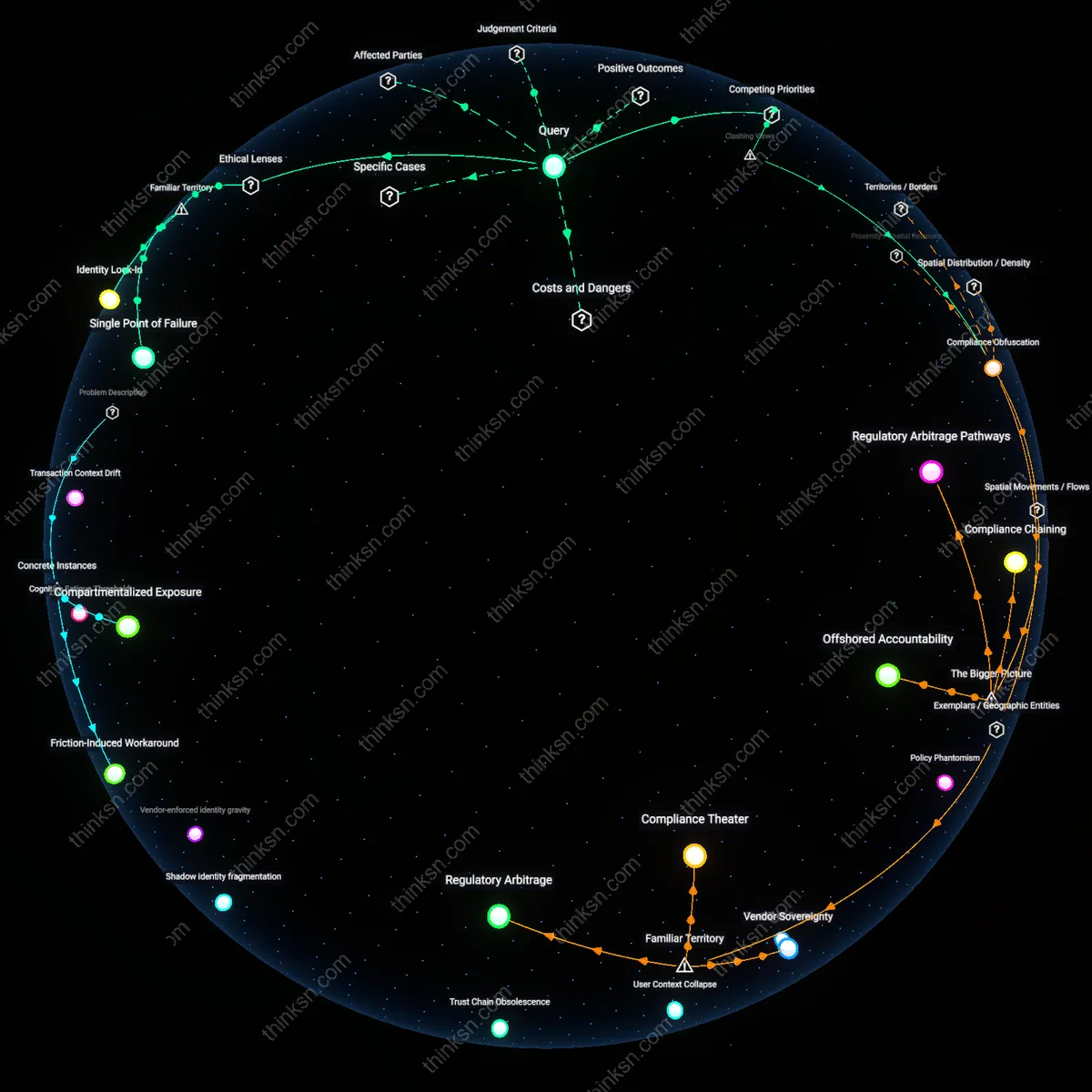
Trust Chain Obsolescence
When an enterprise migrates identity providers after prolonged dependence on one, the underlying trust architecture—once loosely coupled and modular—has already evolved into a monolithic dependency, as seen in healthcare systems transitioning from legacy LDAP to cloud-native SSO frameworks. Federated credentials, API gateways, and conditional access rules become expression-based relics tied to deprecated claims schemas, breaking critical services when mappings fail silently. Evidence indicates that in sectors like financial services, where session continuity is regulated, the drift between old and new identity assertions produces compliance blind spots not during cutover but months later during anomaly reviews. The overlooked shift is that trust itself becomes outdated—not because the original provider failed, but because the ecosystem built on its semantic assumptions no longer interoperates with future-state architectures.
Integration debt
A company locked into a cloud identity provider through years of integration would face substantial operational paralysis during a switch due to deeply embedded dependencies across applications, infrastructure, and access controls. When the City of Los Angeles migrated from Google Workspace back to Microsoft Exchange after six years, it encountered cascading failures in authentication workflows across departments because legacy integrations assumed Google’s identity schema, revealing how identity has become a silent coordination layer beyond mere login. This non-obvious entanglement—where identity becomes a hidden protocol binding systems together—exposes integration debt, a deferred cost of initial cloud adoption that concretizes over time through ambient system dependencies.
Vendor-enforced identity gravity
A company attempting to exit a dominant identity provider after long-term integration will encounter active resistance in the form of proprietary feature lock-in and asymmetric compatibility, as seen when Siemens rebalanced its digital factory stack away from SAP’s identity ecosystem in 2015. Despite having the resources to migrate, Siemens found that SAP’s role-based access controls were inseparable from workflow logic in production planning modules, and third-party audit tools depended on SAP’s logging formats, illustrating how the provider warps surrounding architecture toward its own logic. This reveals vendor-enforced identity gravity, where the identity provider becomes a central mass that distorts adjacent systems to align with its proprietary orbit, making escape trajectories exponentially costlier over time.
Shadow identity fragmentation
When a company initiates a switch from a long-standing identity provider, residual authentication patterns persist in decentralized teams, producing a fractured post-migration identity landscape, as occurred during the Australian Taxation Office’s (ATO) 2018 transition from an on-premise Active Directory to Okta. Even after official cutover, evidence indicates that localized applications—in particular in legacy collections units—continued to reference old directory groups, creating parallel access pathways and inconsistent authorization outcomes. This overlooked consequence—where identity does not transfer cleanly but instead splinters—demonstrates shadow identity fragmentation, a systemic leakage of identity coherence during transitions due to decentralized operational memory and tooling inertia.
Vendor Lock-in Debt
Switching identity providers after years of deep cloud integration would force a company to confront embedded technical dependencies that were never designed for portability. Legacy authentication protocols, user directory schemas, and access control policies are hardwired into applications across AWS, Azure, or G Suite ecosystems, meaning migration demands not just new infrastructure but the reengineering of dozens of interconnected services. The non-obvious reality, often overlooked in discussions of cloud flexibility, is that identity has become a de facto operating system for enterprise software—so tightly interwoven with data access and compliance controls that replacing it resembles transplanting a nervous system. This hidden accumulation of compatibility work, accrued silently over years, constitutes a form of technical debt that resists quick fixes and scales with organizational complexity.
Trust Chain Fracture
Replacing a long-standing identity provider disrupts the implicit trust architecture that governs user access, service-to-service communication, and federated partnerships across cloud platforms. Enterprises such as those using Okta or Microsoft Entra ID have typically extended trust to downstream systems like Salesforce, AWS IAM, or Workday by delegating authentication through SAML or OIDC, creating a chain of verified identities that cannot be severed without cascading revalidation. The underappreciated consequence is that trust is not just a configuration—it is a negotiated state across teams, vendors, and audit regimes—and altering it risks invalidating compliance certifications like SOC 2 or HIPAA, not because of technical failure but because of broken continuity in identity provenance. This rupture is rarely visible until roles mysteriously lose access or automated workflows fail during off-hours.
User Context Collapse
A company that changes identity providers after years of integration will experience a breakdown in user context integrity across its digital workspace, where personalized settings, role-based permissions, and audit trails become misaligned or lost. Employees who relied on single sign-on to navigate between corporate email, cloud drives, and collaboration tools like Slack or Teams will face repeated re-authentication, mismatched profile data, or access to deprecated groups, leading to eroded productivity and spikes in helpdesk volume. What is commonly overlooked in this transition is that identity providers don’t just authenticate—they also carry behavioral metadata that systems have learned to expect; replacing the provider without reconstructing this context collapses the continuity users implicitly depend on. The resulting friction reveals how much organizational memory resides not in documents but in the ambient patterns of access and usage that the old provider governed.
Credential Entropy
A company migrating from one identity provider after years of cloud integration inadvertently exposes dormant credential chains that persist across decommissioned systems, enabling lateral traversal by threat actors who exploit outdated federation agreements still honored by partner services. These residual access paths, often undocumented and scattered across legacy SaaS audit logs, become attack vectors because identity cleanup rarely parallels provider transitions, and federated trust relationships decay slower than technical deprecation schedules—meaning former employee tokens or orphaned service accounts tied to the old provider may still carry implicit authority in third-party systems that never fully revoked trust. This oversight transforms identity migration into a covert privilege escalation event, which standard risk assessments overlook because they focus on active user endpoints rather than the latent topology of expired but valid credentials.
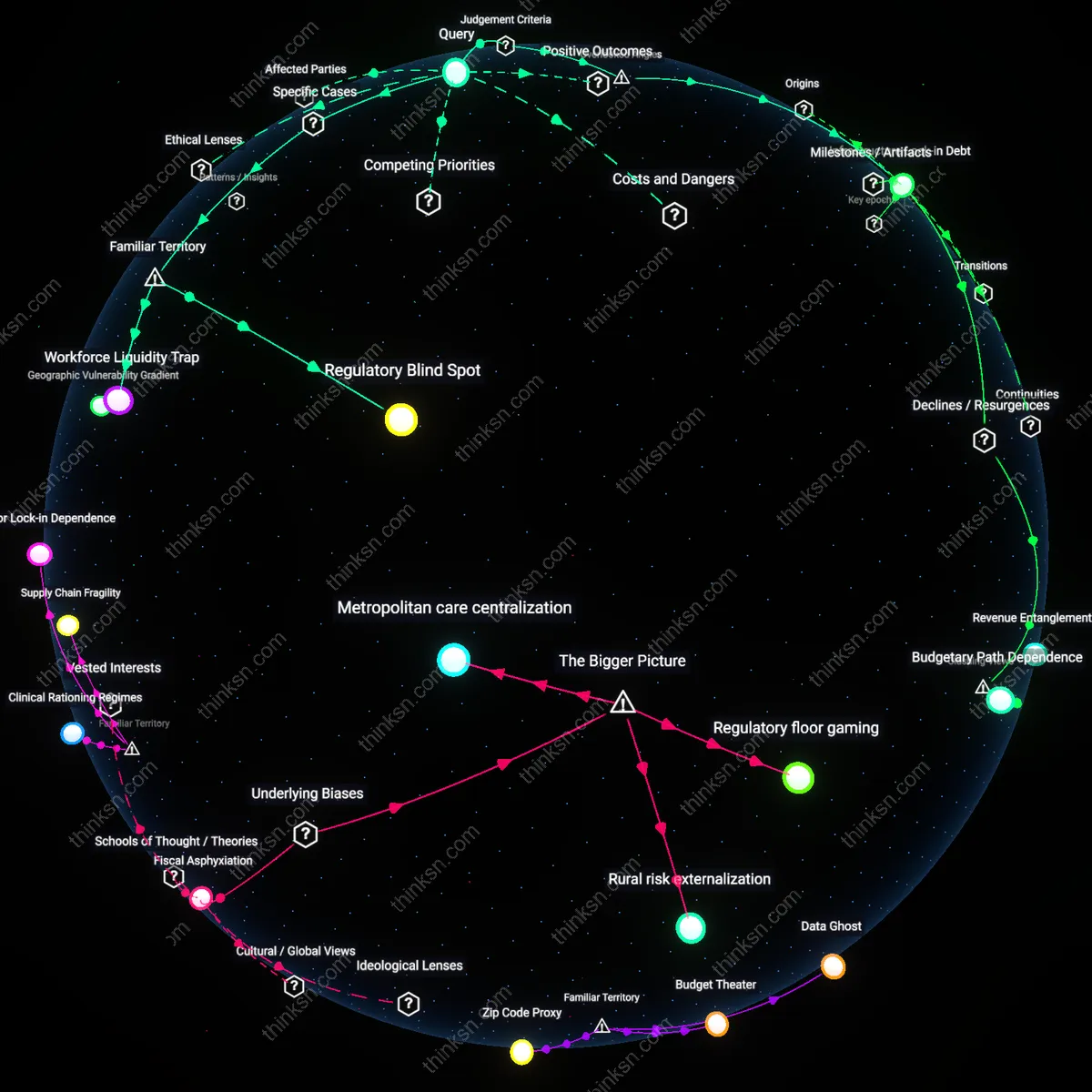
Policy Phantomism
When a company switches identity providers after long-term integration, embedded compliance controls in regulated subsidiaries or regional branches continue to enforce policies predicated on the old provider’s attribute schema, creating undetected gaps in access certification cycles. Because legacy authorization decisions are baked into automated attestations—such as those required under GDPR or SOX—migration disrupts the semantic mapping of roles to permissions, especially when the new provider uses different claim structures or assertion formats, leading to false attestations of compliance. This generates regulatory blind spots not because policies are violated overtly, but because the meaning of compliance itself drifts silently when identity attributes no longer align with the definitions assumed in internal audit logic, a dependency rarely surfaced in migration planning.
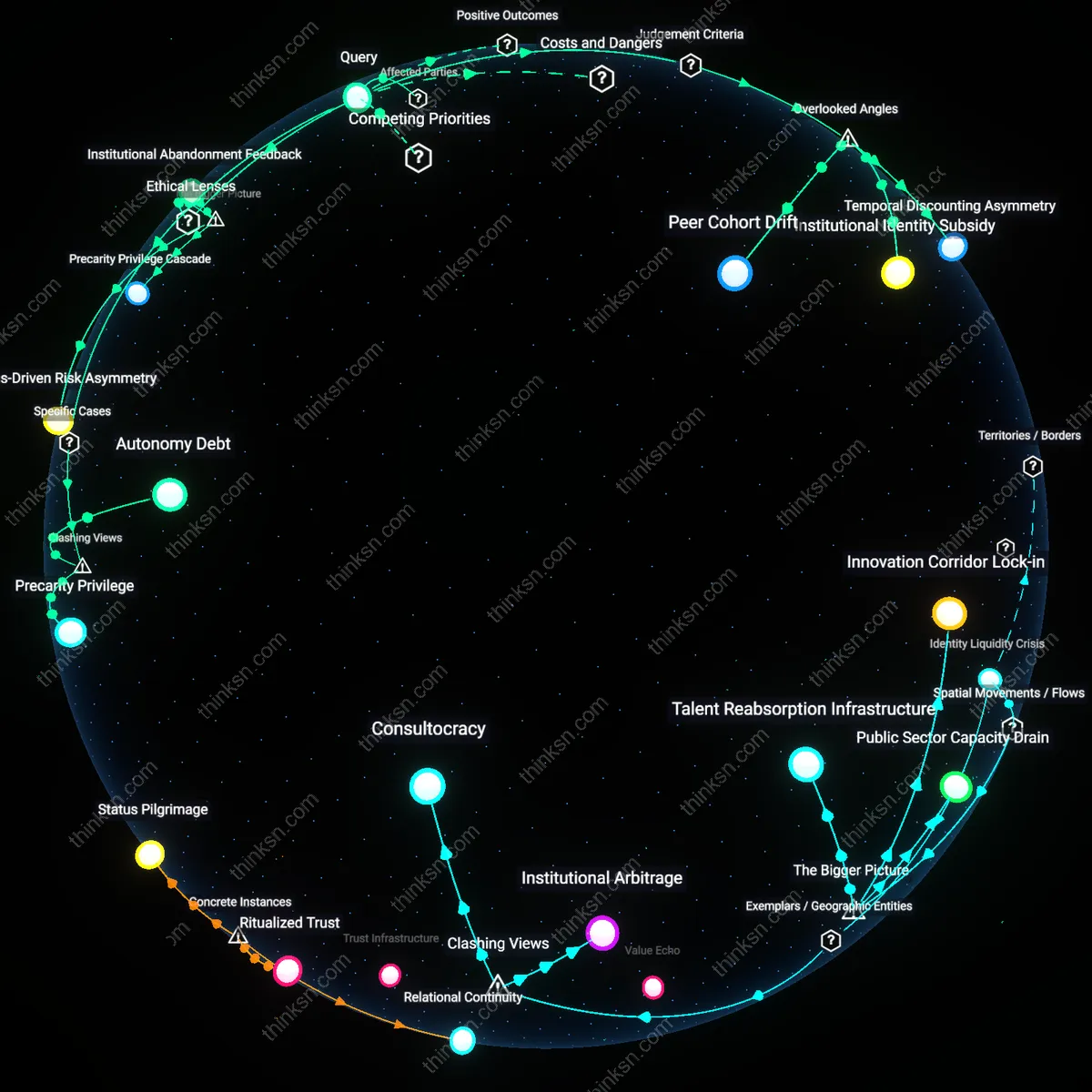
Trust Inertia
Third-party vendors integrated with the original identity provider continue to treat authentication decisions as trusted proxies for corporate due diligence, extending implicit validation to transactions even after the provider switch, because contractual SLAs and integration agreements rarely include dynamic clauses for identity provenance updates. This form of trust inertia manifests when external partners fail to refresh metadata endpoints or re-negotiate SAML assertions, allowing former identity signatures to retain residual authority in ecosystems like supply chain portals or co-managed cloud projects. The unnoticed persistence of these backchannel validations enables procedural fraud risks not through technical breach, but through institutional delay in updating trust boundaries, revealing that identity portability is constrained as much by inter-organizational contract cadence as by technical configuration.
Architectural Debt
Switching identity providers exposes the accumulated architectural debt from years of ad hoc integrations, where developers prioritized speed over abstraction by hardcoding identity calls into microservices, CI/CD pipelines, and monitoring tools. Unlike modular components, these embedded dependencies do not fail gracefully during replacement attempts; instead, they produce unpredictable access outages, authentication timeouts, or privilege escalation risks when the identity source changes. This debt persists because cloud-native development cultures reward feature velocity and decentralized innovation, disincentivizing the creation of unified identity abstraction layers. The overlooked systemic effect is that cloud scalability enables—and even encourages—the deferral of structural discipline, making identity a de facto technical monoculture that resists change long after business needs evolve.