Do Backdoors for Safety Undermine Civil Liberties?
Analysis reveals 5 key thematic connections.
Key Findings
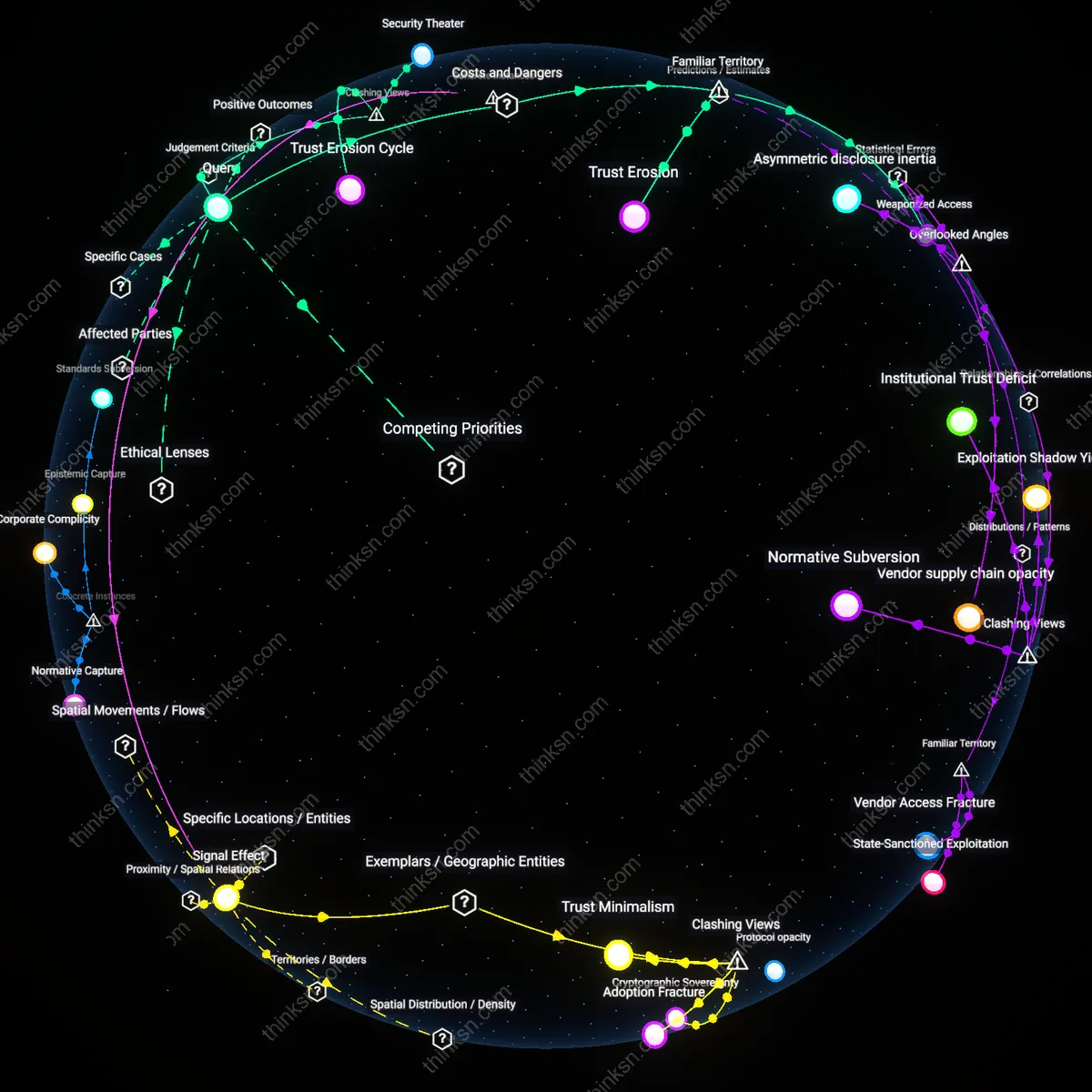
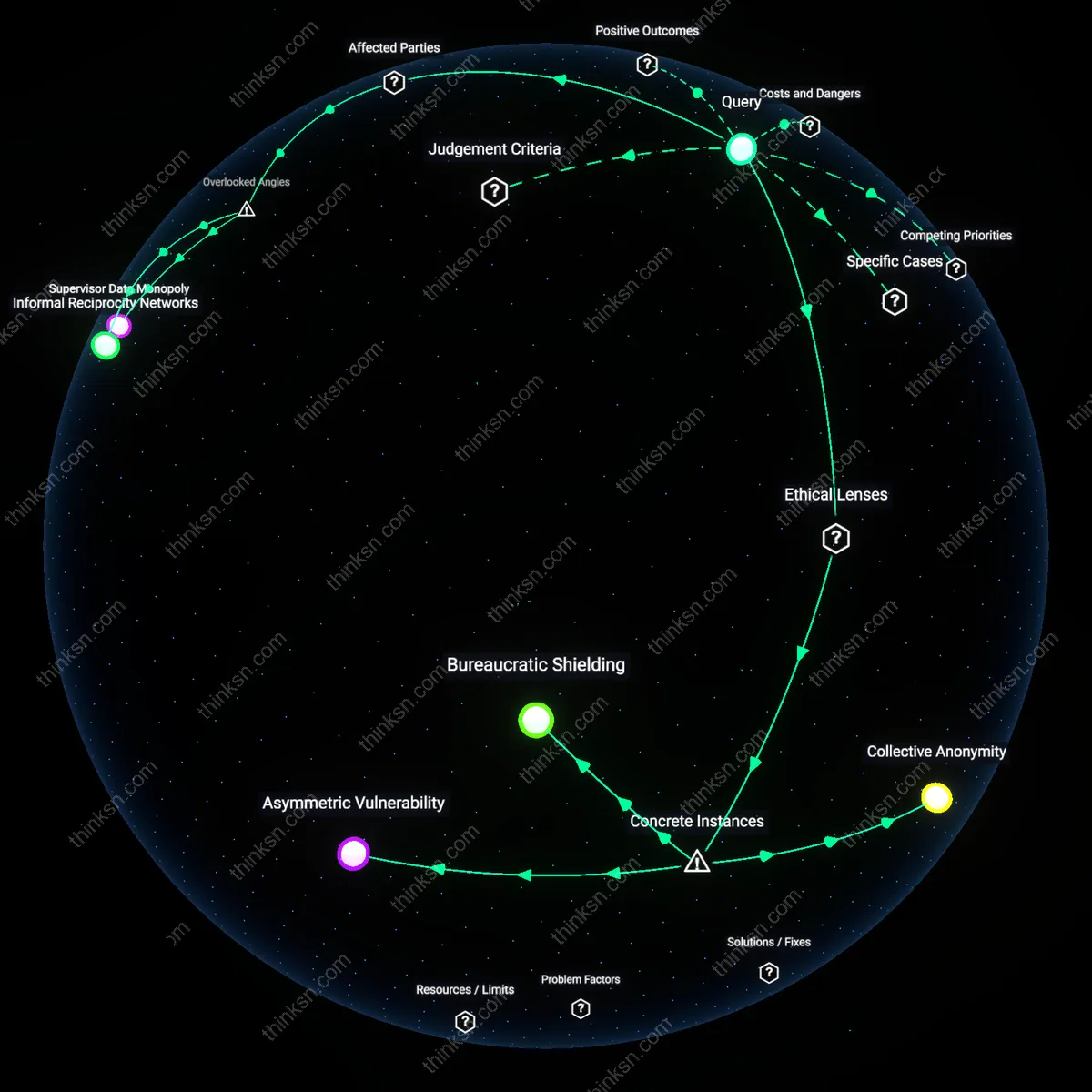
Security Theater
Advocating for mandatory backdoors prioritizes the symbolic performance of public safety over actual security, because state actors like the FBI leverage public fear of terrorism to justify access mandates that do not statistically reduce crime but do expand surveillance infrastructure. The mechanism operates through legislative lobbying and media framing that equate encryption with criminal sanctuary, despite evidence from agencies like NIST showing that backdoored systems are routinely exploited by malicious actors, undermining both privacy and security. This reveals the non-obvious reality that the primary function of backdoor advocacy is not crime prevention but the normalization of state access norms under the guise of protection.
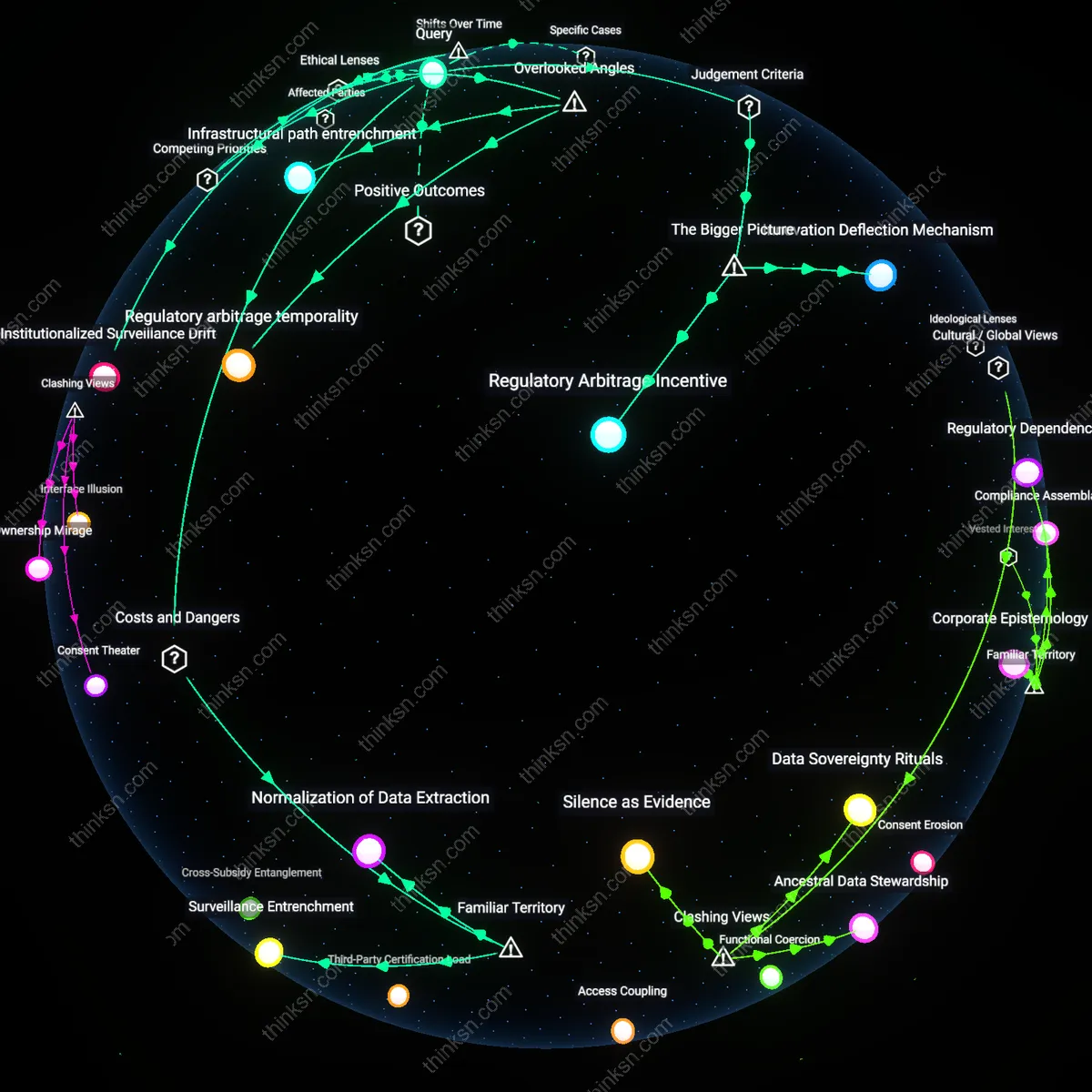
Trust Erosion Cycle
Mandating backdoors inherently weakens the integrity of global communications infrastructure, privileging short-term surveillance gains for states like the United States and UK over the long-term resilience of digital trust ecosystems managed by firms such as Signal or Apple. Because cryptographic systems are only as strong as their weakest implementation, a legal mandate in one jurisdiction enables exploitation by non-democratic regimes through legal precedent or technical leakage, as seen when Pegasus exploited government-justified vulnerabilities. This dynamic exposes how the push for backdoors is less about targeted oversight and more about institutional inertia within intelligence communities resistant to operating in genuinely encrypted environments.
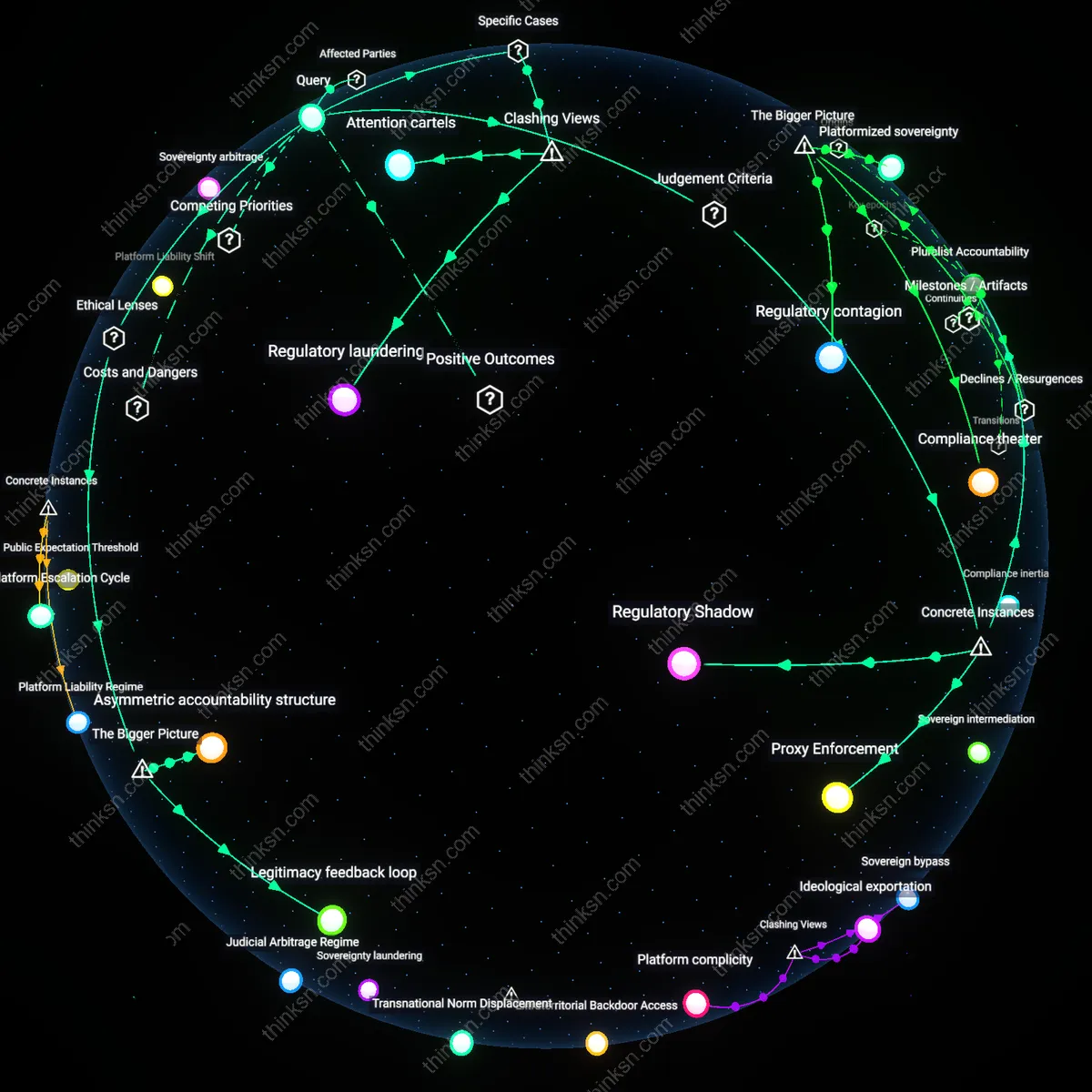
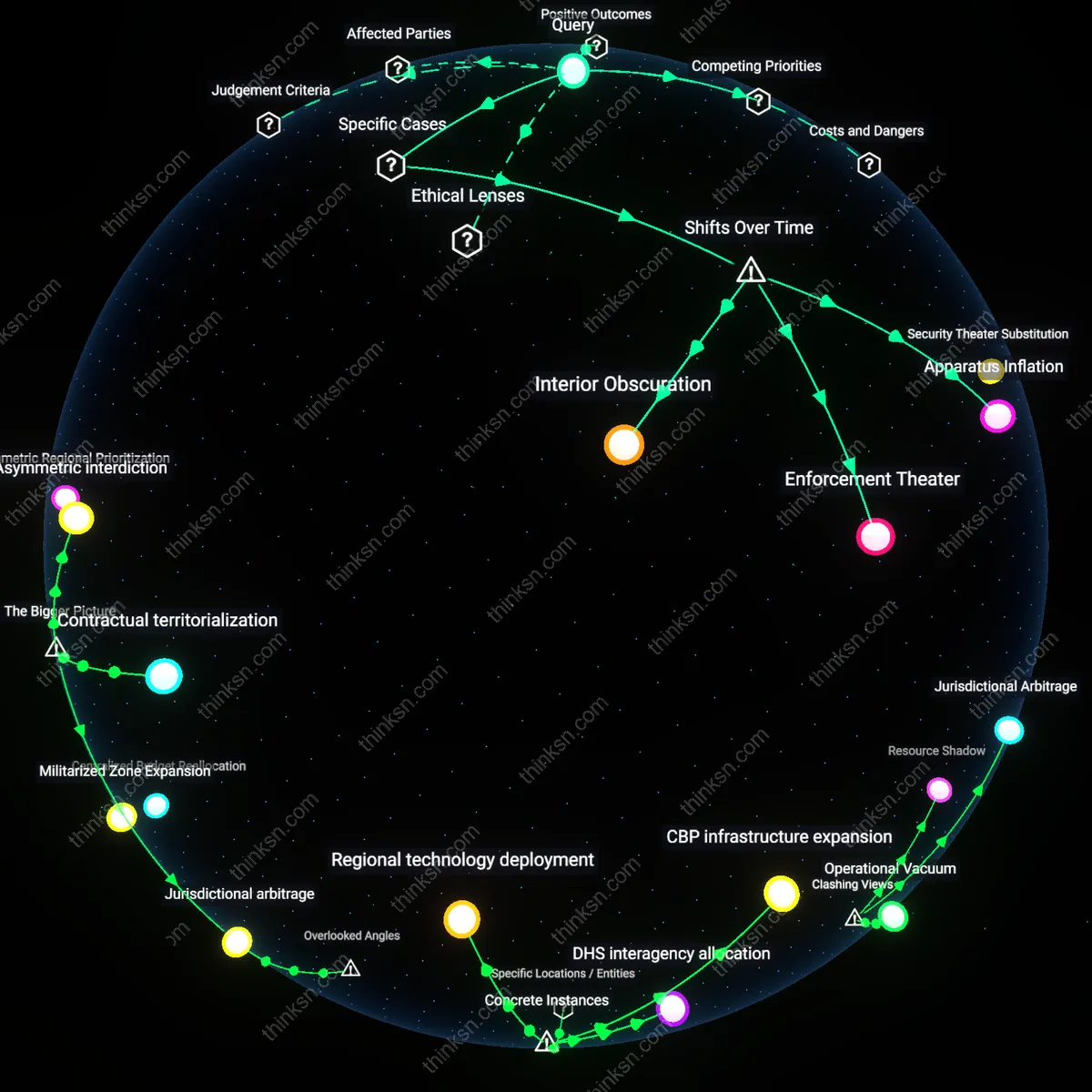
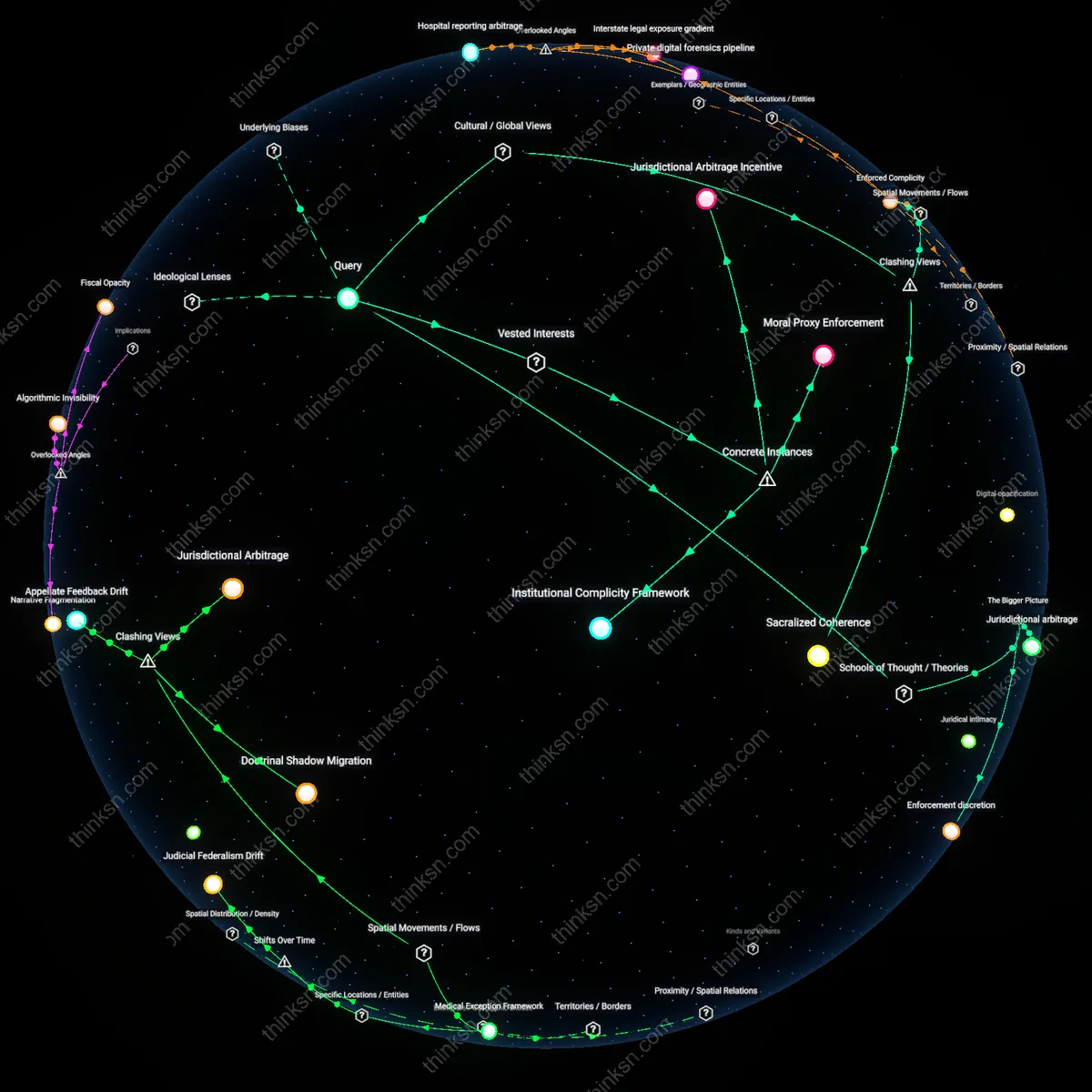
Jurisdictional Arbitrage
State demands for backdoors disproportionately target democratic tech firms bound by rule-of-law constraints, while criminal or authoritarian actors migrate to decentralized or offshore platforms beyond regulatory reach, privileging compliance over efficacy. This asymmetry manifests in legislation like the UK’s Online Safety Act, which pressures companies like Meta to introduce client-side scanning—despite such measures being bypassed easily by actors using non-compliant services hosted in permissive jurisdictions such as Russia or Iran. The overlooked reality is that backdoor mandates function not as security tools but as regulatory capture mechanisms that penalize lawful users and firms while leaving actual threats untouched.
Trust Erosion
Mandating backdoors in encrypted messaging weakens public trust in digital security institutions. When governments compel companies like WhatsApp or Apple to introduce technical vulnerabilities—market leaders whose credibility depends on strong encryption—users perceive these platforms as compromised, regardless of whether surveillance is actually widespread. This effect is amplified by known cases such as the FBI’s 2016 clash with Apple over the San Bernardino iPhone, where even a one-time access demand triggered global concern about precedent, revealing how enforcement actions in democratic states undermine confidence in the very systems meant to protect speech and finance. The underappreciated consequence is not increased crime-fighting efficacy, but a broad decay in faith that any digital interaction remains private, pushing users toward unregulated or offshore platforms beyond legal reach.
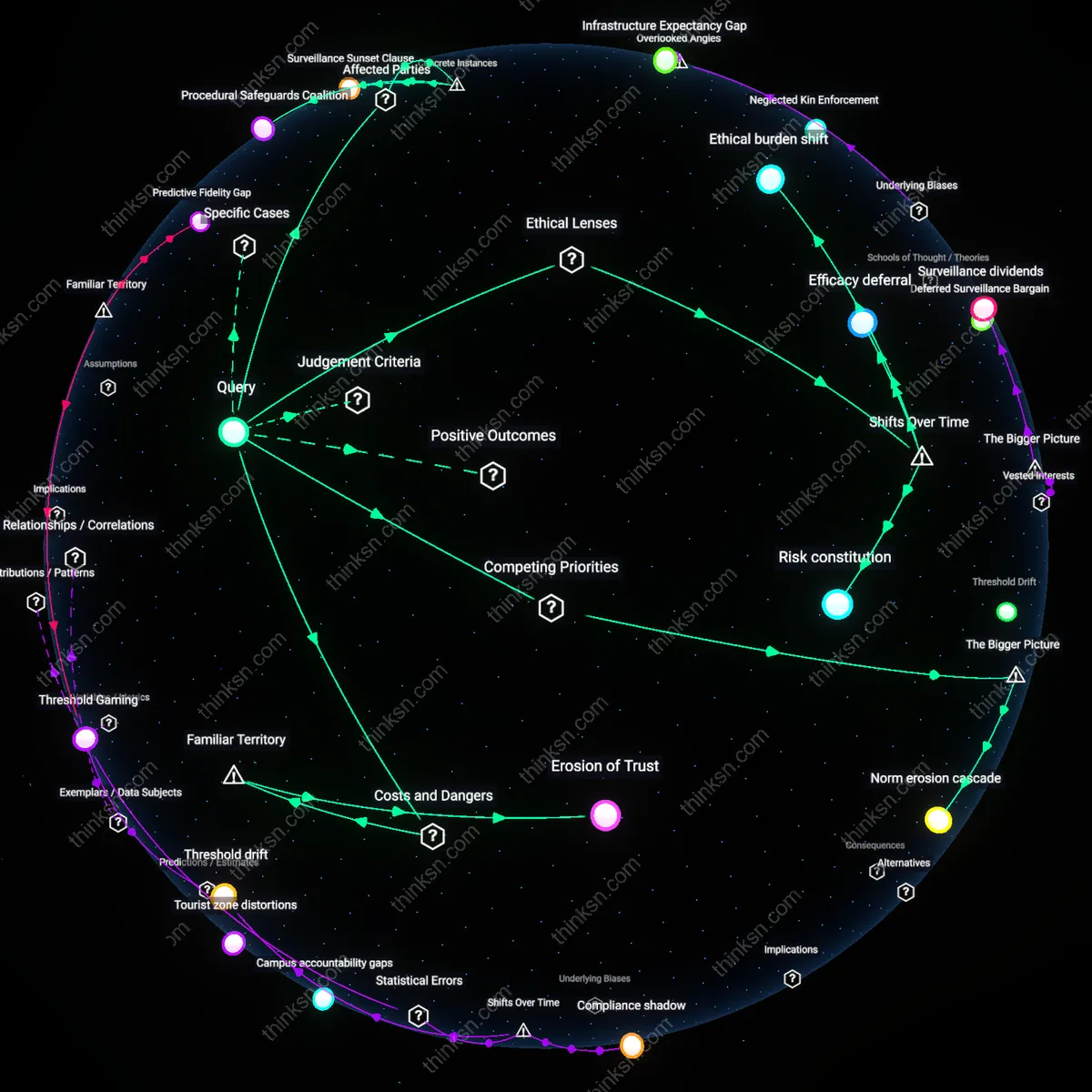
Weaponized Access
Creating state-mandated backdoors inevitably produces exploitable access points that adversaries can repurpose for authoritarian ends. In countries like India or Brazil, where legal orders for message interception have already pressured local tech providers, the existence of a decryption mechanism—even if initially restricted—introduces a blueprint that corrupt officials, cybercriminals, or rival states can coerce or breach, as seen in the Pegasus spyware scandal involving government-purchased zero-day exploits. While public safety arguments focus on preventing terrorism or child exploitation, the systemic danger lies in normalizing a tool that, once built, cannot be contained to noble purposes—turning lawful surveillance capacity into an emergent attack surface, which most users intuitively fear but rarely articulate as an institutional liability.