Is a Companys Privacy Apology Genuine or Just PR?
Analysis reveals 7 key thematic connections.
Key Findings
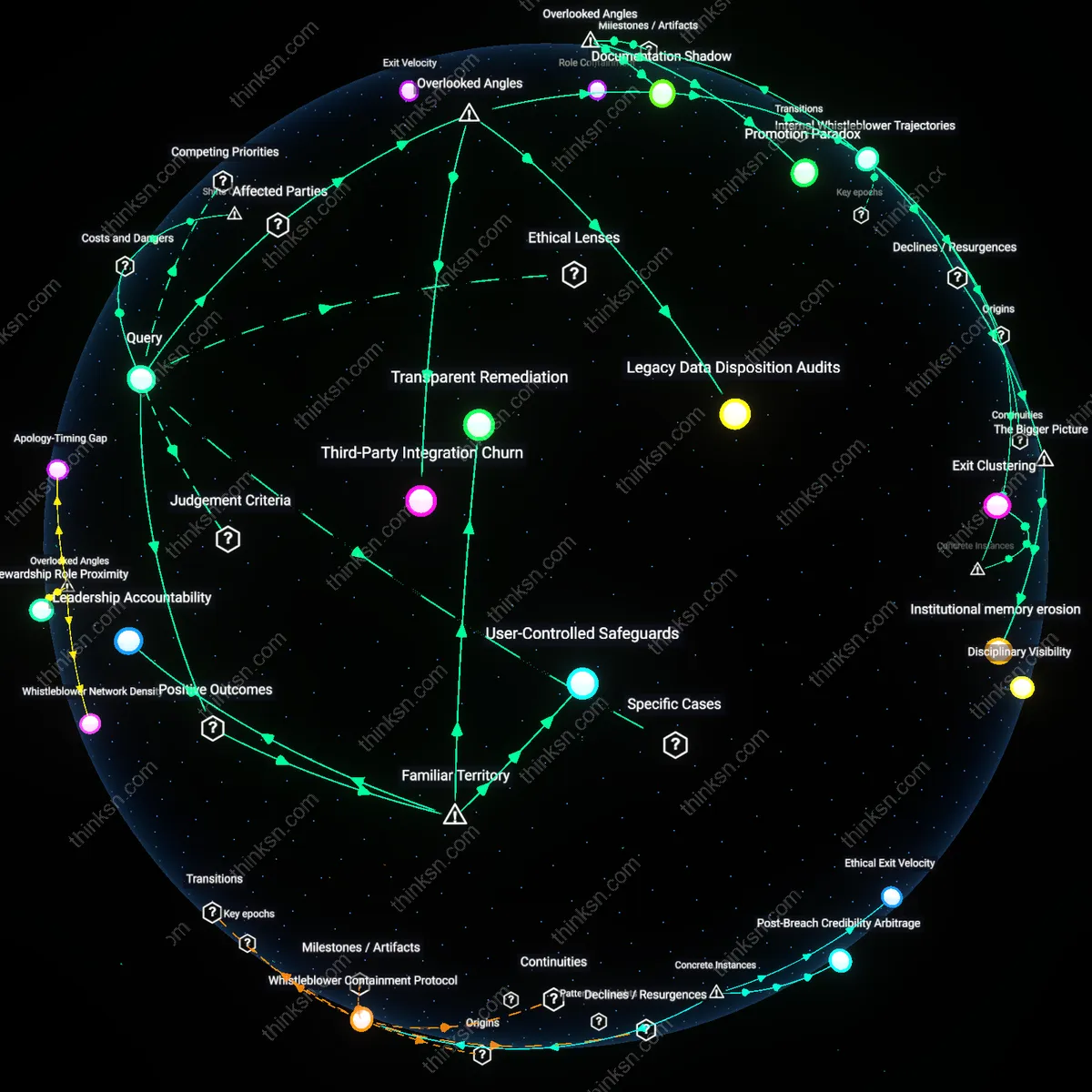
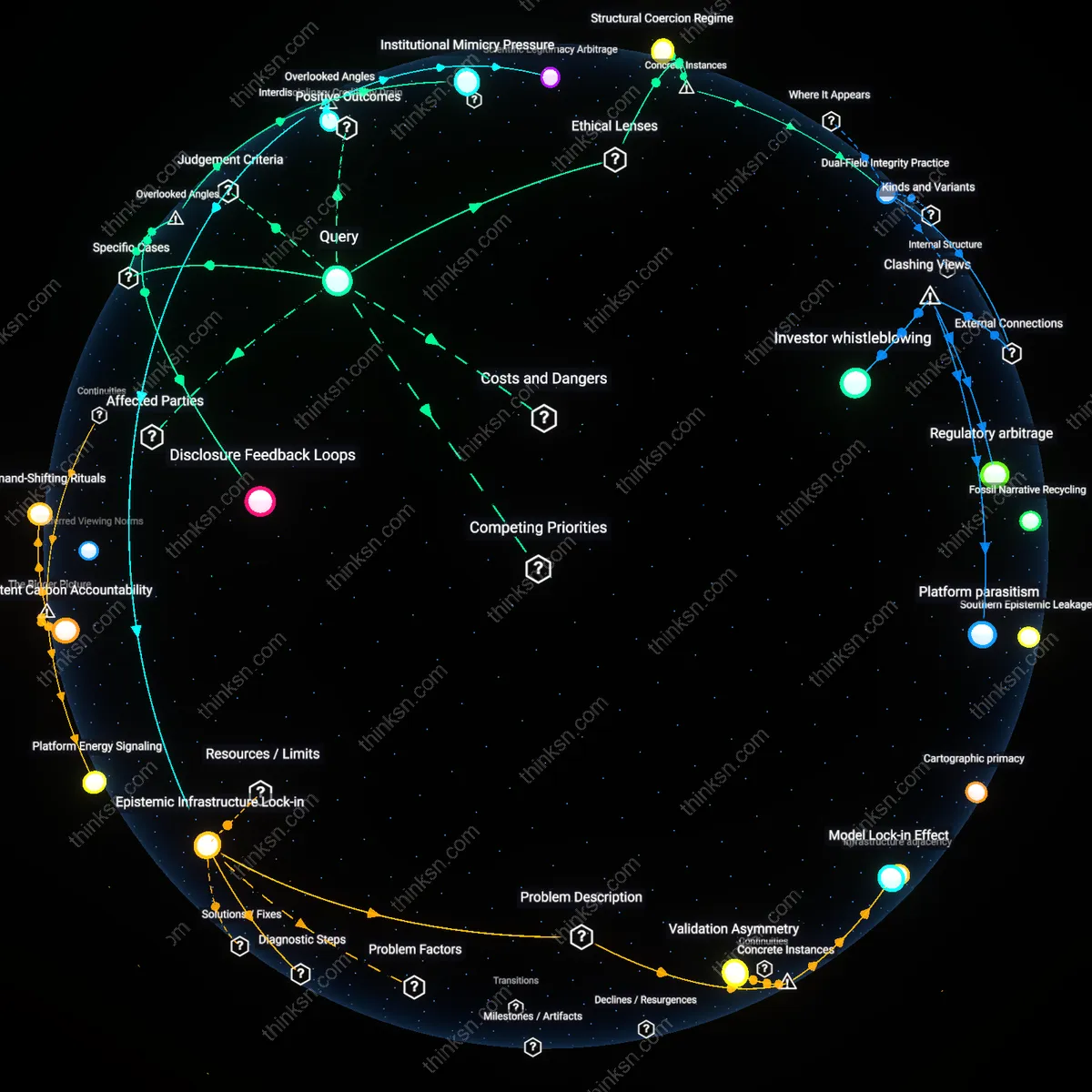
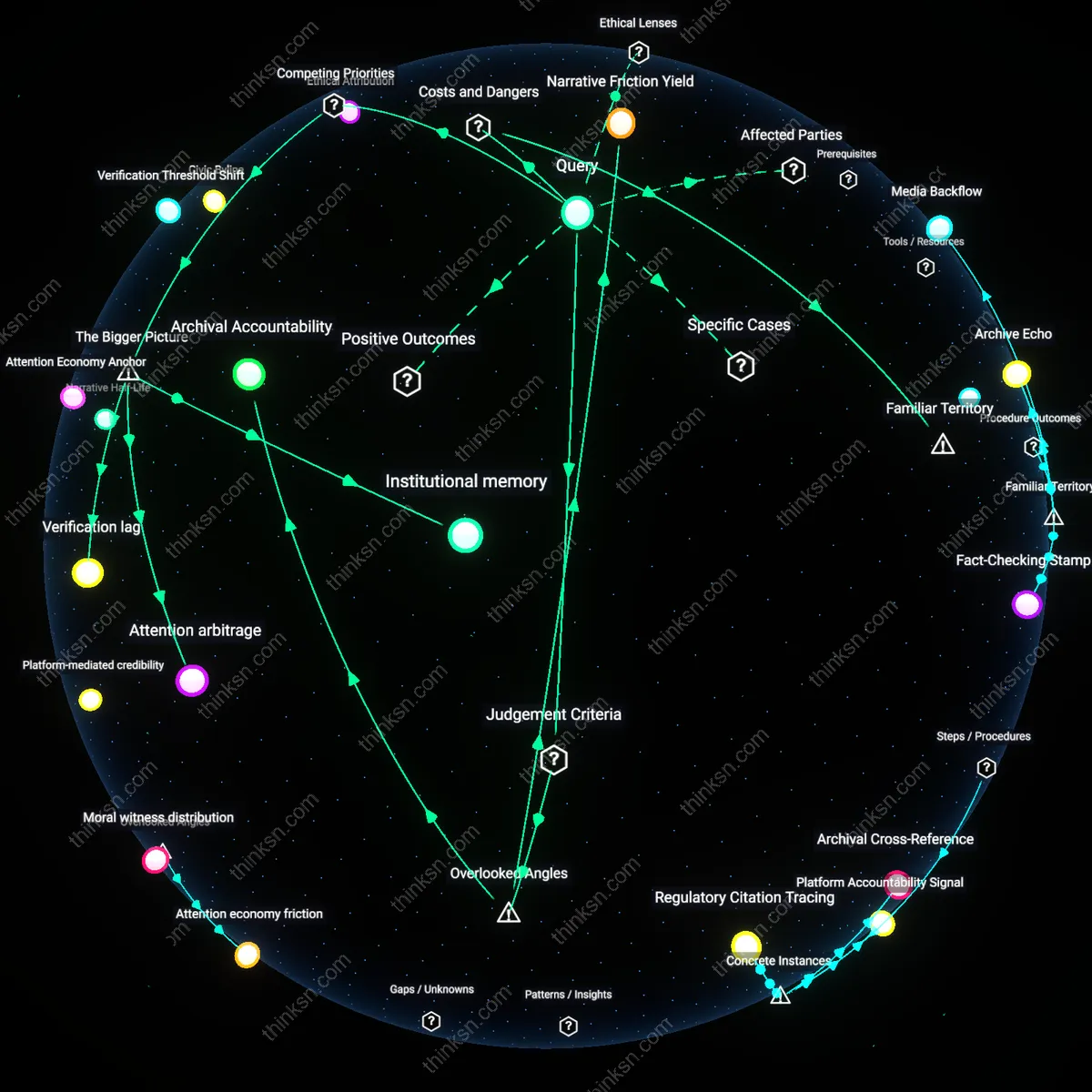
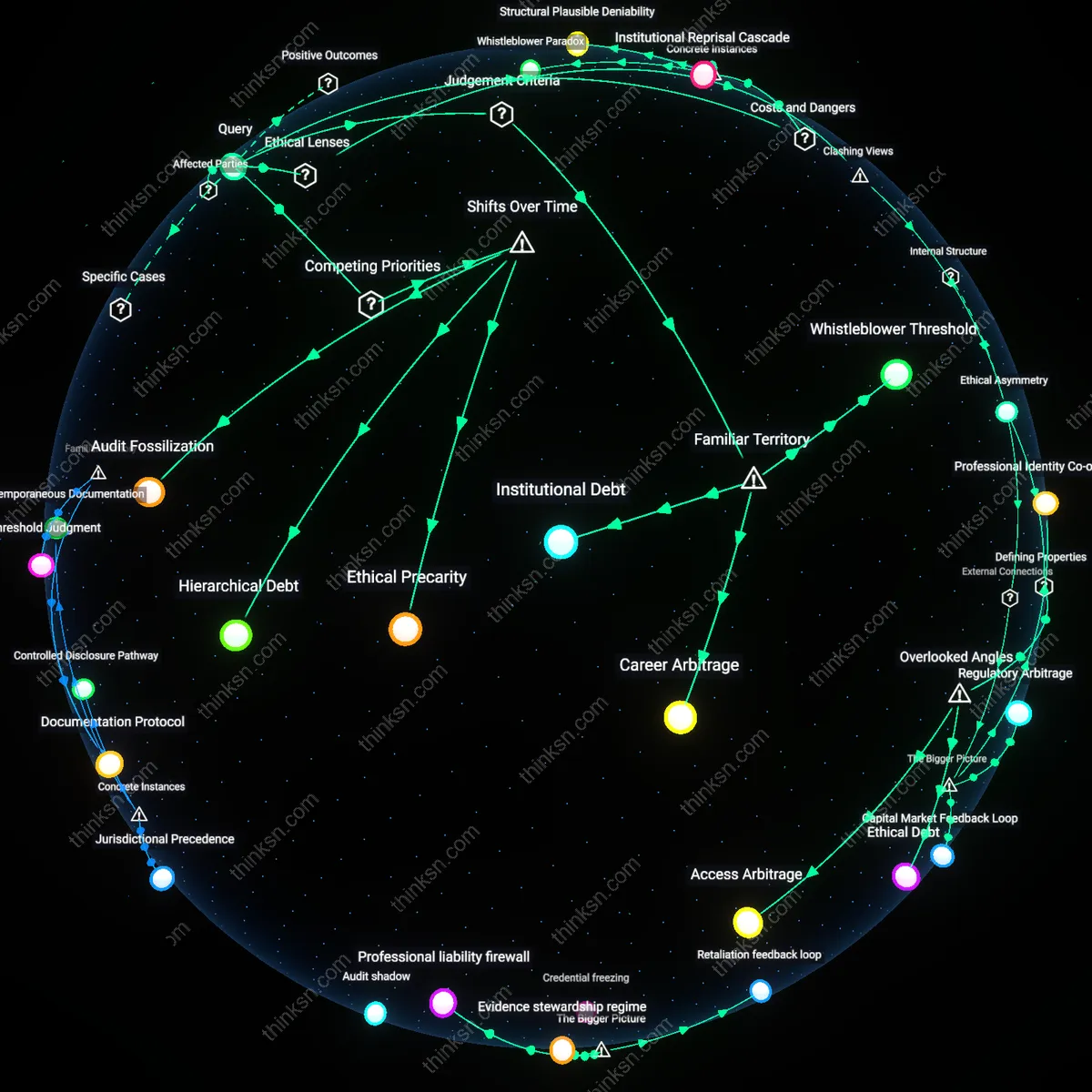
Internal Whistleblower Trajectories
Consumers should assess whether a company’s public apology includes verifiable pathways for internal whistleblowers to report future privacy violations without retaliation, because the presence of protected disclosure mechanisms reveals whether accountability is structurally embedded or performative. Most analyses focus on external statements or regulatory fines, but the treatment of mid-level engineers, compliance officers, or customer support staff who detect breaches—who are often sidelined or punished—determines whether change is sustained; companies that privatize risk while socializing accountability rarely alter internal power hierarchies. The non-obvious dimension here is that genuine reform is signaled not by executive promises but by observable career outcomes for employees who challenge data practices, which most PR campaigns deliberately obscure.
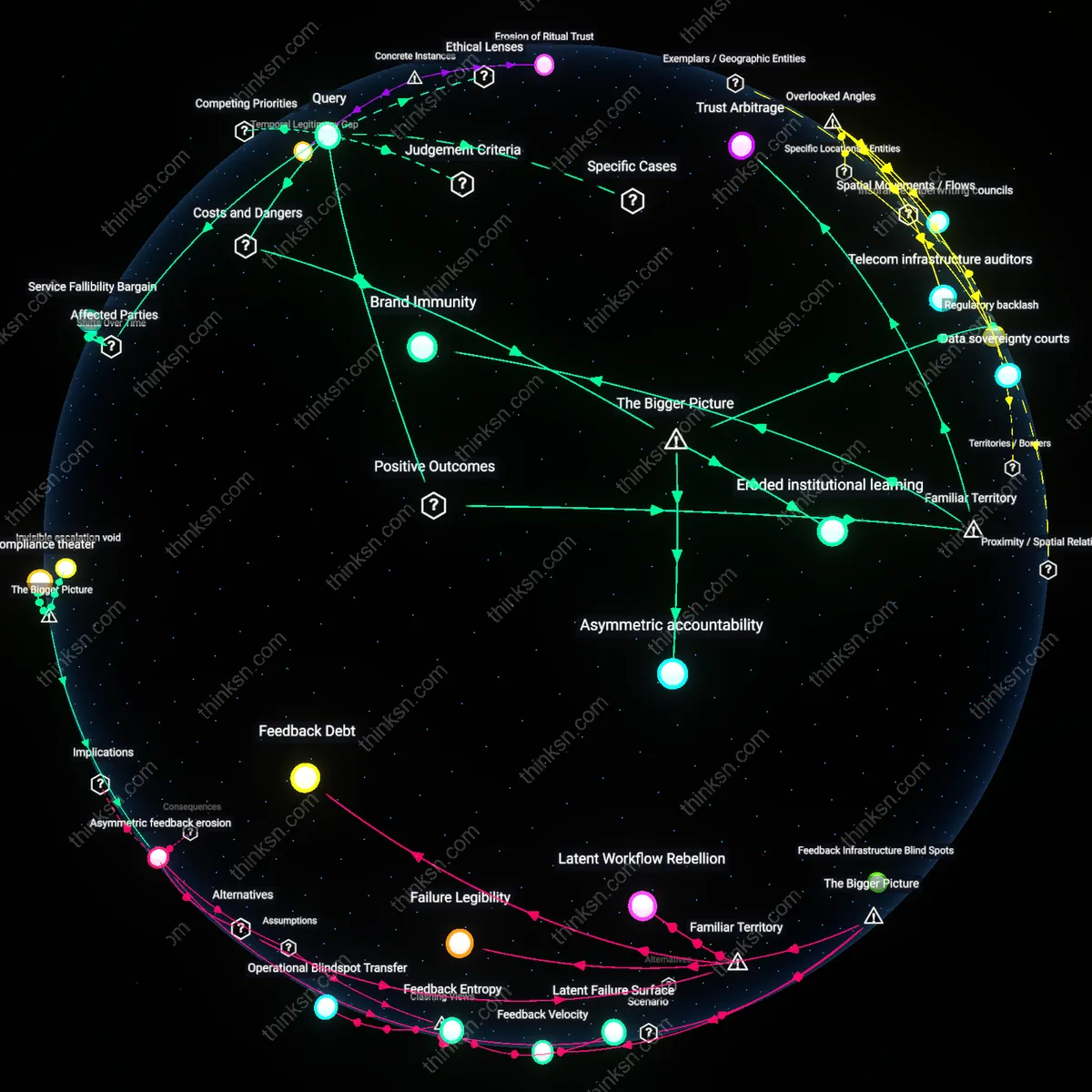
Legacy Data Disposition Audits
Consumers should demand transparency about the destruction or archival status of pre-breach user data, because a company’s willingness to relinquish stored behavioral datasets—not just promise future care—indicates whether the breach is treated as an operational inflection point or a reputational bump. Standard evaluations ignore that many privacy violations stem from legacy data hoarded beyond functional need, and firms that avoid auditing or disclosing retention timelines are often relying on continued data extraction under repaired branding. The overlooked mechanism is that data minimization is a commitment to reduced surveillance capacity, not just better security—a sacrifice that PR-driven companies avoid despite public pledges.
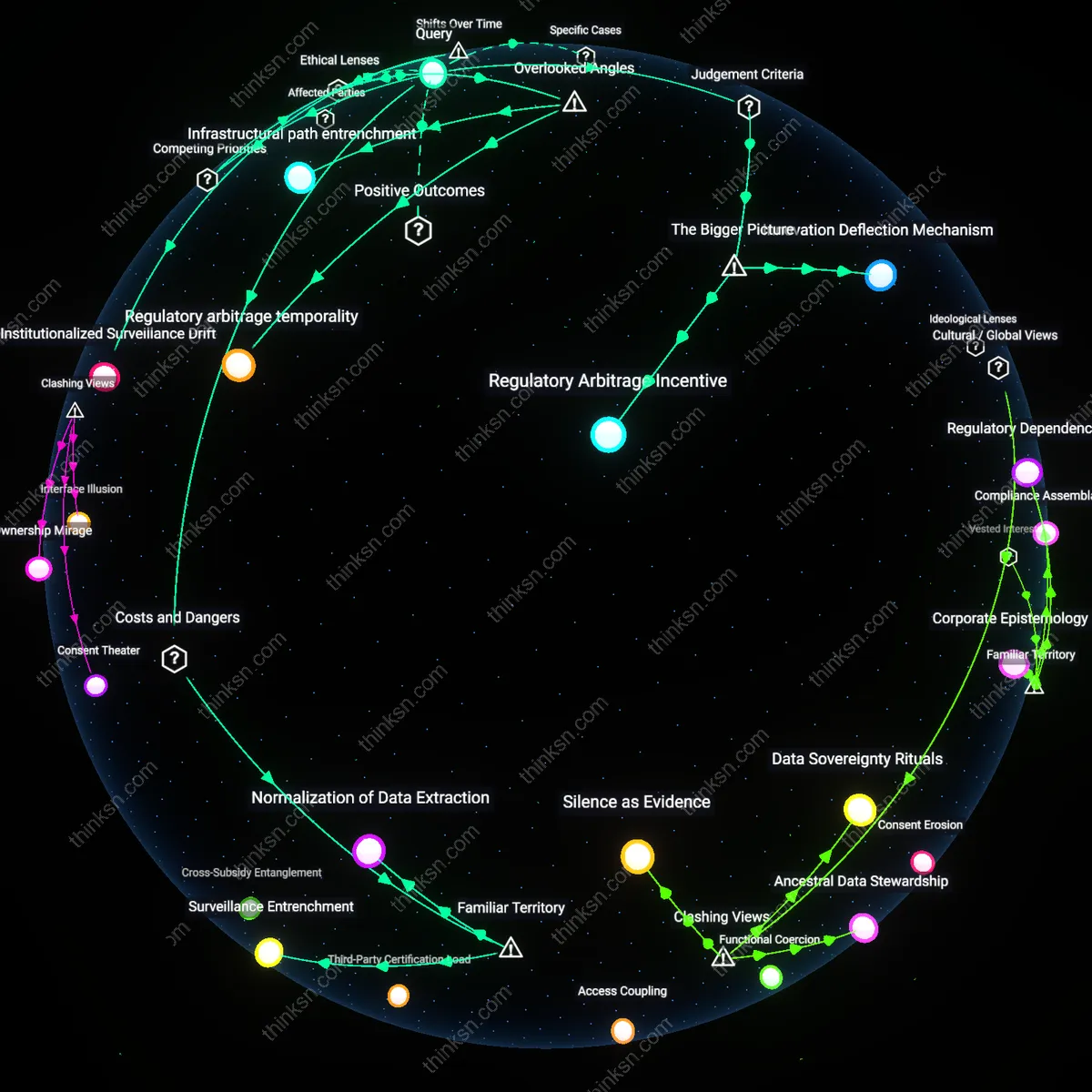
Third-Party Integration Churn
Consumers should track whether a company severs or restructures integrations with data brokers, ad-tech partners, or cloud vendors after a breach, because these external dependencies often enable the very vulnerabilities cited in the apology, yet remain untouched during cosmetic reforms. Most scrutiny stops at first-party practices, but the subcontracted data ecosystem determines real risk exposure, and firms that maintain prior integration patterns—despite claims of overhaul—are preserving the infrastructure of failure. The hidden dynamic is that privacy commitments are hollow if the supply chain of data sharing is unchanged, revealing that control, not security, is the unaddressed core issue.
Leadership Accountability
Consumers should assess whether company executives directly responsible for the privacy breach have been replaced or disciplined, because public apologies gain credibility when leadership consequences follow failures. Real organizational change is signaled not by PR statements but by personnel shifts at the top, particularly when CEOs or data officers are held liable through demotion, resignation, or lost compensation. This mechanism operates through corporate governance structures where board decisions reflect internal accountability, a detail often overlooked because audiences focus on messaging tone rather than power redistribution within firms.
Transparent Remediation
Consumers should look for detailed, public updates about technical and policy changes the company has implemented since the breach, because genuine reform is demonstrated through visible upgrades to data encryption, access controls, or third-party auditing. These improvements become credible when shared via open reports or live dashboards that allow users to verify progress over time, functioning through sustained transparency systems that most companies avoid due to cost and scrutiny. The underappreciated point is that familiar demands for 'transparency' mean little unless they are operationalized in persistent, auditable formats.
User-Controlled Safeguards
Consumers should determine whether the company has granted users new tools to monitor, restrict, or withdraw consent from data use as a direct result of the breach, because real commitment emerges when control is redistributed from institutions to individuals. Features like real-time data tracking, one-click opt-outs, or breach notification triggers put power in users’ hands through product-level design changes, which matter more than statements because they embed accountability into daily interaction. Most people assume apologies stand or fall on sincerity, but the lasting shift lies in whether users gain enforceable agency, not just reassurance.
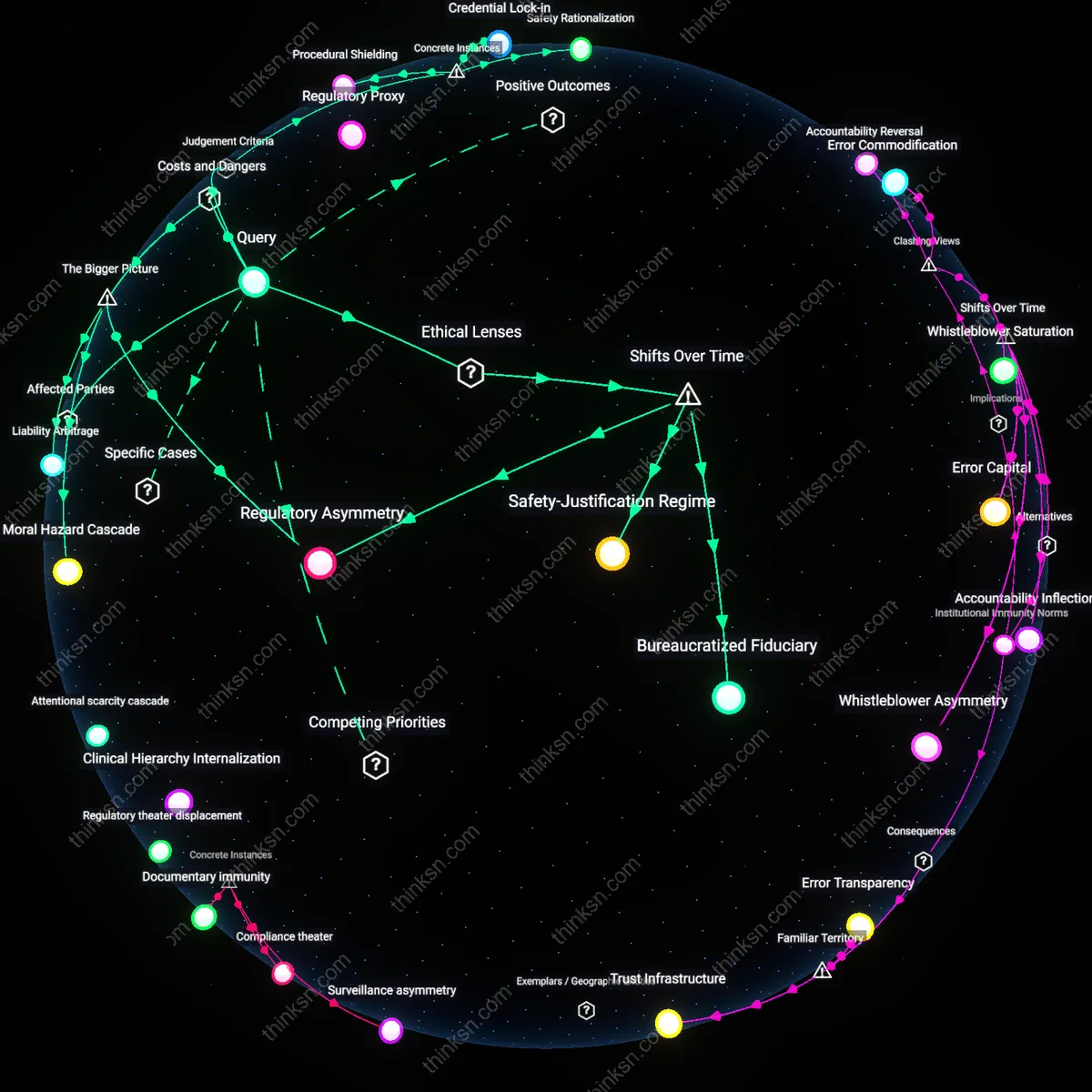
Apology Infrastructure
Consumers should evaluate whether the same legal and PR teams that issued past apologies reappear with identical language after each incident, because since the early 2010s, Silicon Valley firms have institutionalized standardized apology templates, crisis workflows, and algorithmic sentiment responses that operate as a permanent crisis machinery—this shift from ad hoc damage control to a routinized, modular apology system means that speed and consistency of response now signal premeditated PR engineering rather than reflective change. The existence of internal 'apology protocols' staffed by dedicated crisis units, often contracted through third-party risk management firms, demonstrates how authenticity has been replaced by operational efficiency in post-breach communication. This systemic formalization, hidden beneath emotional rhetoric, exposes the apology itself as a predictable cost of doing business rather than a moral turning point.