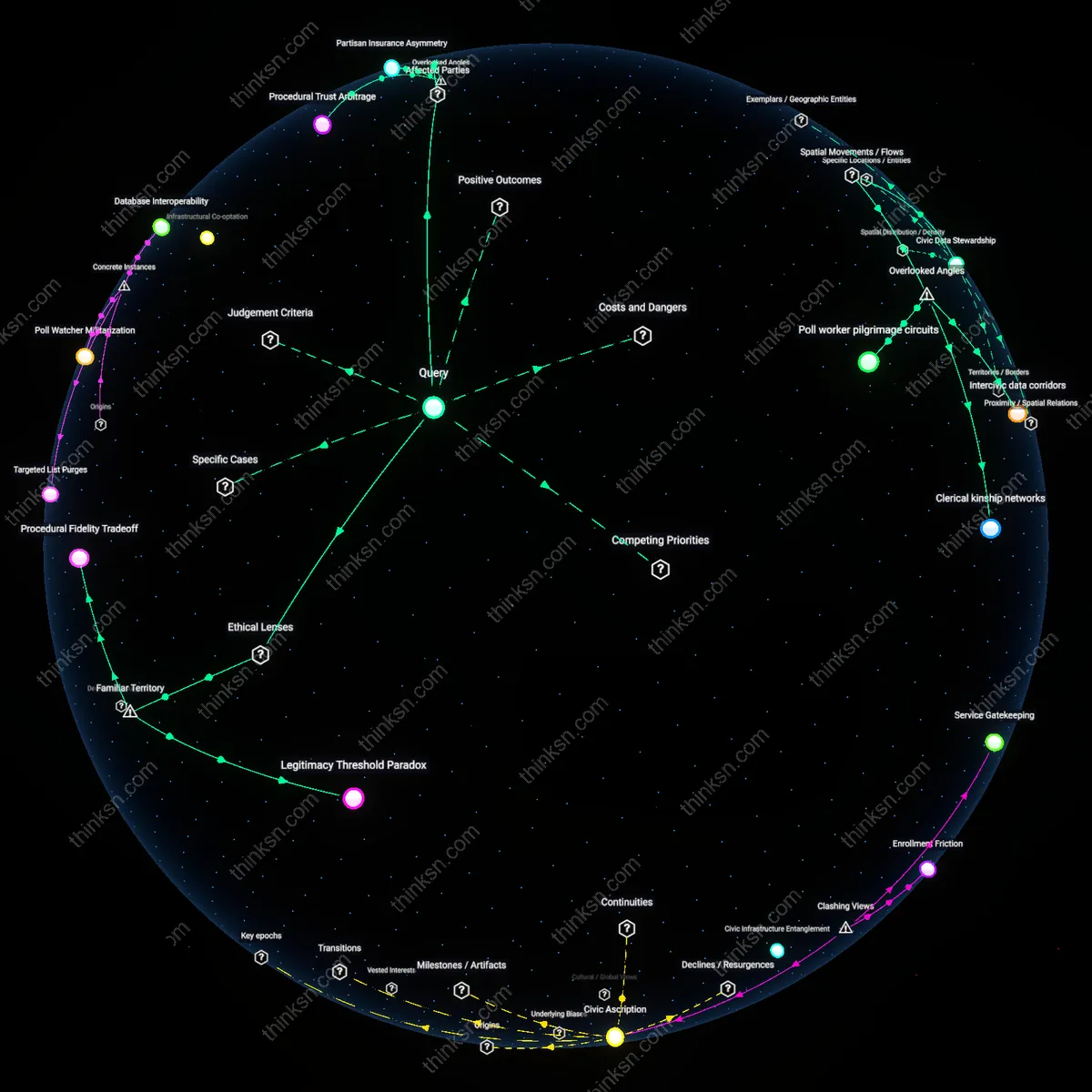
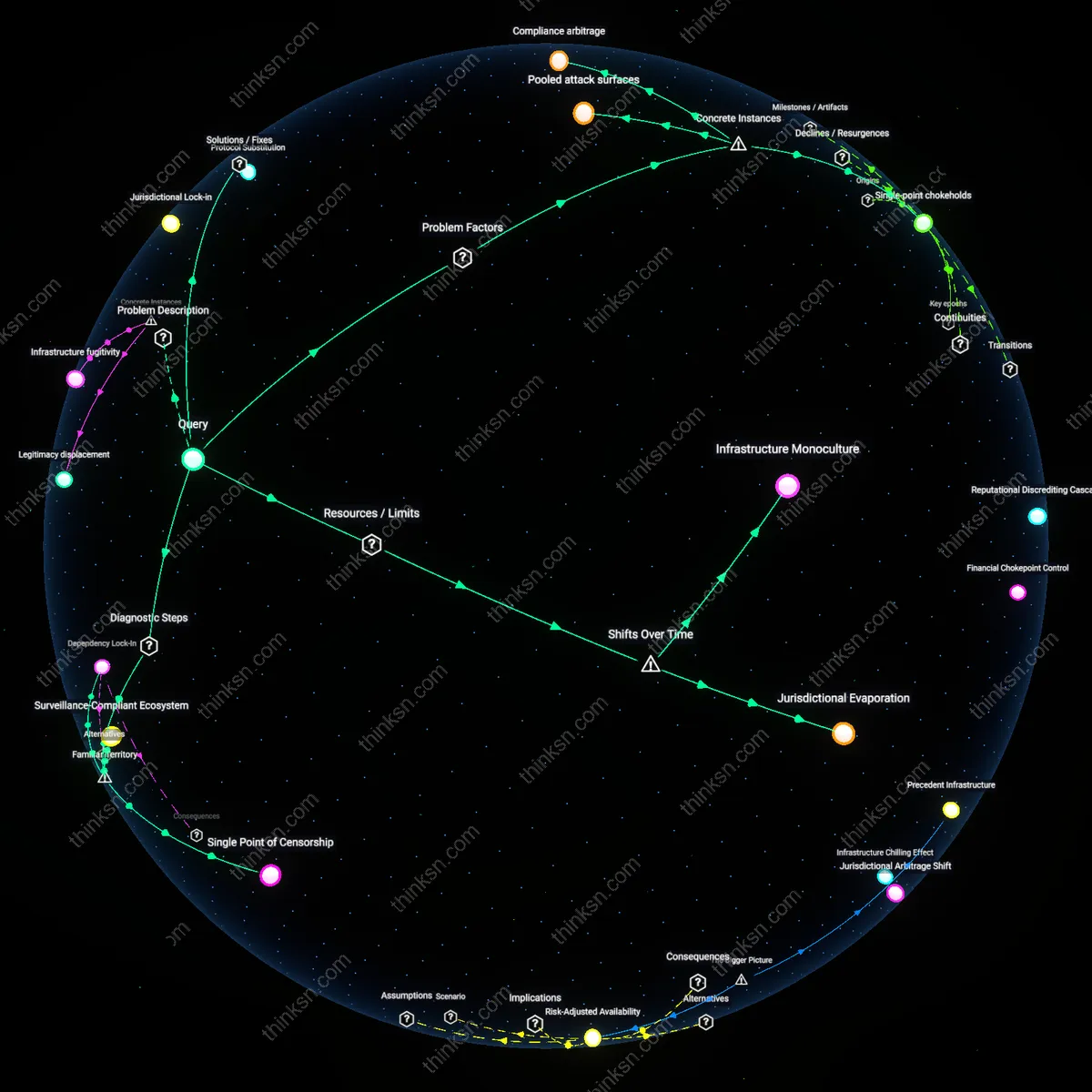
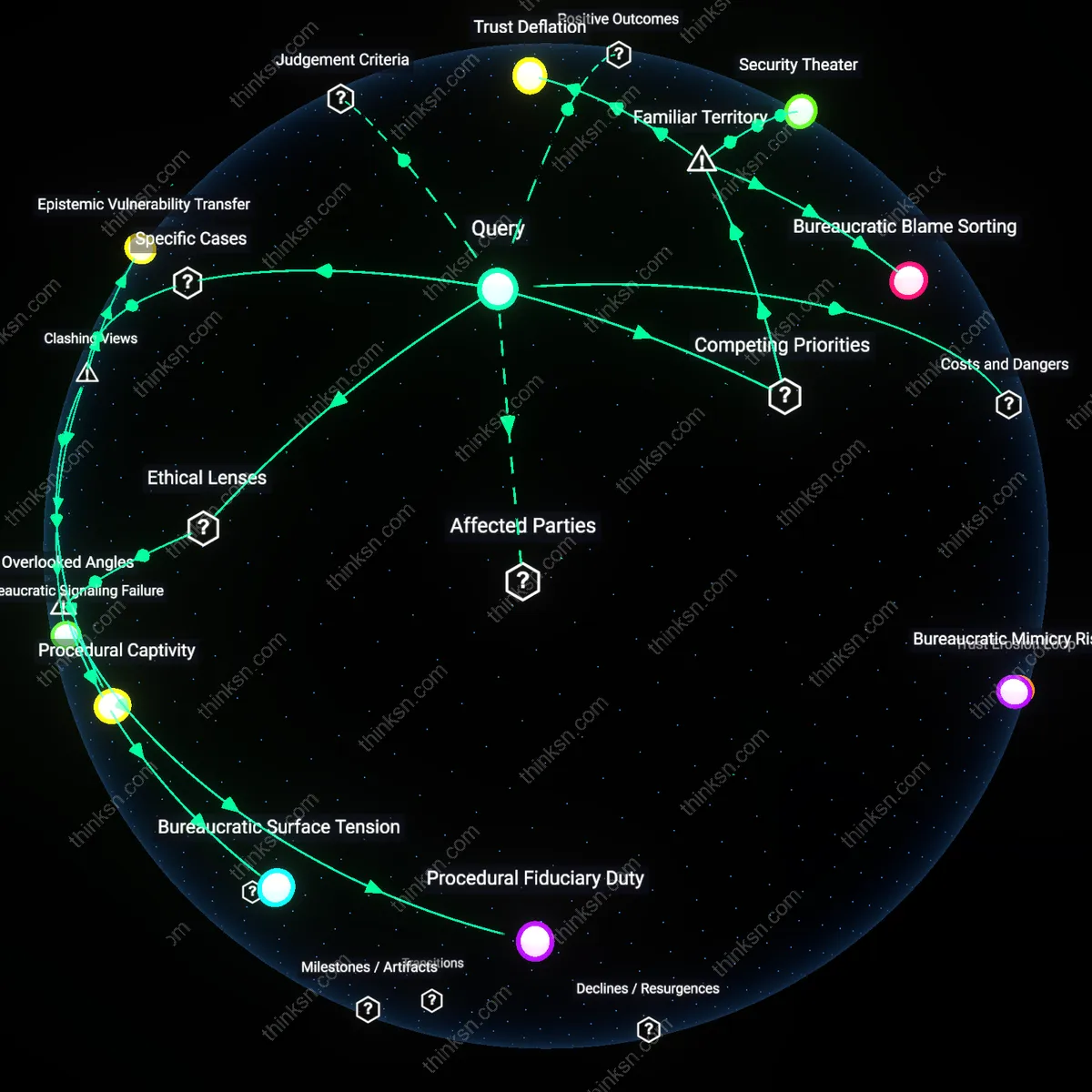
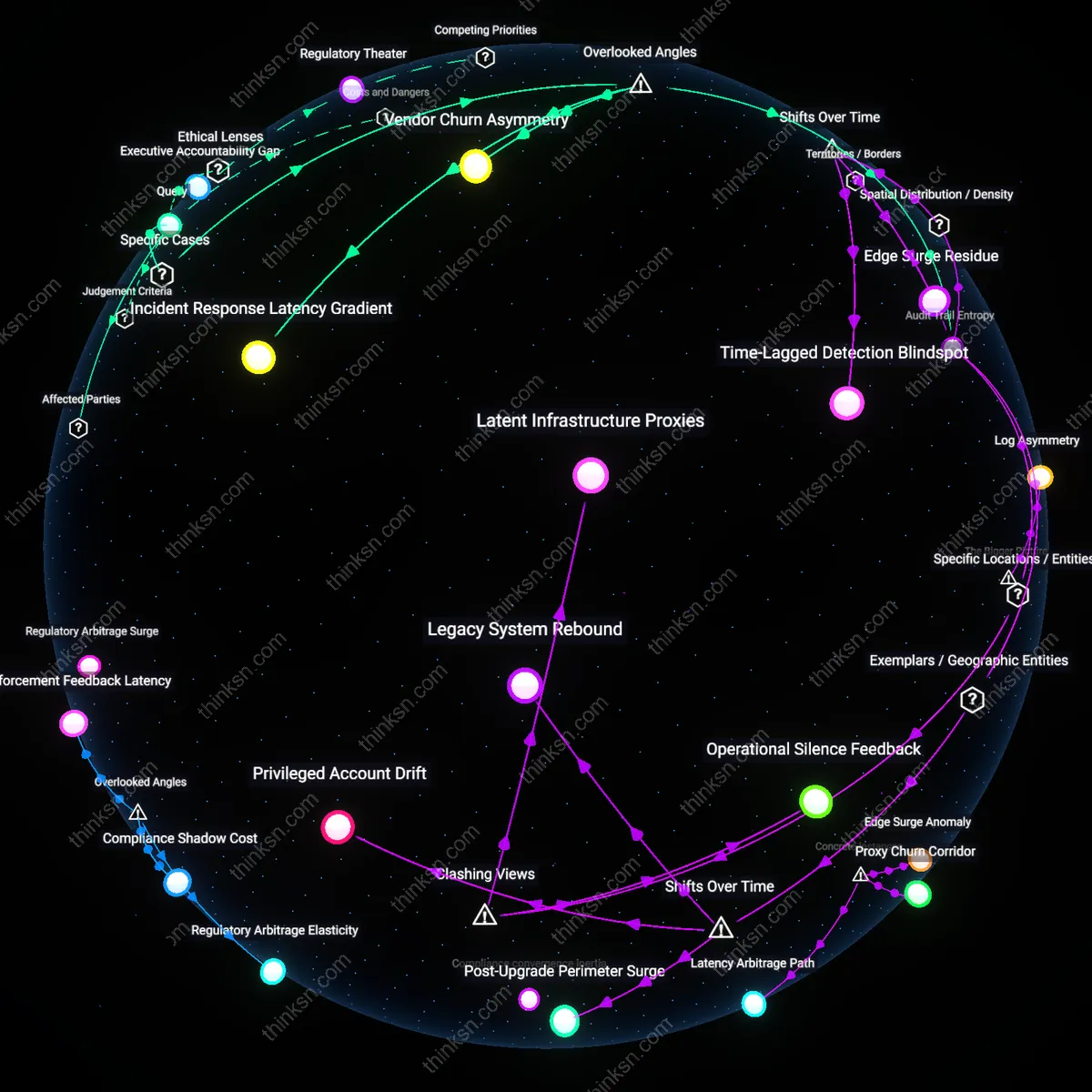
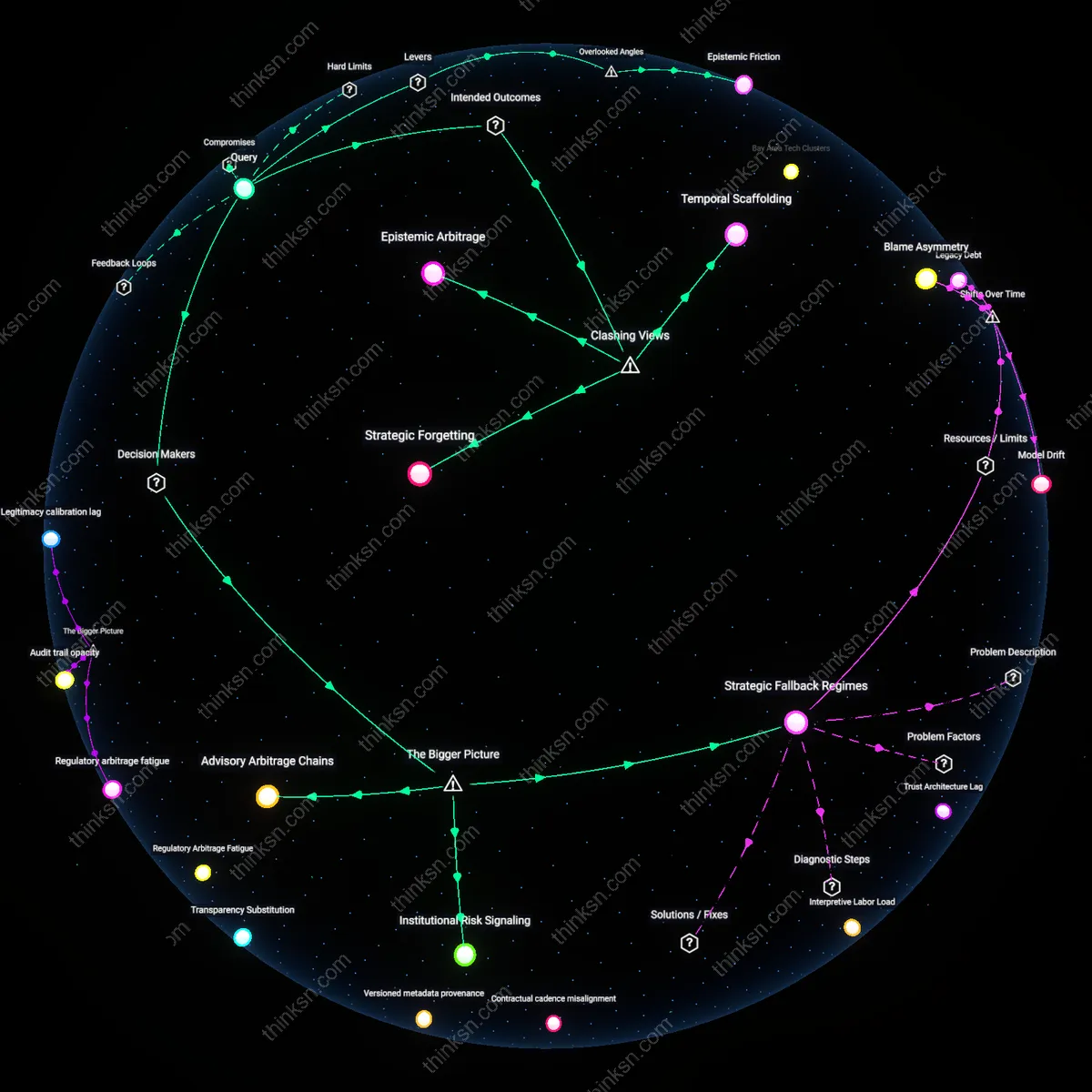
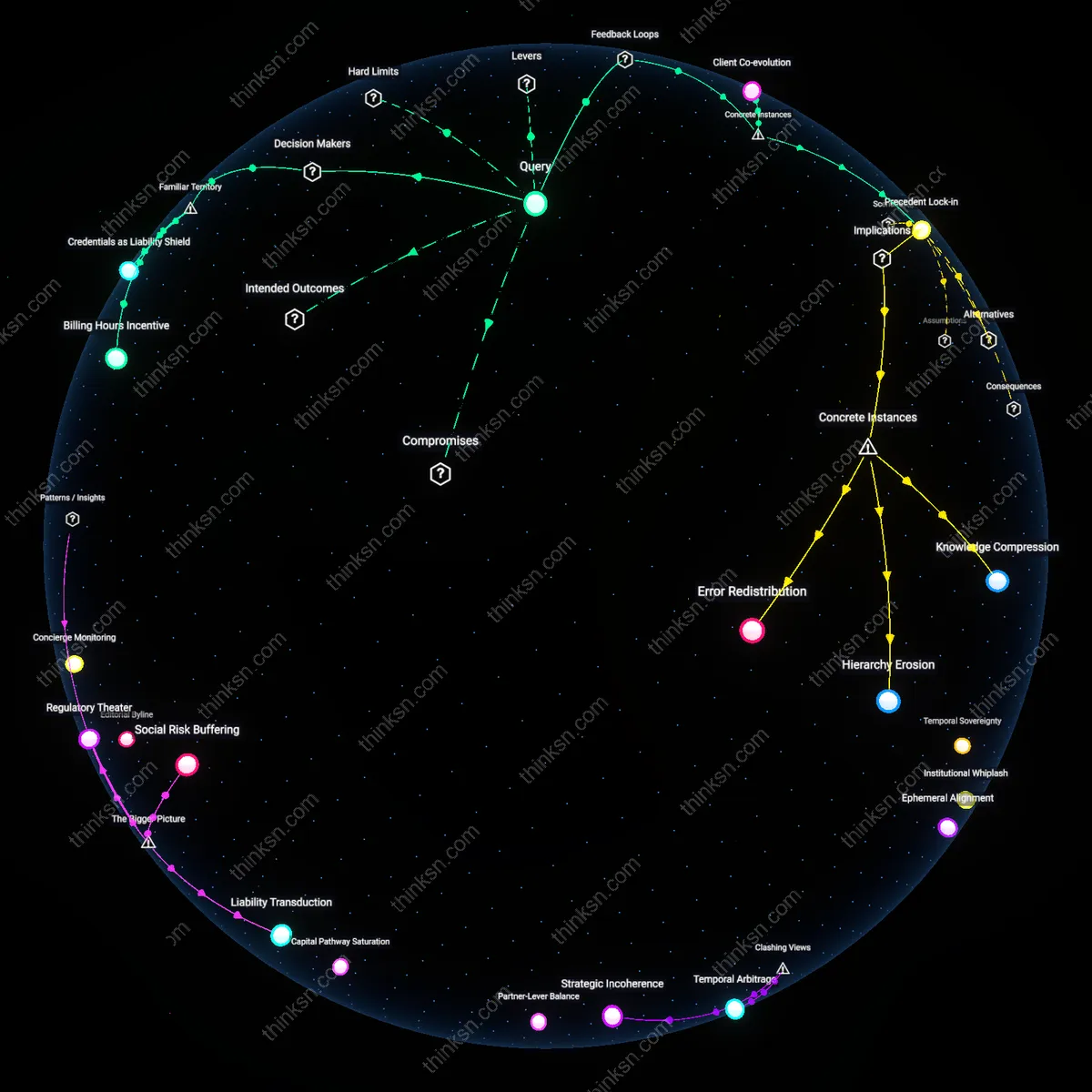
Vendor Governance Capture
Single cloud providers shape the security governance of election systems by setting default configurations, access controls, and incident response protocols that override local election authority policies. Because these configurations are often opaque and change without consultation, state and local election officials unknowingly adopt security postures aligned with commercial incentives rather than democratic integrity requirements. This creates a subtle form of institutional dependency where cloud vendors de facto dictate election cybersecurity standards—an influence rarely acknowledged in procurement or risk assessments, despite determining what counts as ‘secure’ in practice. This dimension is overlooked because oversight focuses on breaches, not the upstream capture of security decision-making by vendor-administered cloud environments.
Geographic Attack Surface Compression
Consolidating election infrastructure on a single cloud provider concentrates geographically dispersed election systems into a small number of physical data centers, unintentionally compressing the national election attack surface into a handful of high-value facilities. This enables attackers to target hardened national election functions through supply chain or physical access exploits against cloud data center operations—such as maintenance personnel or carrier interconnect points—rather than weaker local IT systems. Most risk models assume decentralized systems are more vulnerable, but here centralization creates deeper systemic exposure through underprotected physical and interdependence nodes. This shift from logical to territorial vulnerability is rarely considered in cyber election planning, which treats infrastructure as abstracted from location.
Failover Illusion
The belief that cloud redundancy ensures continuity during cyber attacks ignores that failover mechanisms depend on shared underlying infrastructure, codebases, and identity providers controlled by the same vendor—meaning a compromise in one segment can silently disable backup systems. Election administrators assume resilience is built-in, but failover processes are often invisible, untested under adversarial conditions, and contingent on vendor-side detection that may be delayed or suppressed for reputational reasons. This produces a false sense of redundancy that masks a single point of systemic collapse. This illusion persists because audits focus on uptime metrics, not the vendor-controlled logic that governs recovery, making the dependency on vendor goodwill the real backup system.
Monoculture Attack Surface
Deploy redundant election management systems across different cloud providers using active-active architectures, where identical but isolated environments run simultaneously on AWS, Azure, and Google Cloud under the oversight of state election authorities. This approach mimics distributed computing safeguards used in financial trading systems, where uniform inputs are processed in parallel and divergence triggers immediate audit flags. The widespread public assumption that cybersecurity means stronger firewalls or better passwords obscures the risk of uniformity—when every jurisdiction uses the same underlying cloud stack, a single zero-day exploit can cascade across the entire electoral map like a corn blight across a genetically identical crop.
Critical Service Mirage
Designate core election functions—such as voter verification and ballot tabulation—as offline-conducted processes with cloud systems limited to non-critical, post-hoc data aggregation. This requires reverting to air-gapped machines for vote counting and ID validation, with cloud connectivity restored only after immutable logs are physically transferred via tamper-evident media. Most public debate presumes that cloud migration enhances reliability and modernization, yet this faith overlooks the fundamental mismatch between always-on digital infrastructure and the episodic, high-stakes nature of elections—where the appearance of seamless digital service can mask the fragility of depending on live network availability during targeted disinformation or denial-of-service campaigns.
Temporal Jurisdiction Gap
Dependence on a single cloud provider introduces a temporal jurisdiction gap because the infrastructure governance model—developed in the mid-2010s for commercial agility—assumes rapid iteration cycles incompatible with election integrity requirements, which depend on static, verifiable systems in the 90-day pre-election window; this misalignment, emerging starkly after the 2022 midterms when automatic backend updates altered logging protocols undetected, reveals a deeper shift from fixed electoral timelines to continuous cloud-time, where system configurations drift outside human oversight. The underappreciated reality is that the very stability needed for auditability is undermined by a provider’s normal operations, making compliance with pre-digital election laws a retrospective negotiation rather than a built-in guarantee.