Is Location-Based Auth for Banking Worth Risks of Surveillance?
Analysis reveals 5 key thematic connections.
Key Findings
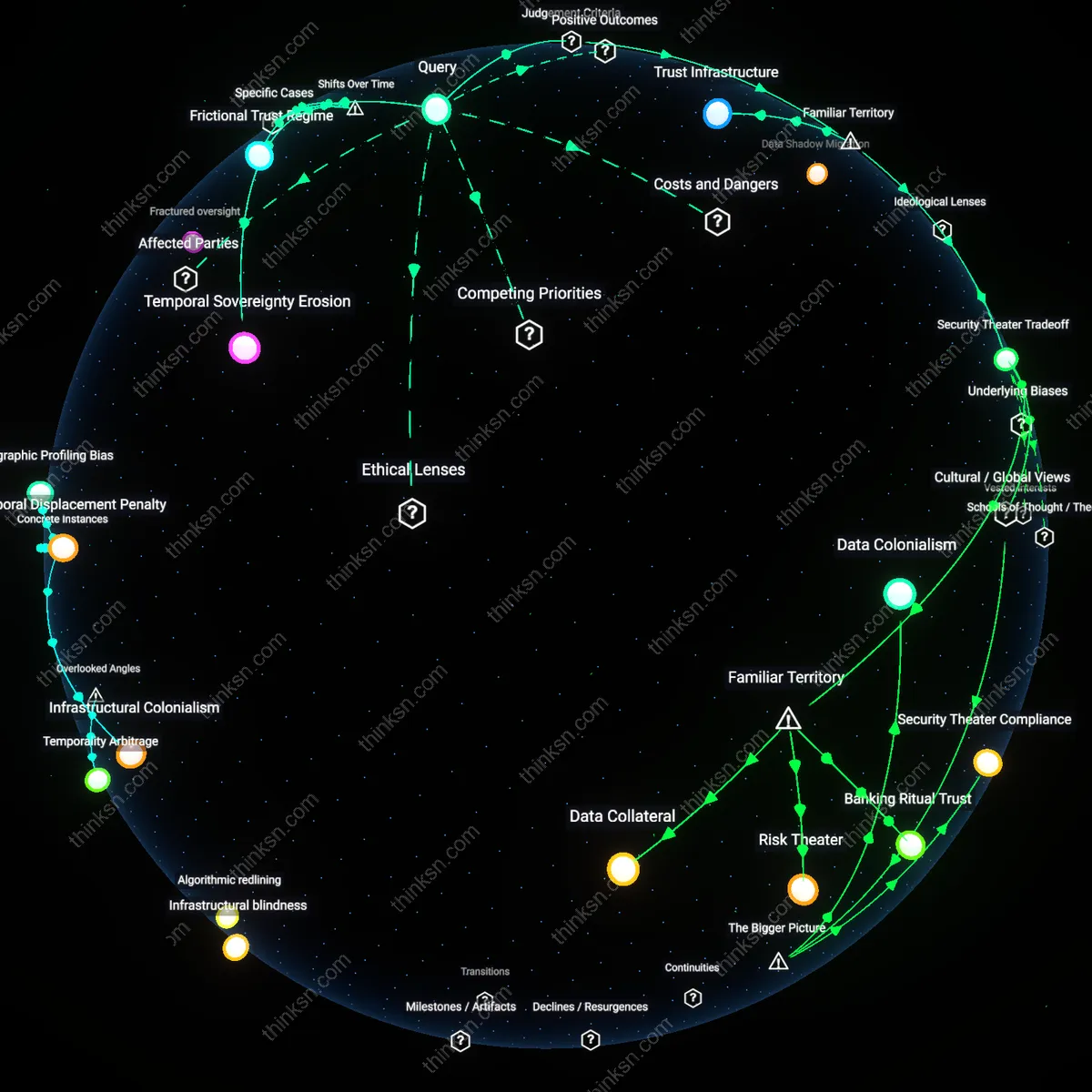
Trust Infrastructure
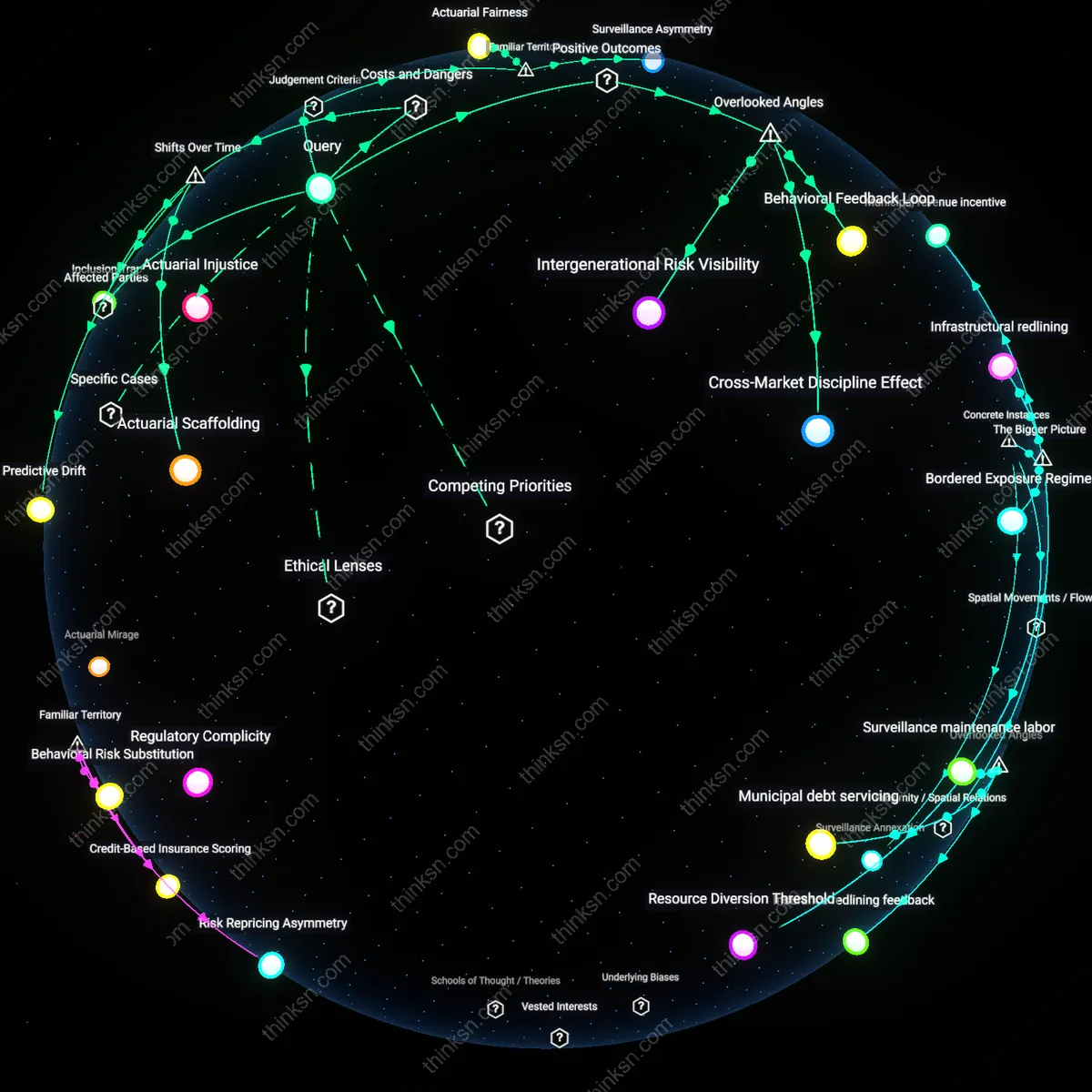
Users should defer to institutional oversight mechanisms when evaluating location-based authentication because the primary yardstick is systemic trust in regulated financial institutions over adversarial state actors. This judgment relies on the principle of institutional fidelity—banks operating under consumer protection laws are held to higher accountability standards than intelligence or surveillance agencies, creating a practical hierarchy of risk where opting into bank security protocols is seen as participating in a monitored, rule-bound system rather than an exploitable data pipeline. The non-obvious insight here, against the backdrop of widespread suspicion of government overreach, is that most users already associate banking apps with protected digital spaces akin to vaults, not data leaks—this familiar framing of banks as fiduciaries precipitates reliance on their infrastructures as trusted intermediaries, even when they collect sensitive data.
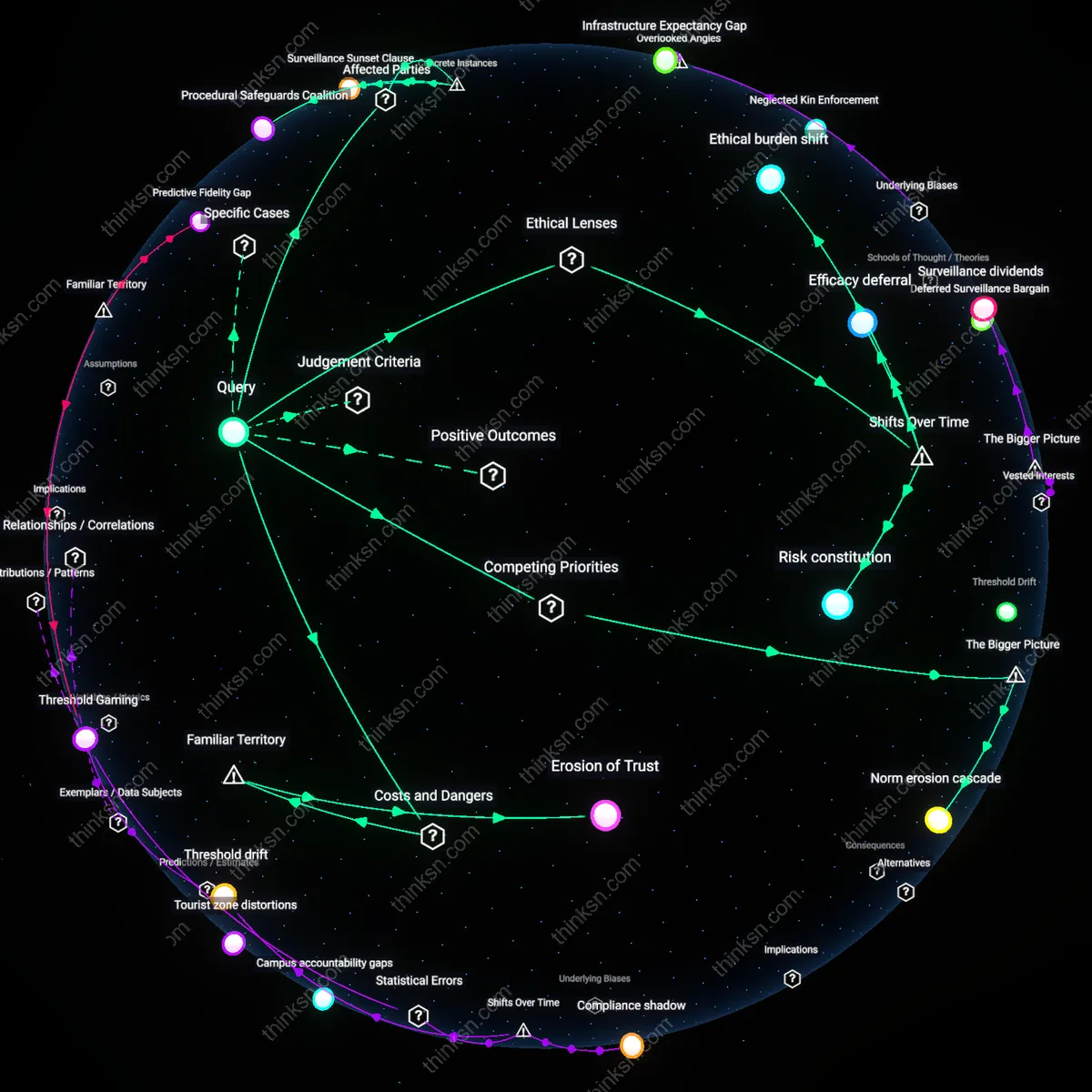
Security Theater Tradeoff
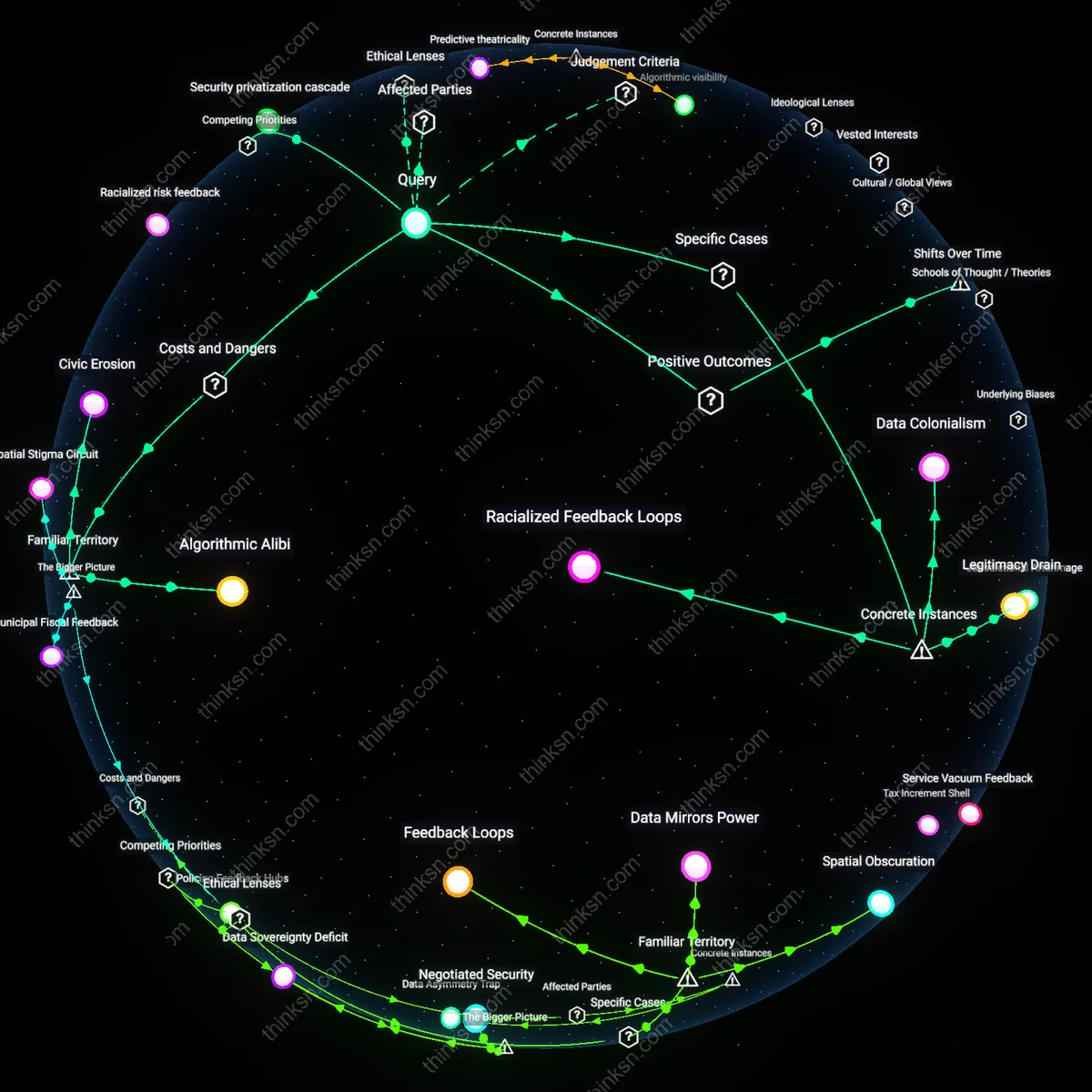
Users should treat location-based authentication as a performative security measure because the dominant yardstick in public perception is symbolic safety rather than actual risk reduction, rooted in the principle of perceived control. This functions through the design logic of banking apps, which prioritize user reassurance—such as requiring location checks during login—over demonstrable fraud prevention gains, capitalizing on the familiar association between GPS tracking and ‘precision’ or ‘modernity’ in digital security. The underappreciated truth, given this lens, is that the real value of location authentication often lies in making users feel protected rather than in materially thwarting attacks, subtly normalizing constant surveillance as the price of participation in formal finance, thus reframing security not as a shield but as a ritualized concession.
Frictional Trust Regime
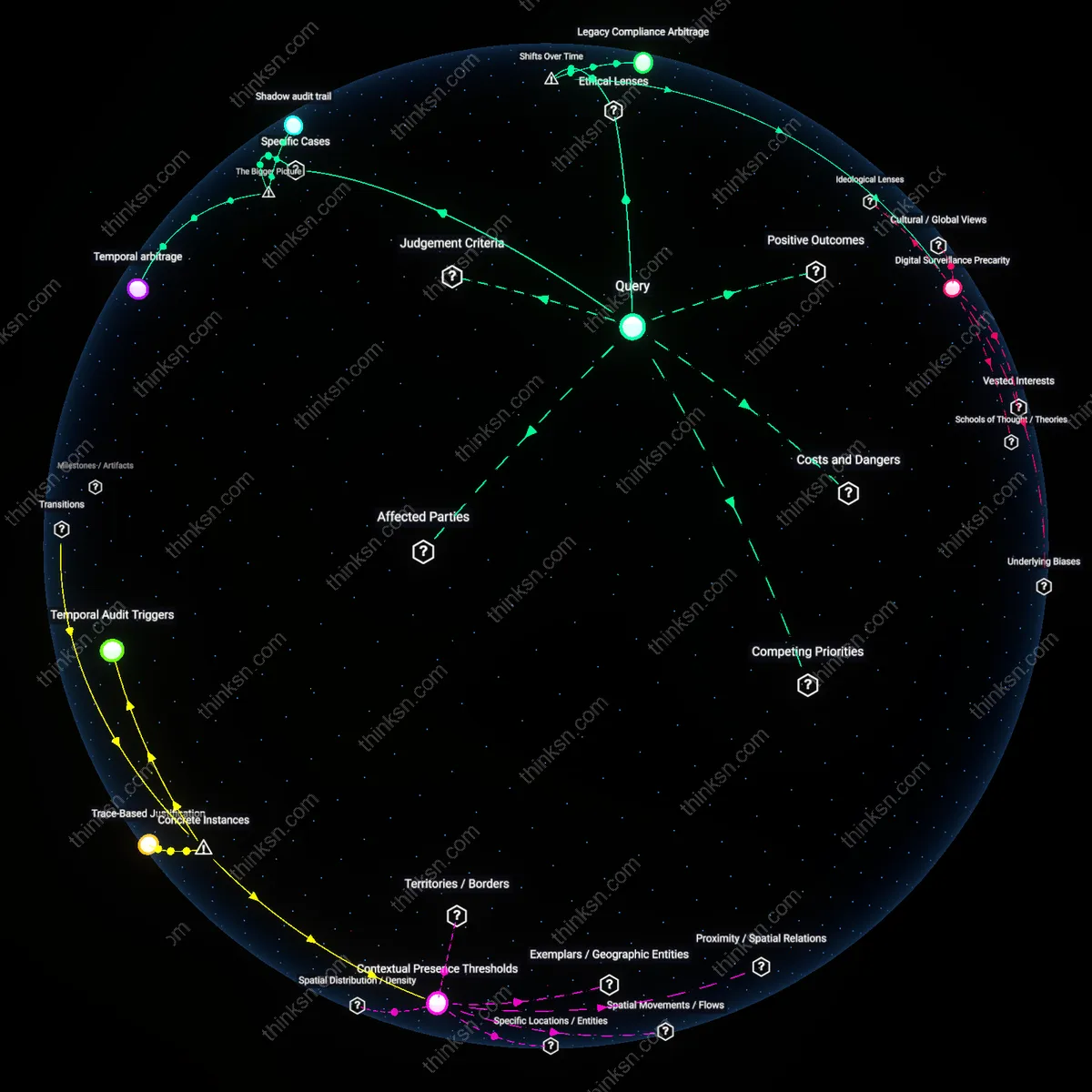
The integration of location-based authentication in Indian banking apps after the 2016 demonetization shift reveals a trade-off where financial inclusion efforts intensified data collection, enabling state actors to repurpose geolocation metadata for monitoring protest movements like the 2019–2020 anti-CAA demonstrations. As the biometric and digital identity infrastructure (Aadhaar-linked banking) expanded under crisis-driven modernization, authentication security became entangled with surveillance capacity, not through direct mandates but via shared backend infrastructures operated by public-private consortia. This post-2016 trajectory shows that the perceived security benefit of location checks was less about reducing fraud and more about enabling centralized verification systems—their analytical significance lying in how crisis temporalities normalized data pooling once considered excessive, producing a new governance rhythm where trust is algorithmically mediated but asymmetrically enforceable.
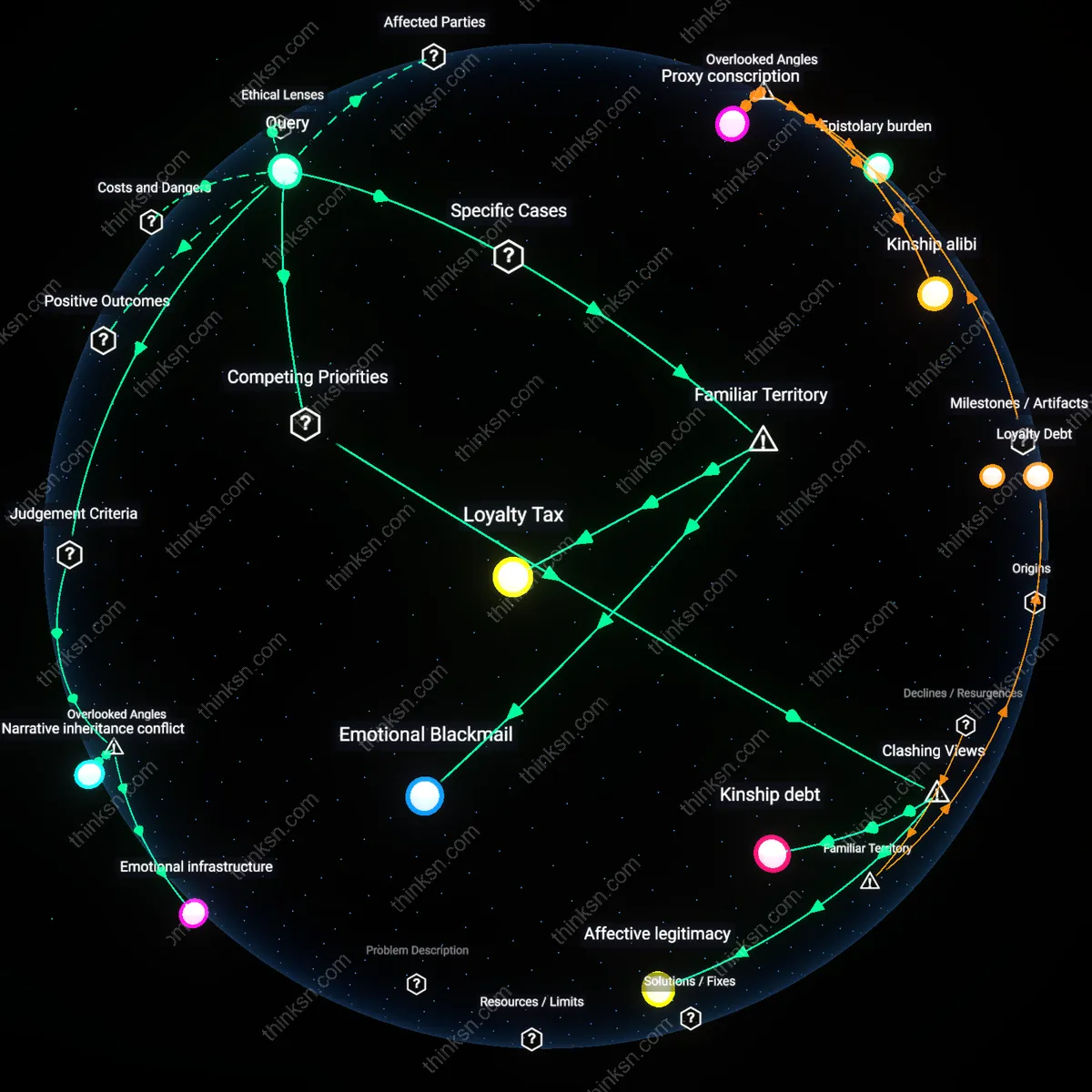
Temporal Sovereignty Erosion
In Belarus during the 2020–2021 political uprisings, state security forces leveraged geolocation data from mobile banking apps, including those operated by state-controlled banks like Belgazprombank, to track opposition figures accessing financial services near protest zones—marking a shift from pre-2010 authentication models that relied on static passwords and regional branch verification. The post-2015 introduction of GPS-triggered login alerts and automatic session locks, marketed as anti-fraud measures, coincided with the migration of banking infrastructure to centralized cloud platforms overseen by Roskomnadzor-aligned contractors, enabling temporal alignment of user authentication events with state event monitoring. The underappreciated mechanism is not data collection per se, but the synchronization of individual financial behavior with state-defined temporal registers—where logging in from a new location at a politically sensitive hour becomes an anomaly flag not just for fraud but dissent, revealing how authentication systems evolved into tools of temporal political control.
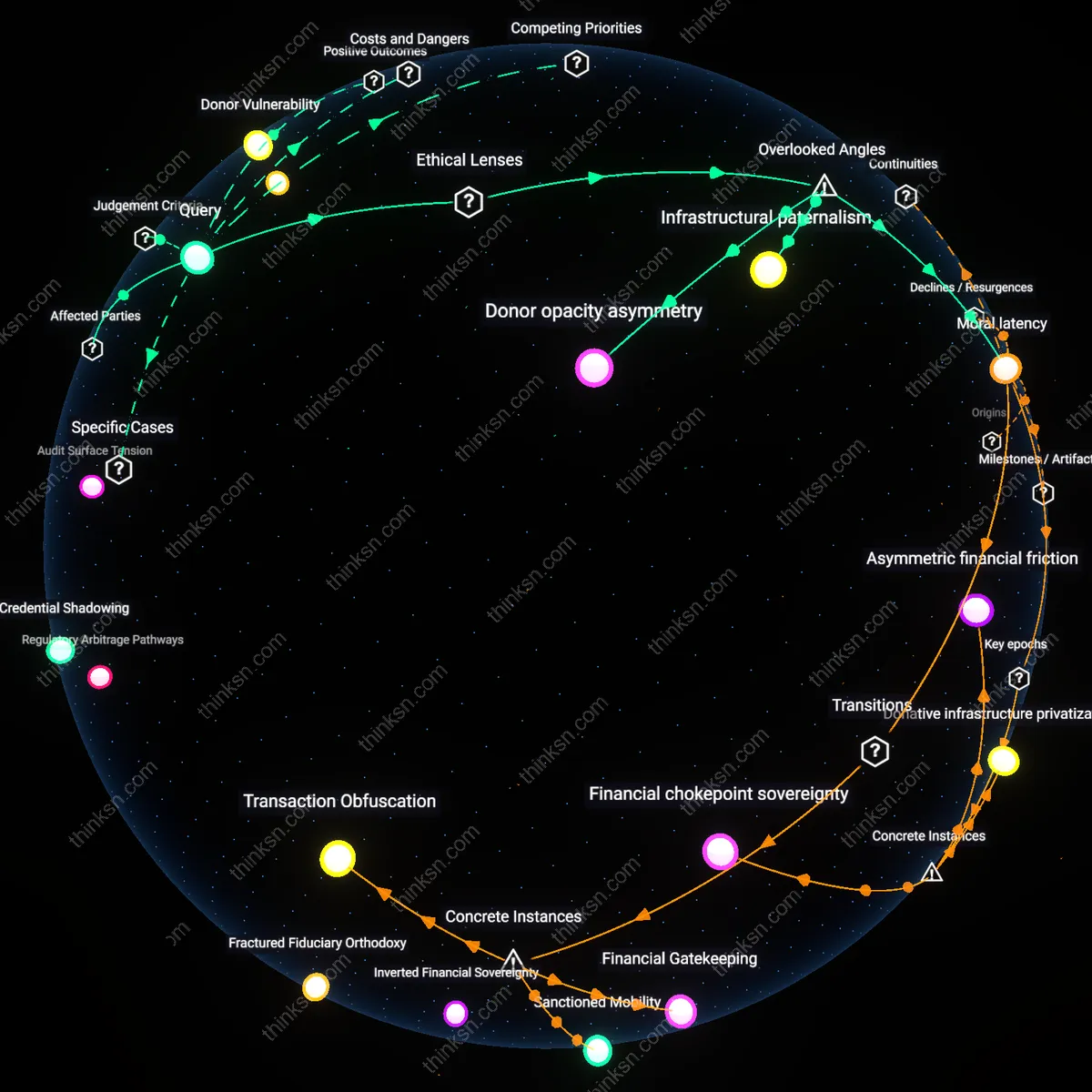
Security-Surveillance Convergence
Starting around 2017, U.S. federal agencies including the FBI and DHS increased collaboration with JPMorgan Chase and Bank of America through the Financial Crimes Enforcement Network (FinCEN) to access real-time geolocation data streams from mobile banking apps, justified under anti-terrorism authentication protocols but later used to map the movements of Black Lives Matter organizers during the 2020 protests. The pivotal shift occurred when banks migrated from device-based to behavior-based authentication models—geolocation becoming one of several dynamic variables scored continuously rather than checked intermittently—creating a constant surveillance byproduct under the guise of adaptive security. What is rarely acknowledged is that this convergence was not the result of regulatory overreach alone, but of banks voluntarily building dual-use systems where the same API that blocks a login from Lagos also flags a cluster of logins near a Minneapolis police precinct, transforming authentication infrastructure into a de facto state monitoring substrate.