Biometric Welfare: Preventing Fraud or Excluding Vulnerables?
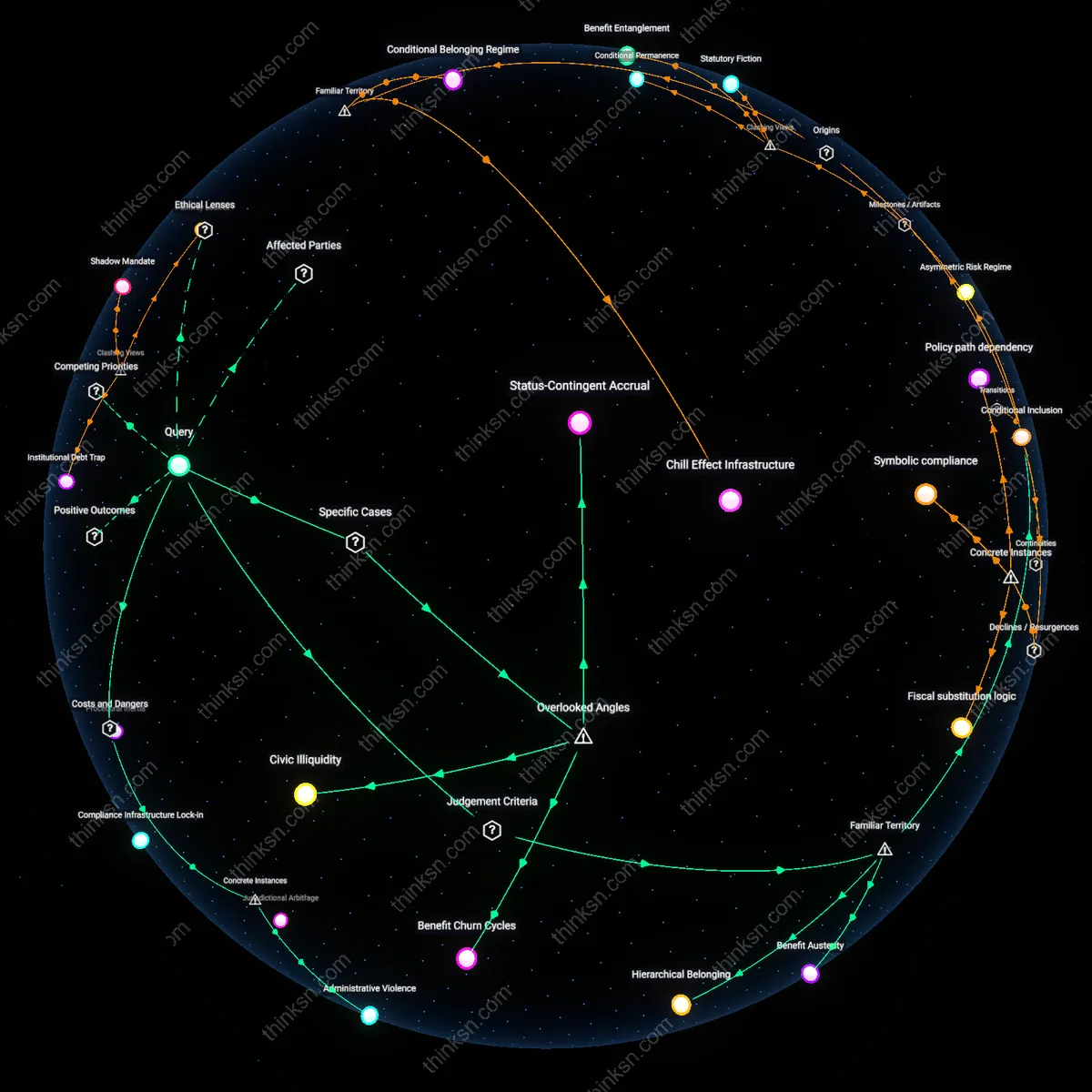
Analysis reveals 3 key thematic connections.
Key Findings
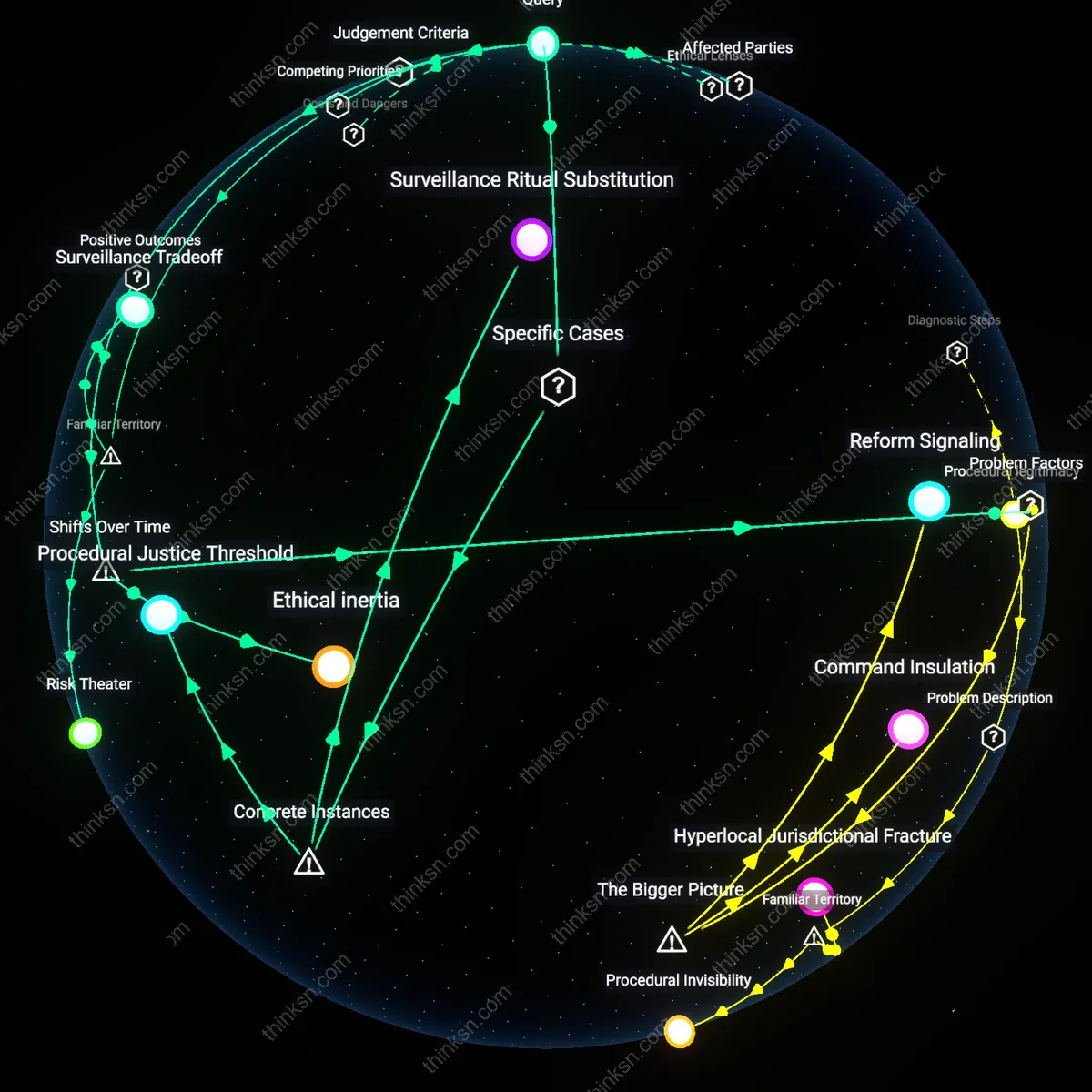
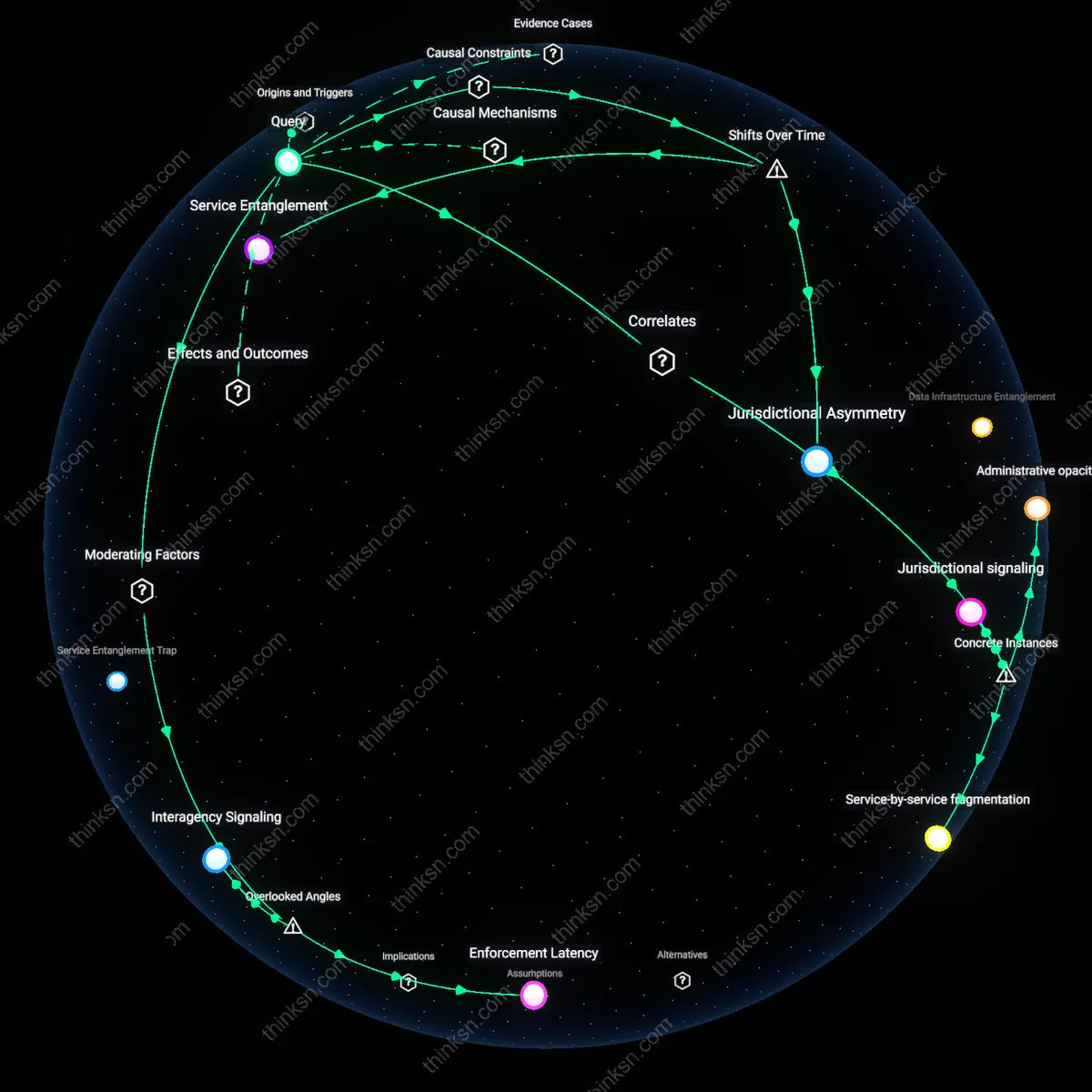
Frictionless Exclusion
Biometric verification optimizes welfare administration not for citizen access but for state scalability, making exclusion faster, quieter, and less contestable. In South African SASSA grant disbursements, automated biometric checks allow mass deactivation of beneficiaries without due process, where the absence of a fingerprint match becomes sufficient cause for termination. The system treats exclusion as a byproduct rather than a violation, embedding it within seamless backend operations—what appears as efficiency is, in fact, the systemic erasure of appeal mechanisms. This reframes the tension not as a trade-off between fraud and access, but as the deliberate substitution of procedural justice with administrative speed, where the greatest harm is not error but the disappearance of redress.
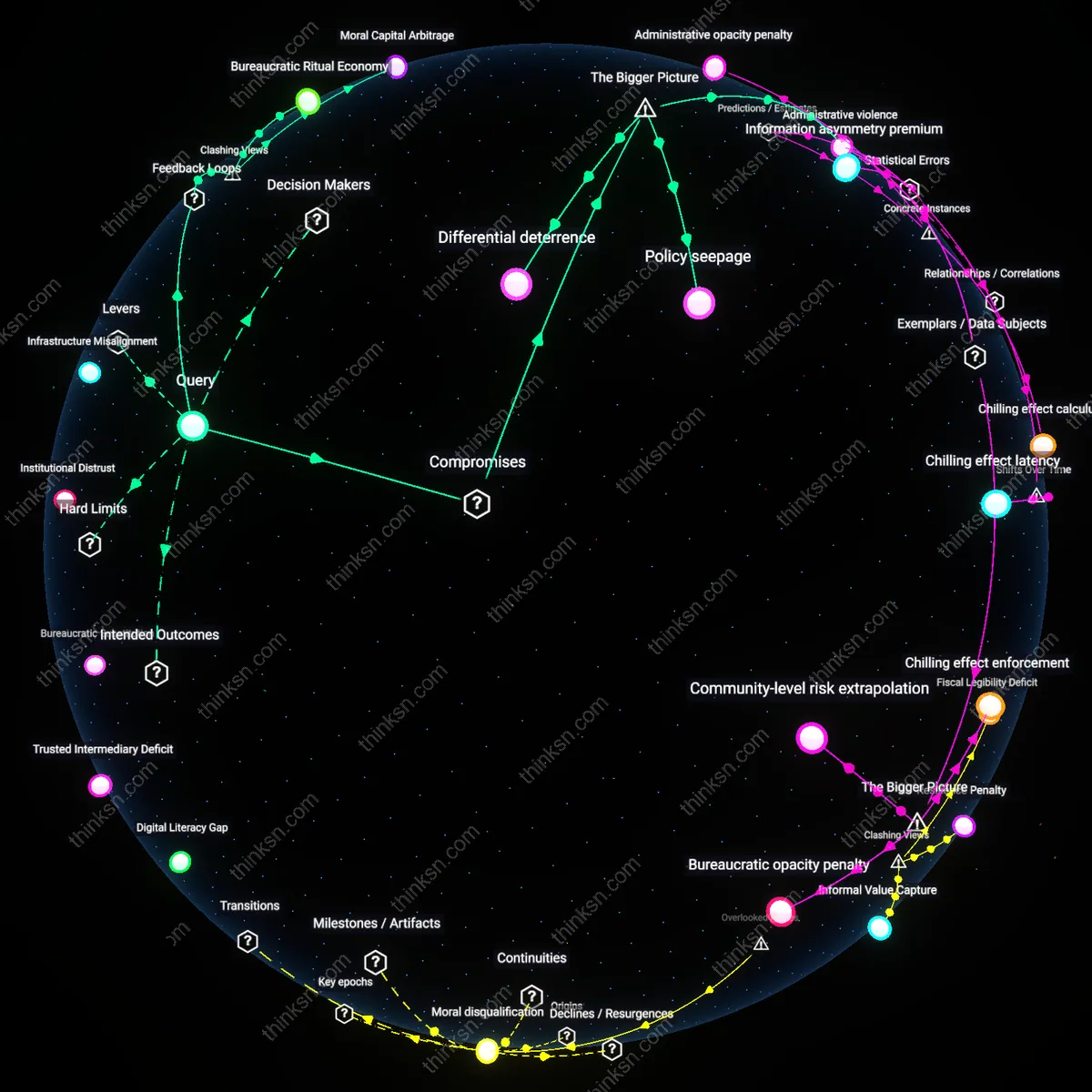
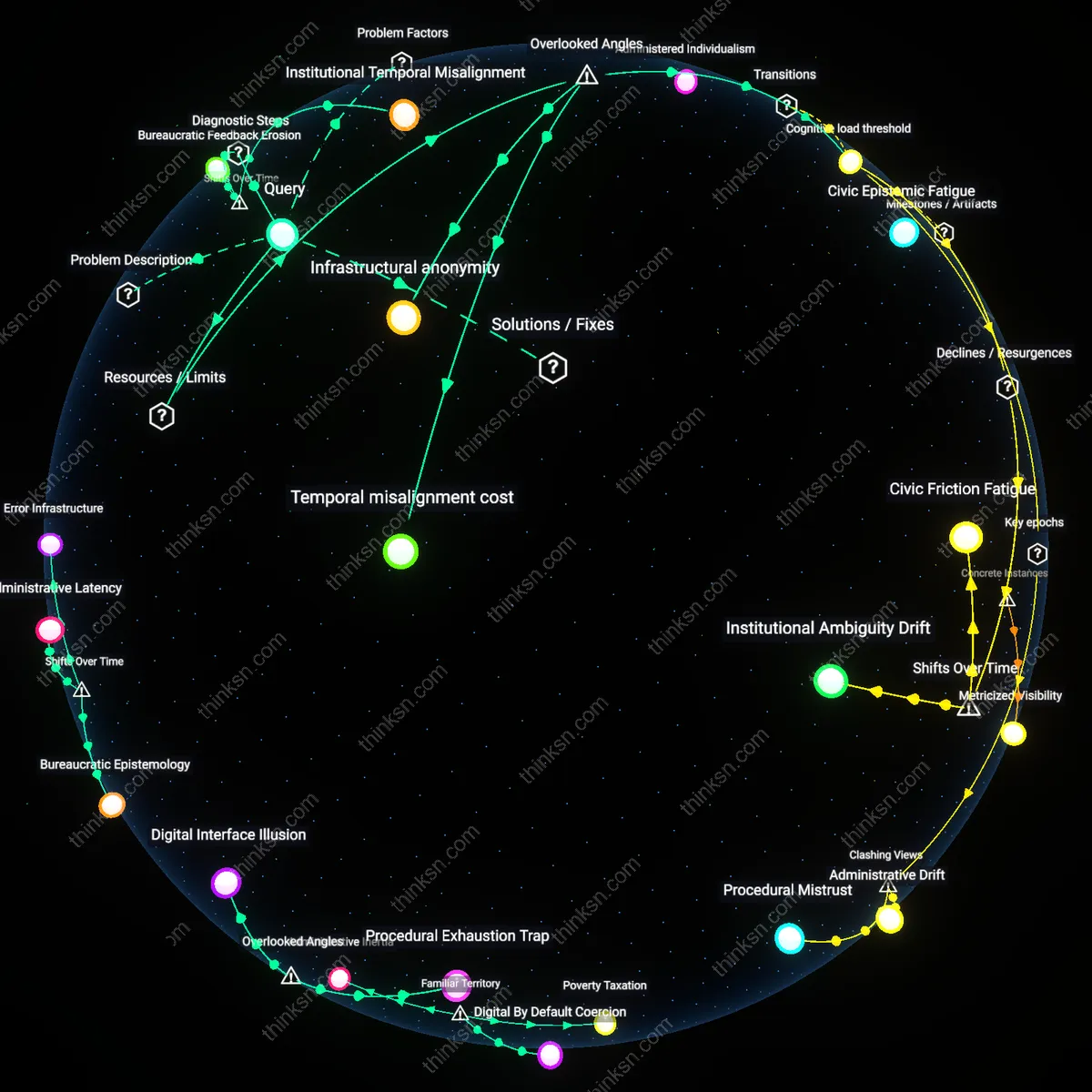
Administrative Legibility Incentives
Biometric verification increases the state’s ability to classify and track welfare recipients as governable subjects, which strengthens institutional incentives to prioritize data consistency over individual access—particularly in decentralized systems like India’s Aadhaar-linked PDS, where local officials are evaluated on audit-ready records. This shifts bureaucratic effort toward maintaining system legibility, often at the cost of enrolling edge cases, such as elderly rural women without stable documentation; the non-obvious mechanism here is not fraud reduction per se, but the redirection of frontline worker attention toward minimizing data irregularities, which makes exclusion an administratively rational outcome rather than a mere oversight.
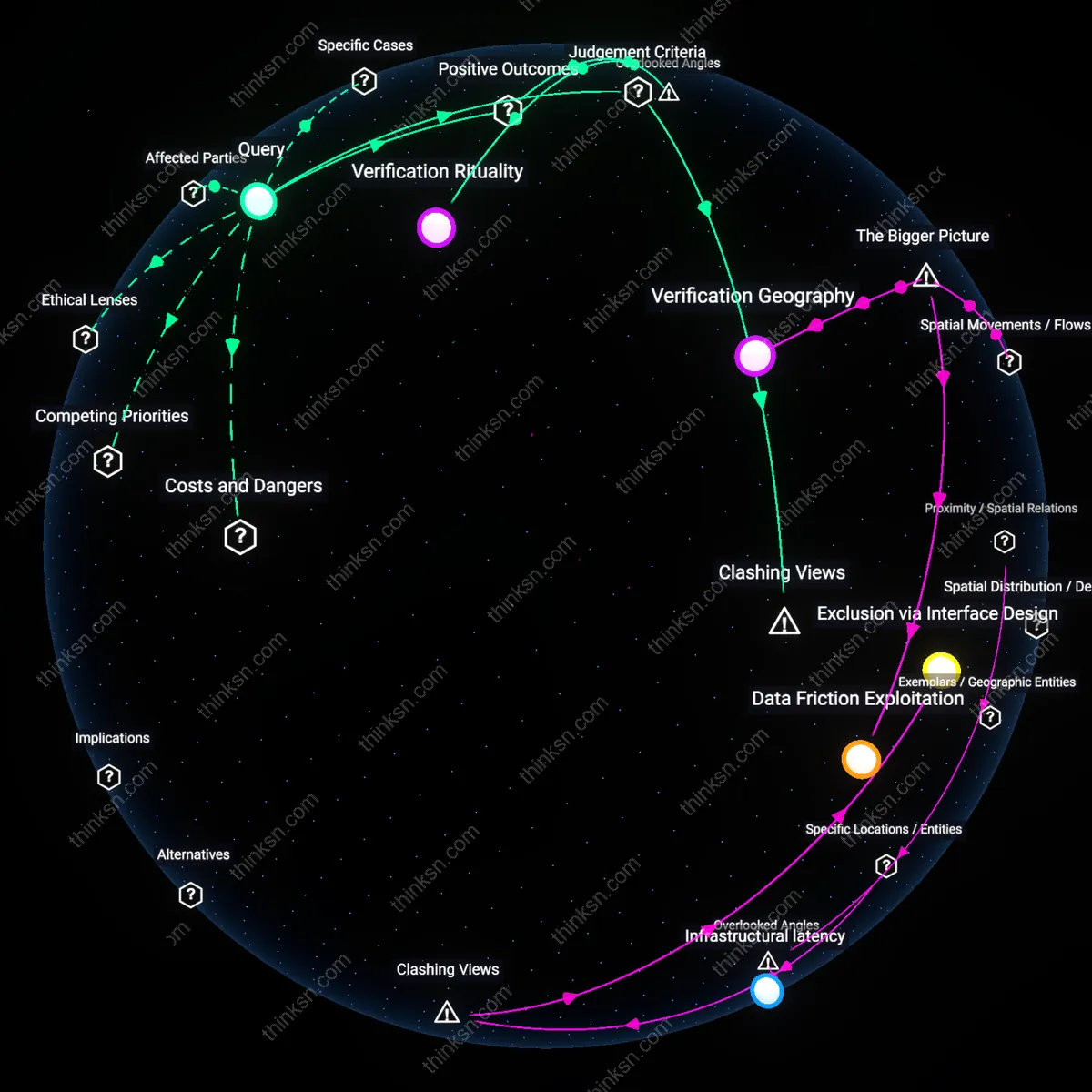
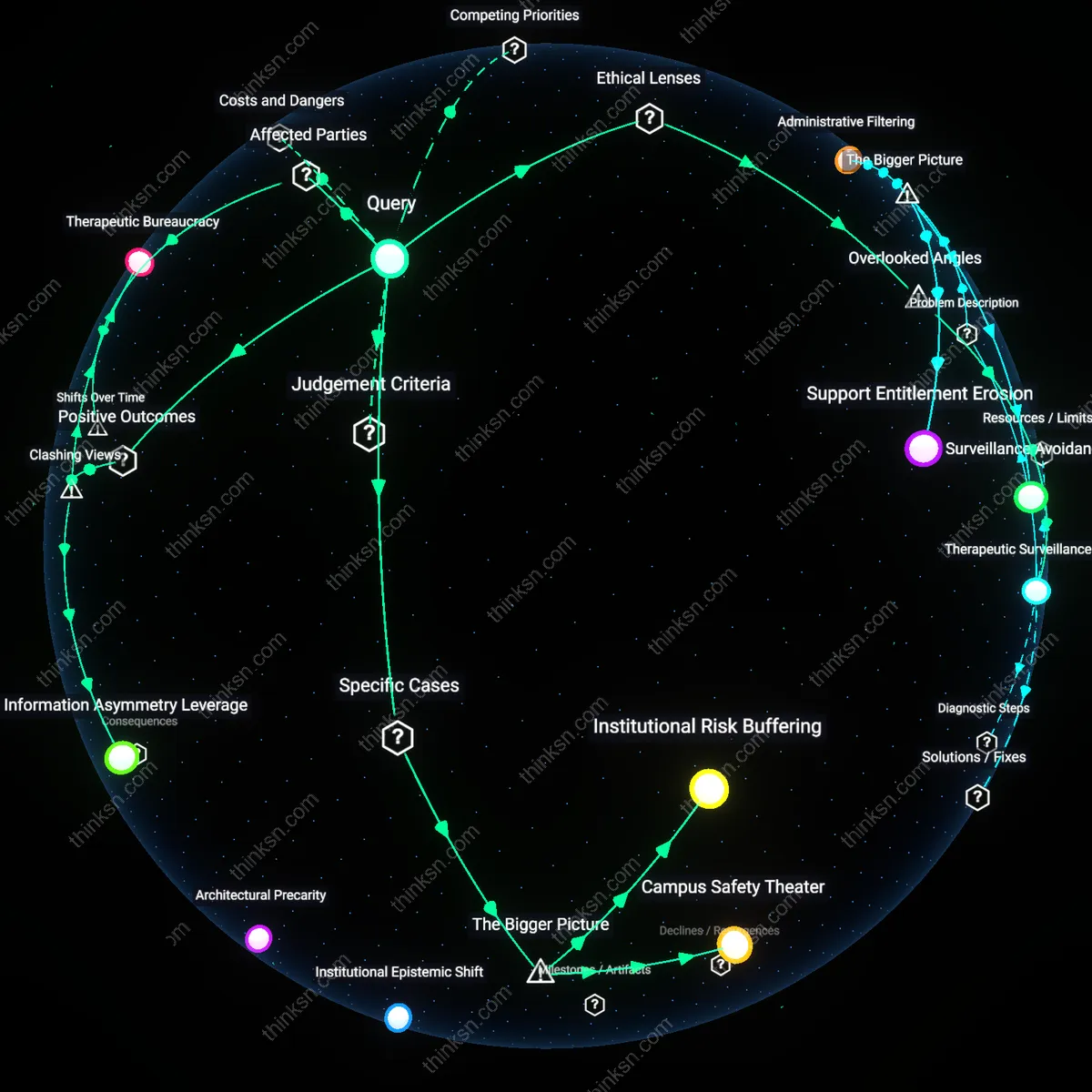
Verification Rituality
Biometric verification becomes a ritual of compliance that signals state authority and beneficiary subjection, even when actual fraud rates are low—as seen in Kenya’s Huduma Namba integration with cash transfers—where the repeated act of scanning fingerprints performs governance more than it prevents abuse. The ritual reassures political stakeholders of control and transparency, diverting scrutiny from deeper structural inefficiencies like fund leakage or eligibility design flaws. What is overlooked is that the symbolic function of verification often outweighs its technical utility, transforming enrollment into a performative act of submission that reinforces hierarchical power relations under the guise of neutrality.