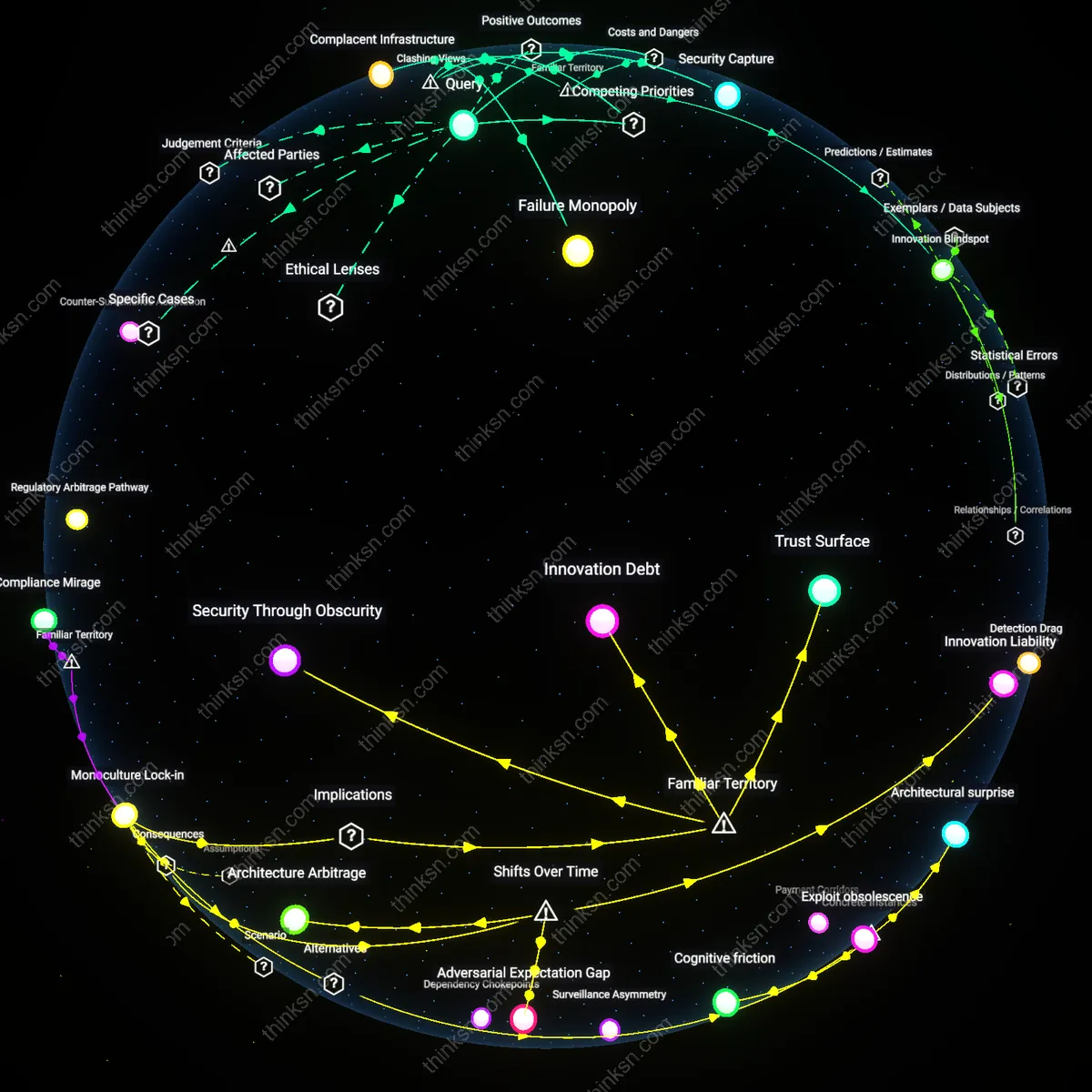
Is Monopoly Power Undermining Fraud Prevention Innovation?
Analysis reveals 6 key thematic connections.
Key Findings
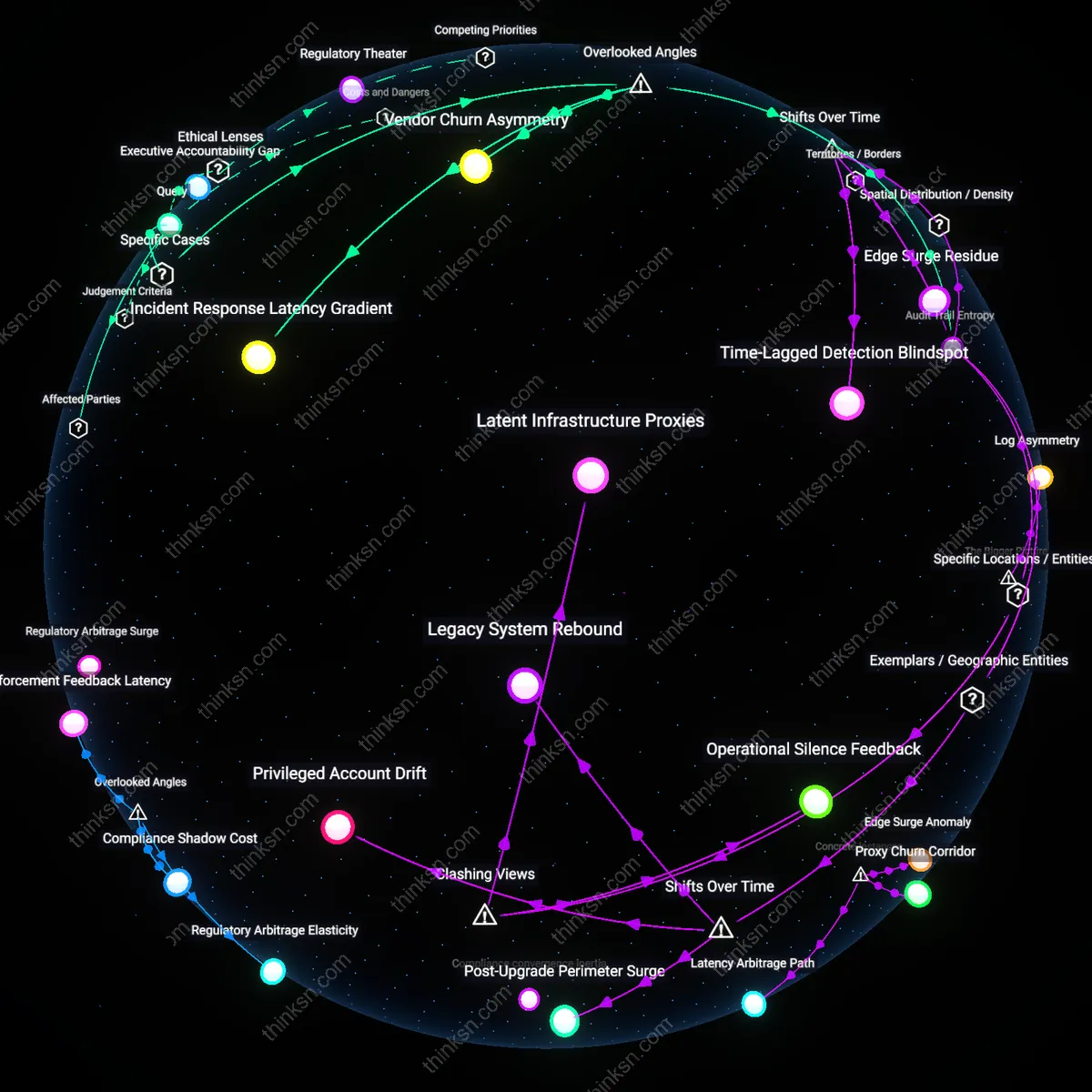
Complacent Infrastructure
It is irrational to rely on one payment processor's fraud prevention because market dominance enables erosion of operational vigilance across the ecosystem. As entities like Visa or Stripe face diminished competitive pressure, their incentive to invest in proactive fraud detection diminishes, allowing known vulnerabilities—such as synthetic identity fraud or merchant-side skimming—to persist longer than in a competitive market. This creates a false sense of security where downstream businesses and consumers assume protection is robust simply because the brand is ubiquitous. The non-obvious danger under familiar concerns about 'big tech monopolies' is that systemic rot sets in not through malice but through accepted underperformance.
Innovation Blindspot
It is irrational to rely on one payment processor's fraud prevention because dominant platforms inherently deprioritize disruptive anti-fraud technologies that threaten their own business model stability. Companies such as PayPal or Square, when dominant, optimize for scale and interoperability, not edge-case detection, leading them to ignore or suppress novel approaches like decentralized identity verification or on-chain forensic analytics. In public discourse, people associate monopolies with high prices, but overlook how dominance freezes technical imagination, especially in backend trust infrastructure. The real cost is not just fraud that slips through, but fraud that could've been prevented by alternatives that never emerge.
Centralized Target
It is irrational to rely on one payment processor's fraud prevention because concentrated transaction processing creates a single high-value attack surface that escalates systemic risk. When services like Stripe handle payments for millions of Shopify stores, adversarial actors—from cybercriminal rings to state-sponsored hackers—focus exploitation efforts on that one node, knowing a single breach yields maximum data yield, as seen in past breaches of centralized gateways. The public often worries about 'hacking' generally, but fails to grasp how market consolidation turns security into a bottleneck, making catastrophic compromise not just possible but probable over time.
Innovation Rent
Relying on a dominant payment processor's fraud prevention is rational for individual merchants because it minimizes immediate transaction losses, but this rationality systematically extracts innovation rent from the broader ecosystem by concentrating control over fraud signatures and risk models in a single proprietary infrastructure. Payment processors like Stripe or PayPal internalize the developmental costs of anti-fraud tools while externalizing stagnation onto competitors and future entrants, who cannot access sufficient transaction data to train alternative models, thus locking in methodological conservatism under the cover of security efficiency. This creates a non-obvious conflict where short-term risk mitigation actively suppresses the variety of approaches needed for long-term fraud resilience, revealing a hidden cost embedded in rational adoption.
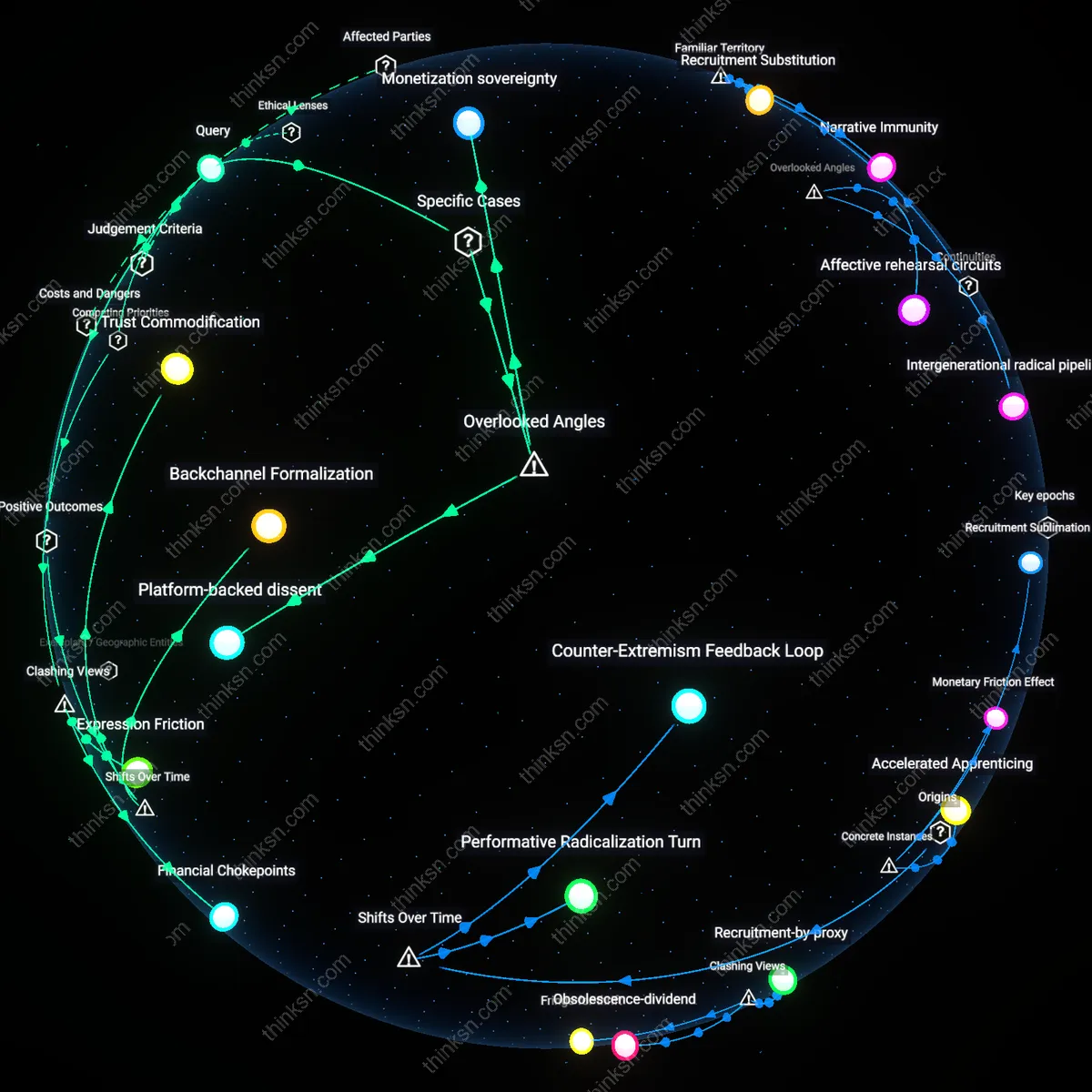
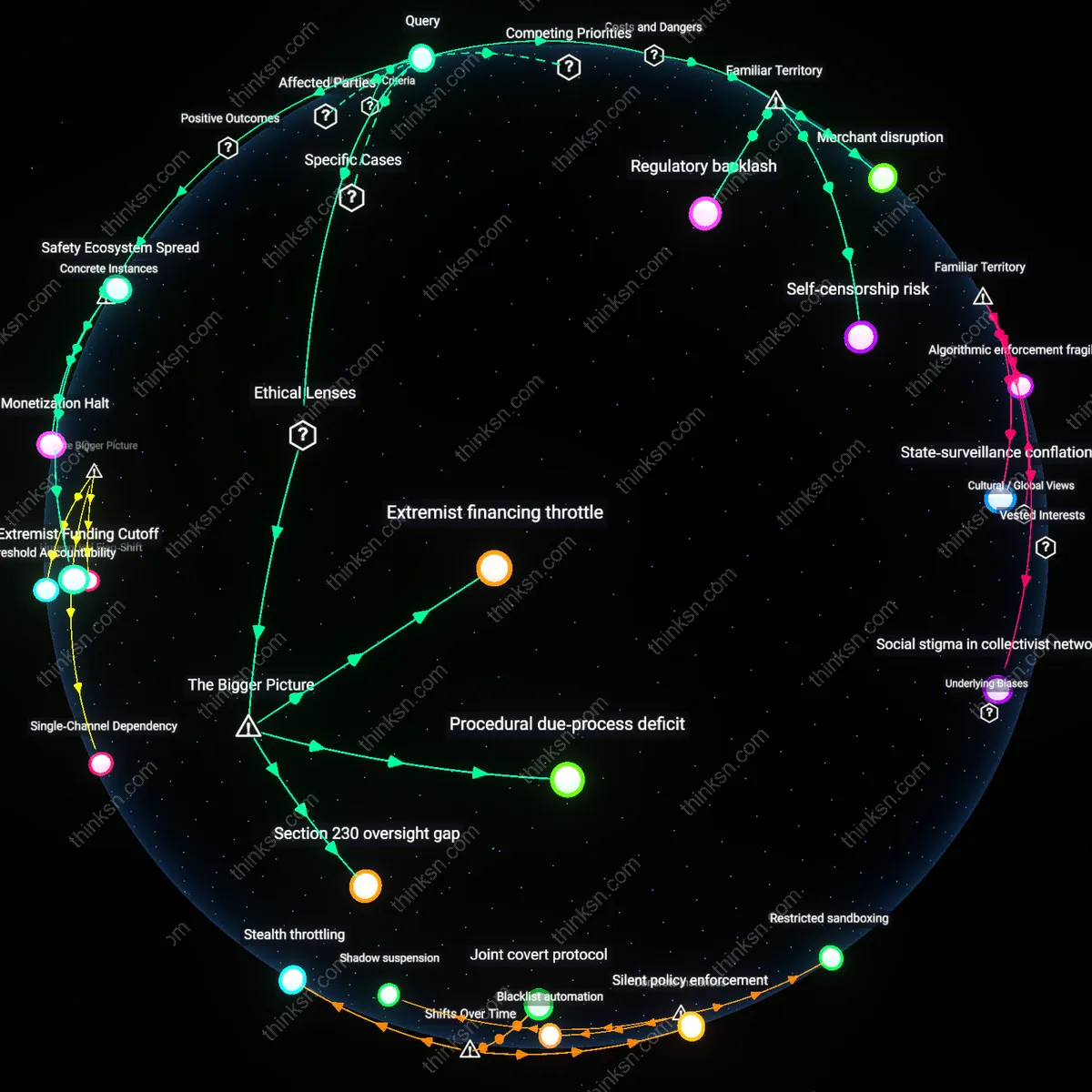
Security Capture
It is rational to rely on a dominant payment processor’s fraud prevention precisely because its market dominance enables regulatory capture under the guise of security standardization, allowing the processor to shape compliance requirements in ways that codify its own technical architecture as mandatory baseline practice. This mechanism, exemplified by Visa and Mastercard’s influence on PCI-DSS enforcement, converts private corporate systems into public de facto standards, making alternative approaches legally nonviable even if technically superior. The non-obvious outcome is that rational reliance is not driven by performance but by institutionalized coercion, where the pursuit of security entrenches control at the expense of methodological pluralism in risk detection.
Failure Monopoly
Rational reliance on a single payment processor’s fraud prevention persists because collective rationality is structured around the avoidance of visible failure, not the optimization of systemic health, creating a failure monopoly where no actor bears responsibility for innovation deficits as long as fraud rates remain below public thresholds. Financial institutions, fintechs, and regulators all benefit from deferring to a dominant processor like Adyen or Square, as it absorbs blame during breaches while shielding others from liability, thereby disaligning incentives to develop competing models. The overlooked dynamic is that rationality here functions as a risk-transfer mechanism, not a technological calculation, exposing how accountability avoidance becomes the hidden engine of dependency.