Digital Identity Benefits vs. State Surveillance Risks?
Analysis reveals 9 key thematic connections.
Key Findings
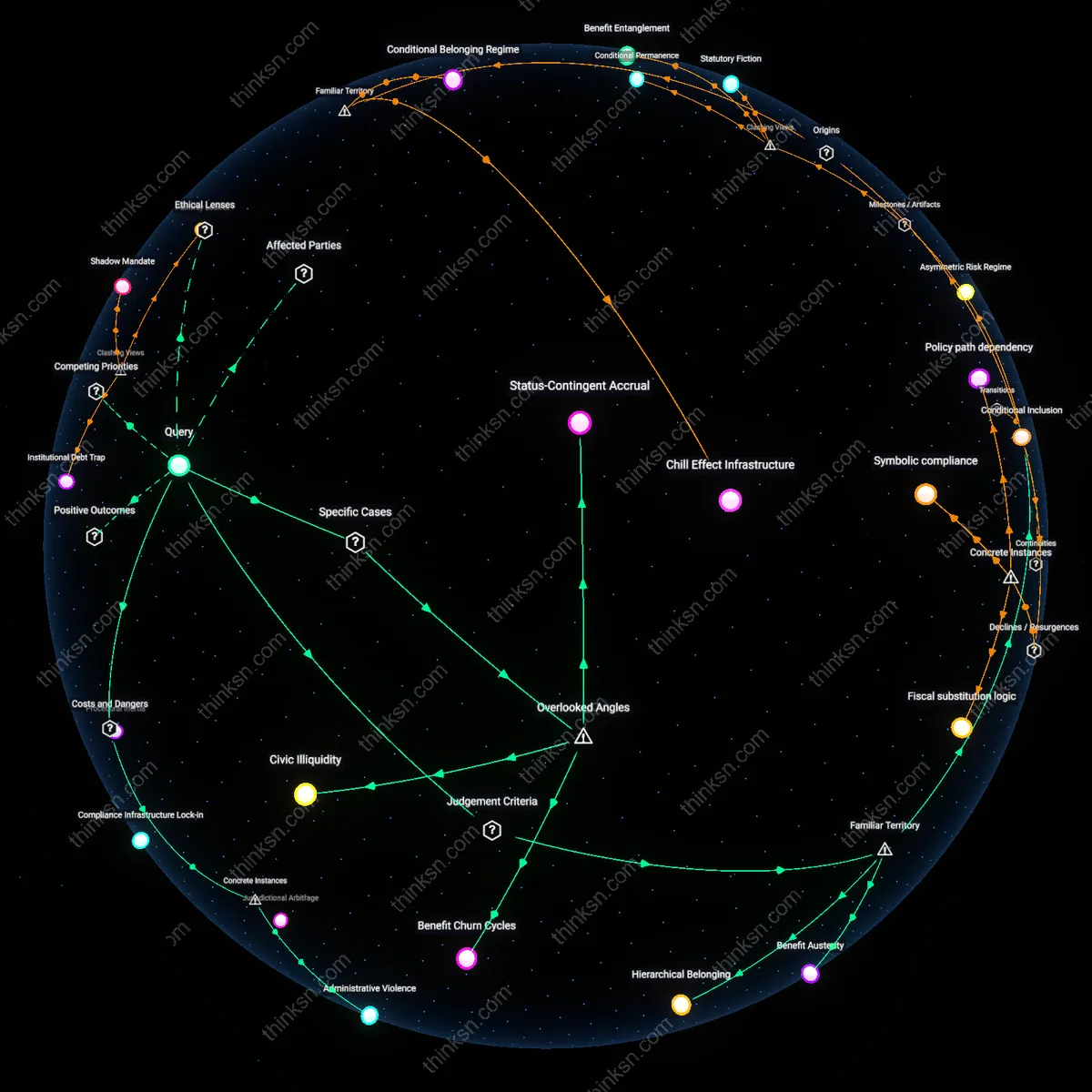
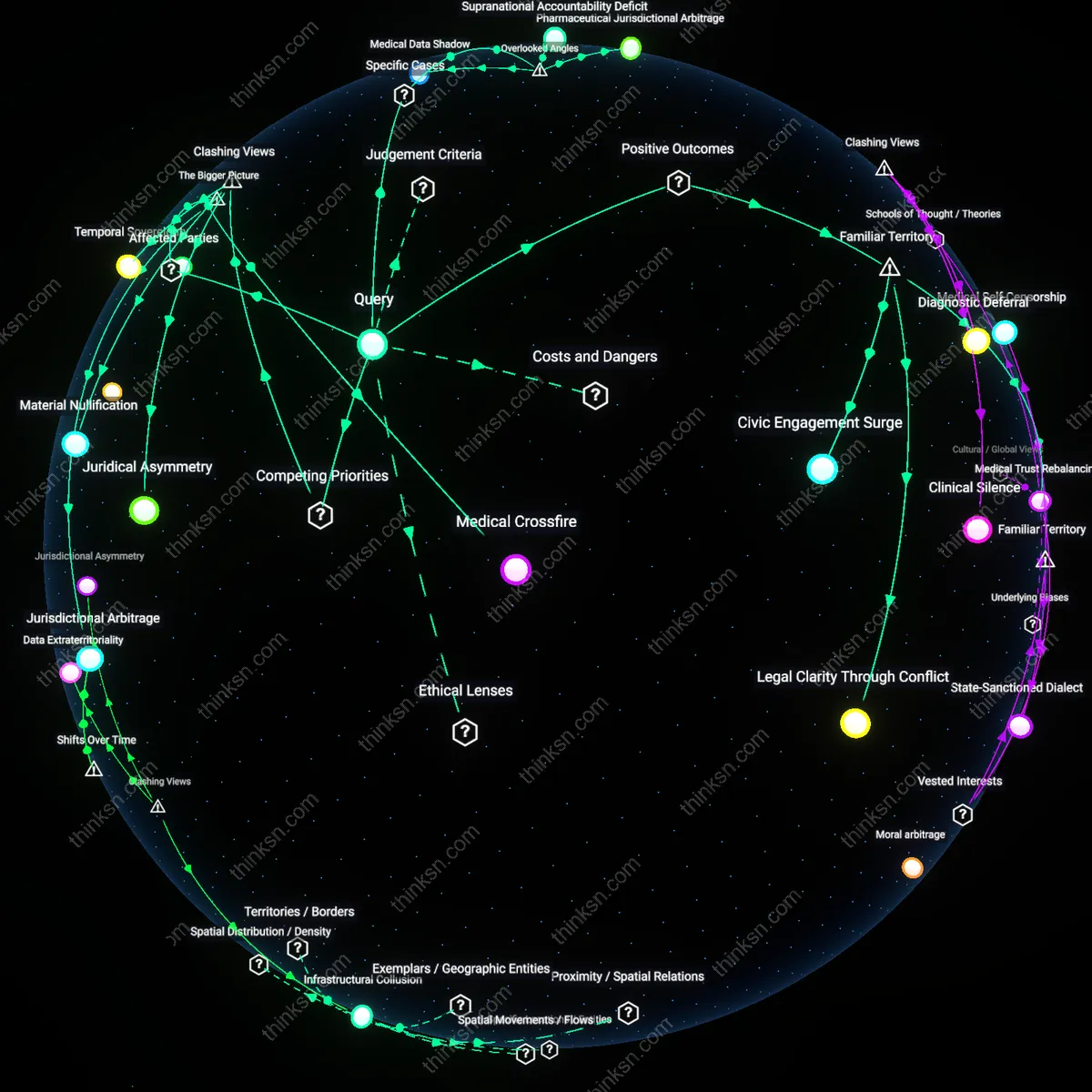
Beneficiary Resistance
Public benefit access is most effectively protected when marginalized recipients organize collective refusal to enroll in state digital identity systems, as seen in rural welfare applicants in India leveraging social mobilization to resist Aadhaar-linked disbursements. This mechanism operates not through legal challenge or technical design but through coordinated non-participation, withdrawing the very data that fuels surveillance expansion. Such resistance is non-obvious because it frames vulnerability not as passivity but as a strategic political stance that disrupts the assumed inevitability of enrollment for survival, revealing that the weakest link in the surveillance-benefits nexus is state dependency on compliance.
Infrastructure Friction
State surveillance overreach is tempered not by privacy laws or oversight bodies, but by the deliberate maintenance of fragmented, analog bureaucratic interfaces within public service delivery systems, such as local pension offices in Brazil that delay digital integration to preserve clientelist discretion. These institutional ‘slow zones’ exploit procedural inefficiencies to create operational friction that limits centralized data aggregation, privileging neighborhood-level gatekeepers over national monitoring. This challenges the dominant narrative that surveillance risk increases with digital maturity, exposing how deliberate technological underdevelopment functions as a covert check on central power.
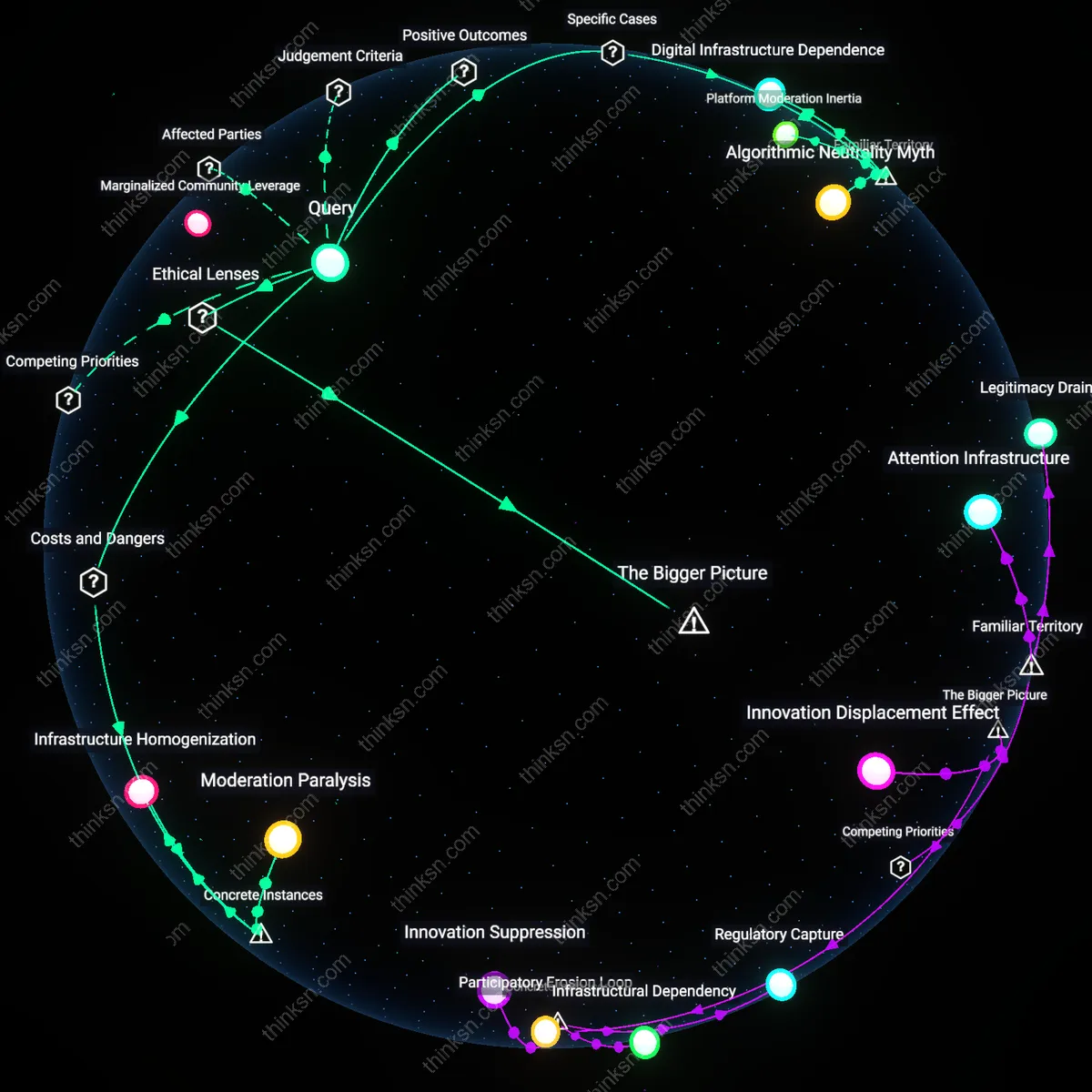
Corporate Containment
The primary check on state surveillance through digital identity lies in corporate actors limiting state data access as a condition for maintaining platform interoperability, exemplified by telecom firms in Kenya withholding biometric integration with the National Integrated Identity Management System (NIIMS) after public backlash. These private providers leverage their control over authentication infrastructure to act as de facto privacy arbiters, framing data protection as a market stability concern rather than a civil right. This upends the conventional state-centric model of surveillance governance by revealing that corporate risk calculus, not citizen advocacy, often becomes the decisive boundary against state overreach.
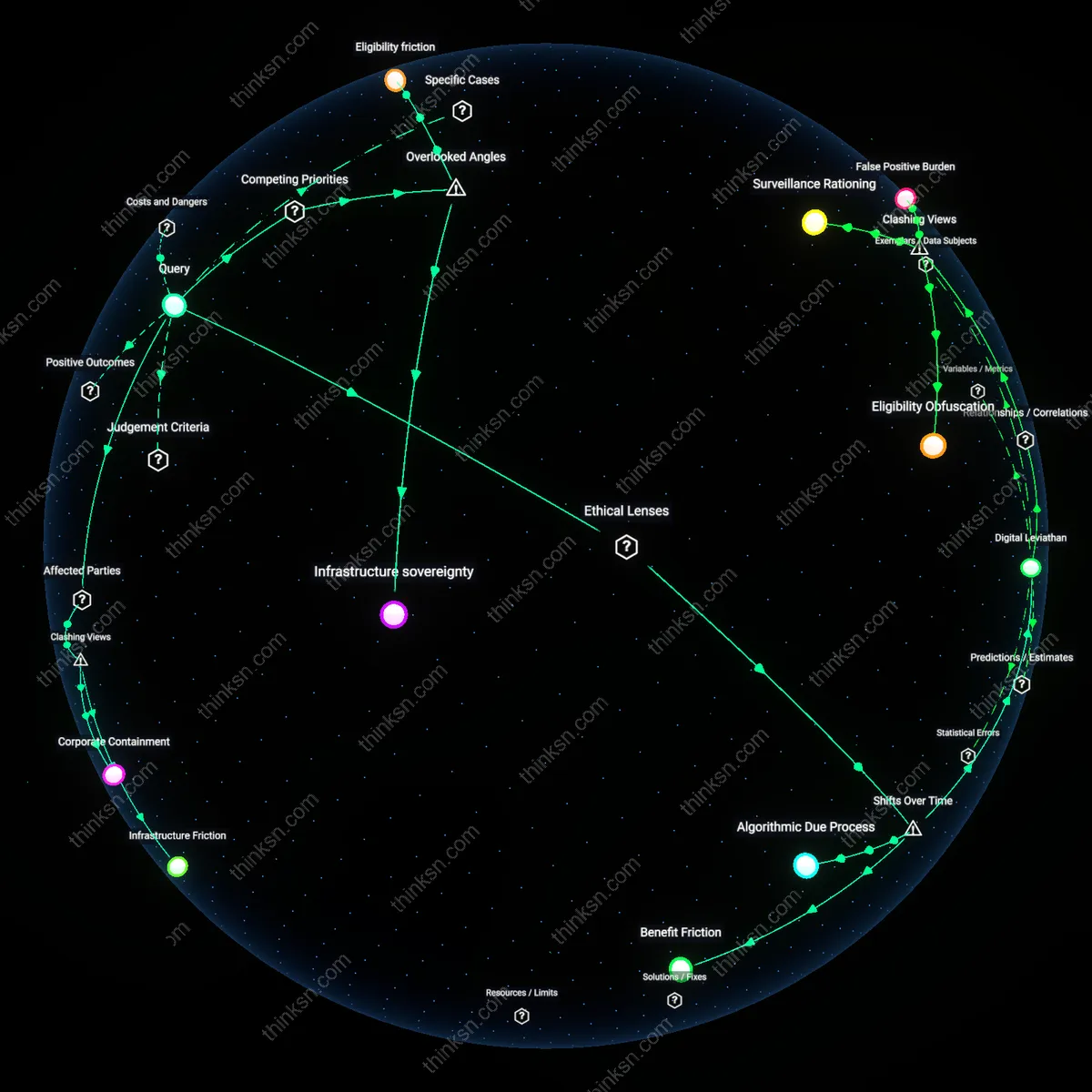
Infrastructure sovereignty
Designing digital identity systems with decentralized data storage controlled by municipal or regional public utilities—not federal agencies—reduces the centralization of surveillance risk while maintaining access to benefits. This shift locates control within semi-autonomous civic entities that are neither fully state-aligned nor privatized, creating a buffer against federal overreach while ensuring service delivery through localized accountability structures. Most discussions assume digital identity must be nationally centralized to be functional, overlooking how federated civic infrastructure can act as a political intermediary that negotiates between individual privacy and state utility.
Behavioral exhaust asymmetry
The risk of surveillance is not proportional to data collection but to the reusability of behavioral byproducts—such as timing, frequency, and sequence of benefit claims—for predictive governance. When digital identity systems are optimized for transactional efficiency, they generate granular behavioral exhaust that can be repurposed for social control, even if content is encrypted. Standard privacy safeguards ignore how metadata patterns become tools for classification and preemption, making the design of consumption workflows a covert surveillance vector masked as administrative logic.
Eligibility friction
Introducing calibrated inefficiencies—such as periodic manual verification or opt-in renewal mechanisms—into digital identity systems can paradoxically protect against surveillance by reducing the smoothness of data aggregation and automated profiling. Surveillance thrives on frictionless data flow; strategic inefficiencies disrupt the continuity required for persistent tracking while preserving access for genuinely eligible users who can navigate minimal procedural barriers. This reframes bureaucratic inconvenience not as a flaw but as a functional counterweight to total visibility, an insight absent from efficiency-driven digital governance models.
Digital Leviathan
State-enforced digital identity systems must be constrained by constitutional privacy doctrines because expansive surveillance capabilities, justified post-9/11 under U.S. national security imperatives, institutionalized risk-managed citizenship that now normalizes real-time consumption monitoring under the guise of service efficiency. The transition from paper-based entitlement verification in the 1990s to algorithmically mediated benefit access after 2010 shifted eligibility from discrete bureaucratic acts to continuous data shadows, embedding surveillance in everyday life — a transformation underappreciated because it reconfigures state-citizen trust not as a breach to be regulated, but as a default architecture.
Algorithmic Due Process
Public digital identity systems must incorporate adjudicative transparency to prevent exclusionary automation, a demand that emerged forcefully after welfare digitization in India post-2016 revealed that biometric authentication on Aadhaar systematically denied rations to marginalized populations during appeals. The shift from analog welfare discretion administered by local officials to centralized algorithmic validation transformed procedural justice from a rights-based framework underpost-colonial social contracts into a technical flaw to be debugged — a change whose ethical consequence is the quiet erasure of accountability mechanisms once tethered to human judgment.
Benefit Friction
Deliberate inefficiencies in digital identity verification must be preserved to protect political anonymity in consumption, a principle that gained urgency after Estonia’s seamless e-residency model post-2000 enabled full state visibility into social spending, eroding spaces where citizens could opt out without losing access. Unlike pre-digital systems where bureaucratic slowness inadvertently shielded behaviors, the erasure of waiting periods and paperwork since the 2010s redefined convenience as exposure — revealing that the historical function of administrative friction was not dysfunction, but a covert safeguard against total legibility.