Welcome to thinksn
About This Analysis
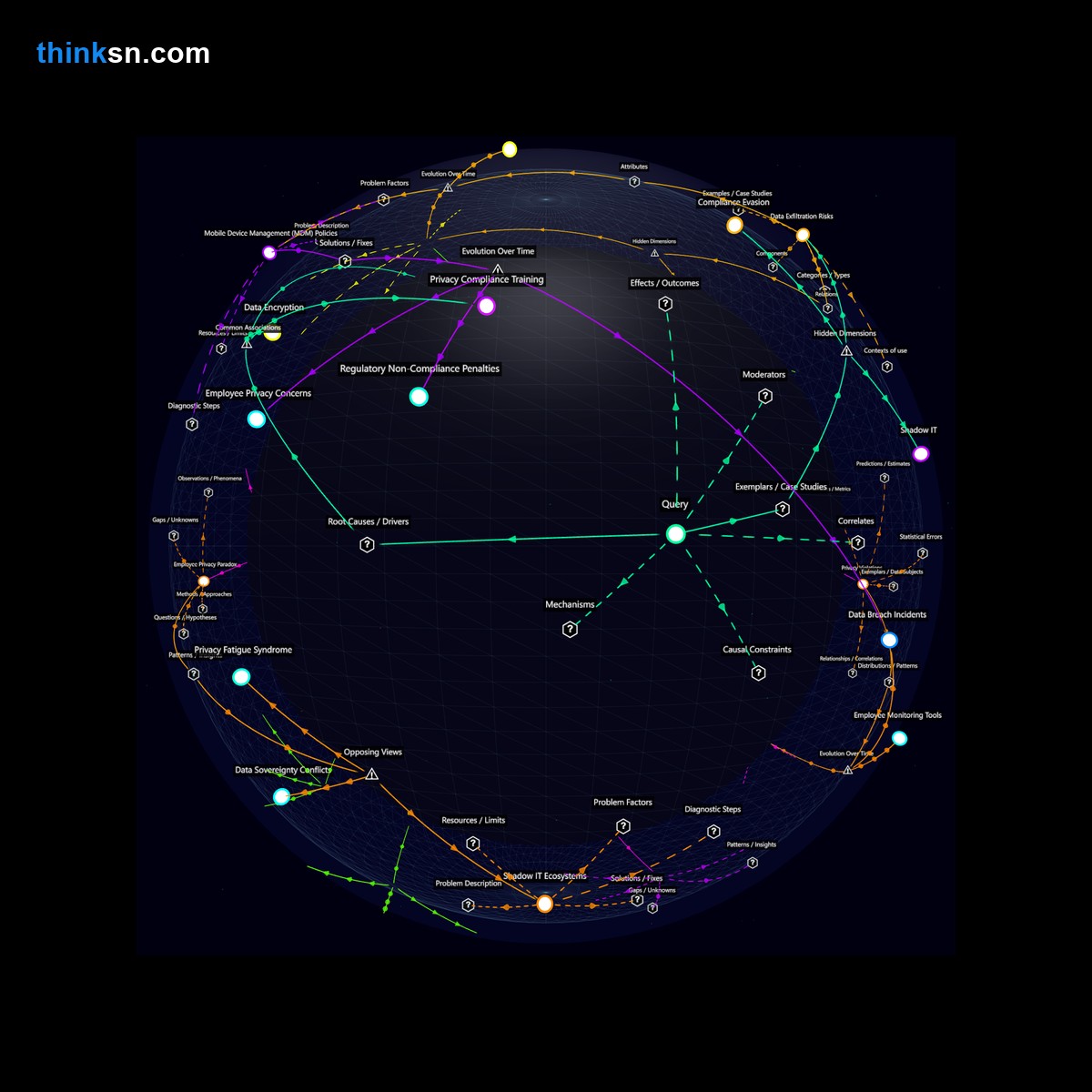
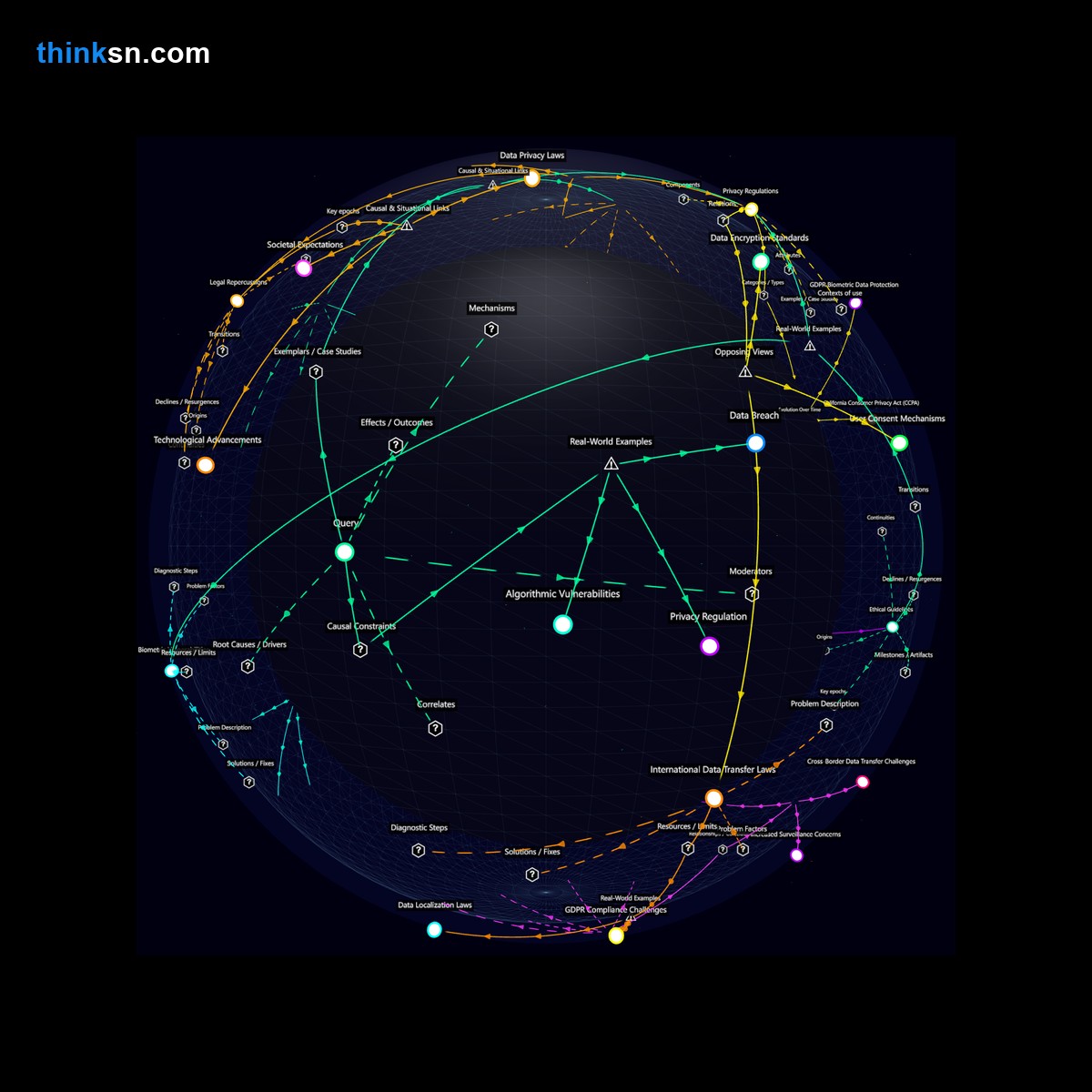
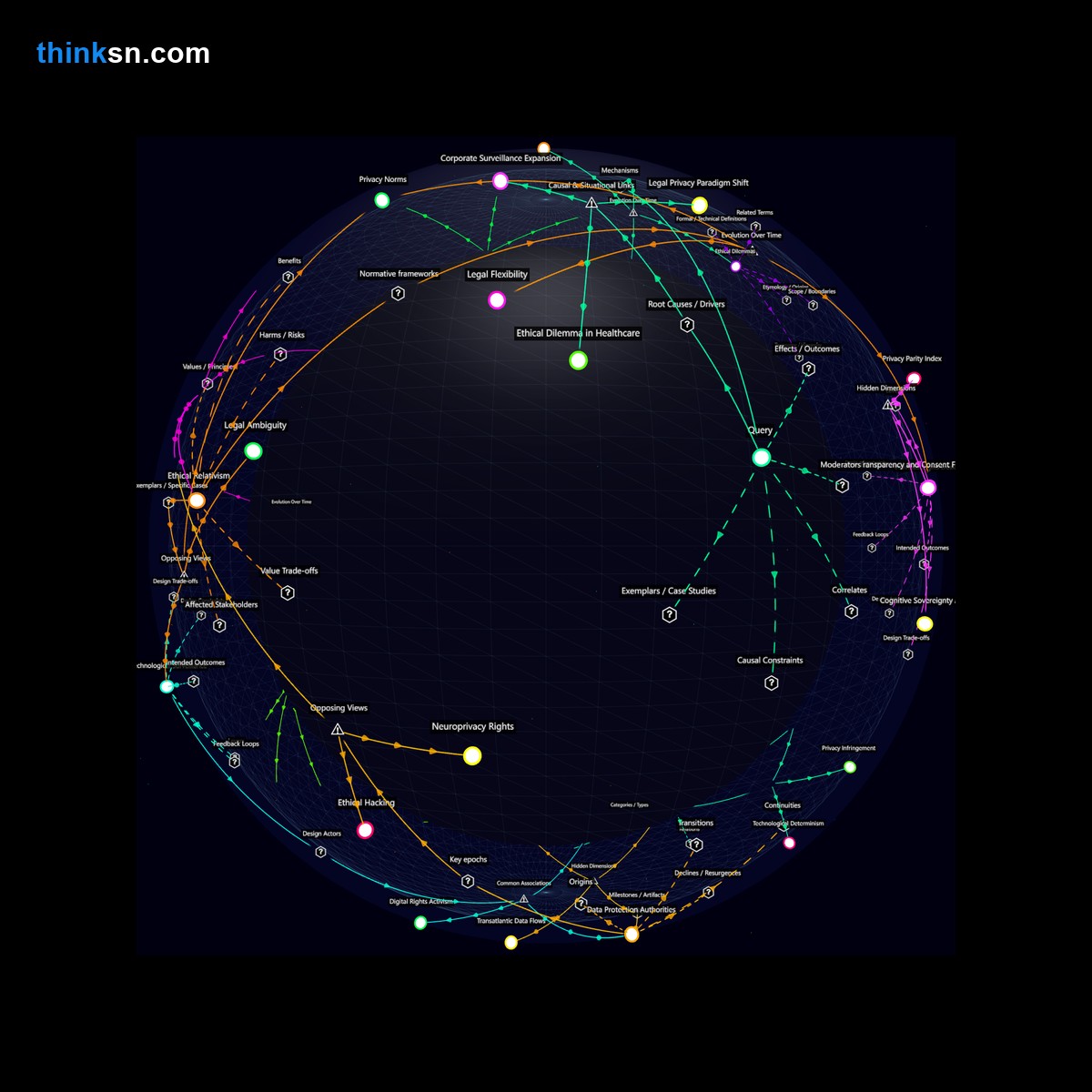
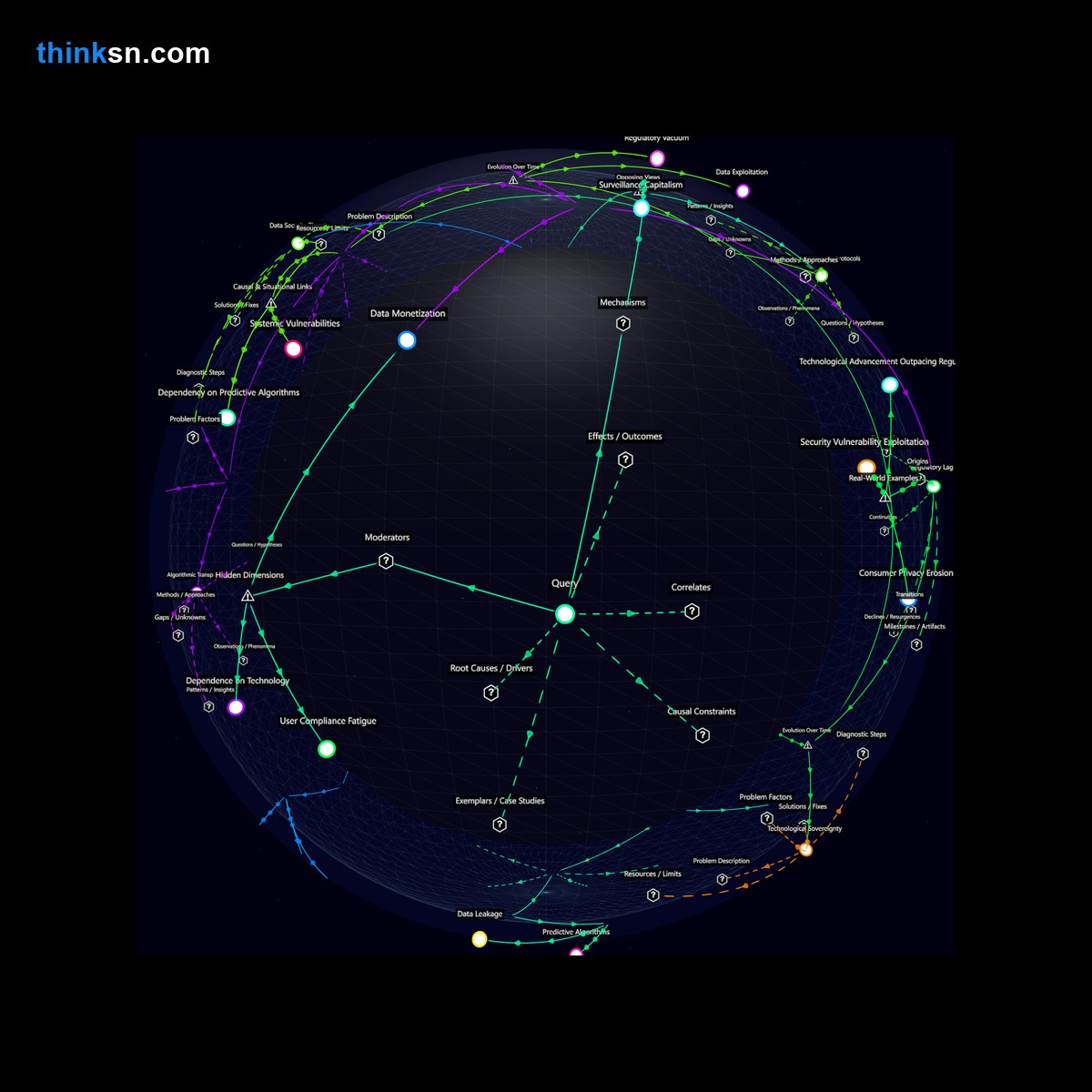
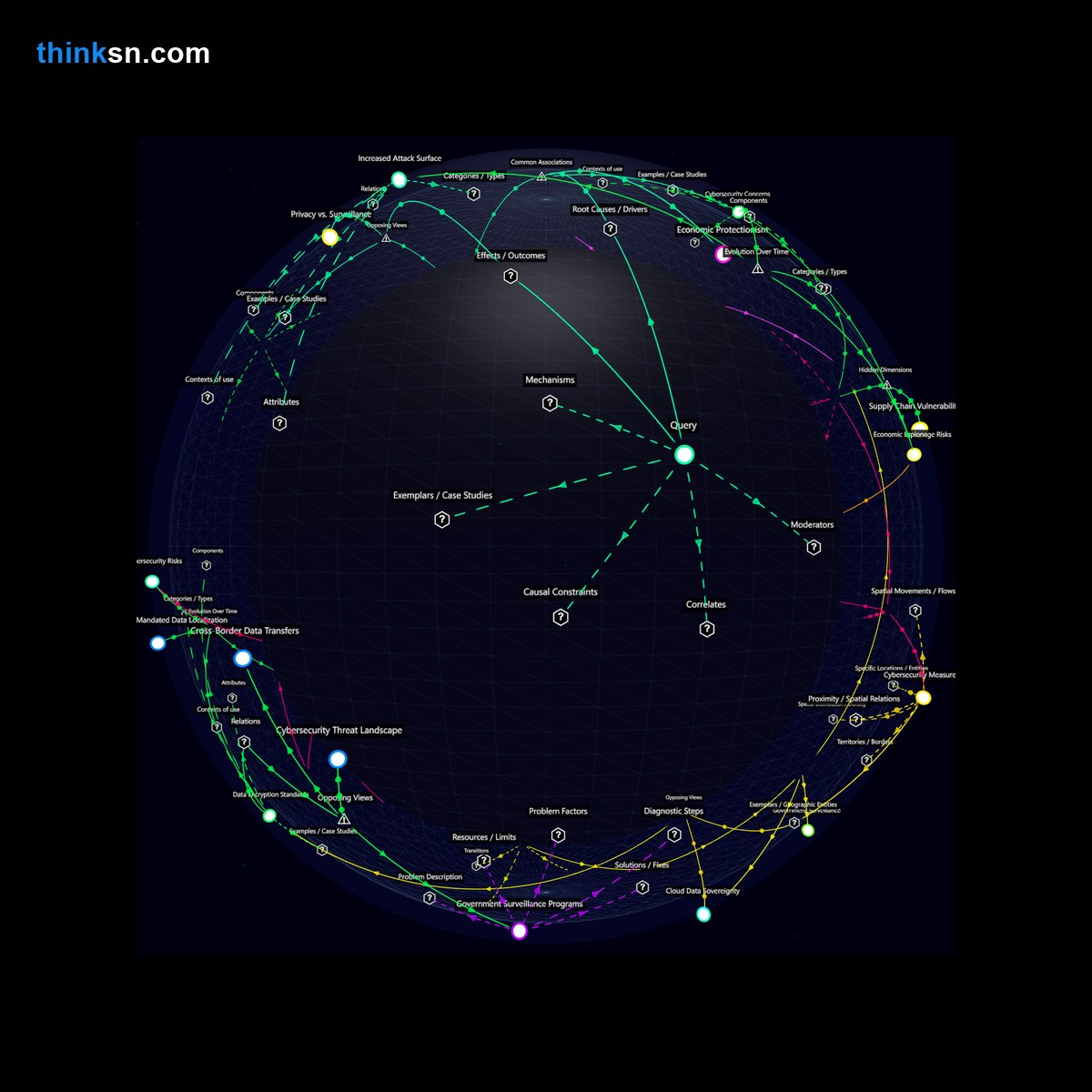
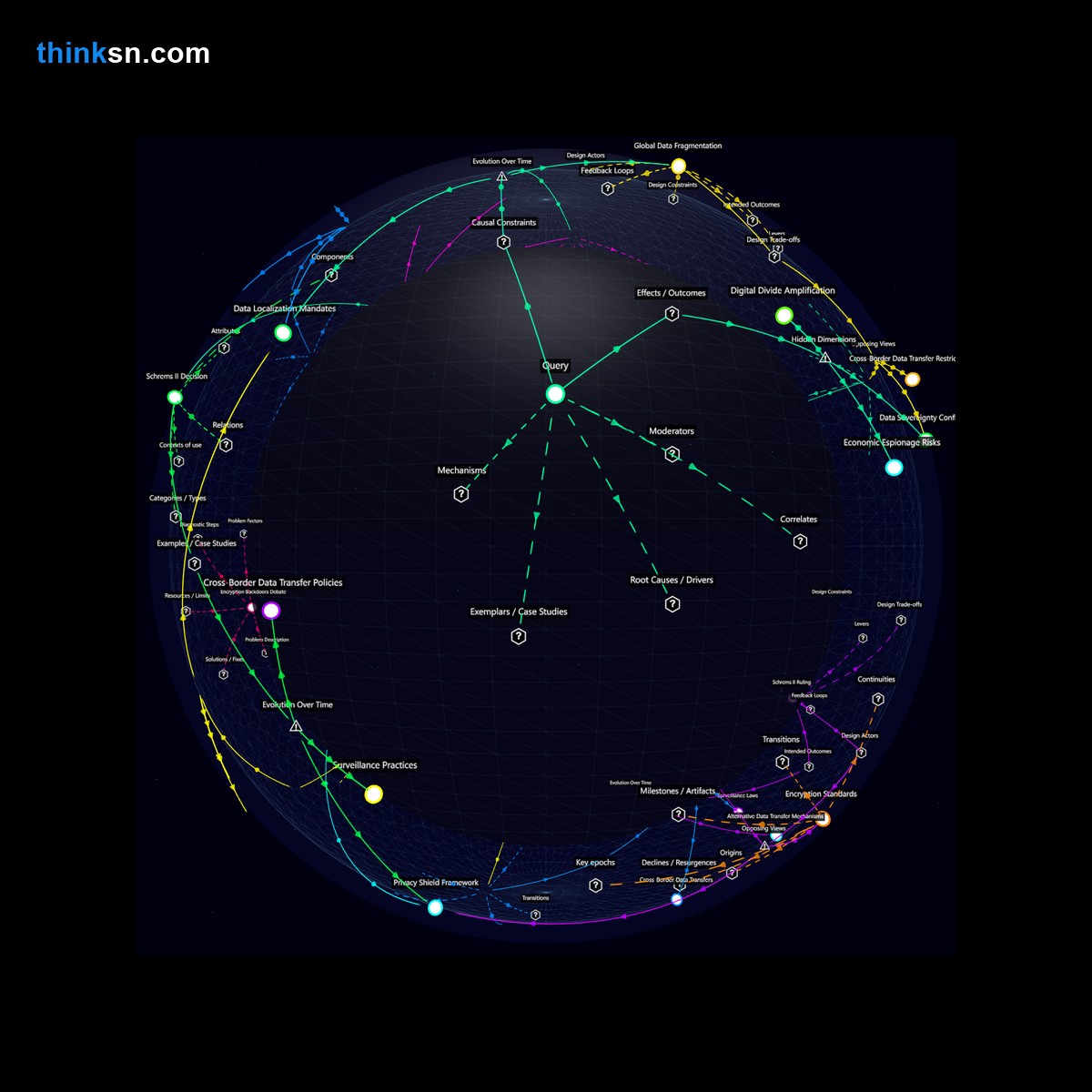
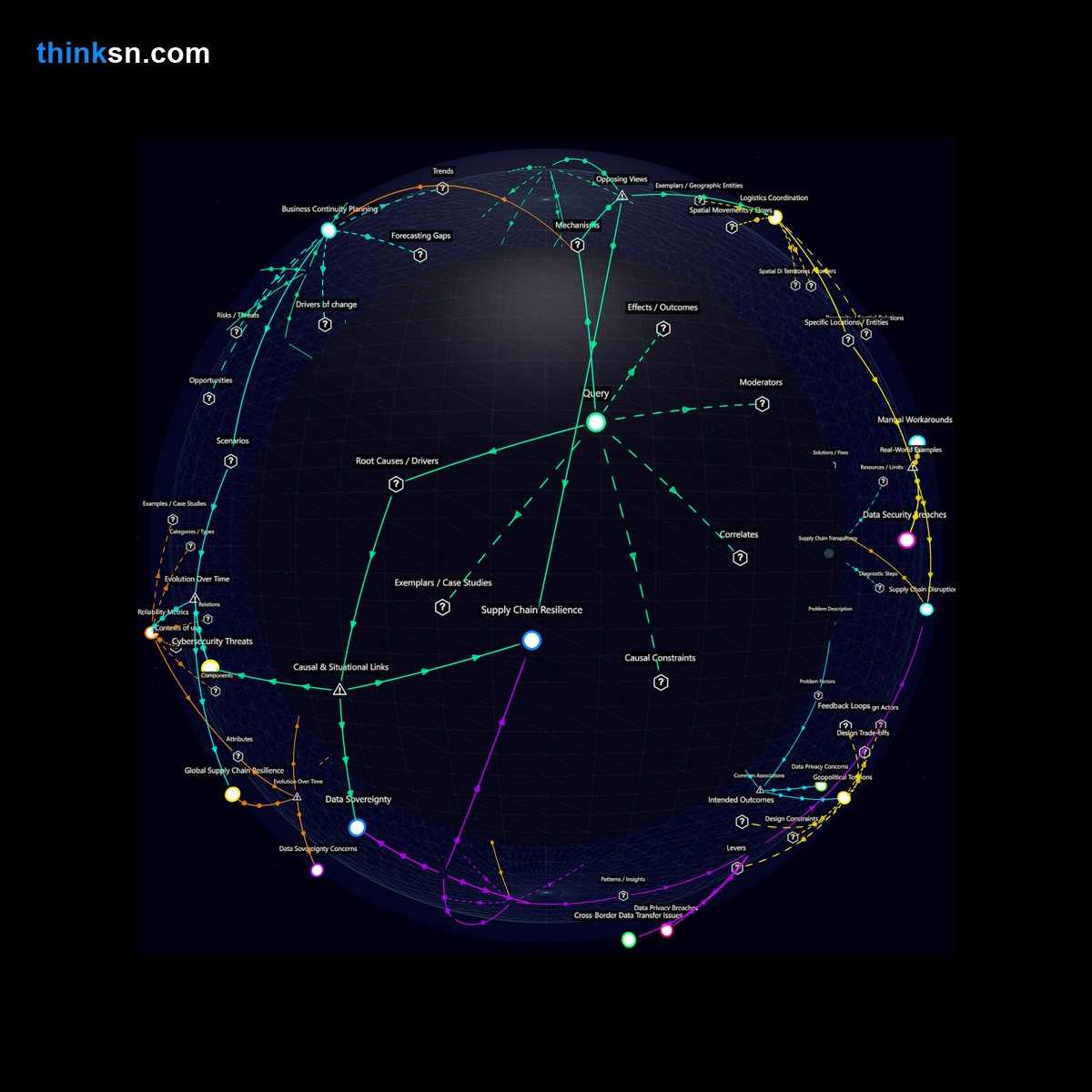
This network was generated by thinksn, an interactive tool for exploring complex questions through structured semantic analysis.
Try it with your own question: Enter any complex topic in the search bar above and explore it through multiple analytical frameworks—causal mechanisms, hidden dimensions, opposing perspectives, and more.
Click the button below to clear the page and try your own question.