Is Linking LinkedIn to Corporate SSO Worth Your Privacy?
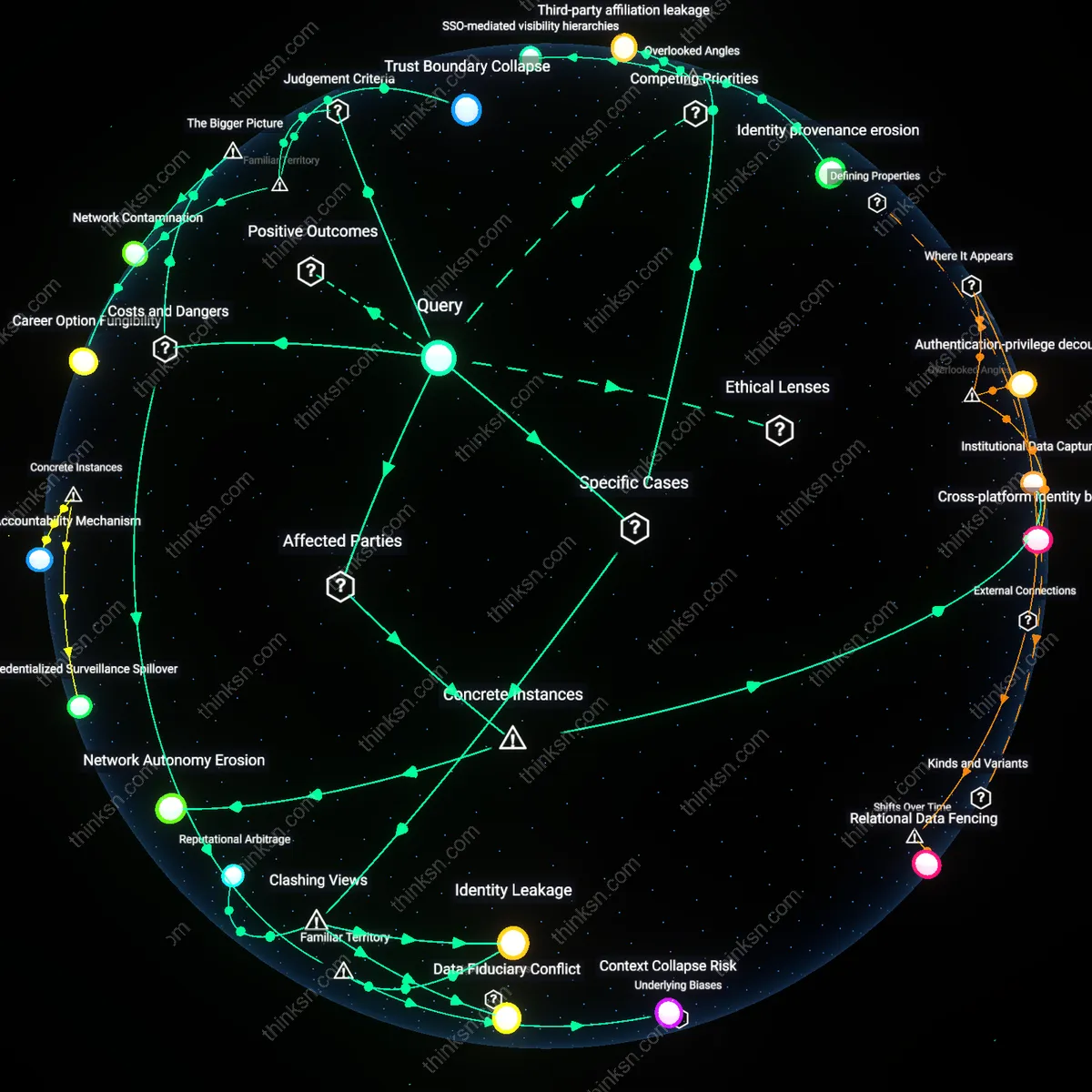
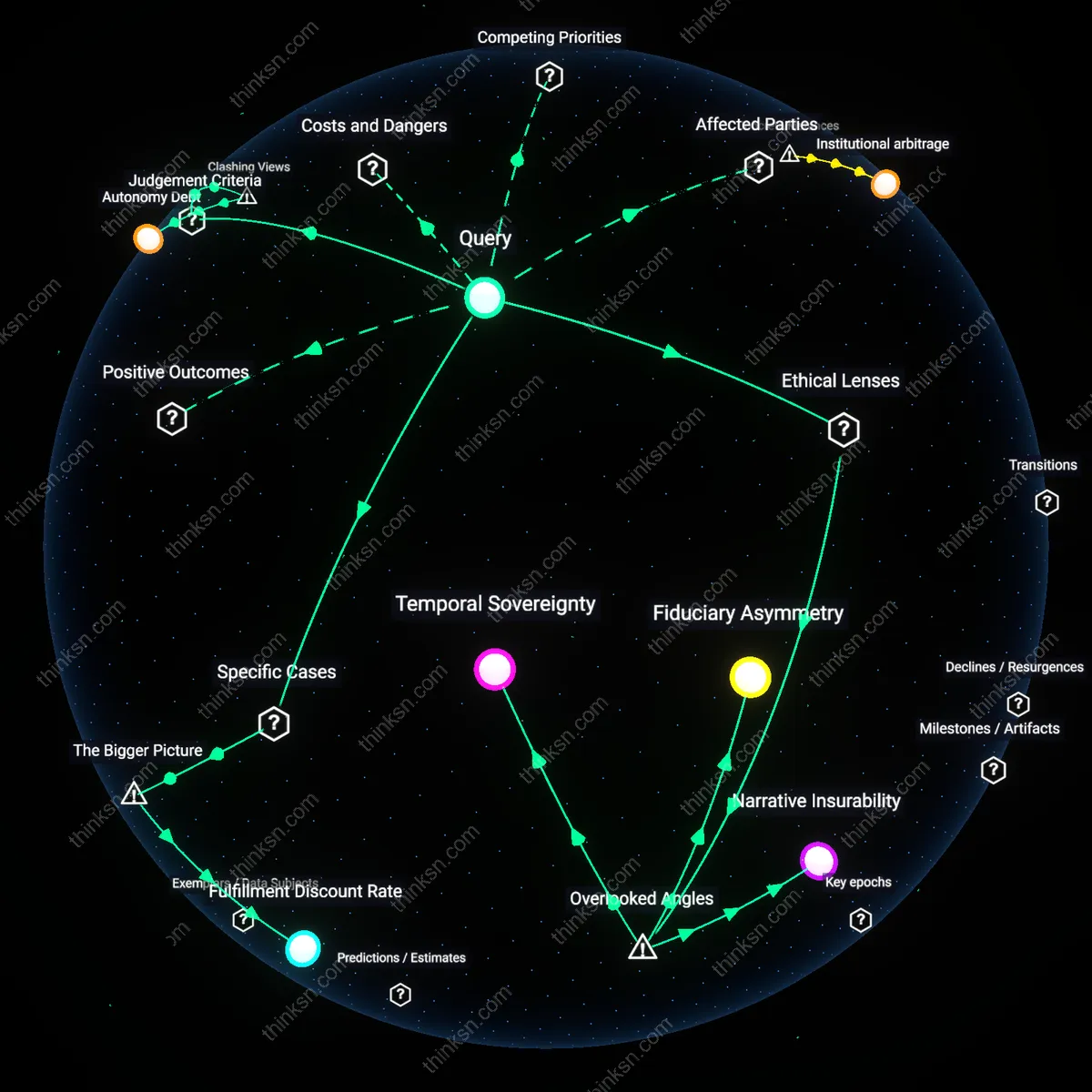
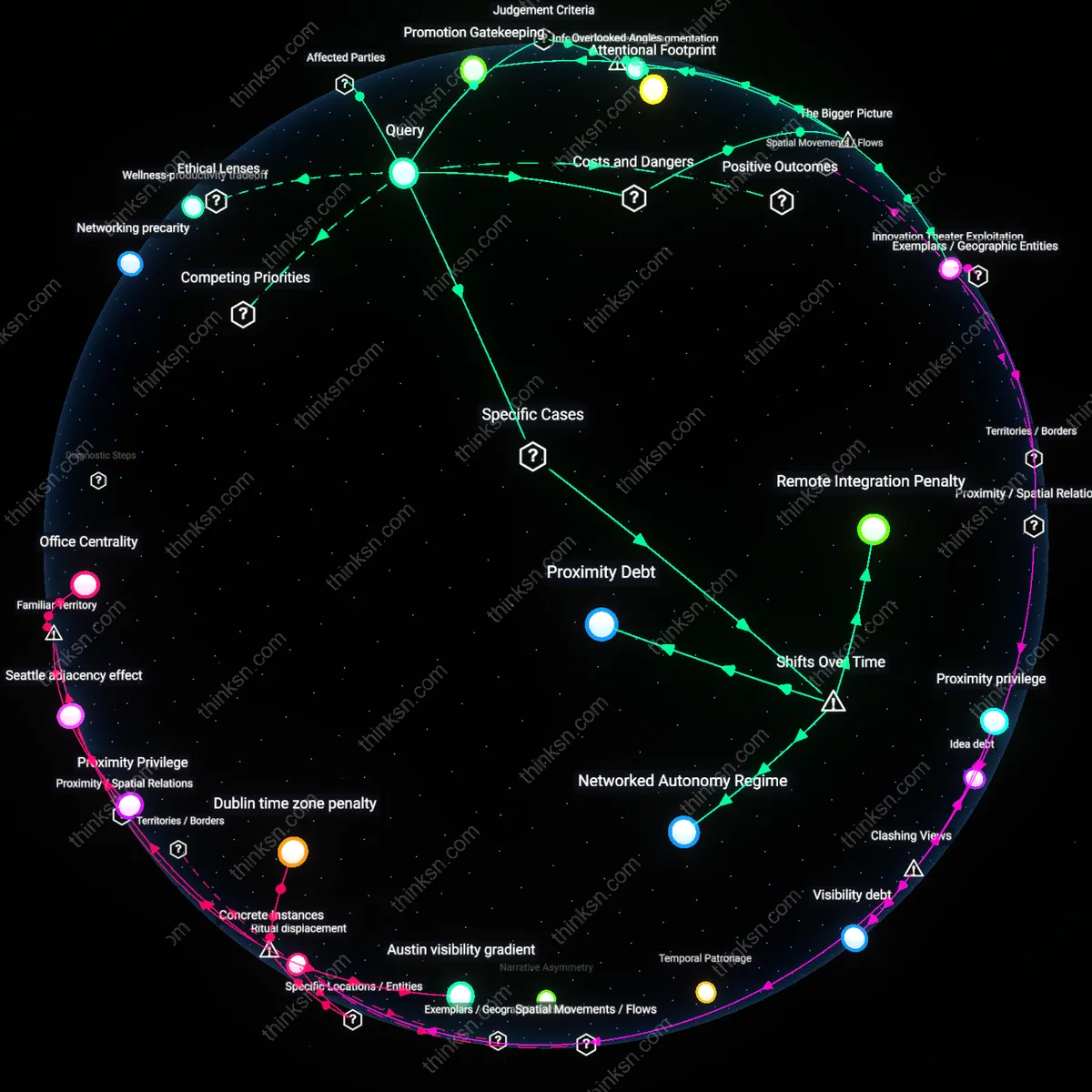
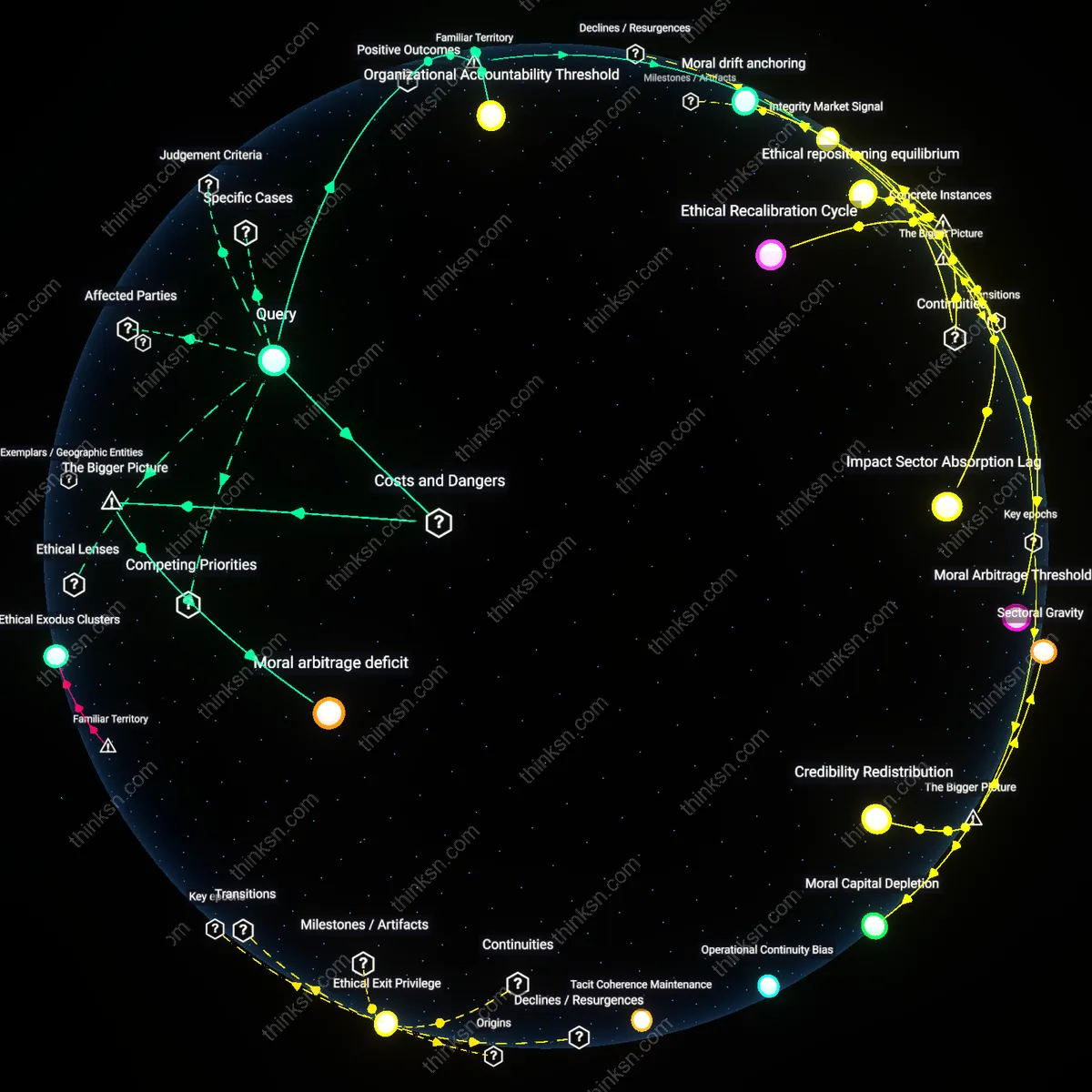
Analysis reveals 14 key thematic connections.
Key Findings
Institutional Data Capture
Connecting LinkedIn to corporate SSO enables employers to systematically archive employee professional networks as institutional assets, as seen when Deloitte integrated LinkedIn with its internal People Analytics platform in 2018, allowing HR to map external client relationships and collaboration patterns across consultants. This mechanism transforms personal professional data into a surveillable, analyzable resource under employer control, revealing that convenience-driven integration can silently shift ownership of external career capital from individuals to organizations—what appears as seamless access is, in practice, infrastructural assimilation of personal networks into corporate intelligence systems.
Network Autonomy Erosion
Employees who link their LinkedIn profiles to corporate SSO may unknowingly forfeit control over how their external connections are categorized and used, exemplified by the 2020 incident at Siemens, where automated SSO-linked systems tagged employee connections as 'strategic partners' or 'competitor affiliates' in internal dashboards without consent. This classification system, driven by algorithmic interpretation of contact lists, altered how employees were assigned projects based on perceived affiliations, exposing how integration can weaponize personal networks through bureaucratic dataflows—not through malice, but through automated categorization made invisible by seamless login design.
Trust Boundary Collapse
Professionals should resist connecting LinkedIn to corporate SSO because it erodes the separation between personal professional identity and organizational surveillance. The integration merges authentication systems that are meant to serve distinct domains—one governed by individual career agency, the other by employer-controlled access protocols—creating a pathway for passive data leakage through login metadata, connection graphs, and behavioral tracking. This collapse is underappreciated because convenience masks the erosion of boundary integrity, making it seem like a neutral technical choice when it substantively recalibrates control over professional visibility.
Institutional Data Asymmetry
Professionals should weigh SSO integration by recognizing that employers gain structural visibility into external networks while offering no reciprocal transparency. Corporate systems can log access patterns, connection overlaps, and off-hours engagement, turning LinkedIn into a de facto talent intelligence feed without explicit consent. The imbalance is rarely acknowledged in onboarding processes, where the language of 'single sign-on' deliberately obscures the directionality of data flow—favoring employer insight over employee informational parity.
Career Option Fungibility
Professionals should treat SSO linkage as a constraint on future job mobility because employer-authenticated access creates a detectable trail that may signal disloyalty or premature job-seeking when they interact with recruiters or competitors. The corporate authentication timestamp becomes an implicit loyalty monitor, altering how professional engagement is interpreted within the current organization. This shifts the perceived neutrality of networking from a standard career practice to a potentially sanctioned act, reducing the freedom to explore options without institutional exposure.
Identity Leakage
Connecting LinkedIn to corporate SSO exposes employees’ external professional identities as readable data streams to employer-controlled systems. Employers gain silent access to network logs, connection patterns, and engagement behaviors—data that was previously fragmented or self-curated—creating a permanent, searchable audit trail of career mobility intentions. This transforms casual networking into observable performance metadata, where associating with recruiters or competitors on LinkedIn can be algorithmically flagged as flight risk without context. The danger lies not in data breach but in normal, intended system operation—compliance with HR tech infrastructure quietly overrides individual privacy expectations.
Behavioral Enforcement
Corporate SSO integration weaponizes convenience to condition professionals into self-policing their external affiliations. Once login systems blend work identity with public platforms, employees begin to treat LinkedIn as a de facto extension of internal HR monitoring, avoiding connections or content that might appear disloyal—even outside work hours. The mechanism mirrors digital panopticon dynamics seen in surveillance capitalism, but here it is enabled not by advertising but by identity convergence. People assume this is about efficiency, not realizing the system’s true function is normative control through perceived observation.
Context Collapse Risk
Merging corporate SSO with LinkedIn collapses distinct social contexts—professional branding, personal growth, job exploration—into a single auditable identity stream. Professionals misjudge the boundary between public signaling and private surveillance, assuming LinkedIn remains a neutral networking space when in fact authentication turns it into a corporate telemetry channel. This misperception is amplified by ubiquitous SSO design patterns that obscure downstream data use, making systemic overreach feel seamless. The real cost emerges when employees unknowingly disclose career transition signals that trigger preemptive management actions.
Network Contamination
Corporate SSO integration with LinkedIn exposes employees’ external professional networks to algorithmic harvesting by employer-controlled analytics tools, resulting in unintended data leakage across organizational boundaries. This occurs through automated data sync mechanisms that treat employees’ connections as proxy signals for competitive intelligence, security risk, or talent flight likelihood—embedding third-party relationships into internal risk models without consent or transparency. The underappreciated systemic effect is that individuals in a professional’s network—unaffiliated with the employer—become indirectly classified, profiled, or deprioritized in hiring or collaboration based on proximity to internal employees, thereby contaminating neutral professional ecosystems with corporate bias. This reveals how platform interoperability can weaponize ambient affiliation through passive data aggregation.
Data Fiduciary Conflict
Professionals should evaluate SSO-linked LinkedIn risks by recognizing that their personal branding becomes a corporate data asset subject to internal governance, as seen at firms like JPMorgan Chase where employee network metadata informs internal mobility algorithms; this transforms individual professional autonomy into an organizational intelligence stream, undermining the assumption that social profiling remains a personal choice — exposing a structural misalignment between employee self-presentation and employer data extraction that recalibrates consent as operational collateral.
Reputational Arbitrage
The benefit of SSO integration must be assessed through the lens of asymmetric visibility, exemplified by consulting firms such as McKinsey, where partner-level scrutiny of junior staff’s external connections determines client-team eligibility; here, the perceived advantage of seamless access masks a covert ranking system in which network composition becomes a proxy for loyalty and risk, flipping the narrative of digital convenience into a mechanism of social sorting that rewards curated affiliations over demonstrated competence.
SSO-mediated visibility hierarchies
Linking a LinkedIn profile to corporate SSO creates asymmetric visibility where employer-controlled identity providers gain passive access to employee network topology, as seen in companies like Salesforce and Dropbox that integrate Okta with internal people-analytics dashboards; this allows HR and leadership teams to infer informal influence networks through connection density and cross-industry ties without direct monitoring, a mechanism that operates through federated identity logging and event streaming platforms like Splunk; what is overlooked is that the trade-off isn't merely about data exposure but about the reconfiguration of organizational power via automated social network analysis—where employees unknowingly supply the metadata that reshapes promotion pipelines and internal mobility decisions.
Third-party affiliation leakage
Connecting LinkedIn to corporate SSO inadvertently reveals employee affiliations with external entities such as side ventures, professional associations, or competitive industries through linked organization pages and group memberships, a phenomenon observed at firms like Intel and IBM where security audits flagged SSO-logged LinkedIn sessions as vectors for detecting undeclared outside activities; the causal mechanism runs through OAuth token permissions that expose not just profile data but behavioral breadcrumbs in third-party ecosystems, which compliance teams can retrospectively mine via API logs; this shifts the privacy calculus from personal disclosure to institutional surveillance of professional pluralism—exposing tensions between corporate loyalty and individual career agency that most policies fail to address.
Identity provenance erosion
Corporate SSO binding to LinkedIn collapses the distinction between personal professional identity and company-managed digital persona, as evidenced in consulting firms like Deloitte and PwC where employees’ externally grown networks are effectively co-opted into the firm’s client engagement analytics via Microsoft Entra ID integrations; the dynamic operates through persistent authentication tokens that allow the employer’s IAM system to retroactively tag and claim credit for business development activities initiated independently by the employee; the overlooked consequence is the blurring of identity provenance—the moment a personal connection becomes a firm asset—which undermines autonomous career capital accumulation and redefines individual reputation as fungible organizational data.