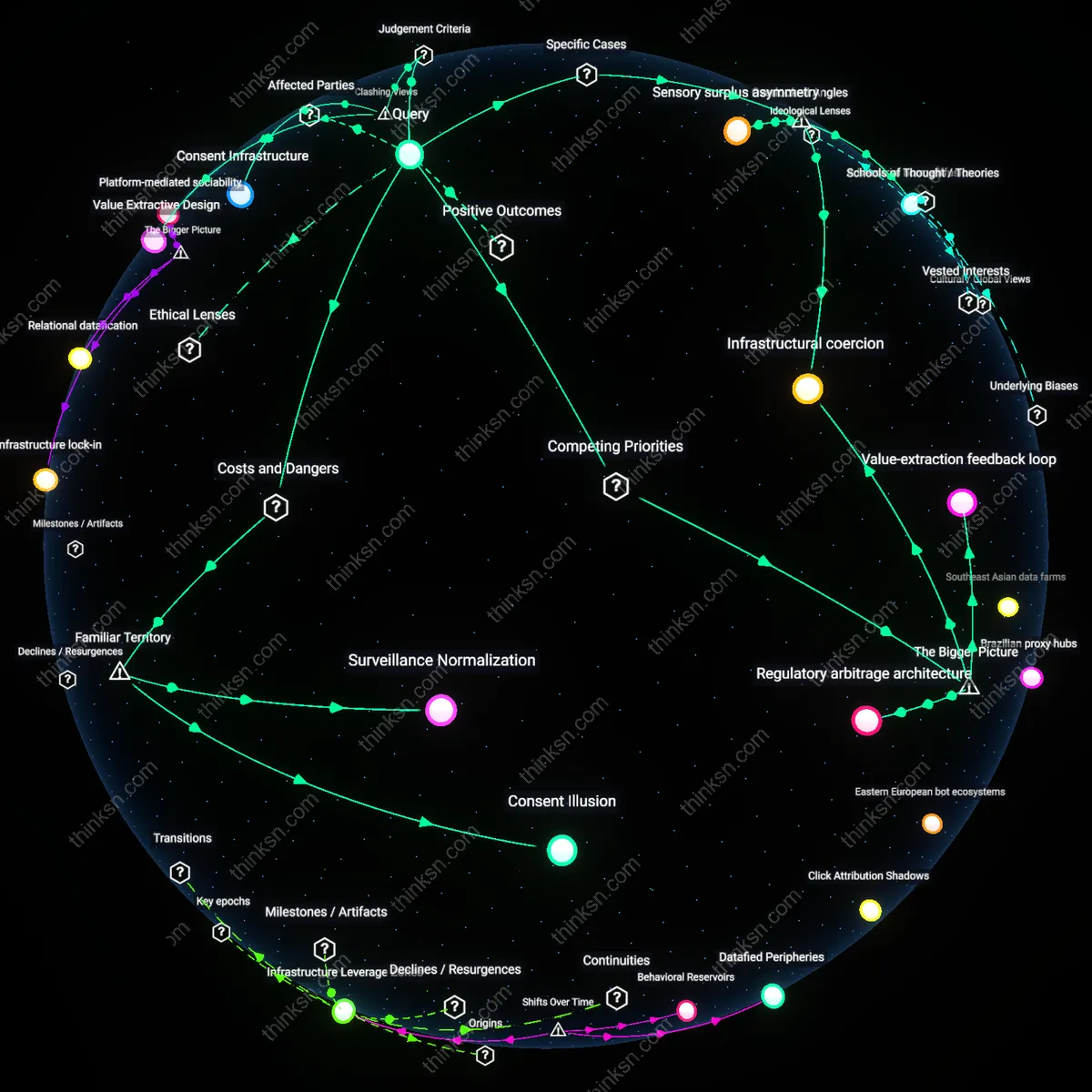
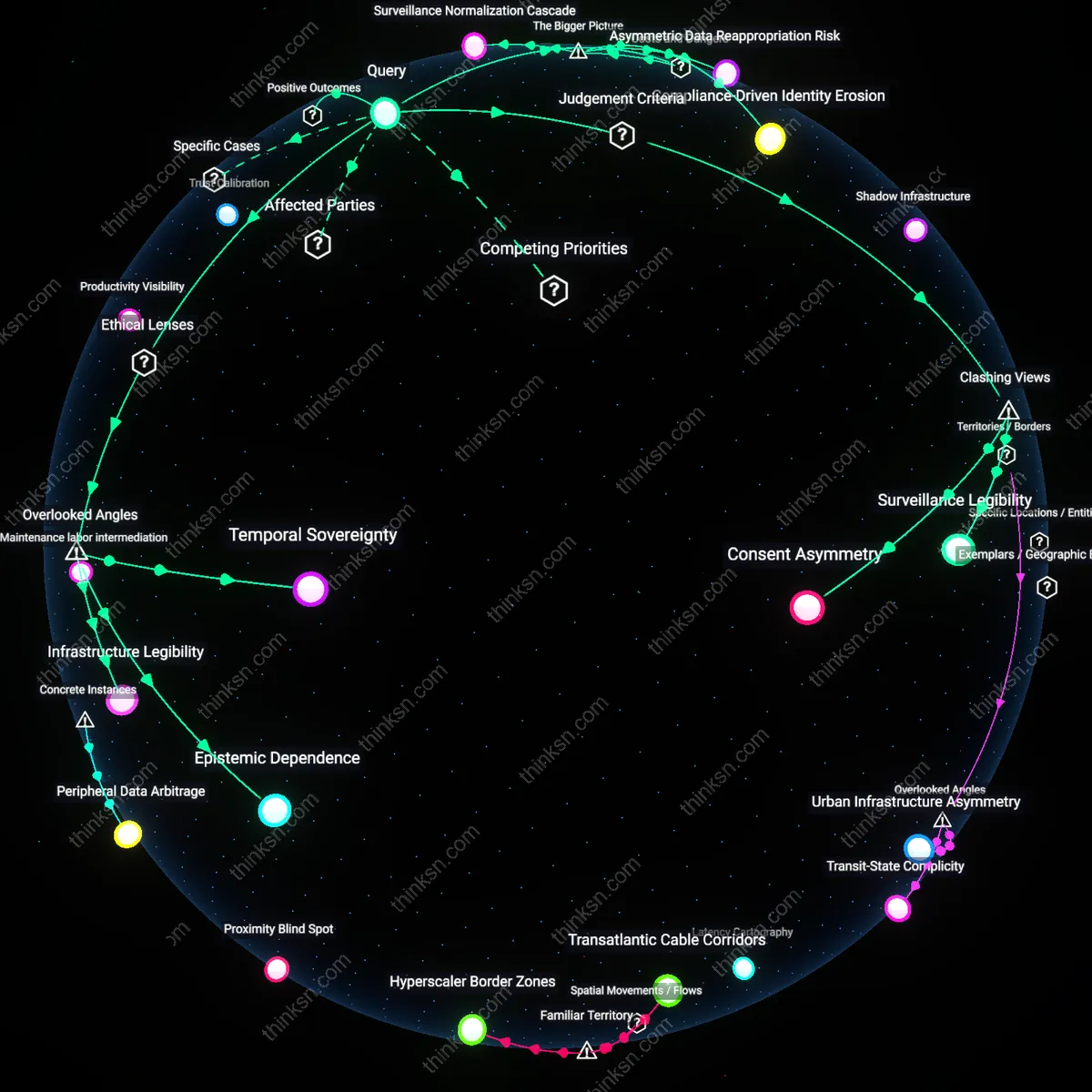
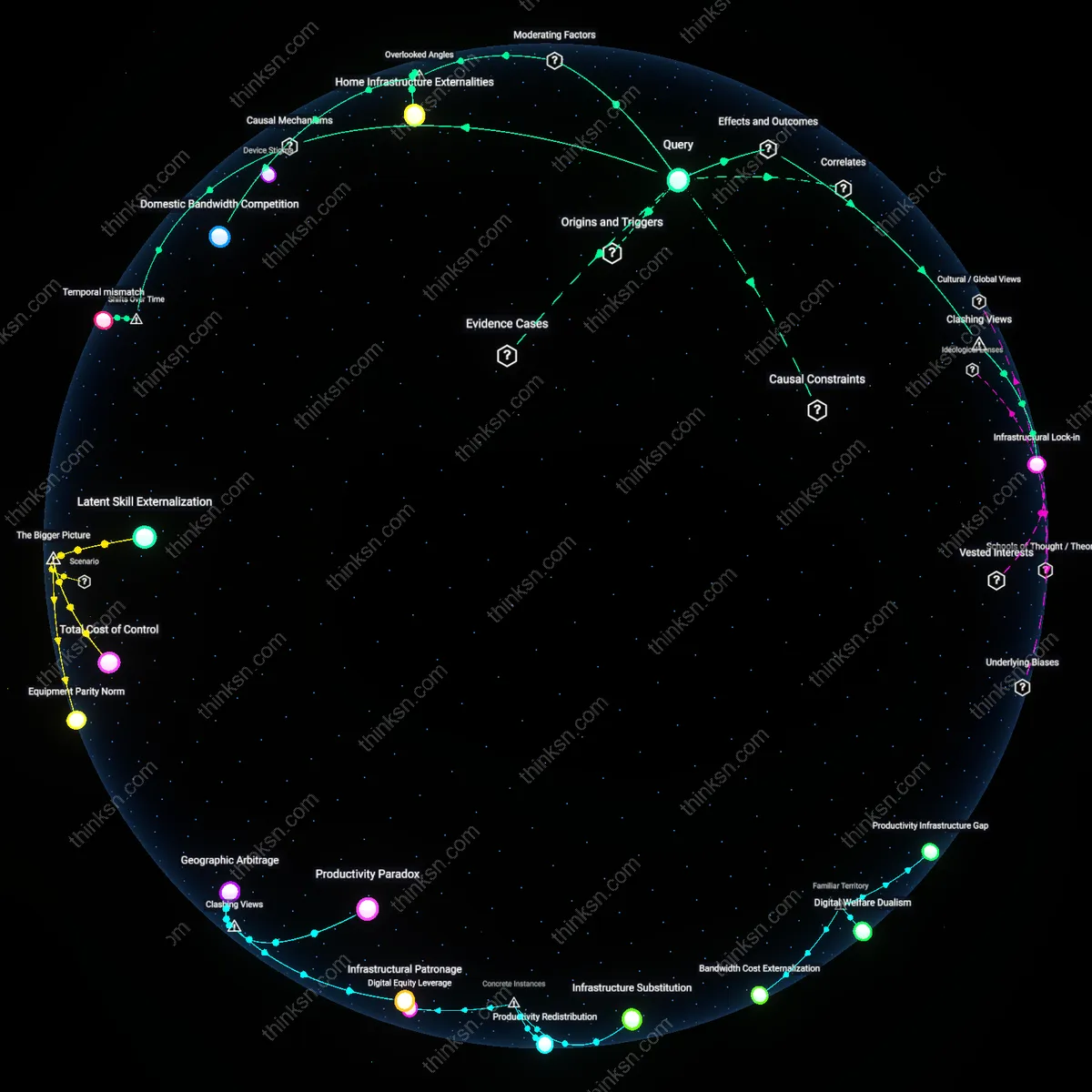
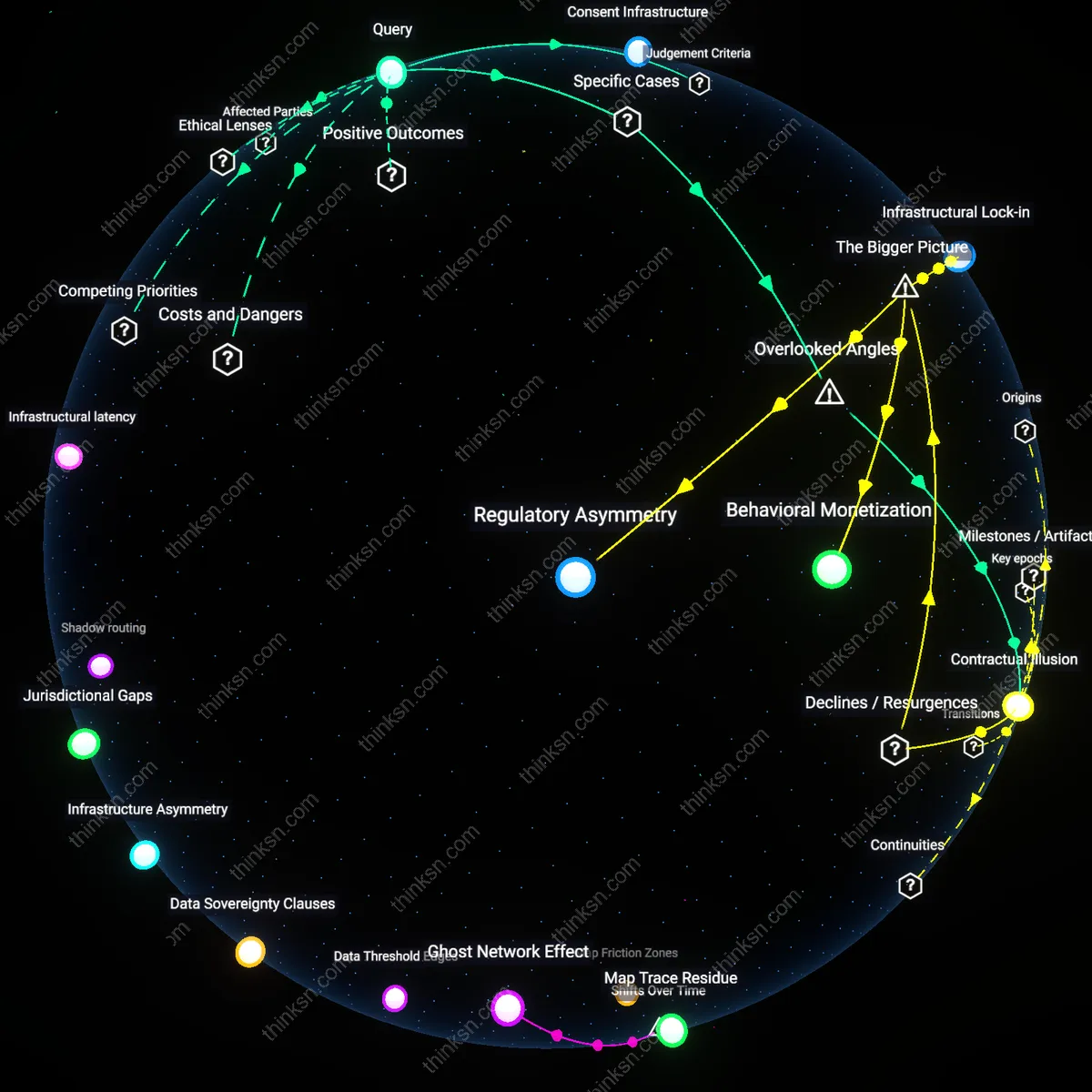
CDN Throttling: Silencing Minority Voices or Necessary Control?
Analysis reveals 9 key thematic connections.
Key Findings
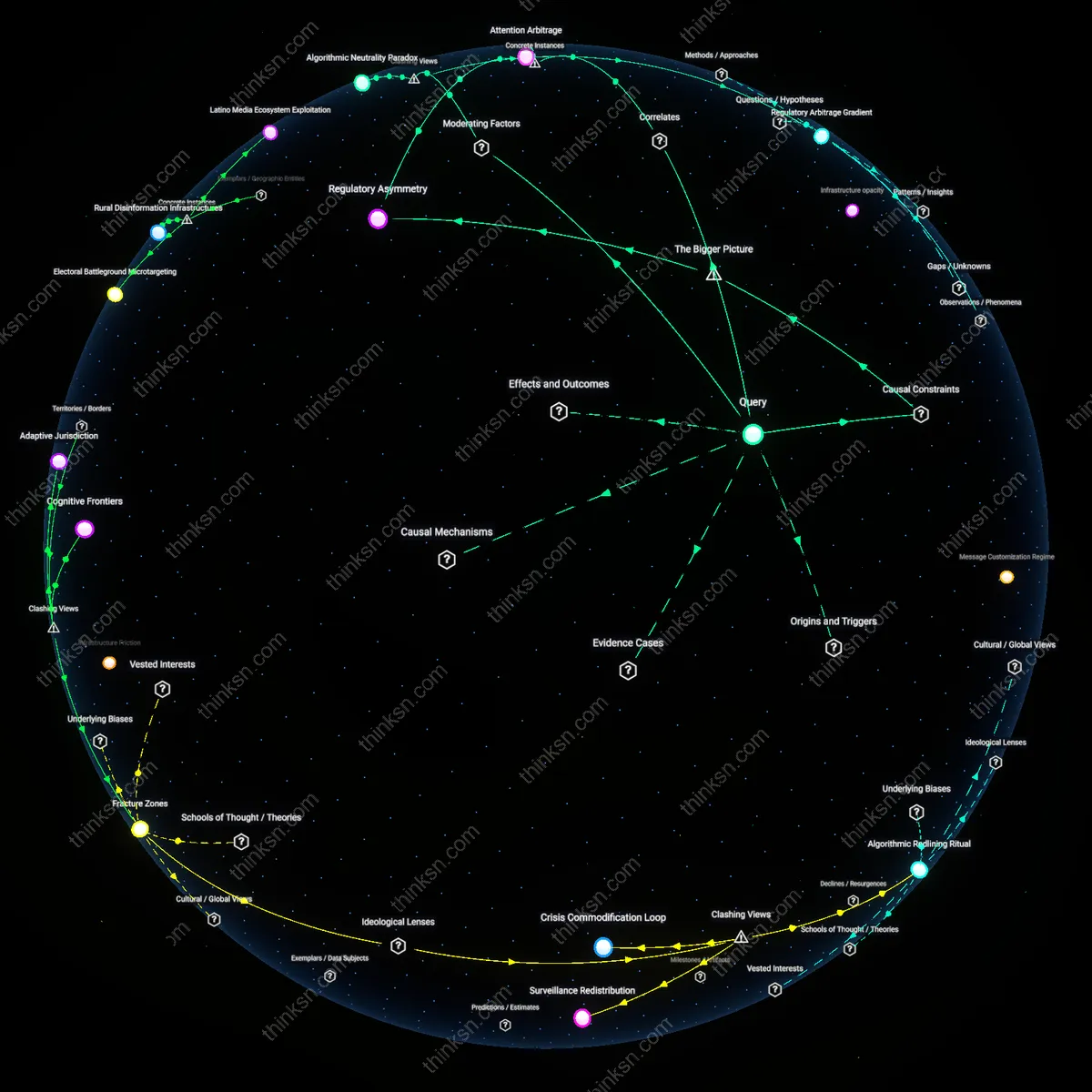
Infrastructural Bias
Content delivery network operators throttle traffic from IP ranges associated with low-income or marginalized urban areas, where minority political movements often originate, because these ranges correlate with higher rates of spam or DDoS attacks. This technical risk assessment, based on historical usage patterns, systematically disadvantages legitimate political organizing by equating it with malicious activity. The mechanism operates through automated reputation scoring systems that lack contextual awareness of sociopolitical mobilization, leading to invisible but widespread suppression of digital outreach, livestreams, and encrypted coordination. What’s underappreciated is that the filter is not political in intent but emerges from routine cybersecurity logic, making it harder to challenge through traditional free speech advocacy.
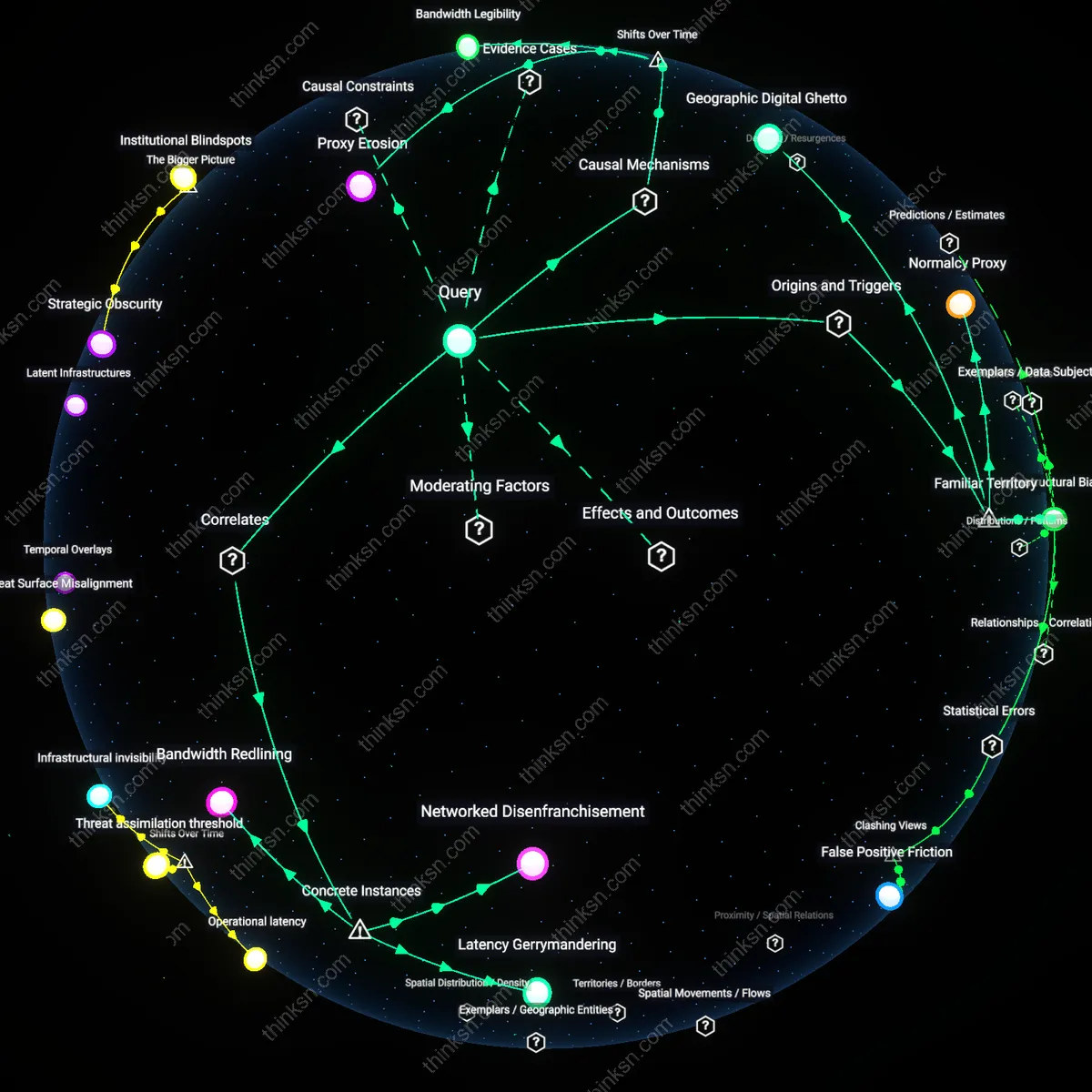
Geographic Digital Ghetto
Network infrastructure providers disproportionately assign static IP blocks in under-resourced neighborhoods to lower-tier transit paths with limited bandwidth and higher latency, which CDNs interpret as low-priority delivery zones. When minority political groups in these areas attempt to distribute video manifestos or real-time protest updates, the throttling appears as poor performance rather than active suppression, masking the structural inequality in internet plumbing. This creates a de facto digital ghetto where speech is not censored outright but degraded to irrelevance. The non-obvious insight is that most users associate censorship with overt blocking, not the mundane tiering of network service quality that quietly enforces spatial segregation online.
Normalcy Proxy
CDN traffic management algorithms rely on baselines of 'normal' usage—defined by volume, timing, and geographic distribution—to detect anomalies, but these baselines are calibrated to mainstream political communication patterns, such as scheduled press releases or centralized media distribution. When minority movements generate sudden, decentralized surges in peer-to-peer content sharing, especially from mobile networks in protest zones, the activity triggers throttling as an aberration. The system interprets political urgency as dysfunction, privileging predictable forms of expression over emergent ones. The overlooked aspect is that 'neutrality' in algorithmic design actually embeds a bias toward established political behavior, rendering insurgent voices structurally suspect by default.
Infrastructural Backlash
Content delivery network traffic throttling based on IP ranges disproportionately slows access to movement-hosted material when those ranges coincide with historically marginalized protest geographies, such as urban cores where minority political organizing intensified after the 2010s platformization of activism. Internet service providers and CDNs began optimizing for content locality and perceived threat profiles post-2016, correlating high traffic from dense, low-income IP blocks with botnet activity, thereby auto-throttling uploads from community centers or activist collectives relying on shared bandwidth—mechanically degrading the visibility of time-sensitive political content. This reflects a shift from content-based to location-implicit suppression, where risk algorithms absorb spatial stigma once held by policing institutions, rendering digital amplification unequal by default.
Proxy Erosion
Global CDNs introduced rate-limiting APIs in the late 2010s that treated all traffic from certain national IP ranges as suspicious following state-backed disinformation campaigns, which inadvertently dismantled the anonymizing benefit of shared infrastructure once used by minority movements in restrictive regimes. Dissident groups in post-2011 Middle Eastern uprisings relied on domestic IP proxies to mask identities while broadcasting via global content networks, but after 2018, large CDNs like Cloudflare and Akamai began deprioritizing packets from regions with high abuse reports, effectively collapsing the protective ambiguity between state trolls and grassroots actors. This marks a reversal from the early 2000s, when distributed server access empowered subnational voices, to a present where systemic distrust in regional traffic flows erodes the tactical advantage of networked anonymity.
Bandwidth Legibility
As CDNs adopted machine learning models in the early 2020s to forecast traffic anomalies, their training data reflected historical engagement norms centered on commercial usage patterns, causing non-commercial surges—like livestreams during the 2020 Black Lives Matter protests—to be flagged as aberrant and throttled. The shift from human-moderated to pattern-based traffic governance privileged predictable, monetizable flows over episodic civic amplification, embedding commercial temporality into infrastructure. This transformation reveals how minority movements, which depend on sudden, decentralized bandwidth demands, now face infrastructural resistance not as censorship per se but as algorithmic misrecognition—a systemic inability to read political urgency as legitimate traffic.
Networked Disenfranchisement
CDN traffic throttling during Sudan's 2019 internet shutdown disproportionately reduced connectivity for protest coordination centers in Khartoum’s peri-urban neighborhoods, where opposition-aligned activists relied on commercial ISPs with upstream CDN dependencies; this created a differential degradation of communication capacity tied to infrastructure geography rather than explicit state censorship, revealing how neutral technical practices can amplify political marginalization when access nodes align with sociopolitical peripheries.
Latency Gerrymandering
During the 2020 Belarusian election protests, CDN providers applied geofenced rate limiting to IP blocks associated with Minsk-based data hubs amid government-imposed network instability, unintentionally privileging state media affiliates that used diversified international peering over decentralized Telegram channels used by coordinators in regional hubs; this demonstrates how traffic management based on aggregate IP behavior can functionally redistribute visibility along informational fault lines that mirror, but are not dictated by, political boundaries.
Bandwidth Redlining
In the 2016 Standing Rock Sioux protests, CDN throttling of IP ranges associated with rural North Dakota cellular carriers degraded livestream reliability for water protector networks relying on mobile hotspots, while mainstream press using urban-originating CDN paths maintained full throughput; this highlights a pattern where content delivery systems interpret low-density, intermittent usage signatures—common in Indigenous and frontier communities—as non-priority traffic, thereby embedding spatial neglect into protocol-level prioritization.