Can Shield Laws Block Patient Record Sharing Across States?
Analysis reveals 10 key thematic connections.
Key Findings
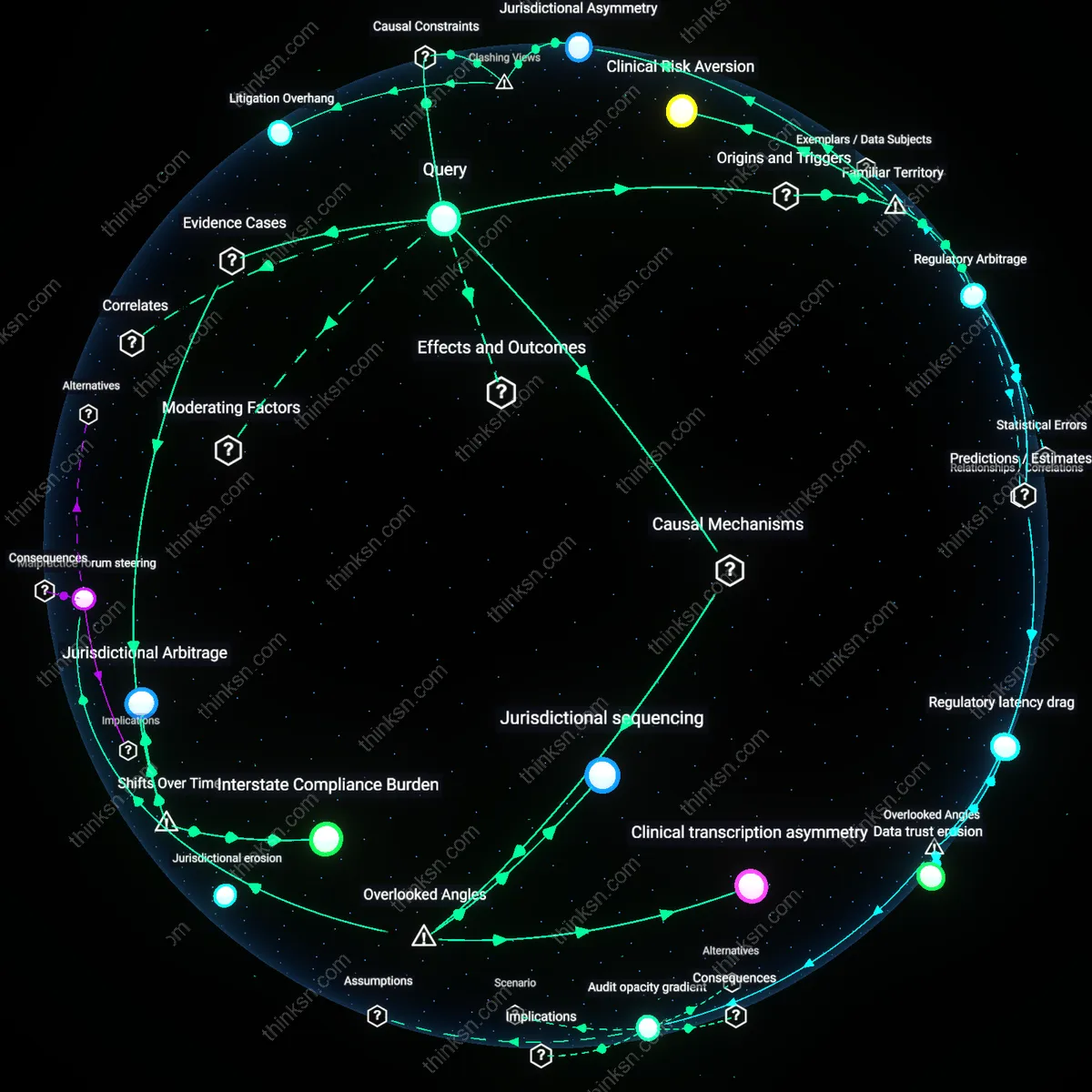
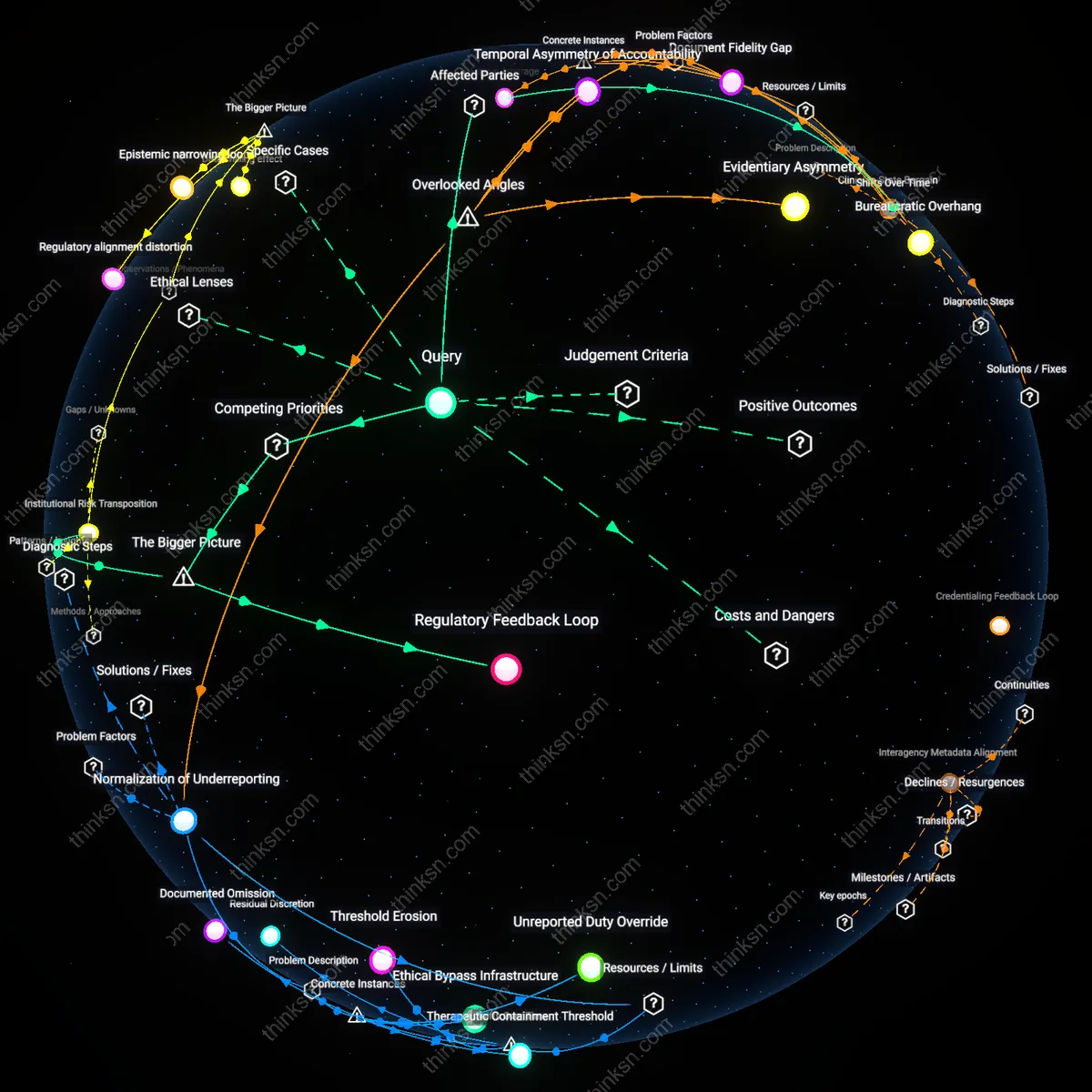
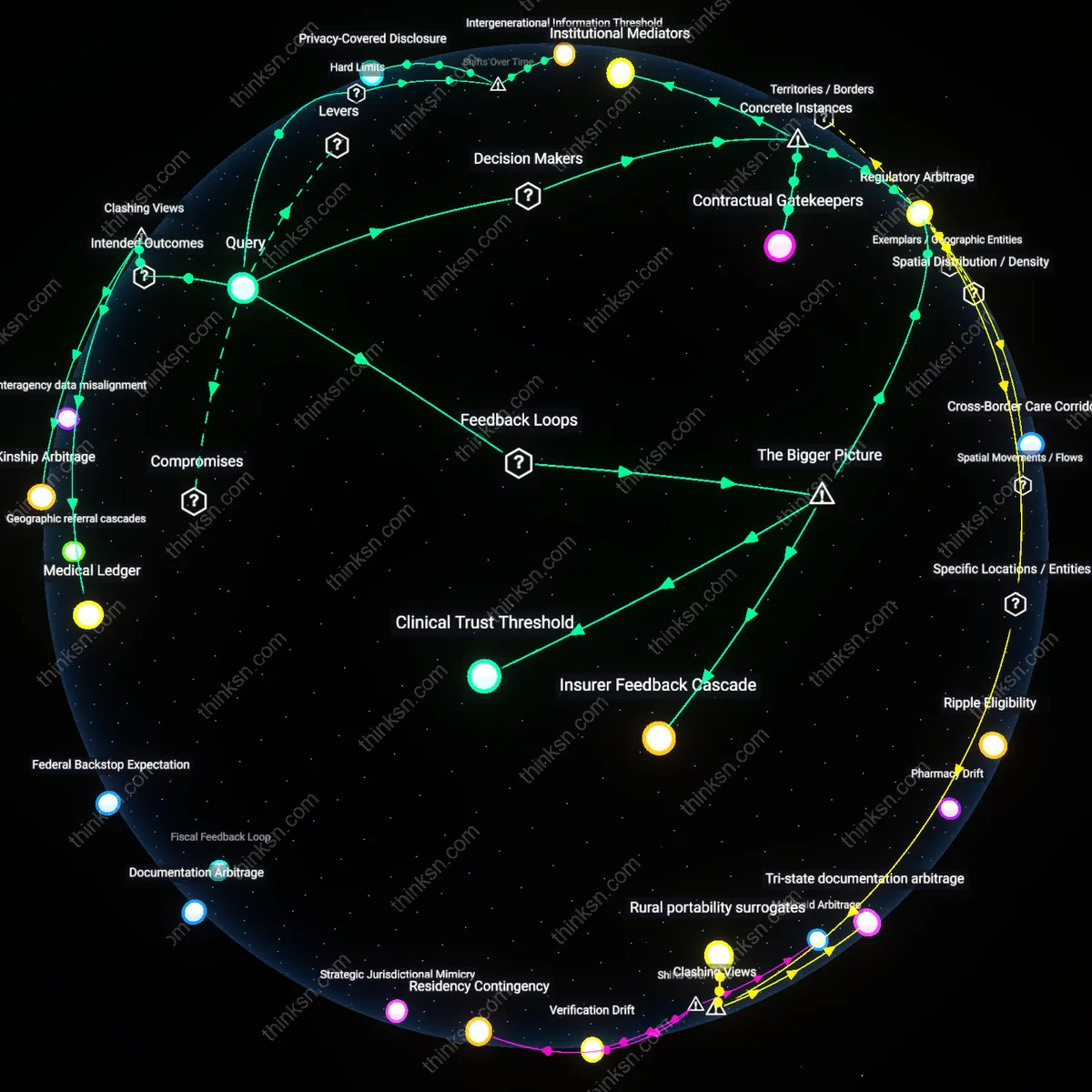
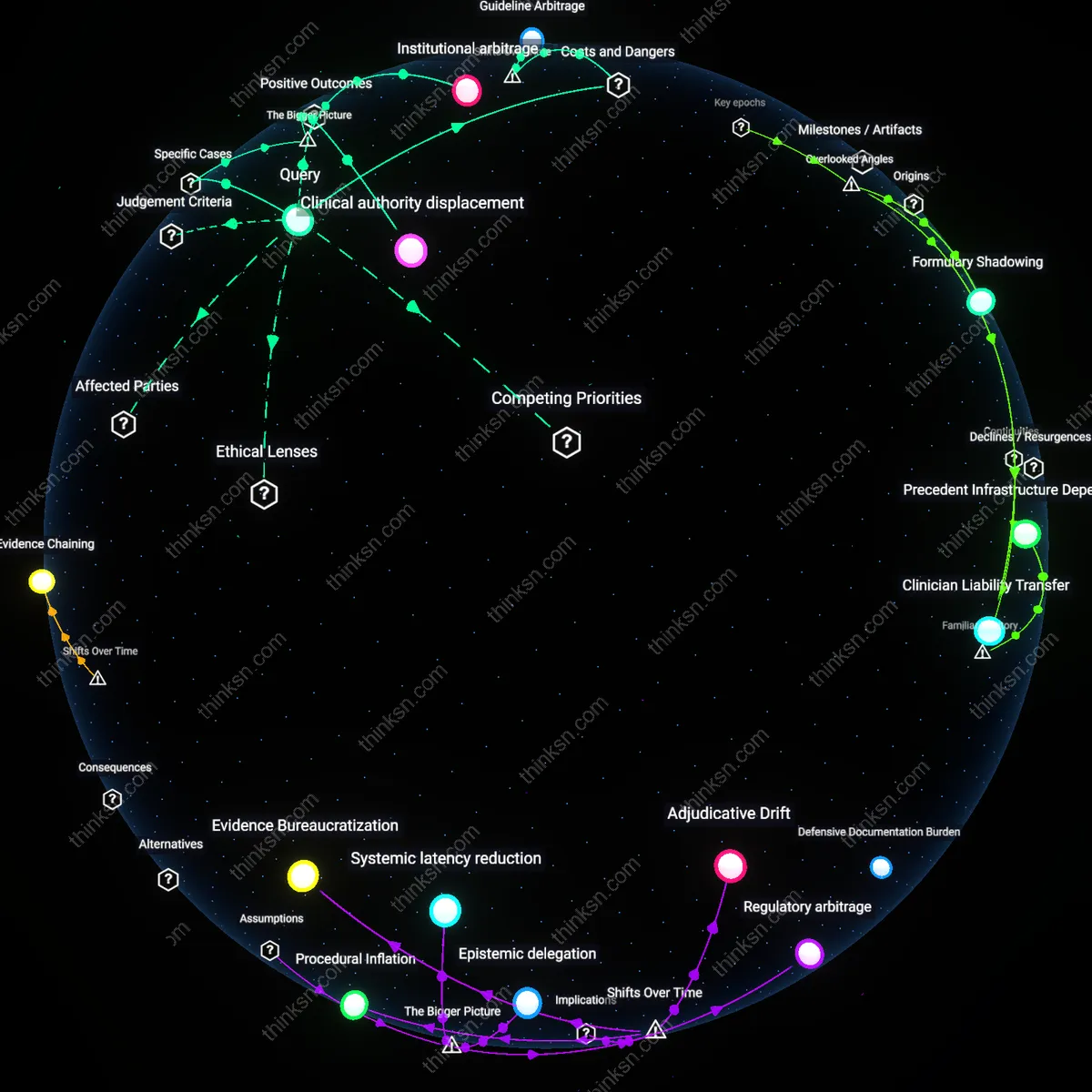
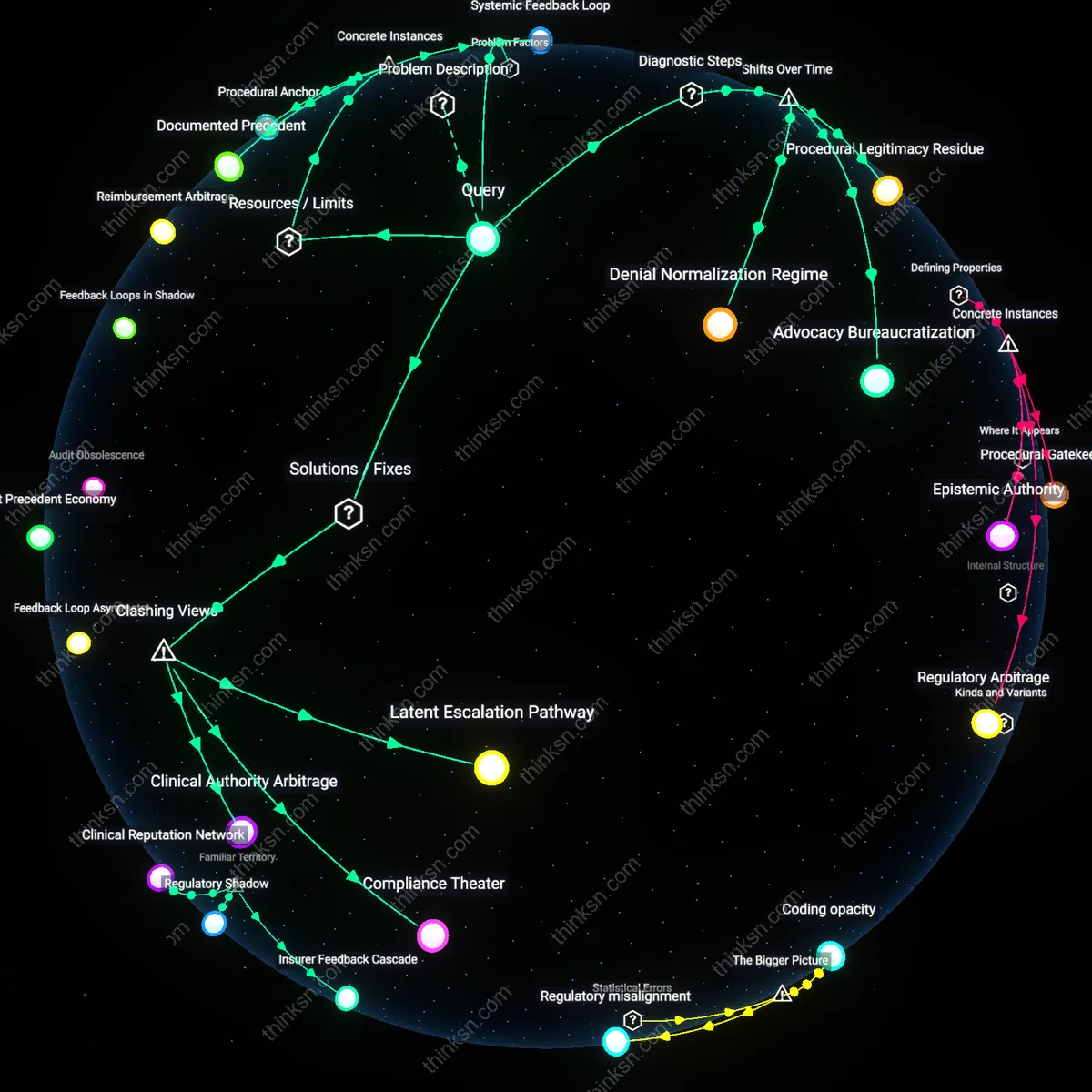
Jurisdictional Asymmetry
State shield laws block cross-state disclosure of patient records by establishing conflicting statutory immunities that prevent providers from sharing data without violating one jurisdiction’s privacy rules. Healthcare providers in border regions—like those in Vermont sharing records with Massachusetts hospitals—must navigate divergent legal standards, where one state’s shield law may immunize refusal to disclose records, while another treats non-disclosure as malpractice. The non-obvious consequence is that shield laws, though intended to empower providers, actually create legal gridlock, as no single interpretation of HIPAA preemption resolves these tensions, leading to under-sharing even when clinically necessary.
Clinical Risk Aversion
Providers withhold patient records across state lines because shield laws amplify perceived liability, making clinicians fear penalties regardless of actual compliance. In states like Texas, where shield laws protect physicians who refuse data sharing on conscience grounds, providers in neighboring New Mexico report delaying transfers of psychiatric records to avoid accusations of aiding prohibited care under Texas law. The core mechanism is anticipatory compliance—where the familiar association of legal protection paradoxically triggers defensive behavior, suppressing information flow not due to legal mandate but institutional caution shaped by politicized enforcement environments.
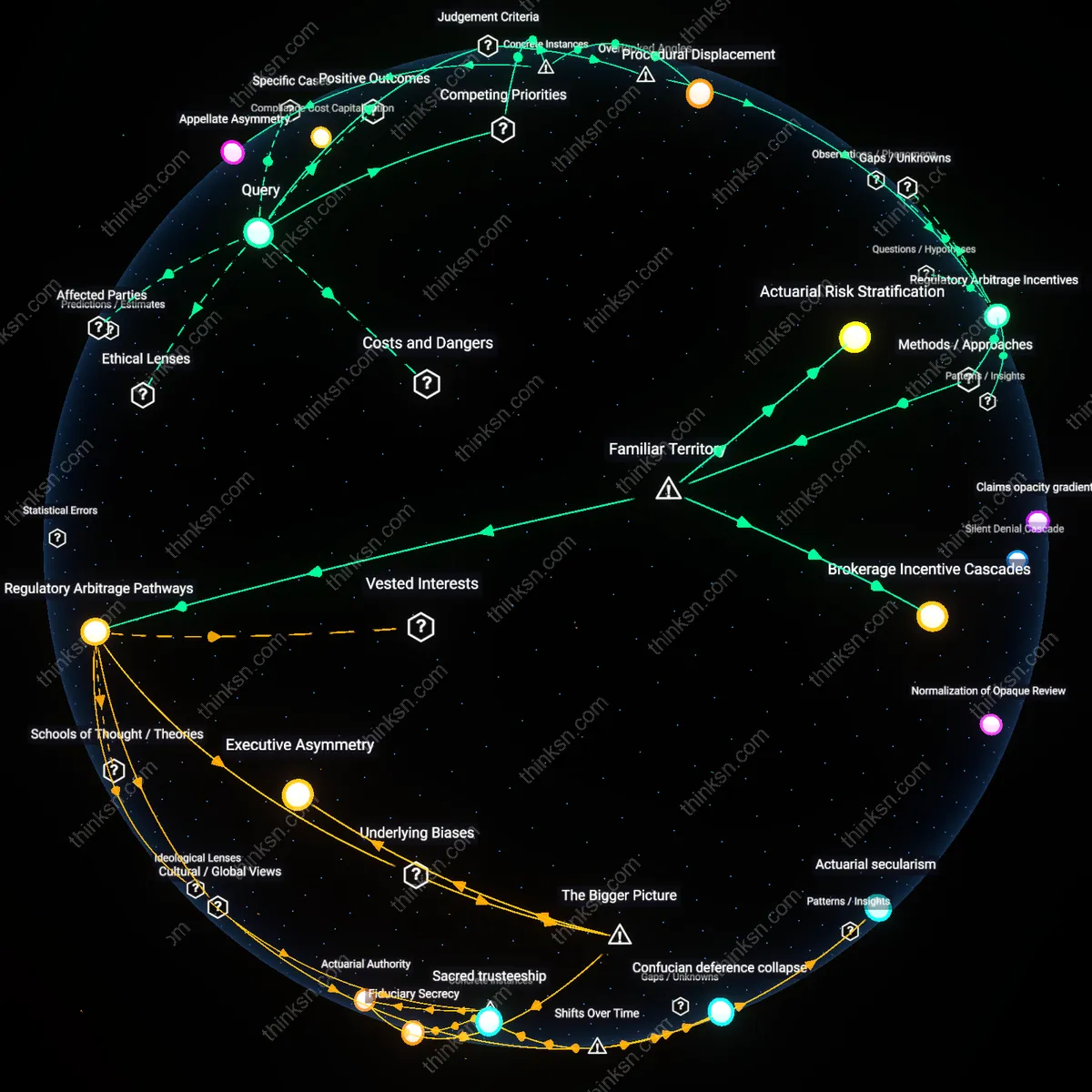
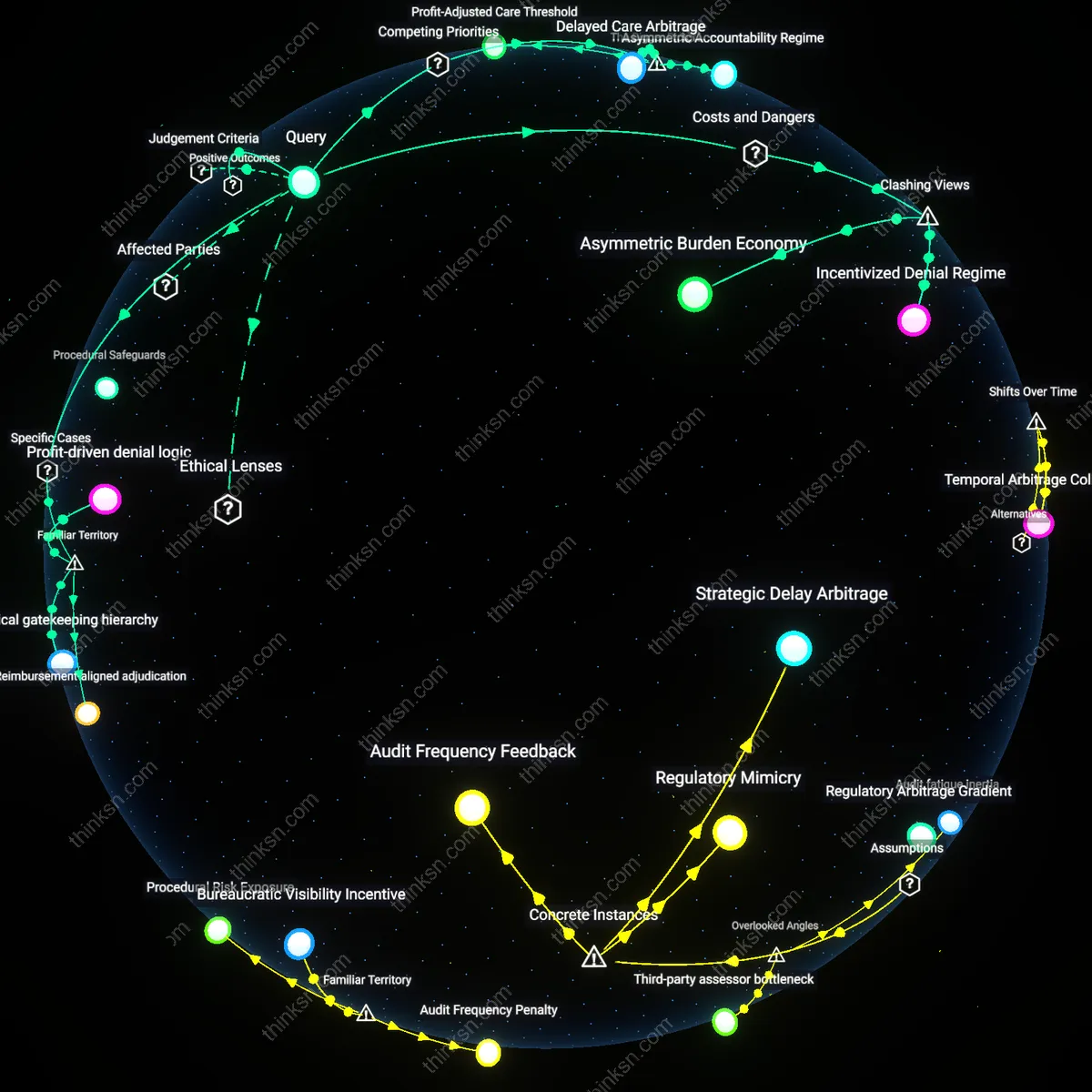
Regulatory Arbitrage
Health systems exploit gaps between state shield laws to design data-sharing protocols that selectively comply with the most permissive jurisdiction, centralizing record management in states like Colorado where shield laws include interoperability exceptions. National telehealth networks, such as those operated by Kaiser Permanente, route patient data through intrastate hubs to bypass stricter regimes in states like Idaho, where broad shield laws lack HIPAA harmonization. The underappreciated reality is that shield laws don’t uniformly restrict data sharing—they enable strategic forum shopping, turning regional legal variation into operational infrastructure for large providers, thus deepening inequities between system-affiliated and independent clinics.
Jurisdictional sequencing
State shield laws create a cascade effect by which the order in which states are entered into care networks determines data-sharing permissibility, regardless of federal interoperability mandates. Healthcare providers in states with stronger shield laws act as de facto gatekeepers, blocking downstream access to records even when subsequent states allow broader sharing, because initial documentation practices embed irreversible consent constraints. This sequencing effect is rarely acknowledged in policy discussions that assume jurisdictional rules apply simultaneously rather than temporally, fundamentally altering how data flows are structured across state lines.
Clinical transcription asymmetry
Shield laws alter the epistemic authority of medical transcriptionists, who in practice determine what becomes part of a shareable record by selectively excluding legally sensitive details in shielded states, thereby creating incomplete data packets that evade liability but compromise clinical utility. Because transcription workflows are governed locally yet inform national databases, this silent editing introduces invisible distortions that providers in receiving states cannot detect or correct, undermining the reliability of cross-border records without violating any explicit rule. The asymmetry arises from an unregulated labor tier whose decisions carry systemic consequences rarely considered in legal or technical compliance models.
Malpractice forum steering
Defensive documentation practices emerge in shield law states not only to comply with privacy rules but to preemptively shape the legal forum in which future malpractice disputes will be adjudicated, thereby influencing what information is preserved or omitted from transferable records. Providers omit elements that, while clinically relevant, could expose them to higher-risk jurisdictions’ tort standards, making shield laws not just privacy tools but strategic instruments in liability risk mapping. This mediating function of malpractice geography is absent from standard analyses focused on HIPAA or data use agreements, revealing how provider behavior is shaped more by anticipated litigation theaters than by privacy statutes themselves.
Litigation Overhang
Shield laws inadvertently elevate the risk of legal exposure in destination states by creating presumptive evidentiary value in civil discovery, which disincentivizes the release of records regardless of HIPAA compliance. For instance, a hospital in Texas releasing psychiatric records to a specialist in Florida may face depositions where the mere existence of shielded records triggers evidentiary motions under Florida’s liberal discovery rules, effectively weaponizing the confidentiality status of documents against the releasing provider. This reveals that privacy protection mechanisms are being exploited as litigation instruments, reversing their intended purpose.
Regulatory Secrecy
The belief that shield laws protect patient privacy is undermined by the fact that these statutes are primarily designed to shield institutions from administrative liability, not individuals from surveillance—this redirects the function of confidentiality toward bureaucratic insulation. For example, New York’s Public Health Law §18 protects substance use treatment records, but its enforcement prioritizes shielding state-certified facilities from OCR audits rather than empowering patients to control cross-state data flows. This exposes a system where privacy is a byproduct, not the objective, reframing inter-state data hesitation as institutional self-preservation.
Interstate Compliance Burden
State shield laws have intensified administrative complexity for multi-state providers since the 2010s, as electronic health record systems expanded across state lines. Systems like Epic deployed nationally after 2012 forced providers such as Kaiser Permanente and the Mayo Clinic to navigate conflicting state-level confidentiality mandates, particularly in mental health and substance use records, where states like California and New York maintain stricter protections than HIPAA requires. This created a de facto compliance cascade where legal risk avoidance became embedded in EHR architecture, revealing that technological scale-up amplified regulatory fragmentation instead of mitigating it—a shift from localized to systemic risk management.
Jurisdictional Arbitrage
After the 1996 HIPAA Privacy Rule, state shield laws began functioning as de facto competitive differentiators, particularly in telepsychiatry and addiction treatment networks operating across borders. Entities like the Hazelden Betty Ford Foundation adjusted patient data routing protocols post-2015, directing record flows through states with stronger statutory shields (e.g., Minnesota, Oregon) to preemptively insulate disclosures from external legal demands. This strategic use of legal geography marks a shift from passive compliance to active legal positioning, where the therapeutic mandate is increasingly filtered through jurisdictional advantage rather than clinical necessity.