Verification hierarchies
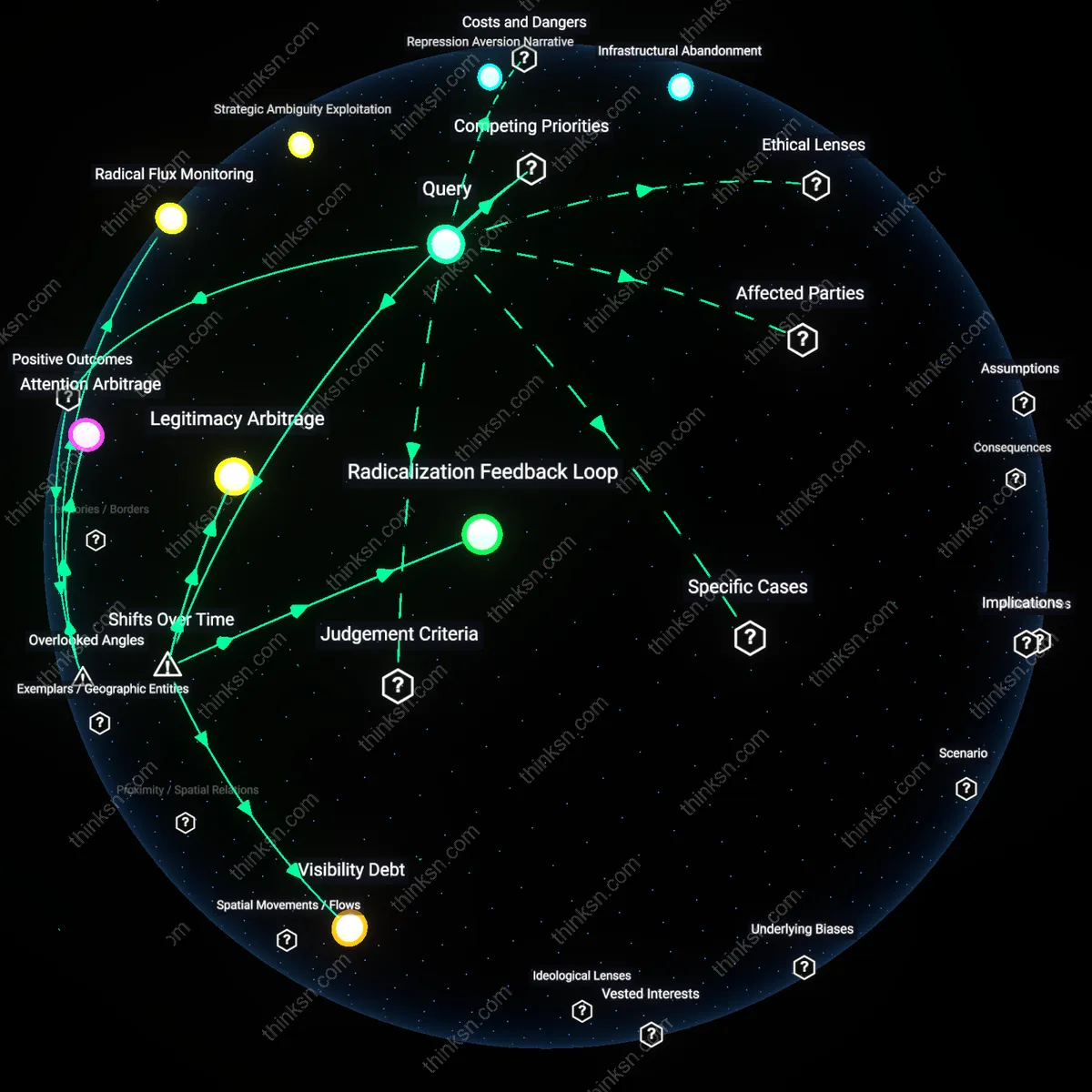
Jurisdictions with robust anti-money laundering frameworks would increasingly treat digital identity interoperability as conditional upon replicating their own identity verification standards, leading to a stratified global system where only states emulating Western KYC/AML regimes gain recognition. This shift began in earnest after the 2019 FATF guidance expanded to cover virtual assets, elevating identity assurance from a domestic compliance task to a geopolitical prerequisite for financial inclusion—what was once a technical standard thus became a boundary of legitimacy, excluding entire regions from formally recognized digital economies not because they lacked technology, but because they prioritized accessibility or privacy over forensic traceability.
Identity sovereignty
Countries resisting external imposition of verification norms would begin to frame digital identity as an assertion of state autonomy, transforming what appeared to be a technical compliance issue into a constitutional struggle over who controls the recognition of personhood. This repositioning crystallized during the 2022 debate over India's Aadhaar-based digital rupee model, when Western regulators questioned its compliance with 'risk-based approaches,' prompting Global South states to organize through the G77 to treat identity design as a domain of postcolonial self-determination—revealing that the current phase of digital identity politics is less about financial integrity than about the re-nationalization of identity in response to decades of harmonization pressure.
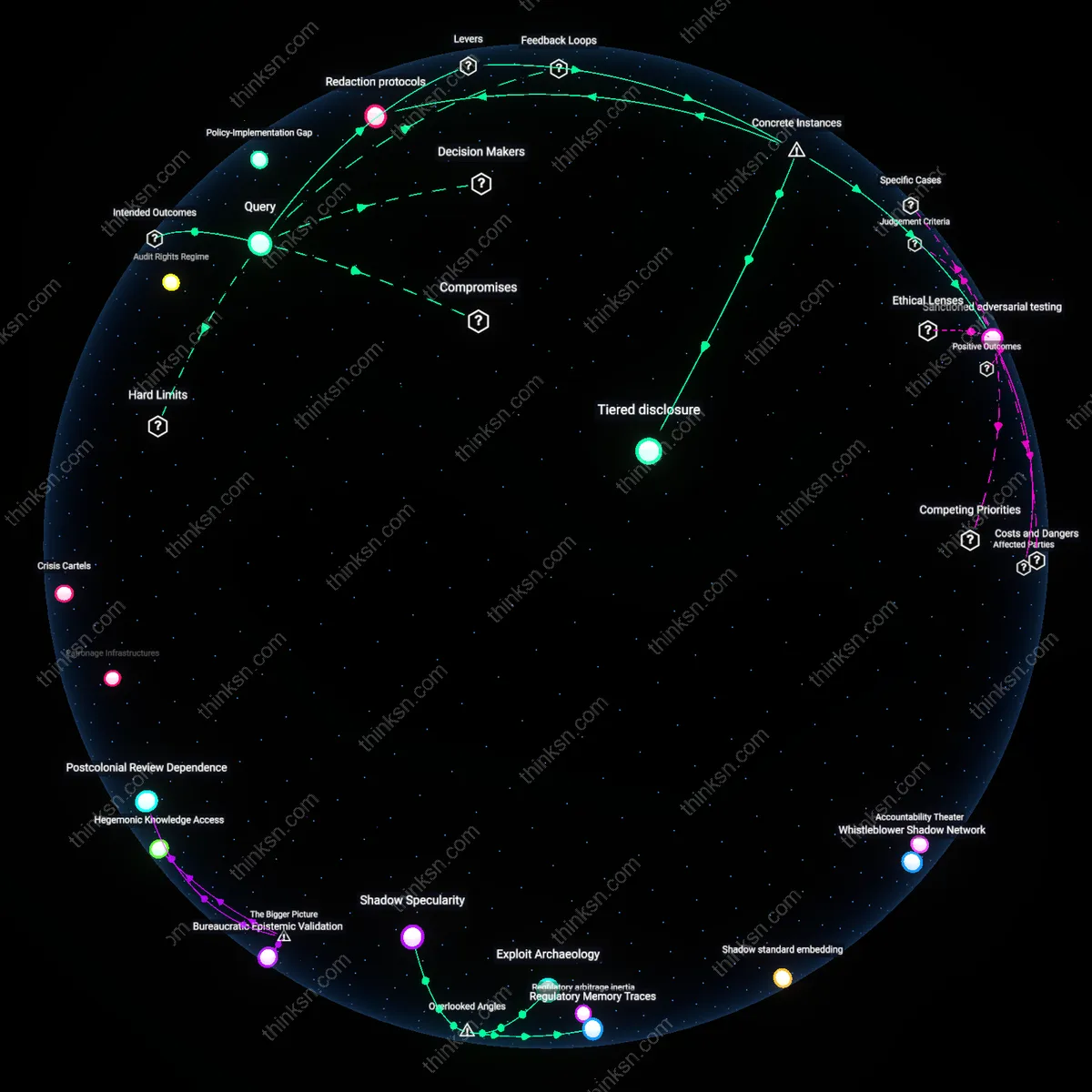
Exclusionary inclusion
By limiting recognition to jurisdictions enforcing state-monitored identity enrollment, liberal democracies inadvertently create a tiered digital citizenship where formal inclusion into the global financial system depends on prior subjection to surveillance-intensive verification, a regime that emerged clearly during the EU's 2023 DORA implementation when member states began conditioning digital ID reciprocity on third-party audit rights over biometric databases—thereby turning financial integrity into a mechanism that expands the extraterritorial reach of surveillance norms under the guise of transparency, a development rarely acknowledged because it is masked by progressive rhetoric.
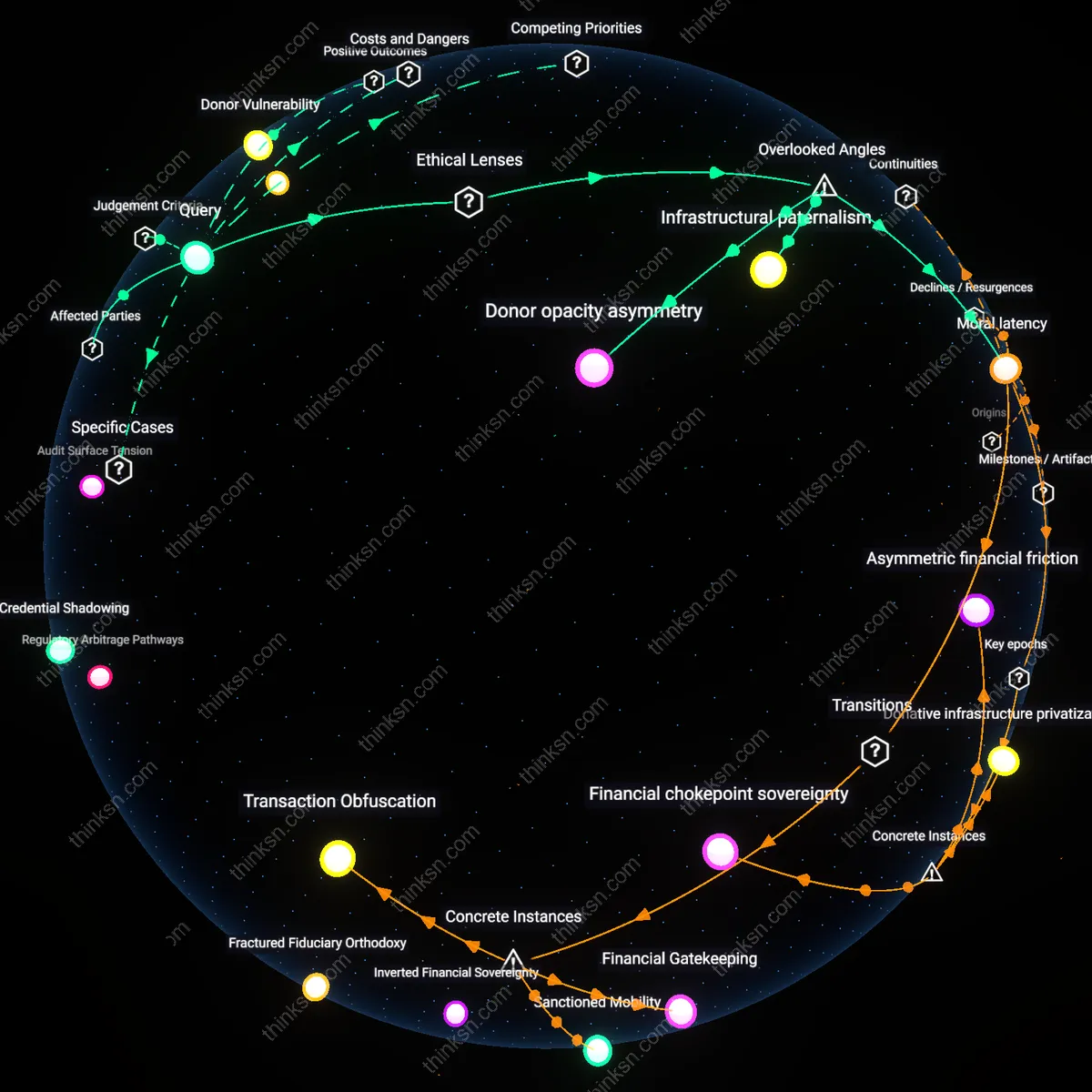
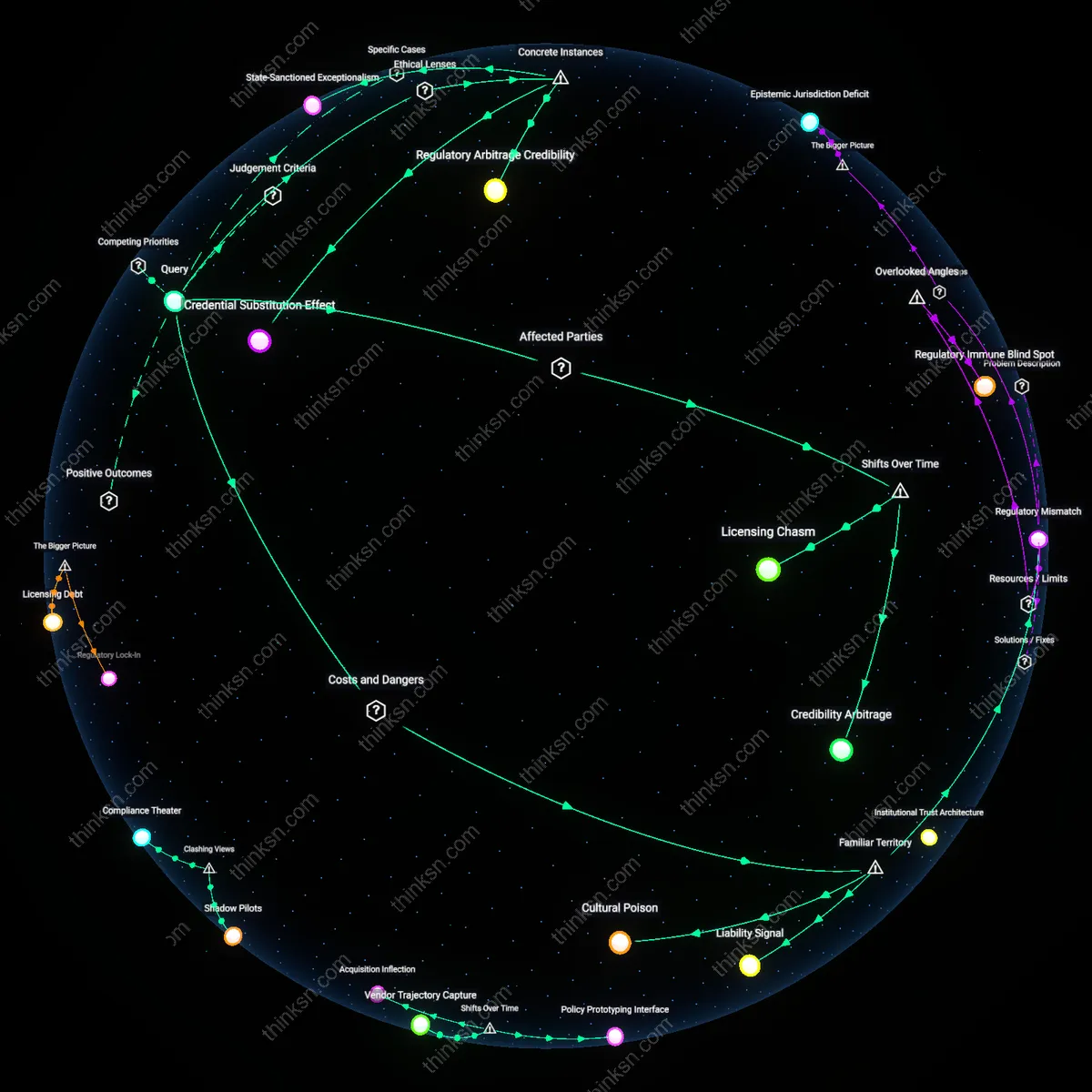
Regulatory Arbitrage Squeeze
Digital identity interoperability restricted to jurisdictions with strict AML compliance would trigger a regulatory arbitrage squeeze, as fintech firms and crypto platforms shift operations to compliant hubs like Estonia or Singapore to retain access to global financial rails. This concentration amplifies systemic risk within those hubs, as their identity infrastructures become critical chokepoints controlled by public-private alliances between national regulators and identity providers. The non-obvious consequence is not enhanced security but the emergence of de facto identity oligopolies, where a few verified jurisdictions disproportionately govern cross-border trust flows.
Asymmetric Interoperability Trap
If only strictly verified digital identities are recognized across borders, a two-tier identity system crystallizes, wherein Global North jurisdictions act as gatekeepers to digital legitimacy, locking out state-backed ID systems from the Global South regardless of their technological sophistication. This creates an asymmetric interoperability trap, where countries like India or Kenya face exclusion despite robust biometric systems because their legal frameworks diverge from Western AML norms. The key dynamic is standard-setting power masquerading as technical compliance, revealing how legitimacy in digital identity is less about verification rigor and more about alignment with geopolitical norms enforced through financial access.
Private Identity Cartels
Enforcing recognition solely on identities from high-compliance jurisdictions would incentivize private sector coalitions—such as SWIFT-participating banks and regulated stablecoin issuers—to form closed identity verification networks that bypass state systems altogether. These private identity cartels would operate through interoperable zero-knowledge proof systems, granting access only to users whose credentials originate from pre-approved registries, effectively privatizing the gatekeeping function of state sovereignty. The underappreciated shift is not state fragmentation but the quiet transfer of identity legitimacy from governments to consortiums of regulated financial intermediaries wielding technical standardization as exclusionary power.
Jurisdictional leverage
Digital identity recognition limited to strict-verification regimes would empower early-adopter states to set de facto global standards, as seen when Estonia’s e-Residency program enabled non-citizens to establish verifiable digital identities recognized by EU financial institutions, compelling smaller economies to align verification norms or lose cross-border service access. The mechanism operates through interoperability asymmetry—where first-mover jurisdictional frameworks become prerequisites for integration into global finance. The underappreciated consequence is that sovereignty in digital identity is not equally distributive; it creates a hierarchy where administrative capacity becomes geopolitical leverage, not just technical policy.
Verification Arbitrage
Countries with strong anti-money laundering laws would incentivize the rise of verification arbitrage, where identity providers in loosely regulated jurisdictions offer near-compliant facade verifications that mimic strict protocols without genuine scrutiny. This occurs because digital identity ecosystems reward interoperability with high-trust zones, enabling low-cost replication of verification signals without the infrastructure of real identity assurance. The non-obvious mechanism here is not evasion per se, but the creation of a shadow market for synthetic compliance that exploits the assumption that technical conformance implies institutional rigor, thereby degrading the integrity of the entire transnational verification network.
Identity Cartelization
Recognition constraints would push compliant jurisdictions to form closed coalitions that mutually validate only their own digital identities, effectively creating identity cartels like the Nordic e-Identity Partnership or EU’s eIDAS expanded to exclude external providers. These blocs would wield disproportionate influence over global digital access not through overt exclusion, but by setting de facto identity standards that smaller or less resourced nations cannot meet, even if they have robust verification systems. The overlooked dynamic is how interoperability privileges institutional familiarity over technical merit, privileging entrenched bureaucracies and disadvantaging sovereign systems with functionally equivalent but structurally different verification regimes.
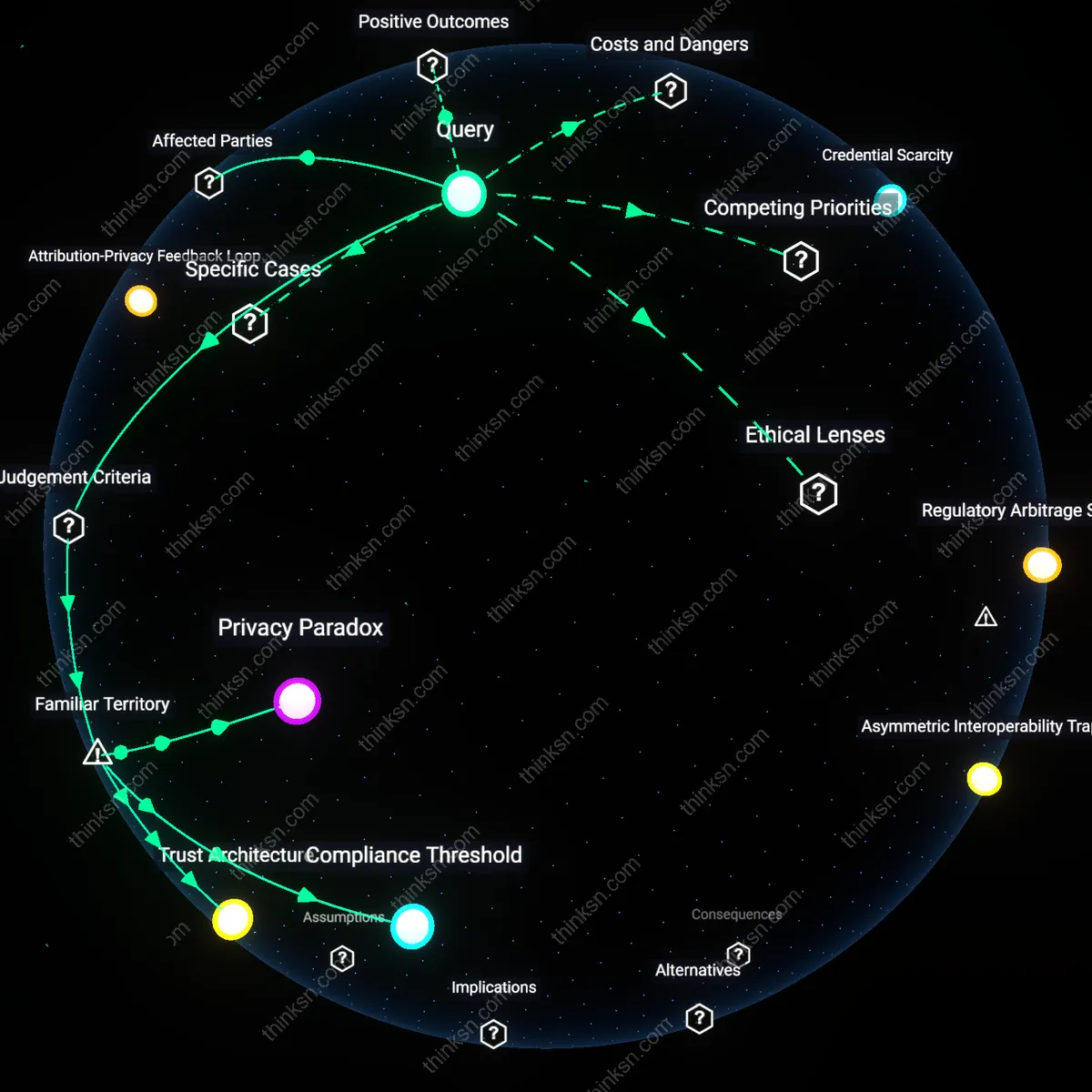
Credential Scarcity
Limiting recognized digital identities to a narrow set of jurisdictions would create artificial credential scarcity, transforming verified identities into a geographically stratified digital commodity controlled by a few regulatory gatekeepers rather than a widely accessible infrastructure. This scarcity would empower private intermediaries—such as global cloud platforms or fintech orchestrators—that can aggregate and broker access to these credentials, effectively becoming de facto identity oligopolists. The underappreciated shift is from state-led identity governance to market-mediated identity gatekeeping, where access to legality in global finance depends less on personal authenticity than on proximity to a handful of credential-issuing hubs.