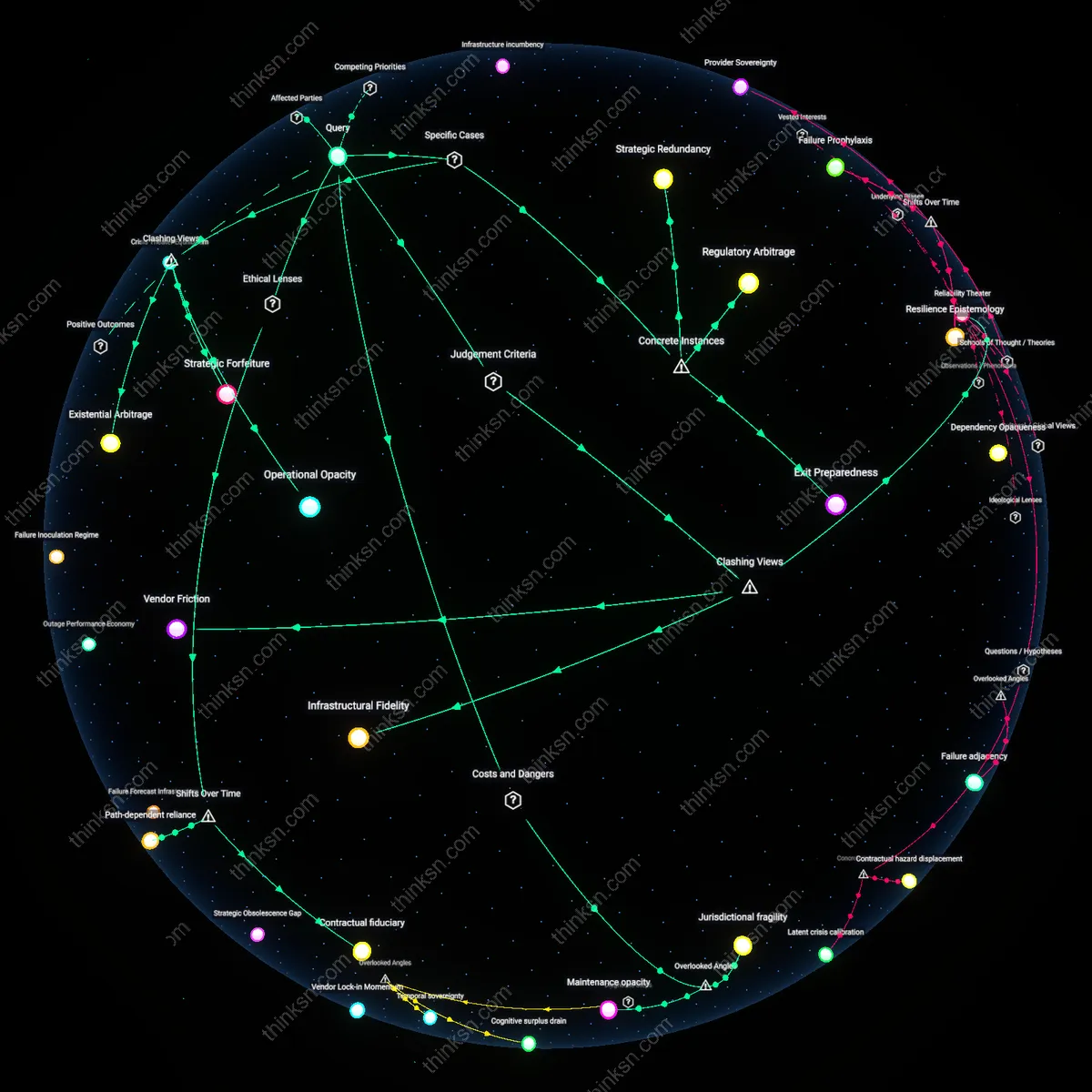
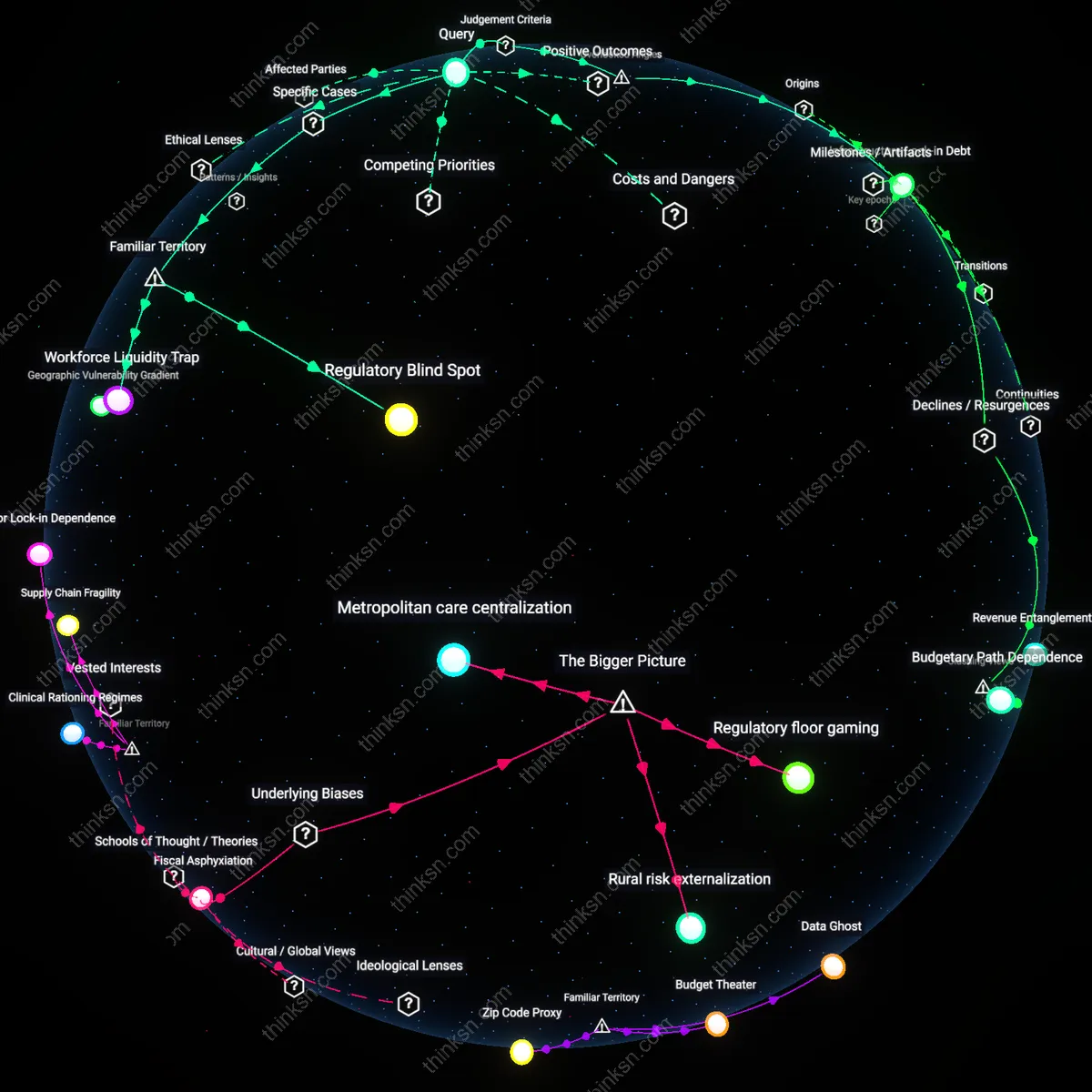
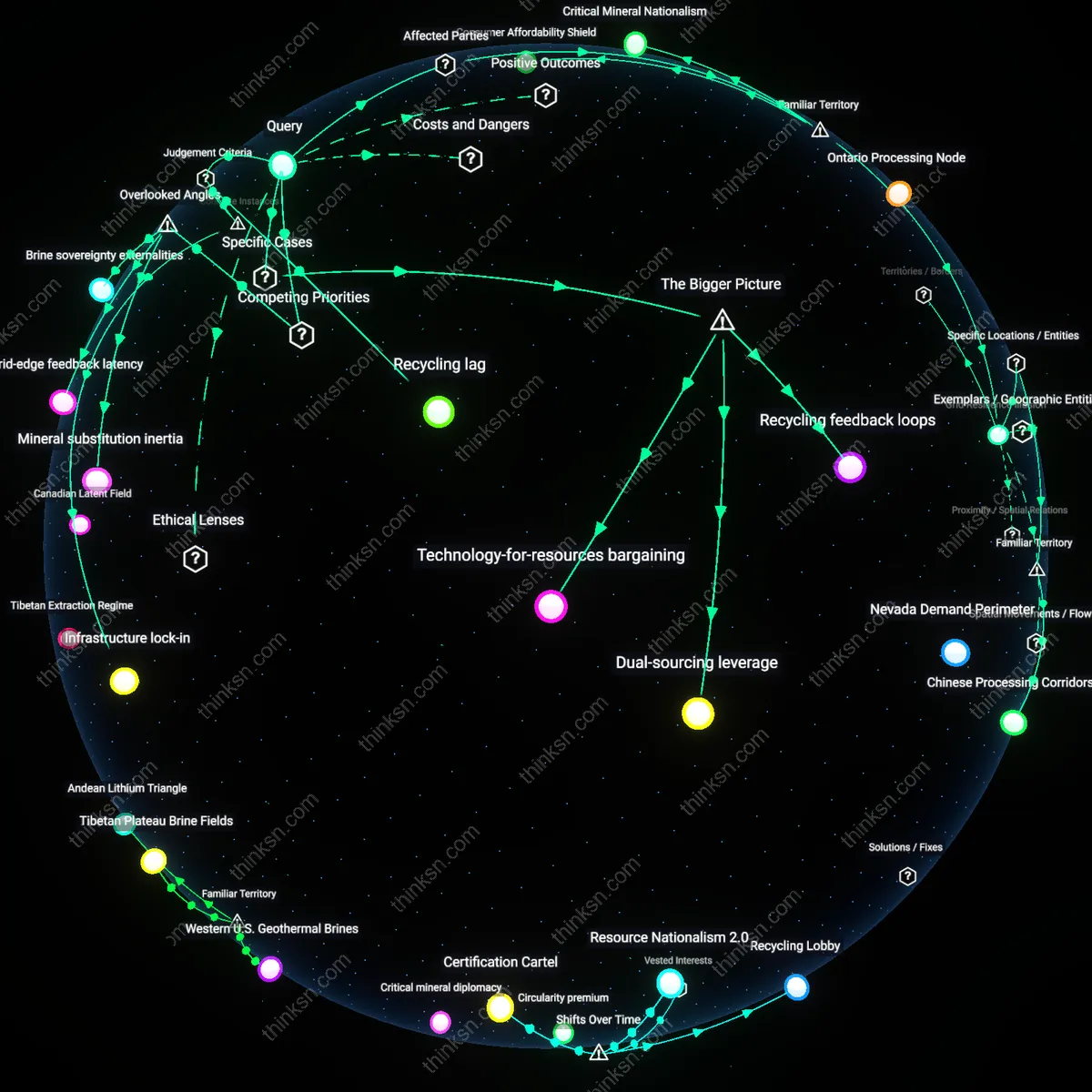
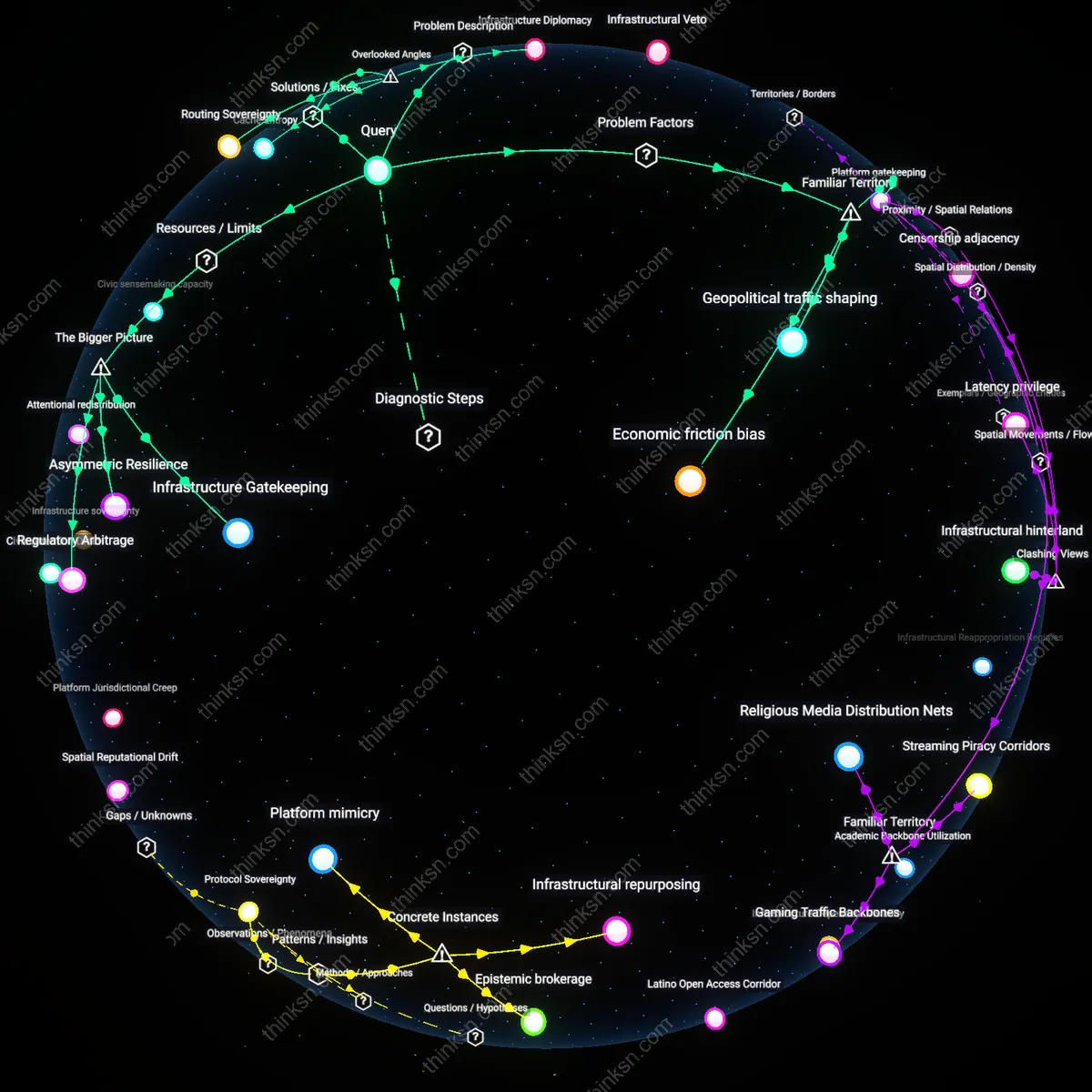
Critical Data on Monopolistic Clouds: Reliability vs. Lock-In Risk?
Analysis reveals 16 key thematic connections.
Key Findings
Regulatory arbitrage
Organizations can mitigate vendor lock-in risks by leveraging differential data sovereignty laws across jurisdictions to maintain operational flexibility. National data localization requirements, such as those in the EU’s GDPR or China’s PIPL, compel cloud providers to offer region-specific infrastructure, enabling firms to distribute critical data across providers in different legal regimes. This fragmentation creates de facto multi-cloud strategies driven not by technical preference but by compliance necessity, where the threat of noncompliance becomes a structural incentive to avoid overreliance on any single vendor. The underappreciated dynamic is that legal coercion, not strategic foresight, often forces organizations into resilient architectures.
Infrastructure incumbency
Organizations prioritize single-cloud reliance when the accumulated technical debt of integration creates irreversible dependencies on proprietary services like AWS Lambda or Azure Active Directory. Development teams become institutionally invested in vendor-specific abstractions, making migration not merely costly but cognitively disruptive, as internal expertise and tooling are co-constituted with the platform’s design logic. This creates a feedback loop where reliability becomes self-reinforcing through organizational learning, not objective superiority—what appears as rational trust in performance is often path dependence masked as optimization.
Infrastructural Fidelity
One should prioritize long-term data sovereignty by resisting dominant cloud providers even at the cost of short-term reliability, because true system resilience depends on the ability to audit, migrate, and govern data under one's own legal and technical standards. State agencies in the Global South, such as public health ministries relying on AWS for vaccine distribution records, often surrender operational transparency when proprietary APIs obscure data lineage and enforcement of local data laws becomes unenforceable—revealing that reliability without fidelity to institutional mandates is a form of systemic erosion. This undermines the principle of accountability by equating uptime with trustworthiness, while obscuring how infrastructure shapes public legitimacy.
Vendor Friction
One should deliberately adopt a dominant cloud provider to exploit its inertia as a strategic counterweight against internal organizational complacency, because the very stickiness of vendor lock-in forces enterprises to confront their own failure to build cross-functional data governance before crisis strikes. Large banks like Deutsche Bank that committed to Microsoft Azure for core banking data discovered that the high cost of exit catalyzed internal reforms—data standardization, API abstraction layers, and vendor negotiation units—that would have otherwise stalled under decentralized IT fiefdoms. This flips the moral principle of autonomy from avoidance of external control to deliberate entrapment as a discipline mechanism, exposing dependency as a perverse incentive for institutional maturation.
Reliability Theater
One should reject dominant cloud providers for critical data not on grounds of actual performance but because their near-perfect uptime metrics serve as a smokescreen for centralized failure modes that evade market correction, turning reliability into a public relations construct rather than an operational guarantee. When Google Cloud’s global authentication outage in 2023 took down emergency services relying on third-party communication tools, it revealed that reliability calculations ignore systemic interdependence, rewarding brand trust over redundant architecture. This destabilizes the economic principle of efficiency by showing that markets optimize for visible uptime, not latent fragility—thus producing 'reliability theater' where perception substitutes for resilience.
Jurisdictional fragility
One should reject sole reliance on a dominant cloud provider for critical data because legal jurisdiction over data becomes functionally meaningless when infrastructure spans politically unstable or legally ambiguous regions. Cloud providers distribute data across zones like Northern Virginia, Dublin, and Jakarta to optimize latency and redundancy, but these locations are embedded in divergent regulatory regimes with asymmetric enforcement capacities—creating blind spots when national laws conflict or collapse. Most risk assessments assume jurisdiction ensures accountability, yet when a cloud operator legally resides in the U.S. but stores encrypted shards in a country with transient governance—such as a data center in a Special Economic Zone vulnerable to abrupt regulatory revocation—the effective authority over data vanishes. This fragility is rarely modeled because dependency maps obscure the political temporality of hosting locations, mistaking geographic redundancy for legal resilience.
Maintenance opacity
One should avoid entrusting critical data to a dominant cloud provider because their internal maintenance protocols generate unreportable failure modes that bypass auditing standards and regulatory scrutiny. When providers like AWS conduct rolling updates on firmware, hypervisors, or network routing tables across regions, these actions are categorized as routine operations and excluded from incident reporting, even when they contribute to cascading degradations such as the 2021 CloudFront outage. The opacity arises not from intentional concealment but from the classification boundaries used in compliance frameworks like ISO 27001, which treat maintenance as a normal operational state rather than a risk vector. This blind spot means that organizations cannot anticipate systemic fragility introduced by the provider’s own invisible change velocity—something most due diligence checklists ignore because they focus on uptime metrics, not the hidden turbulence of continuous internal reconfiguration.
Skill atrophy
One should limit dependence on a dominant cloud provider because long-term use systematically erodes an organization’s ability to execute data recovery under conditions of provider-initiated suspension or degradation. When teams rely on managed services like Azure Backup or Google’s Snapshot Scheduler, they delegate not just storage but the cognitive schema for data integrity management, leading to the erosion of low-level expertise in file system journaling, tape restoration, or block-level copying. This atrophy becomes catastrophic when access is interrupted not by outage but by policy—such as a sudden Terms of Service enforcement that freezes accounts without technical failure, leaving teams unable to reconstruct workflows using alternative tools. The risk is overlooked because standard continuity planning assumes technical access persists during crises, not recognizing that the deepest dependency is not on infrastructure but on the maintenance of organizational technical memory, which cloud abstraction actively disassembles.
Contractual fiduciary
One should use a dominant cloud provider for critical data only when contractual obligations are structured to enforce continuous accountability, as seen in post-2018 EU GDPR-aligned public sector procurement where cloud vendors are bound by data stewardship clauses that legally approximate fiduciary duties. This mechanism emerged after the 2013 Snowden revelations exposed systemic vulnerabilities in U.S.-based infrastructure, triggering European institutions to shift from trust-based vendor relationships to enforceable legal frameworks that treat data hosting as a public trust function. The non-obvious implication is that vendor lock-in is no longer purely a technical or economic concern but a governance failure when providers are not subject to fiduciary-grade duties, revealing a new hybrid role—neither pure vendor nor public agency—that the law now compels through conditional reliance on dominant platforms.
Path-dependent reliance
Organizations should accept vendor lock-in from dominant cloud providers when their operational continuity depends on real-time integration with emergent AI/ML tooling ecosystems, a condition solidified after 2023 when AWS, Azure, and GCP began bundling proprietary models with data storage, making migration not just costly but cognitively infeasible. This shift marks a break from earlier cloud eras where lock-in was financial or contractual, to a new phase where dependence is epistemic—the very knowledge work of the organization becomes shaped by the provider’s evolving architecture. The overlooked consequence is that reliability now presupposes acceptance of irreversible integration, revealing path-dependent reliance as a structural condition of contemporary digital governance, where choice is retroactively erased by the tempo of infrastructural evolution.
Strategic Redundancy
NASA’s Mars Rover missions should use dominant cloud providers for critical data because mission-specific hybrid architectures mitigate vendor lock-in while ensuring reliability through geographically isolated backup systems. NASA partners with AWS for real-time telemetry processing but maintains parallel data streams via the Deep Space Network and on-premise high-assurance storage at JPL, creating a redundancy model where cloud scalability supports burst processing during Mars-Earth communication windows, yet core archival remains under institutional control. This hybrid approach reveals that lock-in risk is not inherent to cloud reliance but depends on whether the organization retains sovereign data pathways and format portability, a distinction often overlooked in enterprise cloud adoption debates.
Regulatory Arbitrage
Deutsche Bank chose AWS for its core trading platform infrastructure in 2018 only after the European Commission enforced GDPR-compliant data residency clauses that constrained AWS’s default global data routing, thereby reducing lock-in risk through regulatory constraint rather than technical design. The bank leveraged EU sovereignty requirements to negotiate isolated regional endpoints and data exit protocols, effectively using supranational regulation as a counterbalance to AWS's structural dominance in the financial sector. This case shows that vendor lock-in can be externally mitigated when jurisdictional authority compels cloud providers to offer escape mechanisms, a dynamic rarely considered in purely market-driven IT governance models.
Exit Preparedness
Spotify’s migration from Google Cloud to a multi-cloud and bare-metal hybrid in 2020 succeeded because the company had systematically instrumented its infrastructure with open telemetry, containerization, and internal abstraction layers before full cloud dependency emerged. By treating cloud provider APIs as transient rather than foundational, Spotify maintained functional interoperability even as it scaled on GCP, demonstrating that lock-in is not a function of reliance but of architectural rigidity. The underappreciated insight here is that exit capability must be engineered proactively during initial adoption, not negotiated retroactively—a discipline visible in few organizations despite its decisive impact on long-term strategic freedom.
Strategic Forfeiture
Organizations strengthen long-term bargaining power by intentionally accepting short-term vendor lock-in to exploit future regulatory interventions. The U.S. Department of Defense’s adoption of AWS for its classified JEDI contract amplified public scrutiny, turning a proprietary dependency into a political liability for the vendor and enabling forced interoperability through legislative pressure, as later seen in the 2023 Federal Cloud Competition Act. This reveals that apparent technological entrapment can be weaponized into leverage when scale attracts regulatory correction, upending the assumption that lock-in is inherently disempowering.
Operational Opacity
Organizations preserve autonomy not by avoiding single providers but by obscuring critical dataflows behind proprietary abstractions only their internal teams understand. Palantir’s deployment at NHS England during the pandemic relied entirely on Google Cloud, yet the firm’s custom data ontology and unshared transformation logic made migration practically impossible even for the host institution. This inversion—where lock-in is sustained not by the vendor’s design but the client’s obscurantism—challenges the view that vendor dependency originates primarily from infrastructure dependency.
Existential Arbitrage
Organizations choose single providers not for reliability, but to make discrete, high-stakes wagers on vendor survival as a form of strategic concentration. When SpaceX selected Amazon Web Services for Starlink telemetry over hybrid alternatives, it accepted long-term lock-in risks in exchange for an implicit bet that AWS would remain operationally viable and politically tolerable through decades of orbital missions. This frames cloud choice as a Darwinian selection mechanism—where locking in becomes rational precisely because the sheer improbability of surviving as a dominant provider signals future resilience, subverting diversification orthodoxy.