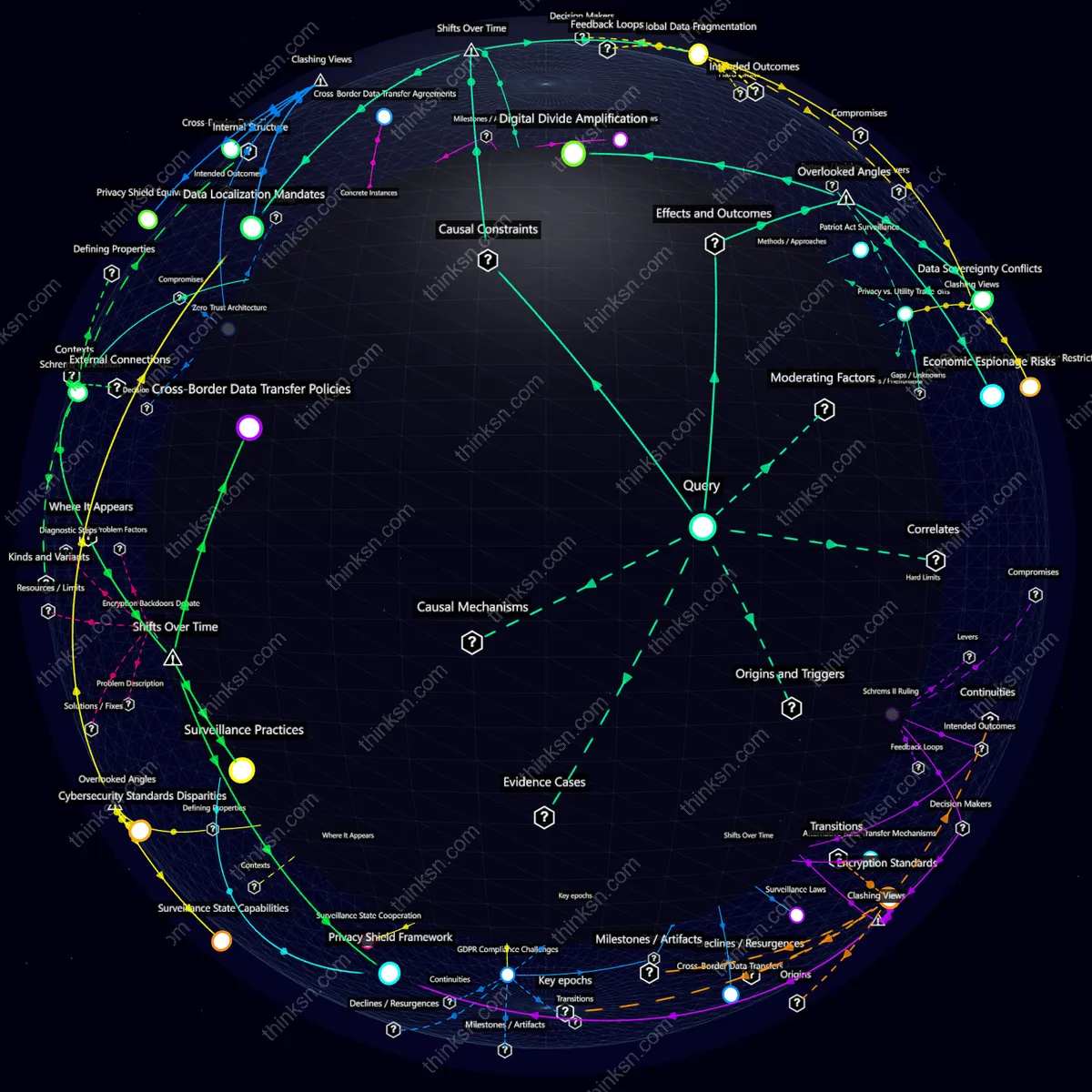
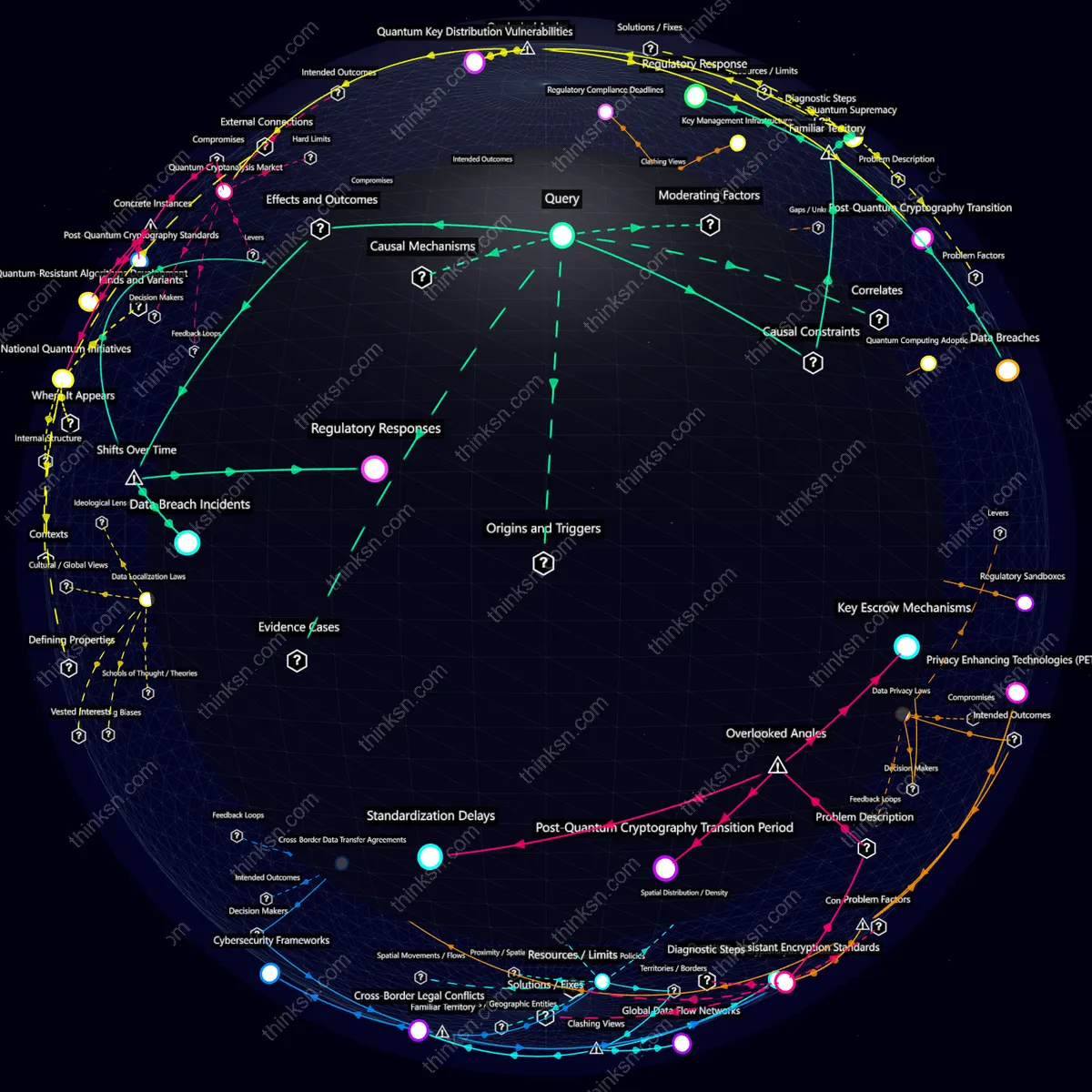
Unintended Consequences of Strict Surveillance Laws on Cross-Border Data Privacy
Analysis reveals 6 key thematic connections.
Key Findings
Data Sovereignty Conflicts
Strict surveillance laws create friction between a major country's desire for data sovereignty and international data flows. This leads to diplomatic tensions, as other nations may impose retaliatory measures, undermining global cooperation on cybersecurity and privacy standards.
Economic Espionage Risks
While intended to protect domestic security interests, such laws inadvertently open new avenues for economic espionage by foreign entities. The complex interplay between data protection and national economic strategies can lead to strategic disadvantages in the global market, particularly affecting businesses that rely on cross-border collaborations.
Digital Divide Amplification
The enforcement of strict surveillance laws disproportionately affects smaller enterprises and developing regions within a country. These entities often lack robust data protection mechanisms and may face significant operational disruptions or compliance costs, exacerbating existing digital inequality gaps.
Data Localization Mandates
Strict surveillance laws push major countries to implement data localization mandates, compelling tech companies to store user data domestically. This shift can isolate digital ecosystems, impeding innovation and collaboration while paradoxically exposing local servers to increased risk from both state actors and cybercriminals.
Surveillance Capitalism
As governments enforce strict surveillance laws for national security, tech giants may exploit this environment by enhancing their own data collection practices under the guise of compliance. This leads to a blurring between public and private surveillance, creating a new form of 'surveillance capitalism' where user privacy is further compromised in favor of corporate profit.
Global Data Fragmentation
The imposition of strict cross-border data regulations can lead to a fragmented global internet architecture. This fragmentation hinders the seamless flow of information and economic transactions, creating new forms of digital colonialism where smaller or less powerful countries struggle with unequal access to technology and knowledge.
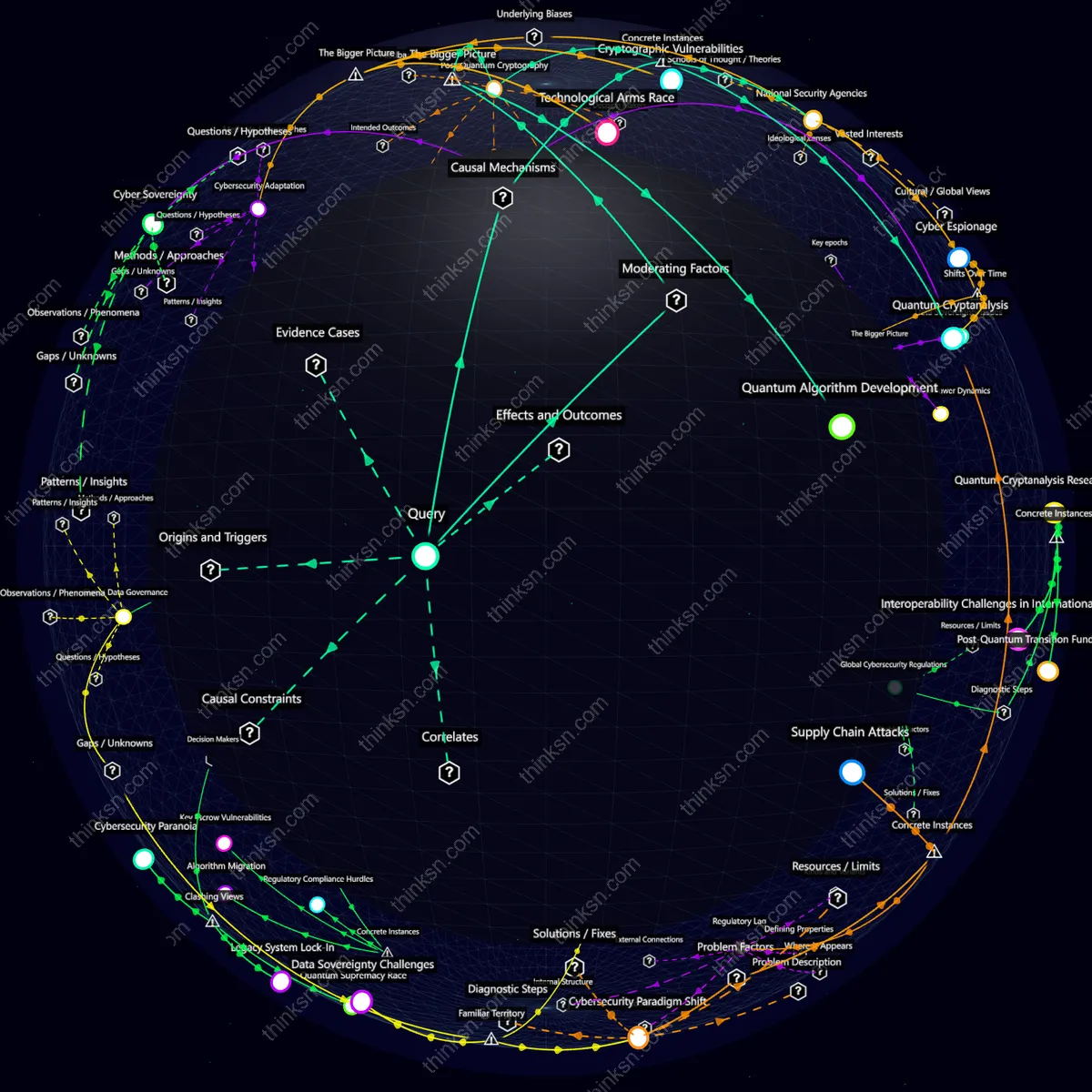
Deeper Analysis
How might surveillance capitalism evolve in response to strict surveillance laws, and what are the potential unintended consequences for cross-border data privacy and security over time?
Data Localization Laws
As nations implement stricter data localization laws to protect privacy, tech giants might shift storage infrastructure within borders, creating new geopolitical vulnerabilities. This move could fragment the internet and lead to increased surveillance by local authorities, undermining global data security.
Zero-Trust Architecture
In response to regulatory pressures, corporations may adopt zero-trust architecture, significantly restricting access and monitoring internal networks. While enhancing security against external threats, this shift could exacerbate privacy issues for employees, eroding trust within organizations as every action is closely scrutinized.
Cross-Border Data Transfer Agreements
Companies will likely engage in complex cross-border data transfer agreements to navigate conflicting national laws. These agreements can become legal quagmires, delaying innovation and increasing operational costs, while still leaving critical privacy gaps for users across different jurisdictions.
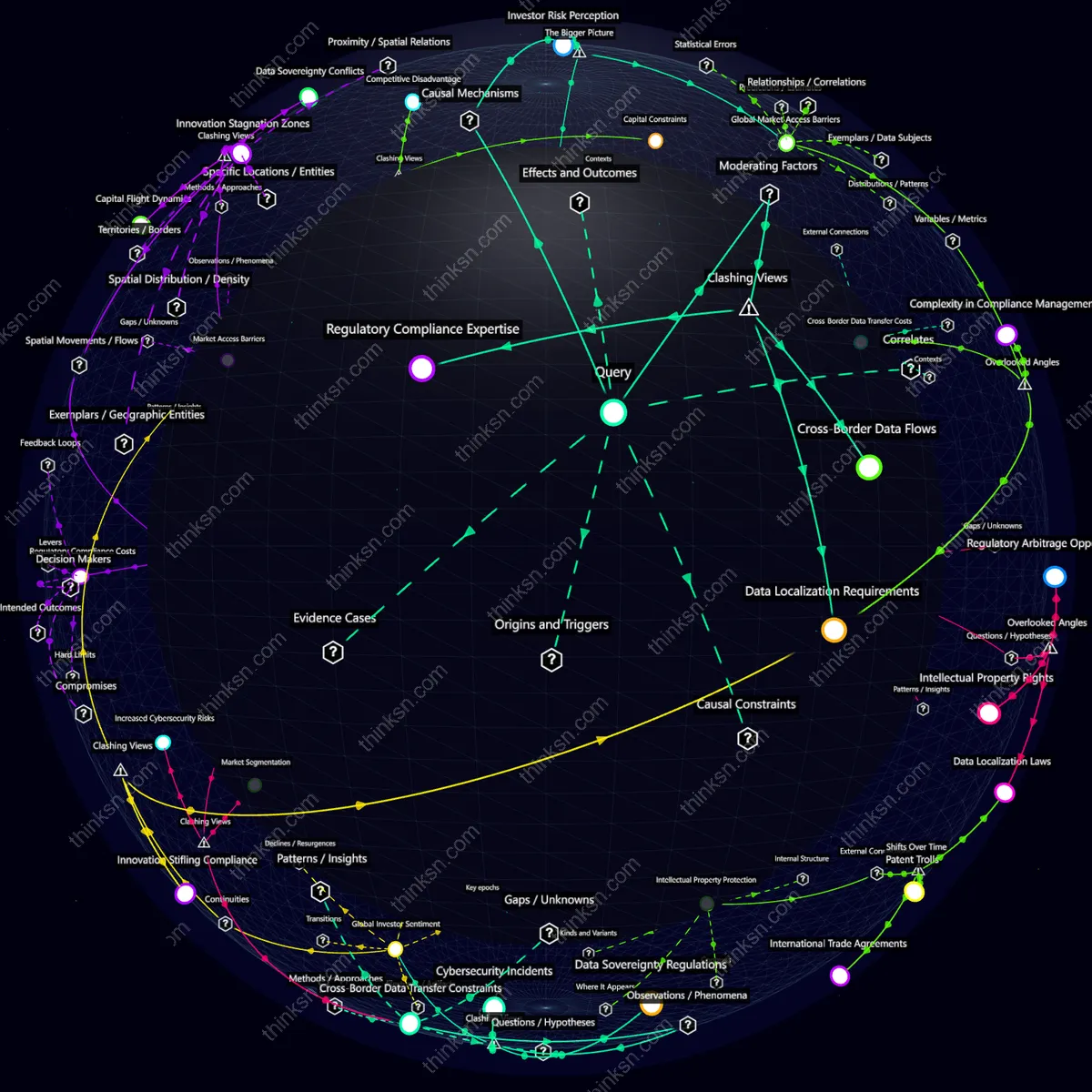
What strategies can be formulated to mitigate global data fragmentation caused by strict surveillance laws in a major country, considering cross-border data privacy and security implications?
Data Sovereignty Conflicts
As major countries enforce strict surveillance laws, data sovereignty conflicts intensify, leading to increased fragmentation. Companies face the dilemma of either adhering to local regulations and risking global accessibility or maintaining a unified data architecture at the cost of legal compliance in certain regions.
Cross-Border Data Transfer Restrictions
The imposition of cross-border data transfer restrictions by governments complicates international business operations. While these measures aim to protect domestic data privacy, they often hinder innovation and economic collaboration by forcing companies to adopt costly and complex local data storage solutions.
Privacy vs. Utility Trade-offs
Stricter surveillance laws exacerbate the tension between data privacy and utility in public services. Governments may use stringent controls to enhance security, but this can undermine user trust and impede the seamless sharing of essential information across borders, crucial for disaster response or health emergencies.
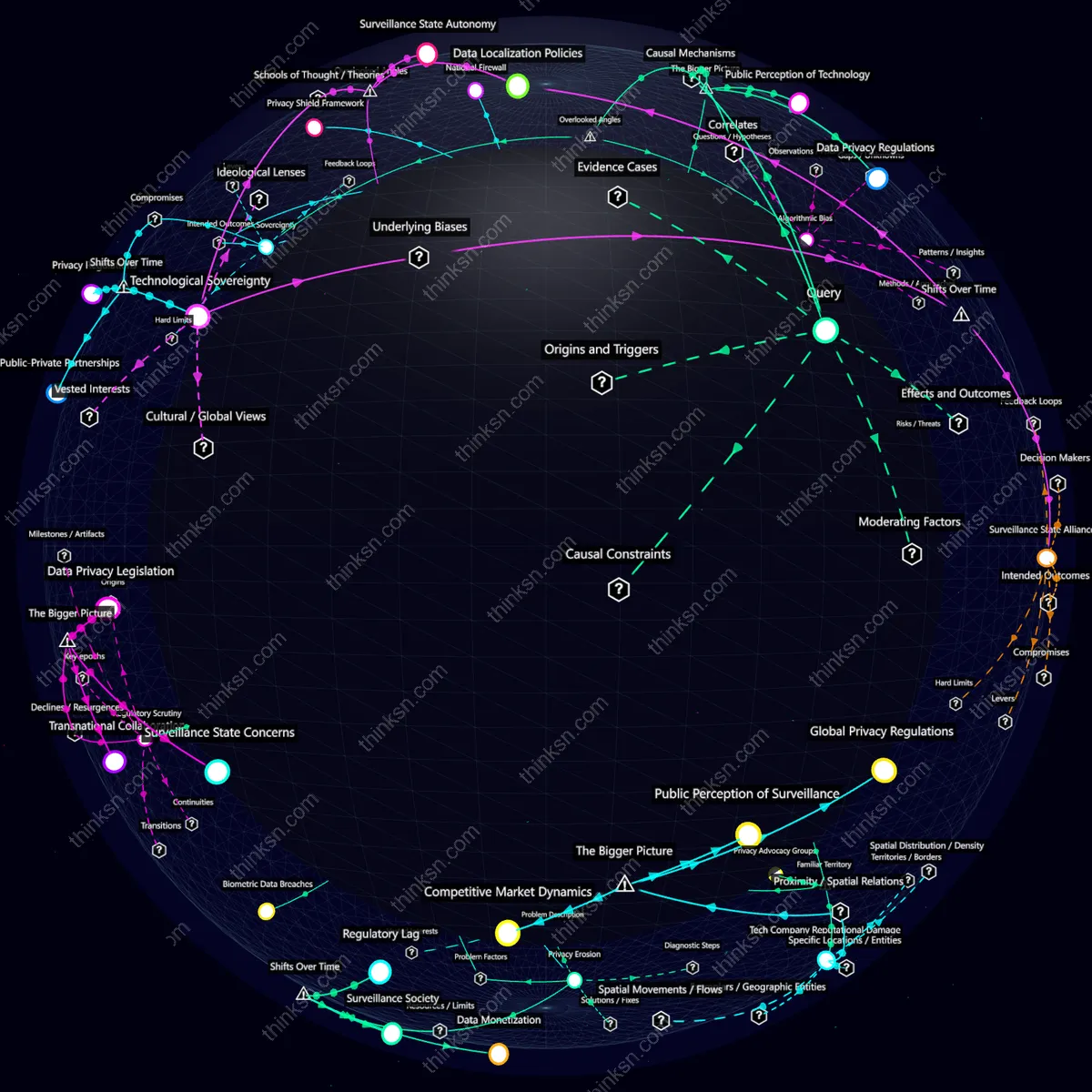
How can organizations implement a Zero-Trust Architecture to mitigate potential unintended consequences of strict surveillance laws on cross-border data privacy and security in a major country?
Data Localization Mandates
Strict data localization laws create friction with Zero-Trust Architecture by necessitating local data storage, which complicates the seamless and secure flow of data across borders. This may undermine the architecture's core principle of verifying every access request regardless of location.
Cross-Border Data Flows
Implementing a Zero-Trust Architecture in a country with strict surveillance laws could paradoxically increase cross-border data flows as organizations seek to circumvent local regulations. This unintended consequence exposes systems to new security risks and complicates compliance.
Privacy Shield Equivalents
The reliance on Zero-Trust Architecture may lead organizations to overlook the need for establishing privacy shield equivalents with foreign partners, potentially leading to legal vulnerabilities when handling cross-border data transfers. This oversight can undermine trust and operational efficiency in international collaborations.
What are the emerging insights and diverse perspectives on how privacy vs. utility trade-offs in strict surveillance laws affect cross-border data privacy and security in a major country?
Schrems II Decision
The Schrems II decision by the Court of Justice of the European Union in 2020 dismantled standard contractual clauses for data transfers to non-EU countries, challenging companies like Facebook and Google to renegotiate privacy agreements. This highlights the tension between EU's strict data protection laws and global tech giants' need for seamless cross-border operations.
Patriot Act Surveillance
The USA PATRIOT Act’s expanded surveillance powers have led to heightened scrutiny of U.S.-based tech firms by foreign governments, complicating international business dealings. Companies like Microsoft face legal challenges in Europe over data transfers due to perceived risks of U.S. government access under the Patriot Act.
Snowden NSA Leaks
Edward Snowden's revelations about the National Security Agency’s global surveillance programs exposed a deep rift between privacy advocates and national security interests, leading to reforms in Germany and other countries wary of U.S. data access but also dependent on American tech infrastructure.
Explore further:
- How does the Schrems II Decision impact the structure and enforcement of strict surveillance laws on cross-border data privacy in a major country?
- How did the Snowden NSA leaks influence the evolution of strict surveillance laws and their impact on cross-border data privacy and security over time in major countries?
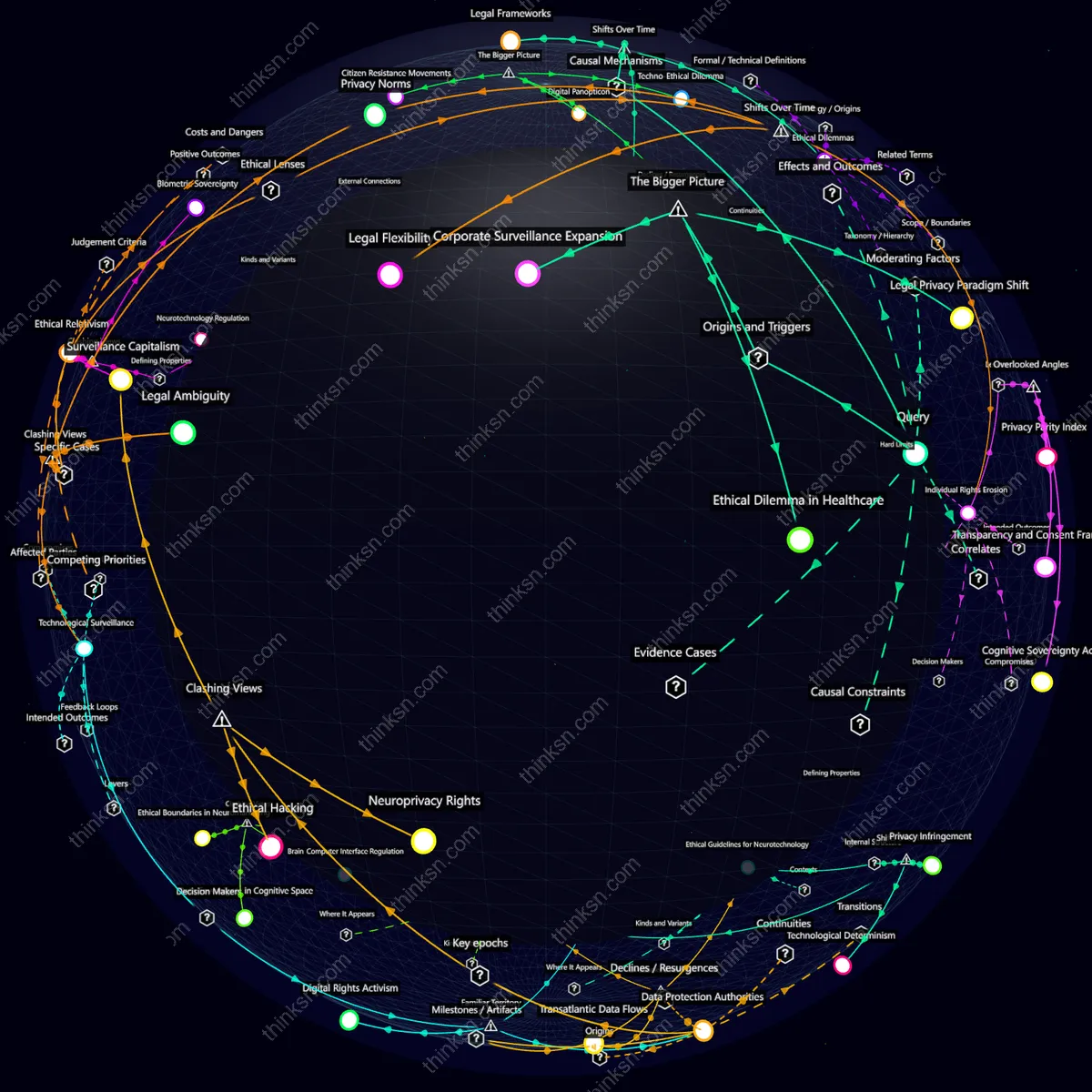
How does the Schrems II Decision impact the structure and enforcement of strict surveillance laws on cross-border data privacy in a major country?
Cross-Border Data Transfer Policies
The Schrems II Decision compels companies to reassess their data transfer mechanisms, often leading to the implementation of complex and costly supplementary measures like encryption and contractual obligations. This shift can create friction with less stringent international partners, potentially undermining economic ties while enhancing privacy protections.
Privacy Shield Framework
The invalidation of Privacy Shield due to Schrems II Decision highlights the fragility of legal frameworks in maintaining transatlantic data flows. Companies may face prolonged uncertainty and operational disruptions as they navigate alternative mechanisms, underscoring the critical importance of ongoing compliance with evolving privacy laws.
Surveillance Practices
Schrems II Decision forces surveillance agencies to reconsider their cross-border data collection strategies, potentially leading to increased scrutiny and regulation. This can result in a delicate balance between national security interests and individual privacy rights, with unintended consequences on intelligence-sharing agreements and operational capabilities.
How did the Snowden NSA leaks influence the evolution of strict surveillance laws and their impact on cross-border data privacy and security over time in major countries?
Schrems II Ruling
The Schrems II ruling by the European Court of Justice in 2020 tightened data privacy regulations, directly challenging the adequacy of U.S. surveillance laws post-Snowden leaks. This led to a significant overhaul of transatlantic data transfer agreements, highlighting the fragile interdependence between digital privacy and international trade.
Encryption Backdoors Debate
The Snowden revelations intensified debates over encryption backdoors for law enforcement, creating tension between national security interests and individual privacy rights. This debate has seen cycles of obsolescence as technology evolves faster than legal frameworks can adapt, illustrating the delicate balance between government access needs and public trust in digital security.
Privacy Shield Framework
Established in response to initial Snowden revelations, the Privacy Shield framework aimed to facilitate safe data transfers between Europe and the U.S. However, its rapid obsolescence due to legal challenges underscores the fragility of international privacy agreements when faced with evolving surveillance capabilities and public scrutiny.
Explore further:
- What alternative strategies can be formulated to protect cross-border data privacy and security in light of strict surveillance laws, considering the implications derived from the Schrems II Ruling?
- What are the potential quantitative and evaluative impacts on cross-border data privacy and security if a major country mandates encryption backdoors in strict surveillance laws, considering systemic failures and trade-offs involved?
What alternative strategies can be formulated to protect cross-border data privacy and security in light of strict surveillance laws, considering the implications derived from the Schrems II Ruling?
Data Localization Policies
In response to Schrems II, countries like China and Russia are tightening data localization laws, mandating local storage of personal information. This shift increases operational costs for multinational firms but also enhances national security by reducing reliance on foreign cloud services.
Privacy Shield Framework
The demise of the Privacy Shield has left US companies scrambling to find alternative legal bases for cross-border data transfers, leading many to adopt Standard Contractual Clauses (SCCs) with additional safeguards. However, this approach remains legally uncertain and may not fully address concerns about surveillance laws in countries like the UK or Canada.
Encryption Standards
Schrems II has spurred calls for stronger encryption standards to protect data privacy during international transfers. While beneficial, stringent encryption can also hinder lawful access by law enforcement agencies, complicating efforts to balance security and privacy.
Privacy Shield 2.0
The failure of the Privacy Shield agreement due to Schrems II accelerated efforts towards creating a new data transfer mechanism, Privacy Shield 2.0, aiming to address EU-US data transfer issues more robustly. However, this process highlights the intricate balance between regulatory compliance and practical business needs, often resulting in prolonged negotiations and delays.
Alternative Data Transfer Mechanisms
In response to Schrems II, various alternative data transfer mechanisms such as Standard Contractual Clauses (SCCs) and Binding Corporate Rules (BCRs) have gained prominence. These solutions aim to ensure legal compliance but often require significant resources for implementation and ongoing scrutiny by regulators, leading to operational inefficiencies.
Explore further:
- How have encryption standards evolved in response to strict surveillance laws, and what are the potential long-term impacts on cross-border data privacy and security?
- What are the structural components and categories of Privacy Shield 2.0, and how do they relate to the potential unintended consequences of strict surveillance laws on cross-border data privacy and security in a major country?
What are the structural components and categories of Privacy Shield 2.0, and how do they relate to the potential unintended consequences of strict surveillance laws on cross-border data privacy and security in a major country?
Data Localization Mandates
Strict data localization policies in major countries can undermine Privacy Shield 2.0 by compelling companies to store user data locally, thereby bypassing the framework's cross-border privacy protections and exposing users to legal systems with less stringent privacy standards.
Surveillance State Capabilities
The expansion of surveillance state capabilities in countries implementing strict data protection laws paradoxically weakens Privacy Shield 2.0 by enabling more invasive monitoring, which can erode trust and undermine the effectiveness of international data transfer agreements.
Cybersecurity Standards Disparities
Privacy Shield 2.0's reliance on standardized cybersecurity protocols faces challenges when countries enforce varying levels of security measures, potentially leaving users in regions with lower standards more vulnerable to cyber threats and breaches.
Data Localization Policies
The implementation of Data Localization Policies in countries like Russia and China can undermine the effectiveness of Privacy Shield 2.0 by requiring companies to store data locally, thus bypassing international privacy protections.
GDPR Compliance Challenges
Privacy Shield 2.0's stringent requirements for cross-border data transfers create a compliance burden that conflicts with GDPR standards in the EU, leading multinational corporations like Google and Facebook to struggle with inconsistent legal frameworks across regions.
Surveillance State Cooperation
In countries where surveillance is state-sanctioned, Privacy Shield 2.0 faces significant challenges as local laws often prioritize national security over individual privacy rights, forcing companies like Microsoft and Apple to navigate complex ethical dilemmas when complying with both.
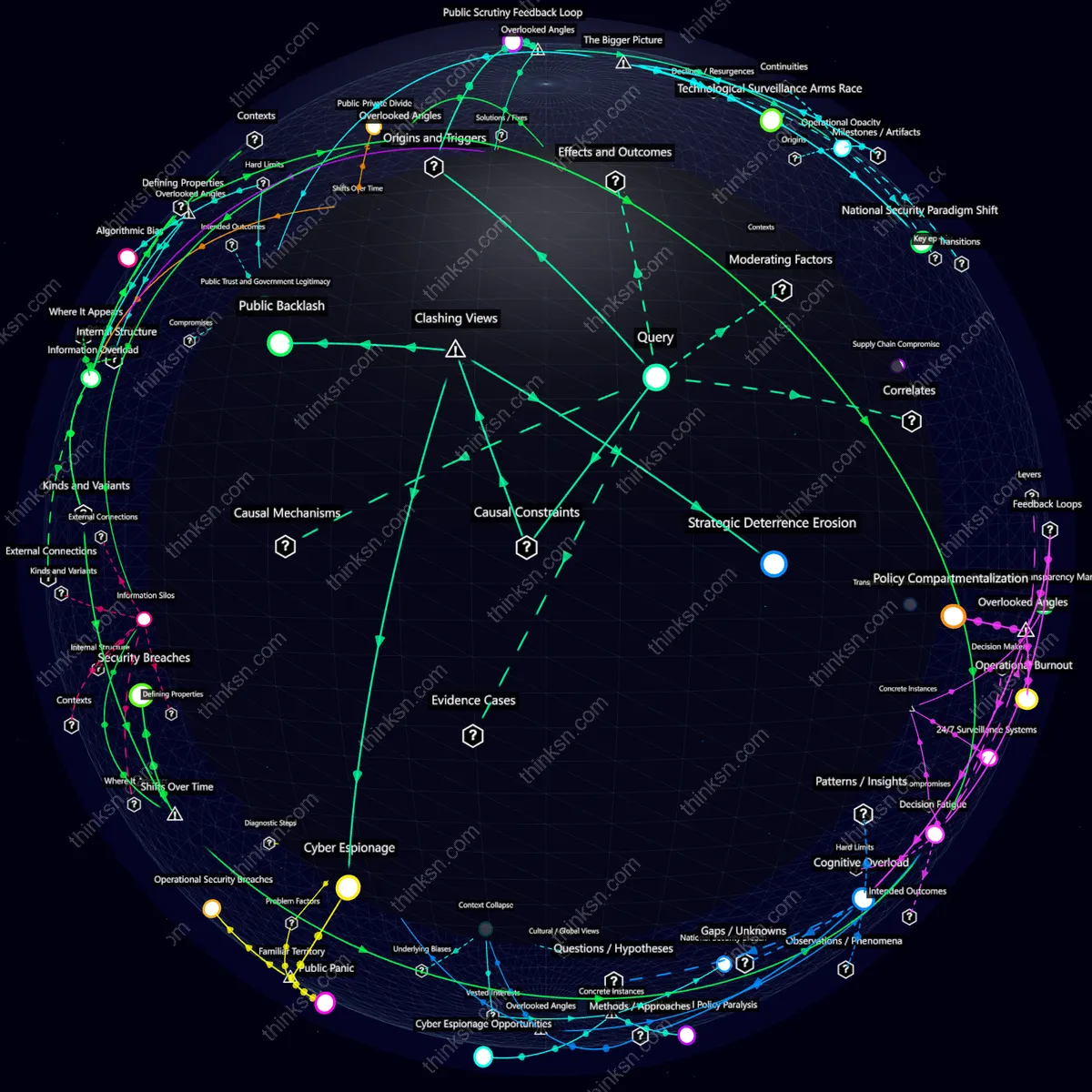
How do data localization policies impact cross-border data privacy and security in a major country under strict surveillance laws?
Cross-Border Compliance Challenges
Data Localization Policies can compel multinational corporations to develop complex compliance frameworks for each jurisdiction. This fragmented approach risks inconsistent data protection standards, creating loopholes and vulnerabilities that could be exploited by cybercriminals or state actors.
National Cybersecurity Paradox
While intended to enhance security within a country's borders, strict Data Localization Policies can paradoxically expose local systems to increased risk due to the isolation from global cybersecurity intelligence and best practices. This can make national networks less resilient against sophisticated threats.
Surveillance State Dynamics
In countries with stringent surveillance laws, Data Localization Policies may enable governments to more easily monitor and control data flows, but this also invites scrutiny from international human rights organizations and diplomatic tensions. This can isolate the country politically and economically.
How do strict surveillance laws impact GDPR compliance challenges over time for cross-border data privacy and security in a major country?
Surveillance Laws
As strict surveillance laws evolve to increase government oversight in a major country, companies face escalating GDPR compliance challenges. This leads to a paradox where enhancing national security and privacy protection can undermine international data standards, forcing firms to navigate conflicting legal landscapes.
Cross-Border Data Transfers
The tension between stringent surveillance laws and cross-border data transfers intensifies GDPR compliance issues over time. Companies must balance the need for global data exchange with the risk of breaching local regulations, leading to complex legal negotiations and potential trade-offs in market access versus privacy standards.
Data Localization Policies
Growing demands for data localization can create significant hurdles for GDPR compliance. As countries mandate that sensitive information be stored within national borders, multinational corporations face the challenge of reconciling divergent legal requirements, risking both operational inefficiencies and potential regulatory penalties.