Stricter AI Controls: Security Shield or Democratic Drag?
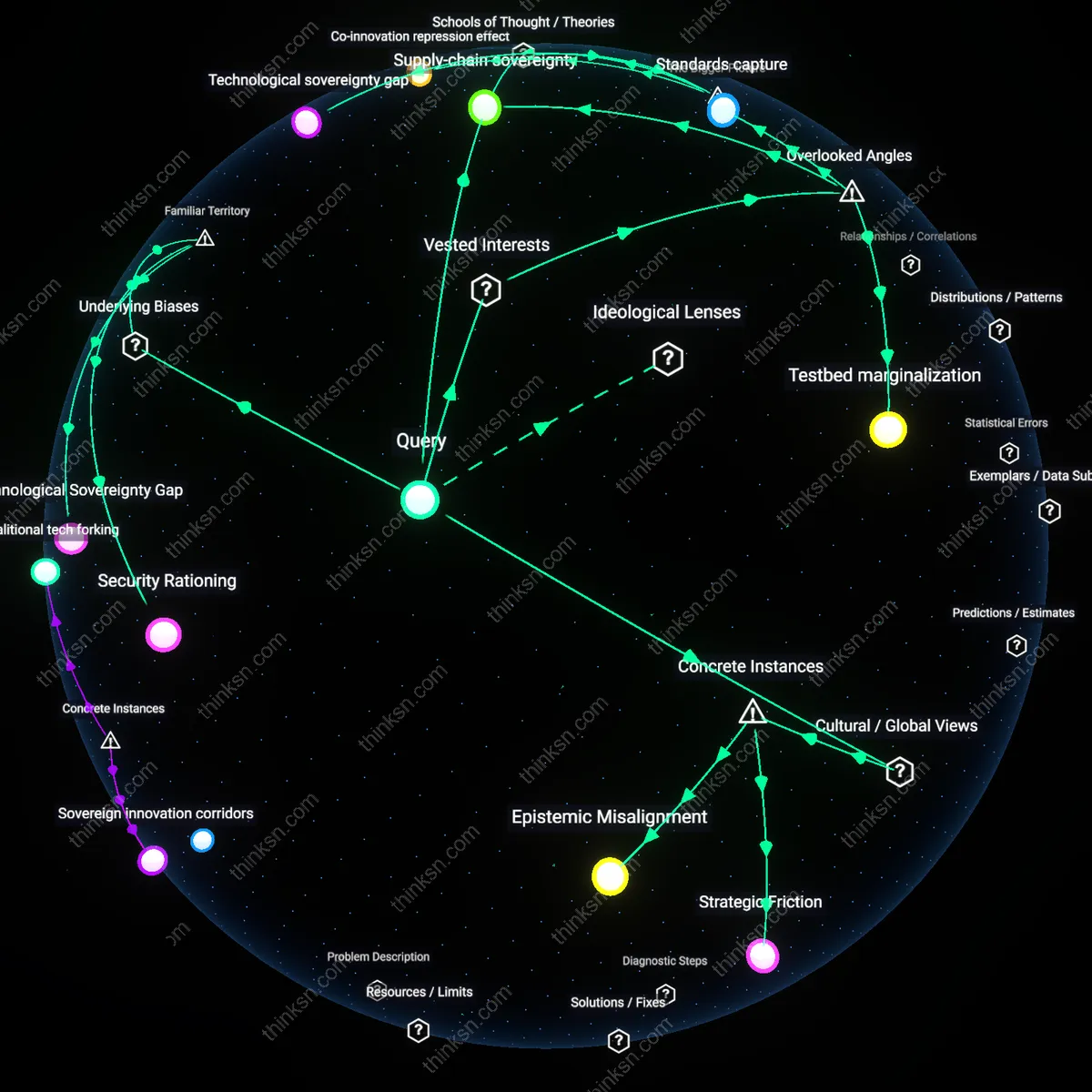
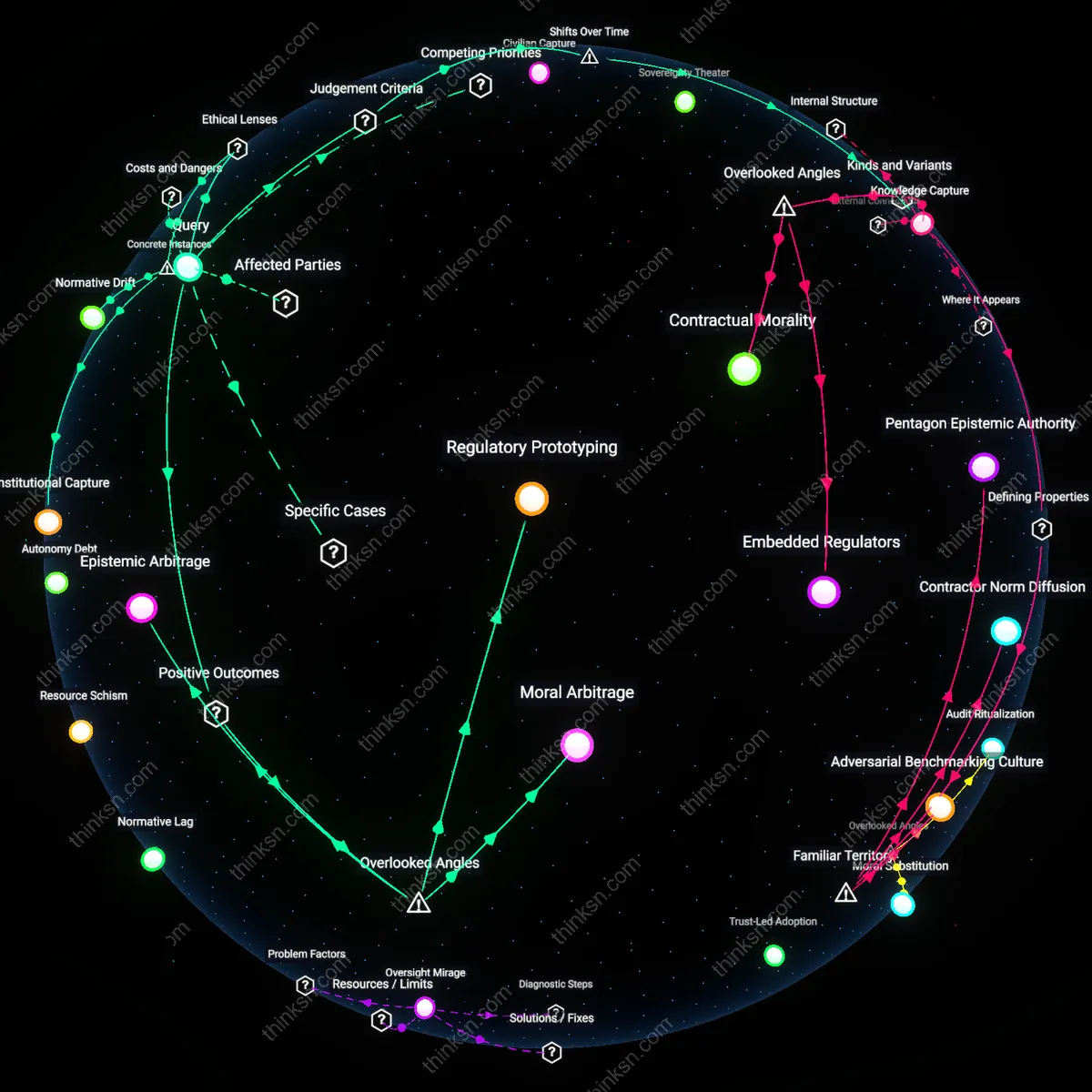
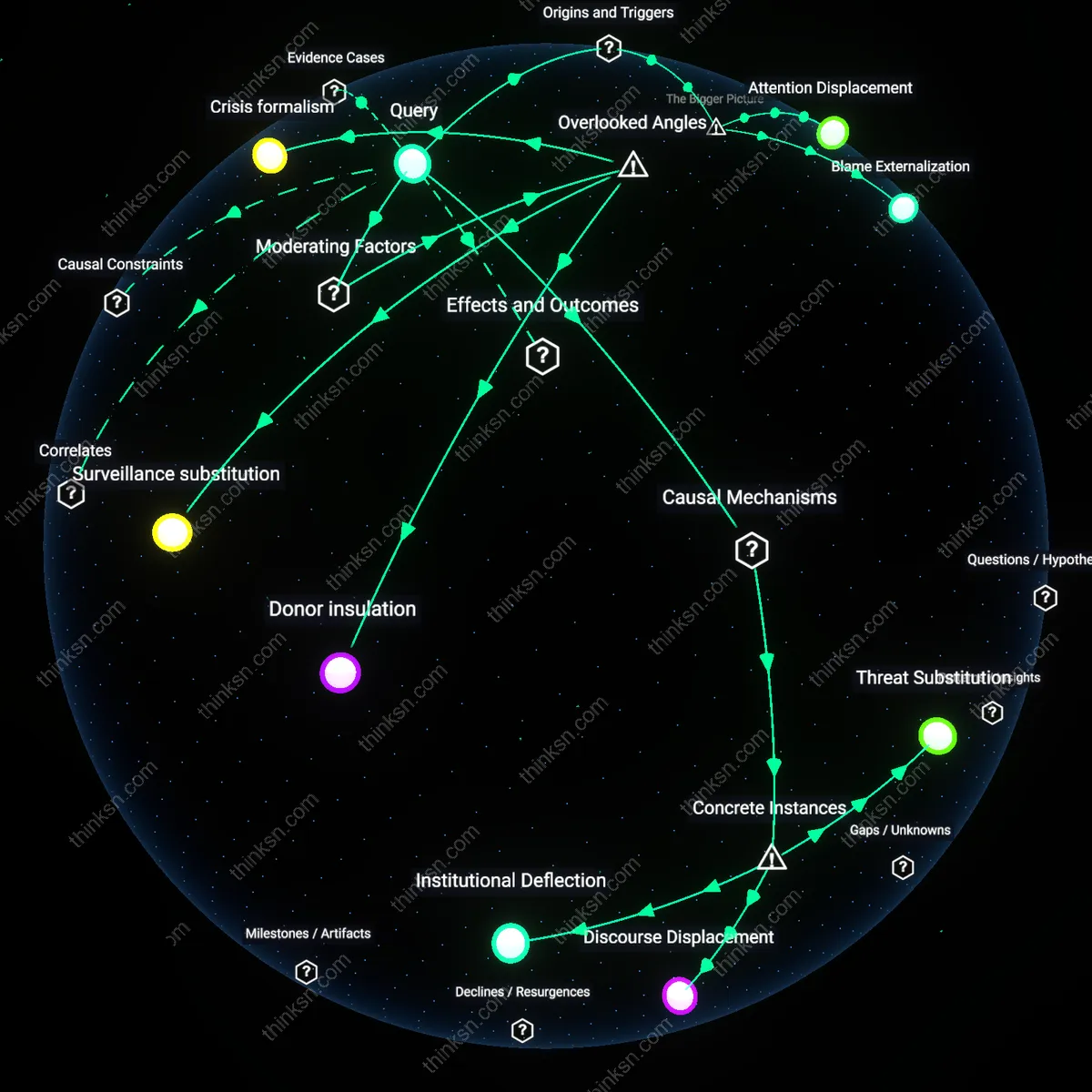
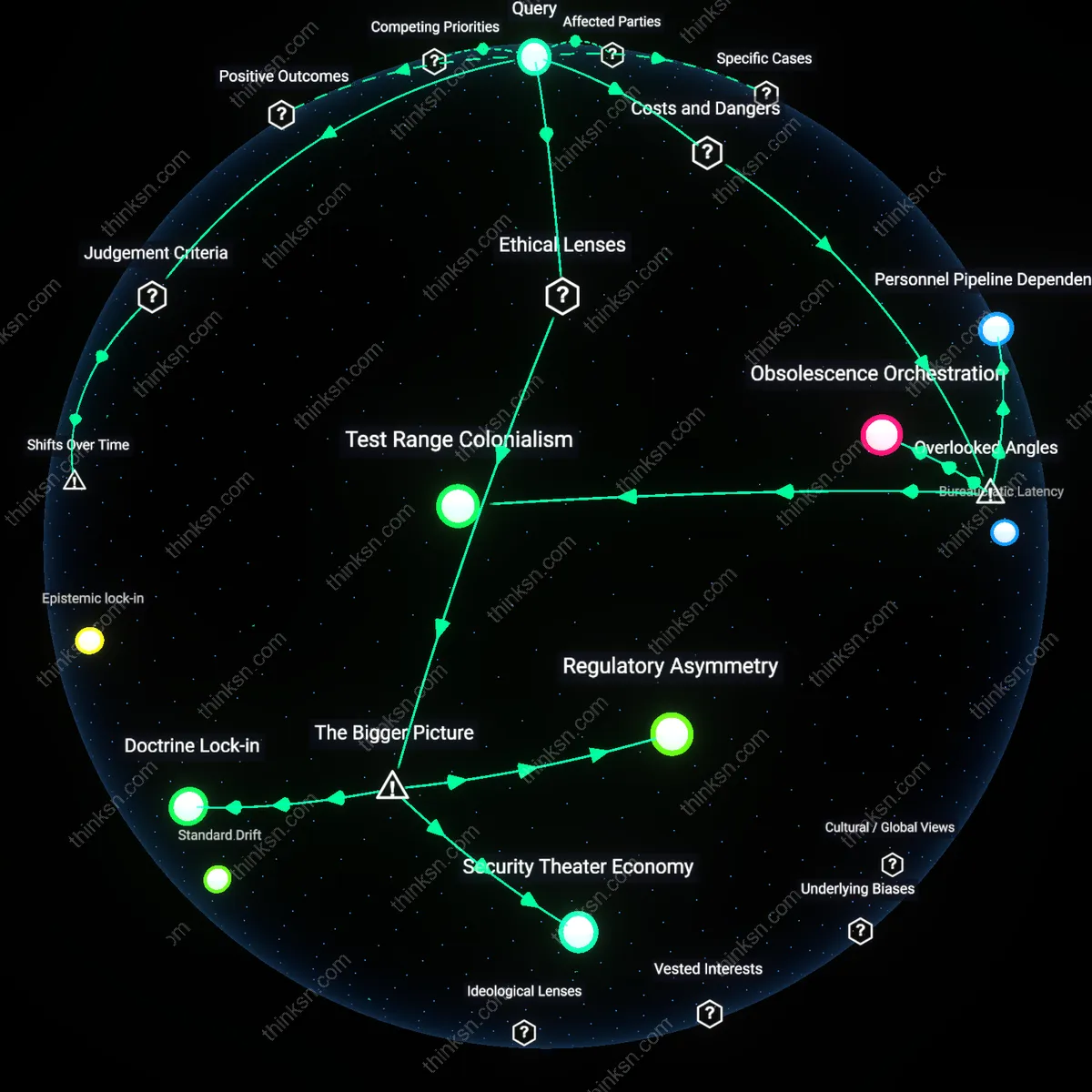
Analysis reveals 12 key thematic connections.
Key Findings
Security-development dilemma
Stricter AI export controls can undermine allied democracies' capacity to develop defensive AI by restricting access to foundational dual-use technologies, thereby creating a trade-off between short-term national security gains and long-term collective technological resilience. This occurs because export regimes like the Wassenaar Arrangement or U.S. Department of Commerce BIS regulations often classify advanced chips and machine learning frameworks as controlled items, limiting their flow even among trusted partners such as Germany, Japan, or South Korea. The mechanism hinges on asymmetric control enforcement where the exporting state (primarily the U.S.) prioritizes non-proliferation over interoperability, weakening co-developed defense AI systems like those used in missile defense or cyber threat detection. What is underappreciated is that these controls, designed to delay adversarial adoption, simultaneously erode the innovation velocity of democracies reliant on shared technological stacks, revealing a systemic trade-off inherent in alliance-centric security governance.
Technological sovereignty gap
By concentrating cutting-edge AI research and semiconductor manufacturing within a narrow set of jurisdictions—primarily the United States and Taiwan—stricter export controls amplify structural dependencies that prevent allied democracies from independently cultivating defensive AI capabilities. Countries like France or Australia face cascading delays in AI integration across military domains because they cannot access restricted tools such as high-bandwidth memory (HBM) chips or AI training platforms optimized for real-time battlefield analytics. This condition persists due to global value chains being deliberately fragmented by state-led export licensing regimes, which disproportionately affect mid-tier democracies lacking domestic alternative supply chains. The overlooked consequence is not just slowed development but the entrenchment of a hierarchy in the democratic techno-alliance, where strategic autonomy becomes inversely proportional to technological self-sufficiency, thus reinforcing a sovereignty asymmetry among allies.
Co-innovation repression effect
Export controls disrupt collaborative R&D ecosystems essential for advancing defensive AI, such as NATO’s AI interoperability initiatives or EU-funded military-civilian AI consortia, by legally fragmenting knowledge flows across otherwise aligned democracies. When institutions like DARPA or the European Defence Fund produce breakthroughs contingent on export-controlled components, partner nations cannot legally integrate, test, or iterate upon those innovations without re-creating entire subsystems from scratch. This regulatory friction operates through project deceleration and duplication, where compliance overhead outweighs cooperative advantage, ultimately depressing joint innovation rates. The non-obvious outcome is that security-driven restrictions morph into systemic barriers that diminish collective learning—the very process through which democracies have historically outpaced authoritarian regimes in adaptive military technology—thereby generating an unintended innovation penalty within the alliance network.
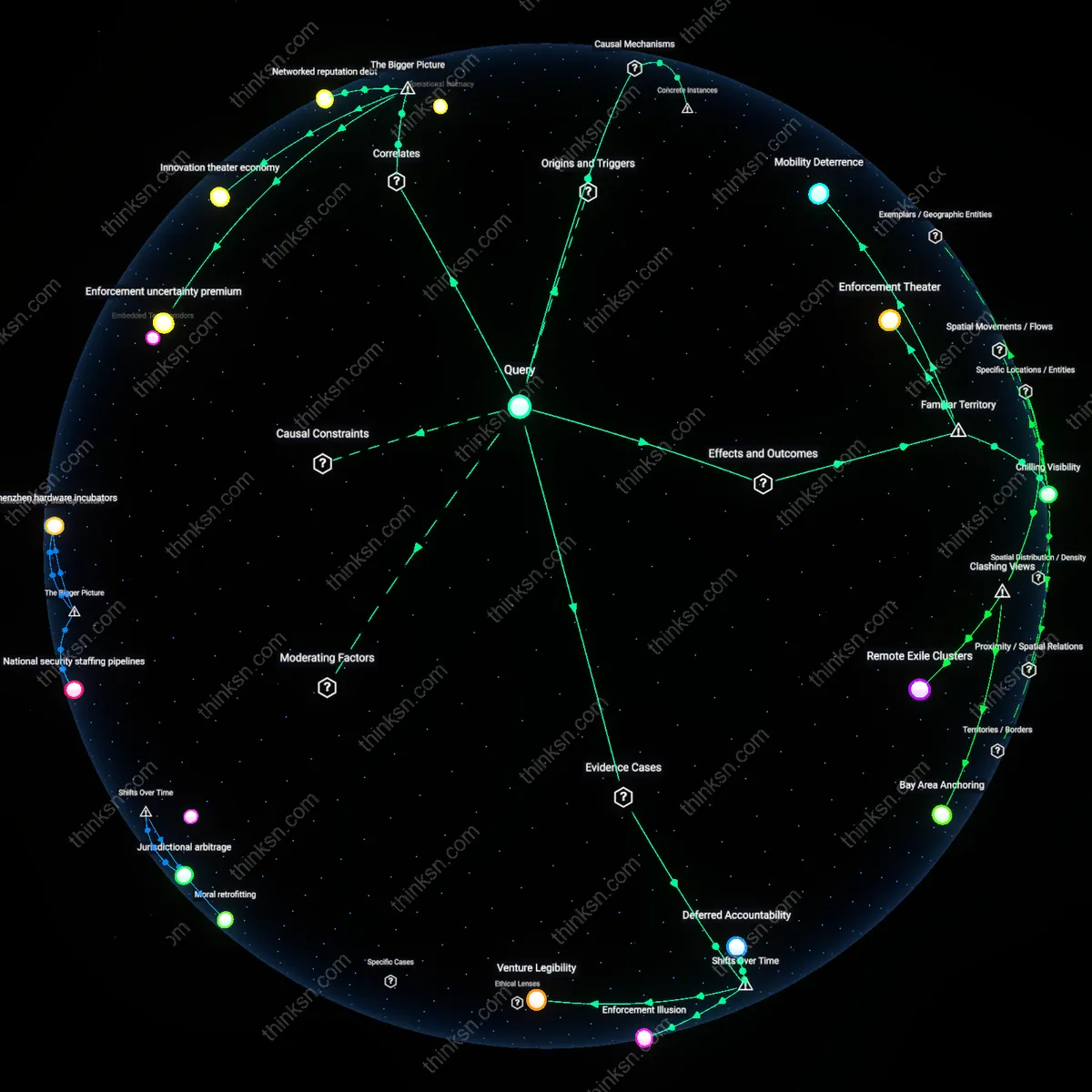
Strategic Friction
Stricter AI export controls imposed by the United States on South Korea restrict access to advanced semiconductor technologies essential for defensive AI systems, slowing Seoul’s ability to develop counter-drone and electronic warfare capabilities despite shared security interests. This occurs because U.S. regulations, shaped by a Western risk calculus prioritizing technology containment over alliance interoperability, treat South Korea as a potential proliferation conduit rather than a trusted peer, exposing how national security frameworks can generate friction within democratic alliances when cultural assumptions about technological stewardship diverge. The underappreciated reality is that these controls operate not through technical inadequacy but through asymmetrical trust architectures rooted in divergent historical experiences with technology leakage.
Epistemic Misalignment
India’s exclusion from access to U.S. AI-enabled satellite surveillance tools due to stringent export controls impedes its capacity to autonomously monitor border incursions, even though New Delhi shares intelligence with QUAD partners, because American regulatory frameworks presuppose a Western, institutionalized model of technology governance that does not align with India’s adaptive, context-responsive defense innovation culture. This misalignment reveals that what the West categorizes as 'security-sensitive' is often perceived in South Asian strategic thought as operational necessity, producing a disconnect in how AI development timelines and threat responses are valued across democracies. The overlooked mechanism is not technological but epistemic—differing cultural logics of military knowledge production shape what is deemed 'defensive' versus 'strategic.'
Technological Hierarchy
The Netherlands’ restriction on exporting ASML’s deep ultraviolet (DUV) lithography machines to Taiwan—even as Taipei seeks to fortify AI-driven cyber defense systems—demonstrates how Western-led export regimes, influenced by U.S. diplomatic pressure, embed a tiered architecture of technological legitimacy where allied democracies are ranked by geopolitical leverage rather than shared democratic values. Because Dutch export decisions reflect a Euro-Atlantic security ethos that subordinates Pacific democracies’ autonomy in capability development to broader containment strategies, the outcome is a de facto stratification where access to foundational AI hardware is determined by strategic geography, not mutual defense need. The unacknowledged consequence is that defensive self-reliance among frontline democracies becomes structurally inhibited by hierarchical norms disguised as cooperation.
Security Rationing
Stricter AI export controls systematically disadvantage allied democracies with less semiconductor infrastructure by restricting access to foundational training hardware, such as high-bandwidth GPUs, which are controlled under U.S. jurisdiction. This creates a tiered innovation system where capabilities in defensive AI—such as deepfake detection or cyber intrusion prediction—advance faster in the controlling state than among peers, particularly those dependent on American technology supply chains. The non-obvious consequence is that national security rationing masquerades as collective defense, but in practice delays allied autonomy in critical response systems, revealing an embedded assumption that security leadership should centralize in Washington rather than distribute across coalitions.
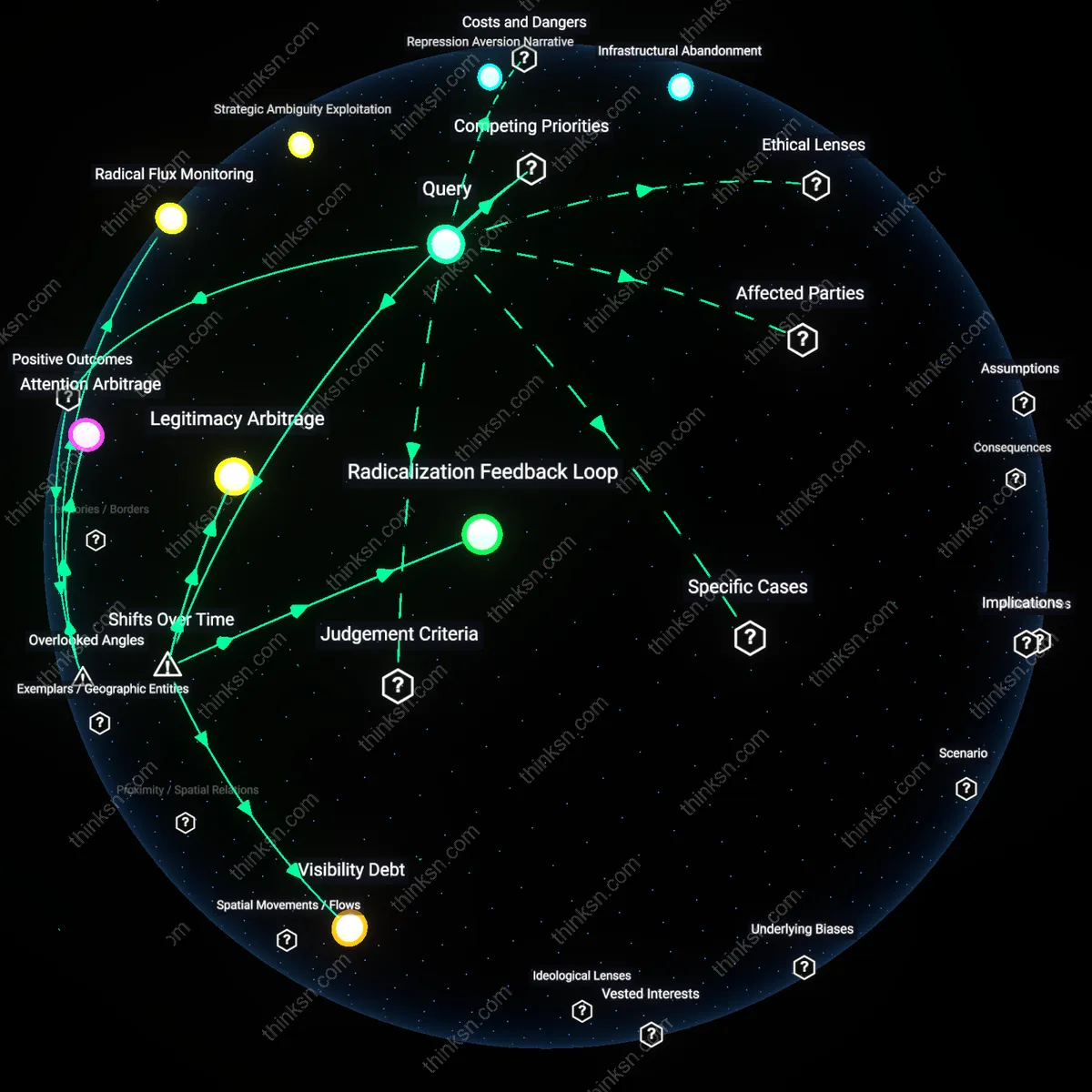
Vulnerability Theater
Export controls are framed as essential for preventing adversary access to dual-use AI, but in practice they spotlight the exporter’s own technical dominance as the primary security asset, elevating visibility and political leverage for U.S. defense contractors and standards bodies. By delaying or degrading allied AI development through restricted toolchains, the policy produces symbolic reassurance—'something is being done'—while leaving actual threat response timelines unimproved. The underappreciated dynamic is that defensive paralysis among allies is not a bug but a feature that reinforces the perception of indispensability, making failure to act appear more dangerous than slow-rolling capability sharing under allied control.
Technological Sovereignty Gap
Western democracies that rely on U.S.-origin AI components face delayed domestic implementation of defensive systems—like automated missile trajectory prediction or signal jamming AI—because re-licensing and integration hurdles multiply under tighter controls, while domestic U.S. agencies bypass these delays via privileged access. This asymmetric friction entrenches a developmental lag between the controlling state and its democratically aligned partners, despite shared threat assessments. The overlooked reality is that 'allied' development assumes parity of access, but export regimes institutionalize divergence, treating sovereignty as a negotiated privilege rather than a shared baseline in coalition defense planning.
Supply-chain sovereignty
Stricter AI export controls enable dominant tech states to reframe dependency on foreign AI components as a security threat, thereby justifying domestic capture of critical nodes in the semiconductor and foundational model supply chains. U.S. semiconductor firms like NVIDIA lobby for controls that restrict China’s access to high-end chips while securing exceptions for allied firms, positioning themselves as arbiters of which democracies qualify for AI capacity. This transforms infrastructure access into a geopolitical currency, where national security logic entrenches corporate-state alliances that selectively throttle allied AI development under the guise of cohesion. The non-obvious dimension is that export controls don’t merely restrict adversaries—they actively redesign the hierarchy of trust within the democratic bloc, privileging nations with integrated supply chains and freezing out smaller allies who rely on distributed sourcing. This shifts the focus from intent (defensive AI) to lineage (where components originate), a dependency rarely acknowledged in alliance strategy.
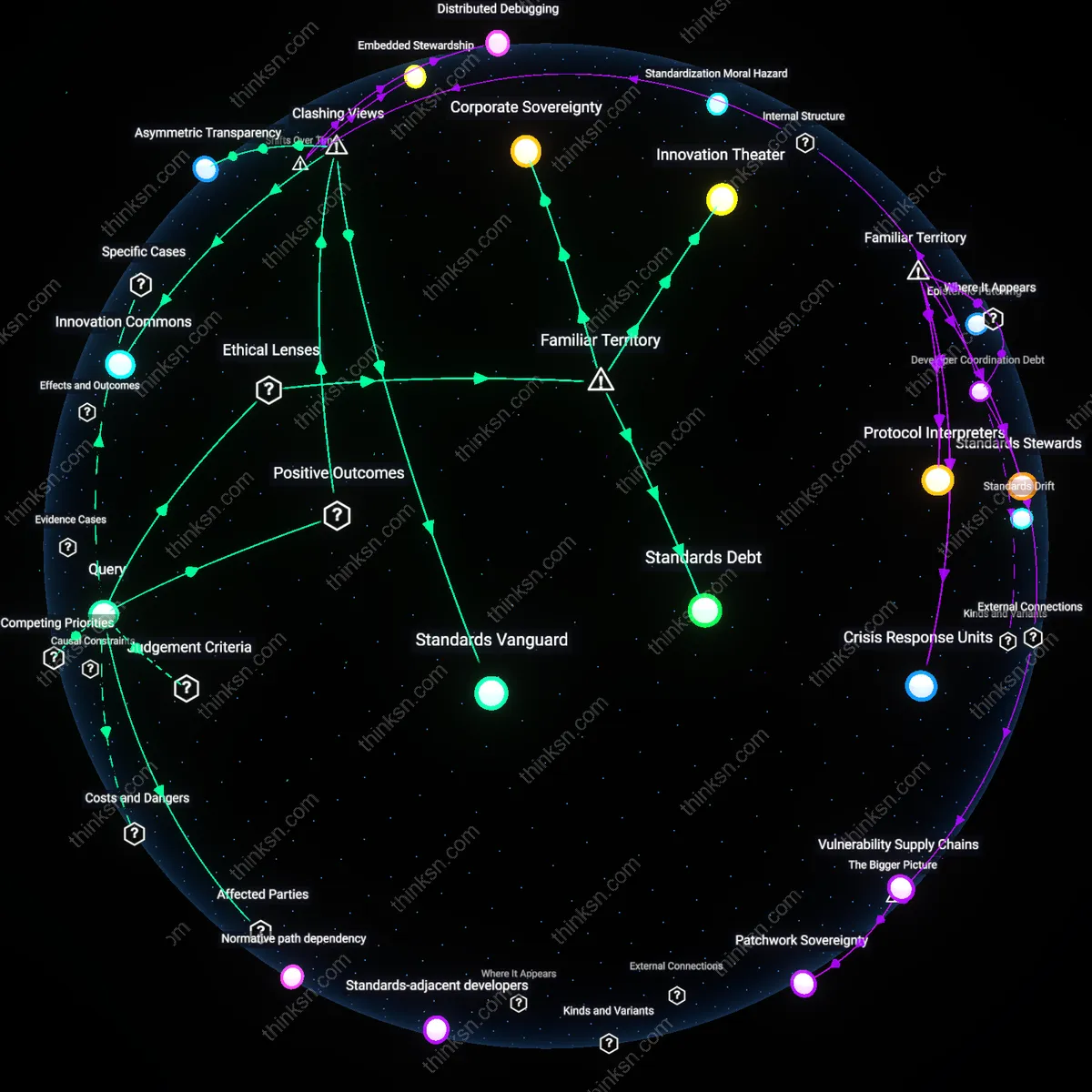
Standards capture
Western regulatory bodies and AI ethics consortia use export control frameworks to embed governance norms—such as auditability and human oversight—into the technical design of AI systems before they are exported, effectively conditioning allied access to defensive AI tools on ideological alignment. By framing certain architectures (e.g., opaque large language models) as inherently risky, they justify restricting not only hardware but the very paradigms available to partner states, privileging Western-developed, rule-compliant models. This allows NGOs and regulatory agencies in the EU and U.S. to exert soft power by making compliance with democratic values a technical prerequisite, not a policy choice. The overlooked dynamic is that control operates not through denial but through design constraints, where the architecture of defensible AI is pre-shaped to reflect the epistemic priorities of the controlling bloc—thus undermining epistemic autonomy among allies who may require different risk-calculus for their threat environments.
Testbed marginalization
Smaller allied democracies with high digital penetration but limited AI R&D capacity—such as Estonia or Singapore—lose access to real-world deployment data when export controls restrict their ability to integrate global AI models into national defense systems, slowing their capacity to generate operational feedback for defensive innovation. The logic of containment assumes that restricting capability diffusion preserves security, but it simultaneously denies mid-sized democracies the iterative testing environments needed to refine context-specific AI defenses against hybrid threats like disinformation or drone swarms. These nations become dependent on prepackaged, sanitized AI solutions from major powers, which lack adaptability to localized attack surfaces. The hidden dependency is that defensive AI maturity relies not just on access to hardware or models, but on the right to fail—and learn—in sovereign operational domains, a condition eroded when export controls outsource risk assessment to the exporting state.